1.List the system commands commonly used by each role.
2.Compare the target commands from step 1 against the supplied sample
/etc/rbac/cmd_priv database.
3.If you find matching entries after performing the previous steps, use those entries as a guide for assigning authorizations.
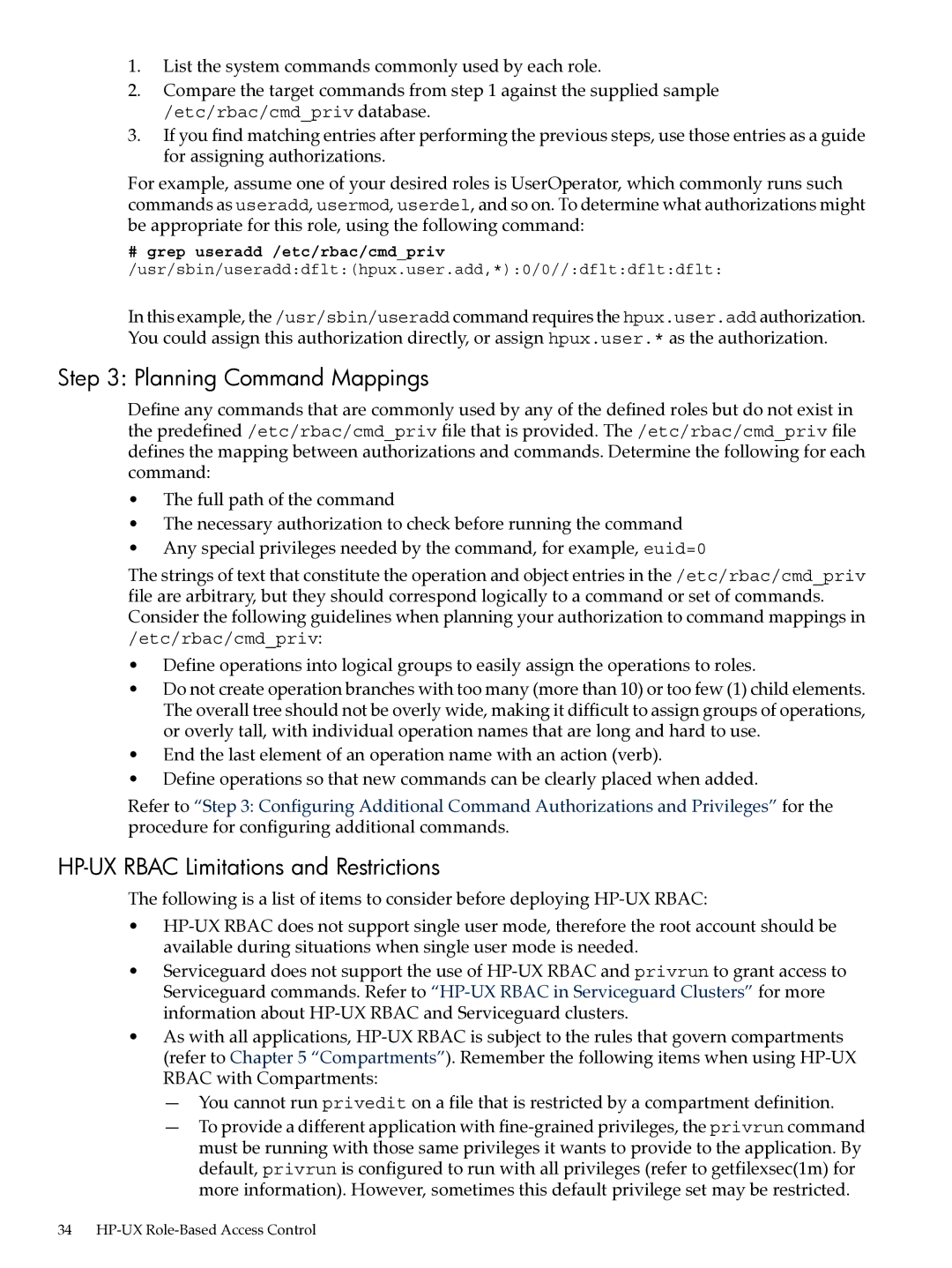
For example, assume one of your desired roles is UserOperator, which commonly runs such commands as useradd, usermod, userdel, and so on. To determine what authorizations might be appropriate for this role, using the following command:
#grep useradd /etc/rbac/cmd_priv /usr/sbin/useradd:dflt:(hpux.user.add,*):0/0//:dflt:dflt:dflt:
In this example, the /usr/sbin/useradd command requires the hpux.user.add authorization. You could assign this authorization directly, or assign hpux.user.* as the authorization.
Step 3: Planning Command Mappings
Define any commands that are commonly used by any of the defined roles but do not exist in the predefined /etc/rbac/cmd_priv file that is provided. The /etc/rbac/cmd_priv file defines the mapping between authorizations and commands. Determine the following for each command:
•The full path of the command
•The necessary authorization to check before running the command
•Any special privileges needed by the command, for example, euid=0
The strings of text that constitute the operation and object entries in the /etc/rbac/cmd_priv file are arbitrary, but they should correspond logically to a command or set of commands. Consider the following guidelines when planning your authorization to command mappings in /etc/rbac/cmd_priv:
•Define operations into logical groups to easily assign the operations to roles.
•Do not create operation branches with too many (more than 10) or too few (1) child elements. The overall tree should not be overly wide, making it difficult to assign groups of operations, or overly tall, with individual operation names that are long and hard to use.
•End the last element of an operation name with an action (verb).
•Define operations so that new commands can be clearly placed when added.
Refer to “Step 3: Configuring Additional Command Authorizations and Privileges” for the procedure for configuring additional commands.
HP-UX RBAC Limitations and Restrictions
The following is a list of items to consider before deploying
•
•Serviceguard does not support the use of
•As with all applications,
—You cannot run privedit on a file that is restricted by a compartment definition.
—To provide a different application with
34