Text Part Number OL-29168-01
Americas Headquarters
Page
Iii
N T E N T S
Advanced Setup for the Appliance
Interface Support
Understanding Inline Vlan Pair Mode
Vii
Configuring Alert Severity
Viii
Example String XL TCP Engine Match Offset Signature
Understanding Worms
Configuring Global Correlation
Configuring IP Logging
Xii
Routers
Xiii
Using Rommon
Xiv
Configuring the ASA 5585-X IPS SSP
Upgrading, Downgrading, and Installing System Images
Xvi
NotificationApp
Xvii
AIC Engine B-10
Xviii
Creating the Service Account C-5
Xix
Communication Problems
Understanding the show tech-support Command C-75
Xxi
CLI Validation Error Messages D-6
Xxii
Organization
Contents
Audience
Xxiv
Related Documentation
Conventions
Convention Indication
Xxv
Xxvi
Obtaining Documentation and Submitting a Service Request
Ii-1
Logging In Notes and Caveats
Supported User Roles
Ii-2
Logging In to the Appliance
For More Information
Config t
Connecting an Appliance to a Terminal Server
Ii-3
Exit Wr mem
Asa# session ips
Logging In to the ASA 5500-X IPS SSP
Ii-4
Asa# session
Logging In to the ASA 5585-X IPS SSP
Ii-5
Ii-6
Logging In to the Sensor
Ii-7
Ii-8
Supported IPS Platforms
IPS CLI Configuration Guide
Sensor Configuration Sequence
User Roles
Service
Administrator
Operators
Viewers
Following tips help you use the Cisco IPS CLI
CLI Behavior
Prompts
Help
Recall
Command Line Editing
Case Sensitivity
Display Options
Keys Description
Regular Expression Syntax
IPS Command Modes
Character Description
String
Matches a as well as b
Only if it is at the end of the string
Matches any character
Or more times
Sensor# configure terminal
Generic CLI Commands
CLI Keywords
OL-29168-01
Initializing Notes and Caveats
Initializing the Sensor
Understanding Initialization
Simplified Setup Mode
System Configuration Dialog
Example 2-1 Example System Configuration Dialog
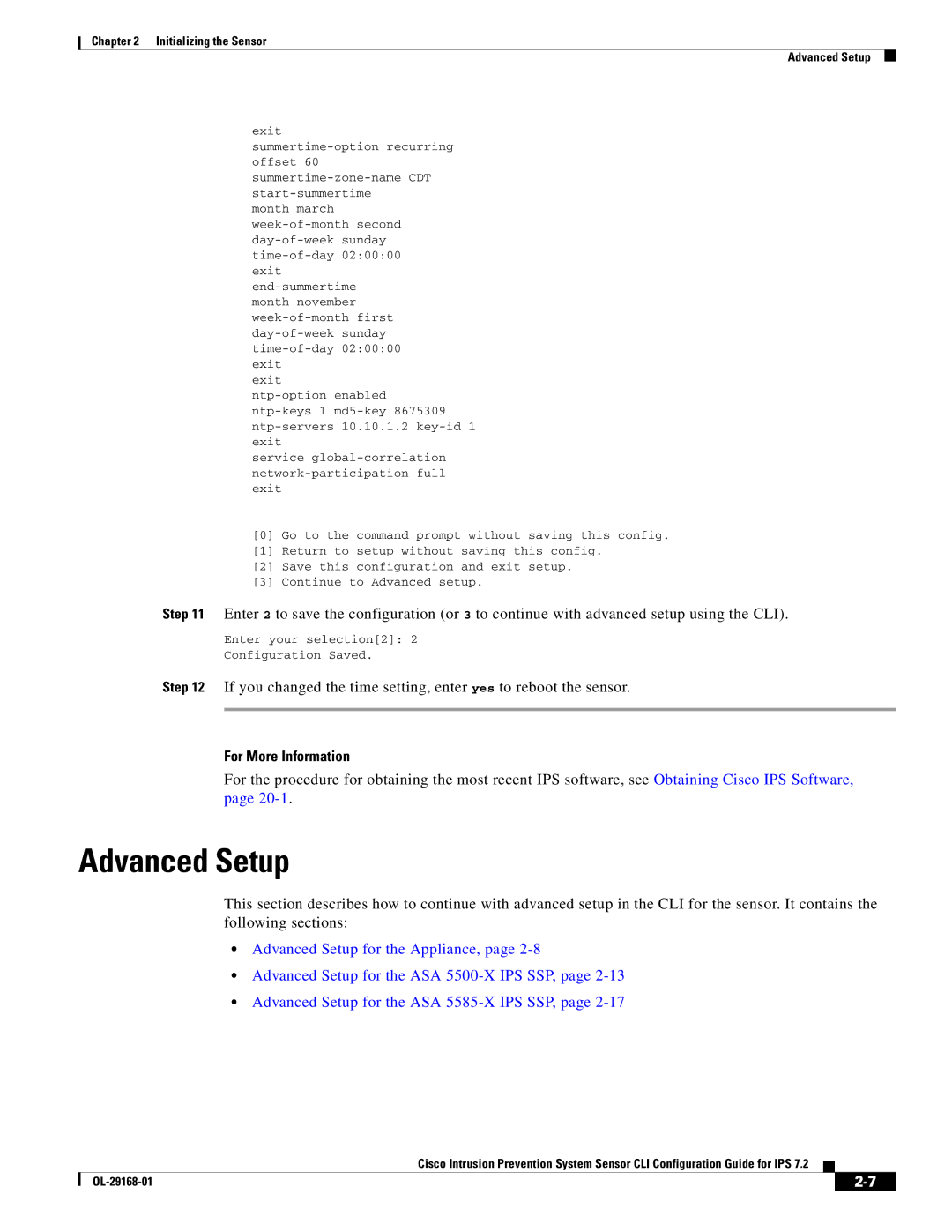
Example 2-1shows a sample System Configuration Dialog
Initializing the Sensor Basic Sensor Setup
Basic Sensor Setup
Initializing the Sensor Basic Sensor Setup
Following configuration was entered
Initializing the Sensor Advanced Setup
Advanced Setup
Advanced Setup for the Appliance
Enter a subinterface number and description
Enter 1 to edit the interface configuration
Enter numbers for Vlan 1
Press Enter to return to the available interfaces menu
Press Enter to return to the top-level editing menu
Enter 2 to edit the virtual sensor configuration
Enter 2 to modify the virtual sensor configuration, vs0
Host-ip 192.168.1.2/24,192.168.1.1
Enter 2 to save the configuration
Reboot the appliance
Advanced Setup for the ASA 5500-X IPS SSP
Enter a name and description for your virtual sensor
Enter 2 to modify the virtual sensor vs0 configuration
Modify default threat prevention settings?no
Asa-ips#show tls fingerprint
Reboot the ASA 5500-X IPS SSP
Advanced Setup for the ASA 5585-X IPS SSP
Enter 2 to edit the virtual sensor configuration
Exit Service analysis-engine
Ips-ssp#show tls fingerprint
Reboot the ASA 5585-X IPS SSP
Verifying Initialization
Sensor# show configuration
View your configuration
Sensor# show tls fingerprint
Display the self-signed X.509 certificate needed by TLS
Setup Notes and Caveats
Setting Up the Sensor
Changing Network Settings
Understanding Sensor Setup
Changing the Hostname
Enter network settings mode
Exit network settings mode
Change the sensor IP address, netmask, and default gateway
Changing the IP Address, Netmask, and Gateway
Enabling and Disabling Telnet
Enable Telnet services
Verify that Telnet is enabled
Changing the Access List
Remove the entry from the access list
Verify the change you made to the access-list
Change the value back to the default
Verify the value has been set back to the default
To change the FTP timeout, follow these steps
Changing the FTP Timeout
Change the number of seconds of the FTP timeout
Verify the FTP timeout change
Verify the banner login text message
Adding a Login Banner
Add the banner login text
Verify the login text has been removed
Verify the settings
Enable a DNS server
Login-banner-text defaulted dns-primary-server
Enabling SSHv1 Fallback
Verify that SSHv1 fallback is enabled
Change the number of seconds of the CLI session timeout
Changing the CLI Session Timeout
Verify the CLI session timeout change
Exit authentication mode
TLSDHERSAWITHAES256CBCSHA256 TLSDHEDSSWITHAES256CBCSHA256
Changing Web Server Settings
When disabled, the client can use the following ciphers
Change the port number
Sensor# configure terminal Sensorconfig# service web-server
Turn on logging for web session inactivity timeouts
Specify the web session inactivity timeout
Verify the defaults have been replaced
Turn on TLS client ciphers restriction
Adding and Removing Users
Configuring Authentication and User Parameters
Sensorconfig# username tester privilege administrator
Sensorconfig# username username password password privilege
Specify the parameters for the user
Sensor# show users all
Sensor# configure terminal Sensorconfig# no username jsmith
Configuring Authentication
To remove a user, use the no form of the command
Radius Authentication Options
Configuring Local or Radius Authentication
Enter AAA submode
Sensorconfig-aaa-rad#default-user-role operator
Enter the Radius server IP address
Ips-role=administrator Ips-role=service
Enter the IP address of the second Radius server
Specify the type of console authentication
AAA Radius Users
Configuring Packet Command Restriction
Exit AAA mode
Check your new setting
Enter authentication submode
Sensorconfig-aut#permit-packet-logging true
Sensorconfig-aut#permit-packet-logging false
Sensorconfig# user username privilege service
Creating the Service Account
Radius Authentication Functionality and Limitations
Service Account and Radius Authentication
Configuring Passwords
Exit configuration mode
Changing User Privilege Levels
Change your password
Change the privilege level from viewer to operator
Showing User Status
Display your current level of privilege
Verify all users. The account of the user jsmith is locked
Example
Configuring the Password Policy
To unlock the account of jsmith, reset the password
Locking User Accounts
Set the value back to the system default setting
Check that the setting has returned to the default
Unlocking User Accounts
Enter global configuration mode
Parentheses
Unlock the account
IPS Standalone Appliances
Configuring Time
Time Sources and the Sensor
ASA IPS Modules
Configuring Time on the Sensor
Correcting Time on the Sensor
Symbol
Manually Setting the System Clock
Displaying the System Clock
Sensor# show clock
Enter the month you want to start summertime settings
Configuring Recurring Summertime Settings
Enter start summertime submode
Sensor# clock set 1321 Mar 29
Enter the month you want to end summertime settings
Verify your settings
Enter end summertime submode
Specify the local time zone used during summertime
Exit recurring summertime submode
Configuring Nonrecurring Summertime Settings
Exit non-recurring summertime submode
Configuring Time Zones Settings
Configuring NTP
Exit time zone settings submode
Sensorconfig-hos-tim#standard-time-zone-name CST
Example
Configuring a Cisco Router to be an NTP Server
Enter service host mode
Configuring the Sensor to Use an NTP Time Source
Configure unauthenticated NTP Enter NTP configuration mode
Verify the unauthenticated NTP settings
Configure authenticated NTP Enter NTP configuration mode
Configuring SSH
Verify the NTP settings
Exit NTP configuration mode
Adding Hosts to the SSH Known Hosts List
Understanding SSH
Add an entry to the known hosts list
Sensorconfig# ssh host-key
View the key for a specific IP address
Sensor# show ssh host-keys
Adding Authorized RSA1 and RSA2 Keys
Sensorconfig# no ssh host-key
Generating the RSA Server Host Key
Sensor# show ssh server-key
Sensor# ssh generate-key
Understanding TLS
Configuring TLS
Adding TLS Trusted Hosts
Sensorconfig# tls trusted-host ip-address 10.89.146.110 port
View the fingerprint for a specific host
Displaying and Generating the Server Certificate
Remove an entry from the trusted hosts list
Verify that the key was generated
Understanding the License Key
Installing the License Key
Obtaining and Installing the License Key
Service Programs for IPS Products
Installing the License Key
Verify the sensor is licensed
Licensing the ASA 5500-X IPS SSP
Sensor# erase license-key
Uninstalling the License Key
Verify the sensor key has been uninstalled
Setting Up the Sensor Installing the License Key
OL-29168-01
Interface Notes and Caveats
Configuring Interfaces
IPS Interfaces
Understanding Interfaces
Sensor Command and Control Interface
Command and Control Interface
Sensing Interfaces
TCP Reset Interfaces
Understanding Alternate TCP Reset Interfaces
2lists the alternate TCP reset interfaces
Designating the Alternate TCP Reset Interface
Sensor Alternate TCP Reset Interface
None
Base Chassis Cards Sensing Ports Inline Interface Pairs
Interface Support
Interfaces Not
Combinations Supporting Command and Control
Interface Configuration Restrictions
Configuring Interfaces Understanding Interfaces
Interface Configuration Sequence
Configuring Physical Interfaces
Display the list of available interfaces
Configuring the Physical Interface Settings
Specify the interface for promiscuous mode
Add a description of this interface
Remove TCP resets from an interface
Sensorconfig-int-phy#alt-tcp-reset-interface none
Exit interface submode
Configuring Promiscuous Mode
Understanding Promiscuous Mode
IPv6, Switches, and Lack of Vacl Capture
Configuring Promiscuous Mode
Set span 930, 932, 960, 962 4/1-4 both
Configuring Inline Interface Mode
Understanding Inline Interface Mode
Creating Inline Interface Pairs
Configuring Inline Interface Pairs
Name the inline pair
Enable the interfaces assigned to the interface pair
Display the available interfaces
It can monitor traffic see Step
Verify that the interfaces are enabled
Verify the inline interface pair has been deleted
Exit interface configuration submode
Sensorconfig-int#no inline-interfaces PAIR1
Understanding Inline Vlan Pair Mode
Configuring Inline Vlan Pair Mode
Configuring Inline Vlan Pairs
Been configured
Configuring Inline Vlan Pairs
OL-29168-01
Verify the inline Vlan pair settings
Set up the inline Vlan pair
Sensorconfig-int#no inline-interfaces interfacename
Designate an interface
To delete Vlan pairs Delete one Vlan pair
Configuring Vlan Group Mode
Understanding Vlan Group Mode
Deploying Vlan Groups
Configuring Vlan Groups
Configuring Inline Vlan Groups
None Subinterface-type
Assign the VLANs to this group Assign specific VLANs
Set up the Vlan group
Specify an interface
Add a description for the Vlan group
Configure unassigned VLANs
Verify the Vlan group settings
Delete Vlan groups Delete one Vlan group
Configuring Inline Bypass Mode
Understanding Inline Bypass Mode
Configure bypass mode
Configuring Inline Bypass Mode
Configuring Bypass Mode
Configuring Interface Notifications
Configuring Interface Notifications
Configuring CDP Mode
Enable CDP mode
Enabling CDP Mode
Sensorconfig-int#cdp-mode forward-cdp-packets
Displaying Interface Statistics
Sensor# show interfaces Interface Statistics
Sensor# show interfaces brief
Clear the statistics
Display the statistics for a specific interface
Sensor# show interfaces Management0/0
Sensor# show interfaces clear Interface Statistics
Displaying Interface Traffic History
To display interface traffic history, follow these steps
Displaying Historical Interface Statistics
Display the interface traffic history by the hour
Display the interface traffic history by the minute
Bytes Received Mbps
Virtual Sensor Notes and Caveats
Configuring Virtual Sensors
Advantages and Restrictions of Virtualization
Understanding the Analysis Engine
Understanding Virtual Sensors
Inline TCP Session Tracking Mode
Http Advanced Decoding
Normalization and Inline TCP Evasion Protection Mode
Adding, Editing, and Deleting Virtual Sensors
Restrictions
Adding Virtual Sensors
Adding a Virtual Sensor
Sensorconfig-ana-vir#description virtual sensor
Add a virtual sensor
Add a description for this virtual sensor
Verify the virtual sensor settings
Enable Http advanced decoding
Assign an event action rules policy to this virtual sensor
Assign a signature definition policy to this virtual sensor
Exit analysis engine mode
Editing or Deleting a Virtual Sensor
Editing and Deleting Virtual Sensors
Edit the virtual sensor, vs1
Edit the description of this virtual sensor
Delete a virtual sensor
Verify the edited virtual sensor settings
Sensorconfig-ana-vir#physical-interface GigabitEthernet0/2
Sensorconfig-ana# exit
Creating a Global Variable
Configuring Global Variables
Create the variable for the maximum number of open IP logs
Create the flow depth variable
Sensor# show statistic analysis-engine
Create the variable for service activity
Verify the global variable settings
OL-29168-01
Understanding Policies
Signature Definition Notes and Caveats
Working With Signature Definition Policies
Sensor# list signature-definition-configurations
Delete a signature definition policy
Sensor# copy signature-definition sig0 sig1
Confirm the signature definition policy has been deleted
Reset a signature definition policy to factory settings
Understanding Signatures
Creating Signature Variables
Configuring Signature Variables
Understanding Signature Variables
Adding, Editing, and Deleting Signature Variables
Signature Definition Options
Configuring Signatures
Configuring Alert Frequency
Specify the signature you want to configure
Configuring Alert Frequency
Enter alert frequency submode
Specify the summary key
Configuring Alert Severity
Configuring Alert Severity
To configure the alert severity, follow these steps
Assign the alert severity
Exit signatures submode
Configuring the Event Counter
Configuring the Event Counter
Enter event counter submode
Optional Enable alert interval
Specify the signature fidelity rating for this signature
Configuring Signature Fidelity Rating
Configuring the Signature Fidelity Rating
Choose the signature you want to configure
Configuring the Status of Signatures
Changing the Signature Status
Change the status for this signature
Specify the vulnerable OSes for this signature
Configuring the Vulnerable OSes for a Signature
Configuring Vulnerable OSes
Assigning Actions to Signatures
Specify the percentage for rate limiting
Configuring Event Actions
Configure the event action
Exit event action submode
Configuring AIC Signatures
Understanding the AIC Engine
AIC Engine and Sensor Performance
Configuring the Application Policy
Enable inspection of FTP traffic
Configuring the Application Policy
Enable Http application policy enforcement
Sensorconfig-sig-app-htt#aic-web-ports 80-80,3128-3128
Signature ID Define Request Method
AIC Request Method Signatures
Signature ID Signature Description
AIC Mime Define Content Type Signatures
Signature ID Signature Description
Signature ID Signature Description
Signature ID Transfer Encoding Method
AIC Transfer Encoding Signatures
Signature ID FTP Command
AIC FTP Commands Signatures
Creating an AIC Signature
Defining a MIME-Type Policy Signature
Define the content type
Specify the event action
Define the signature type
Signature ID and Name Description Range Default Action
Configuring IP Fragment Reassembly
Understanding IP Fragment Reassembly
For More Information
Configuring the Method for IP Fragment Reassembly
Configuring IP Fragment Reassembly Parameters
Enter edit default signatures submode
Specify the engine
Understanding TCP Stream Reassembly
Configuring TCP Stream Reassembly
Configuring the IP Fragment Reassembly Method
Verify the setting
TCP Stream Reassembly Signatures and Configurable Parameters
TCP Stream Reassembly Signatures
SYN
SYN
Configuring TCP Stream Reassembly Signatures
Configuring the Mode for TCP Stream Reassembly
Sensorconfig-sig-str#tcp-reassembly-mode strict
Configuring the TCP Stream Reassembly Parameters
Sensorconfig-sig-str#tcp-3-way-handshake-required true
Configuring IP Logging Parameters
Configuring IP Logging
Specify the number of packets you want logged
Specify the length of time you want the sensor to log
Sequence for Creating a Custom Signature
Creating Custom Signatures
Example String TCP Engine Signature
Creating a String TCP Engine Signature
Verify the settings
Example Service Http Engine Signature
Enter signature description mode
Creating a Service Http Engine Signature
Specify a signature name
Specify the alert traits. The valid range is from 0 to
Example Meta Engine Signature
Configure the Regex parameters
Exit alert frequency submode
Exit Regex submode
Meta Signature Engine Enhancement
Defining Signatures Creating Custom Signatures
Creating a Meta Engine Signature
Example IPv6 Engine Signature
Specify the IP version
Sensorconfig-sig-sig#engine atomic-ip-advanced
Specify IPv6
Specify the L4 protocol
Creating a String XL TCP Engine Signature
Example String XL TCP Engine Match Offset Signature
Specify the String XL TCP engine
Sensorconfig-sig-sig-str#specify-exact-match-offset yes
Specify the regex string to search for in the TCP packet
Specify an exact match offset for this signature
Specify a minimum match offset for this signature
Example String XL TCP Engine Minimum Match Length Signature
Specify a signature ID and subsignature ID for the signature
Specify a new Regex string to search for and turn on UTF-8
OL-29168-01
Event Action Rules Notes and Caveats
Configuring Event Action Rules
Understanding Event Action Rules
Understanding Security Policies
Signature Event Action Processor
Action filter
Alert and Log Actions
Deny Actions
Understanding Deny Packet Inline
Other Actions
TCP Normalizer Signature Warning
Event Action Rules Configuration Sequence
Sensor# copy event-action-rules rules0 rules1
Working With Event Action Rules Policies
Working With Event Action Rules Policies
Event Action Variables
Reset an event action rules policy to factory settings
Delete an event action rules policy
Confirm the event action rules instance has been deleted
Understanding Event Action Variables
When configuring IPv6 addresses, use the following format
IPv4 Addresses
IPv6 Addresses
Working With Event Action Variables
Sensorconfig-eve#variables variable-ipv4 address
Adding, Editing, and Deleting Event Action Variables
Verify that you edited the event action rules variable
Verify that you added the event action rules variable
Delete an event action rules variable
Verify the event action rules variable you deleted
Calculating the Risk Rating
Configuring Target Value Ratings
2illustrates the risk rating formula
Understanding Threat Rating
Adding, Editing, and Deleting Target Value Ratings
Adding, Editing, and Deleting Target Value Ratings
Understanding Event Action Overrides
Configuring Event Action Overrides
Configuring Event Action Overrides
Write an alert to Event Store
Log packets from both the attacker and victim IP addresses
Write verbose alerts to Event Store
Write events that request an Snmp trap to the Event Store
Understanding Event Action Filters
Configuring Event Action Filters
Configuring Event Action Filters
OL-29168-01
Configuring Event Action Filters
Add any comments you want to use to explain this filter
Verify the settings for the filter
Edit an existing filter
Edit the parameters see Steps 4a through 4l
Verify that the filter has been moved to the inactive list
Sensorconfig-eve#filters move name1 inactive
Move a filter to the inactive list
Understanding Passive OS Fingerprinting
Configuring OS Identifications
Passive OS Fingerprinting Configuration Considerations
IP Address Range Set
Adding, Editing, Deleting, and Moving Configured OS Maps
IOS
Unix
Specify the host OS type
Configuring OS Maps
Verify the settings for the OS map
Edit an existing OS map
Enable passive OS fingerprinting
Verify that you have moved the OS maps
Move an OS map to the inactive list
Displaying and Clearing OS Identifications
Sensorconfig-eve-os#no configured-os-map name2
Delete an OS map
Verify that the OS map has been deleted
Displaying and Clearing OS Identifications
Configuring General Settings
Verify that the OS IDs have been cleared
Sensor# clear os-identification learned
Understanding Event Action Aggregation
Understanding Event Action Summarization
Configuring Event Action General Settings
Configuring the General Settings
Enable or disable the summarizer. The default is enabled
Enter general submode
Verify the settings for general submode
Configuring the Denied Attackers List
Sensorconfig-eve-gen#global-filters-status enabled disabled
Adding a Deny Attacker Entry to the Denied Attackers List
Adding Entries to the Denied Attacker List
Monitoring and Clearing the Denied Attackers List
Remove the deny attacker entry from the list
Enter yes to remove the deny attacker entry from the list
Delete the denied attackers list
Displaying and Deleting Denied Attackers
Displaying Events
Monitoring Events
Clear only the statistics
Important to know if the list has been cleared
Sensor# show events
Displaying Events
To display events from the Event Store, follow these steps
Sensor# show events alert past
Sensor# show events error warning 100000 Feb 9
Display alerts from the past 45 seconds
Display events that began 30 seconds in the past
Clearing Events from Event Store
Enter yes to clear the events
Sensor# show events past
OL-29168-01
Anomaly Detection Notes and Caveats
Configuring Anomaly Detection
Understanding Worms
Understanding Anomaly Detection
Anomaly Detection Modes
Anomaly Detection Zones
Anomaly Detection Configuration Sequence
Signature ID Subsignature ID Name Description
Anomaly Detection Signatures
Signature ID Subsignature ID Name Description
Enabling Anomaly Detection
Enable anomaly detection operational mode
Working With Anomaly Detection Policies
Exit analysis engine submode
Sensor# copy anomaly-detection ad0 ad1
Working With Anomaly Detection Policies
Delete an anomaly detection policy
Reset an anomaly detection policy to factory settings
Configuring Anomaly Detection Operational Settings
Sensor# list anomaly-detection-configurations
Verify that the anomaly detection instance has been deleted
Configuring Anomaly Detection Operational Settings
Configuring the Internal Zone
Specify the worm timeout
Sensorconfig-ano-ign#source-ip-address-range
Configuring the Internal Zone
Configuring the Internal Zone
Enable the internal zone
Configure TCP protocol Configure UDP protocol
Configure the other protocols
Configuring TCP Protocol for the Internal Zone
Configuring Internal Zone TCP Protocol
Enable TCP protocol
Them and configure your own scanner values
Enable the service for that port
Verify the TCP configuration settings
Set the scanner threshold
Configuring UDP Protocol for the Internal Zone
Enable UDP protocol
Configuring the Internal Zone UDP Protocol
Verify the UDP configuration settings
Associate a specific port with UDP protocol
Configuring Anomaly Detection Configuring the Internal Zone
Configuring the Internal Zone Other Protocols
Configuring Other Protocols for the Internal Zone
Enable the other protocols
Associate a specific number for the other protocols
Verify the other configuration settings
Configuring the Illegal Zone
Configuring the Illegal Zone
Configuring the Illegal Zone
Understanding the Illegal Zone
Sensorconfig-ano-ill#ip-address-range
Configuring TCP Protocol for the Illegal Zone
Enable the illegal zone
Configuring the Illegal Zone TCP Protocol
Enabled true defaulted Sensorconfig-ano-ill-tcp#
Configuring the Illegal Zone UDP Protocol
Configuring UDP Protocol for the Illegal Zone
Sensorconfig-ano-ill-udp-dst-yes# scanner-threshold
Configuring the Illegal Zone Other Protocols
Configuring Other Protocols for the Illegal Zone
Verify the other protocols configuration settings
Understanding the External Zone
Configuring the External Zone
Configuring the External Zone
Enable the external zone
Configuring TCP Protocol for the External Zone
Configuring the External Zone
Configuring the External Zone TCP Protocol
Sensorconfig-ano-ext-tcp#
Configuring the External Zone UDP Protocol
Configuring UDP Protocol for the External Zone
Sensorconfig-ano-ext-udp-dst-yes# scanner-threshold
Configuring Other Protocols for the External Zone
To configure other protocols for a zone, follow these steps
Configuring the External Zone Other Protocols
KB and Histograms
Configuring Learning Accept Mode
Example Histogram
Configuring Learning Accept Mode
Configuring Learning Accept Mode
Sensorconfig-ano#learning-accept-mode manual
Sensorconfig-ano#learning-accept-mode auto
Displaying KB Files
Working With KB Files
Display the KB files for all virtual sensors
Sensor# show ad-knowledge-base files
Display the KB files for a specific virtual sensor
Saving and Loading KBs Manually
Manually Saving and Loading KBs
Save the current KB file and store it as a new name
Copying, Renaming, and Erasing KBs
Remove a KB file from a specific virtual sensor
Copying, Renaming, and Removing KB Files
Rename a KB file
Comparing Two KBs
Displaying the Differences Between Two KBs
To compare two KBs, follow these steps
Locate the file you want to compare
Displaying the Thresholds for a KB
Sensor# show ad-knowledge-base vs1 files Virtual Sensor vs1
Displaying KB Thresholds
Sensor# show statistics anomaly-detection vs0
Displaying Anomaly Detection Statistics
To display anomaly detection statistics, follow these steps
Display the statistics for all virtual sensors
Disabling Anomaly Detection
Disable anomaly detection operational mode
OL-29168-01
10-1
Global Correlation Notes and Caveats
10-2
Understanding Global Correlation
Participating in the SensorBase Network
1shows how we use the data
Understanding Reputation
Type of Data Purpose
10-3
10-4
Understanding Network Participation
10-5
Understanding Efficacy
10-6
Global Correlation Features and Goals
Understanding Reputation and Risk Rating
10-7
Global Correlation Requirements
10-8
Understanding Global Correlation Sensor Health Metrics
10-9
Global Correlation Update Client
Sensorconfig-glo#global-correlation-inspection on
Configuring Global Correlation
Turn on global correlation inspection
Specify the level of global correlation inspection
Turn on reputation filtering
Configuring Network Participation
Exit global correlation submode
10-11
Turn on network participation
Turning on Network Participation
Enter yes to agree to participate in the SensorBase Network
10-12
10-13
Troubleshooting Global Correlation
Disabling Global Correlation
10-14
Displaying Global Correlation Statistics
Disabling Global Correlation
10-15
Clear the statistics for global correlation
10-16
11-1
External Product Interface Notes and Caveats
Understanding External Product Interfaces
11-2
Understanding the CSA MC
11-3
External Product Interface Issues
11-4
Configuring the CSA MC to Support the IPS Interface
Adding External Product Interfaces and Posture ACLs
11-5
Adding External Product Interfaces
11-6
Sensorconfig-ext-cis-hos#posture-acls insert name1 begin
Sensorconfig-ext-cis-hos#allow-unreachable-postures yes
Enter the network address the posture ACL will use
Choose the action deny or permit the posture ACL will take
11-8
Troubleshooting External Product Interfaces
Exit external product interface submode
12-1
IP Logging Notes and Caveats
12-2
Configuring Automatic IP Logging
Understanding IP Logging
12-3
Configuring Automatic IP Logging
Monitor the IP log status with the iplog-status command
Configuring Manual IP Logging
12-4
Sensor# iplog vs0 192.0.2.1 duration
Displaying the Contents of IP Logs
Display a brief list of all IP logs
Stopping Active IP Logs
Disabling IP Logging Sessions
Stop the IP log session
Stop all IP logging sessions on a virtual sensor
Copying IP Log Files to Be Viewed
Copying IP Log Files
12-7
12-8
Copy the IP log to your FTP or SCP server
13-1
Packet Display And Capture Notes and Caveats
13-2
Understanding Packet Display and Capture
Displaying Live Traffic on an Interface
Sensor# packet display GigabitEthernet0/1
Displaying Live Traffic From an Interface
13-3
Display information about the packet file
Capturing Live Traffic on an Interface
13-4
Expression ip proto \\tcp
View the captured packet file
Capturing Live Traffic on an Interface
13-5
Sensor# packet capture GigabitEthernet0/1
13-6
Copying the Packet File
View any information about the packet file
Erasing the Packet File
View the packet file with Wireshark or Tcpdump
Erase the packet file
Verify that you have erased the packet file
13-8
14-1
Blocking Notes and Caveats
14-2
Understanding Blocking
14-3
Vlan B
Destination IP Signature ID Signature Name Protocol
Understanding Rate Limiting
Data
Icmp
Before Configuring ARC
Understanding Service Policies for Rate Limiting
UDP
TCP
14-6
Supported Devices
14-7
Configuring Blocking Properties
Sensorconfig# service network-access
Enter network access submode
Allowing the Sensor to Block Itself
14-8
Exit network access submode
Configure the sensor not to block itself
Disabling Blocking
14-9
To disable blocking or rate limiting, follow these steps
Blocks on the devices are updated
Enable blocking on the sensor
Verify that the setting has been returned to the default
14-11
Specifying Maximum Block Entries
Sensorconfig-net-gen#default block-max-entries
Return to the default value of 250 blocks
Change the maximum number of block entries
14-12
Specifying the Block Time
Time for manual blocks is set when you request the block
Signatures
These steps
14-14
Enabling ACL Logging
14-15
Enabling Writing to Nvram
Disable writing to Nvram
Logging All Blocking Events and Errors
Verify that writing to Nvram is disabled
14-16
14-17
Configuring the Maximum Number of Blocking Interfaces
Verify the default setting
Return the setting to the default
Specify the maximum number of interfaces
Verify the number of maximum interfaces
Configuring Addresses Never to Be Blocked
Configuring Addresses Never to Block
Sensorconfig-net-gen#never-block-hosts
For a network
Specify the password for the user
Configuring User Profiles
Create the user profile name
Enter the username for that user profile
Specify the enable password for the user
Configuring Blocking and Rate Limiting Devices
How the Sensor Manages Devices
14-21
14-22
Configuring the Sensor to Manage Cisco Routers
14-23
Routers and ACLs
Specify the IP address for the router controlled by the ARC
14-24
14-25
Switches and VACLs
14-26
Sensorconfig-net-cat#communication telnet ssh-3des
Specify the Vlan number
Configuring the Sensor to Manage Cisco Firewalls
Optional Add the pre-VACL name
Optional Add the post-VACL name
14-28
Configuring the Sensor to be a Master Blocking Sensor
14-29
Configuring the Master Blocking Sensor
Sensorconfig-web# exit
Enter password
Sensorconfig# tls trusted-host ip-address 192.0.2.1 port
Add a master blocking sensor entry
Specify whether or not the host uses TLS/SSL
Configuring Network Blocking
Configuring Host Blocking
Blocking a Host
End the host block
Blocking a Network
Configuring Connection Blocking
End the network block
14-32
Blocking a Connection
Obtaining a List of Blocked Hosts and Connections
End the connection block
Blocks are
14-34
15-1
Snmp Notes and Caveats
Understanding Snmp
15-2
Configuring Snmp
15-3
Configuring Snmp General Parameters
15-4
Configuring Snmp Traps
Exit notification submode
Enable Snmp traps
Configuring Snmp Traps
Specify whether you want detailed Snmp traps
Enter the trap community string
Supported Mibs
CISCO-ENHANCED-MEMPOOL-MIB CISCO-ENTITY-ALARM-MIB
CISCO-CIDS-MIB
15-6
15-7
15-8
16-1
Displaying the Current Configuration
16-2
First Review Cisco Confidential
16-3
Displaying the Current Submode Configuration
16-4
16-5
16-6
16-7
16-8
Sensorconfig# service health-monitor
16-9
16-10
16-11
16-12
16-13
Severity warning defaulted protected entry zone-name csi
16-14
16-15
Sensorconfig# service trusted-certificate
16-16
Filtering the Current Configuration Output
To filter the more command, follow these steps
Filtering Using the More Command
Press Ctrl-Cto stop the output and return to the CLI prompt
16-17
16-18
Filtering the Current Submode Configuration Output
Filtering the Submode Output
Displaying the Contents of a Logical File
16-20
Displaying the Logical File Contents
16-21
16-22
16-23
Backing Up the Current Configuration to a Remote Server
Restoring the Current Configuration From a Backup File
16-24
Creating and Using a Backup Configuration File
Erasing the Configuration File
16-25
Press Enter to continue or enter no to stop
16-26
17-1
Administrative Tasks for the Sensor
Recovering the Password
Administrative Notes and Caveats
Understanding Password Recovery
17-2
Using the Grub Menu
Recovering the Password for the Appliance
Platform Description Recovery Method
17-3
Using Rommon
Recovering the Password for the ASA 5500-X IPS SSP
Enter the following commands to reset the password
Sample Rommon session
Press Enter to confirm
Enter your new password twice
Session to the ASA 5500-X IPS SSP
17-5
Using the Asdm
Recovering the Password for the ASA 5585-X IPS SSP
Asa# hw-module module 1 password-reset
17-6
Asa# show module
Session to the ASA 5585-X IPS SSP
17-7
Disabling Password Recovery Using the CLI
Disabling Password Recovery
Disabling Password Recovery Using the IDM or IME
17-8
Troubleshooting Password Recovery
Verifying the State of Password Recovery
Sensorconfig-hos#show settings include password
Clearing the Sensor Databases
17-10
Clearing the Sensor Database
Enter yes to clear the inspectors database
Over the past 60 minutes and over the past 72 hours
Displaying the Inspection Load of the Sensor
Show the histogram of the inspection load
17-11
17-12
17-13
Configuring Health Status Information
ASA 5500-X IPS SSP and Memory Usage
Configuring Health Statistics
Platform Yellow Red Memory Used
17-14
17-15
Set the threshold for memory usage
Set the number of days since the last signature update
Set the missed packet threshold
17-16
17-17
Showing Sensor Overall Health Status
Exit health monitoring submode
Create the banner login
Creating a Banner Login
Show the health and security status of the sensor
Enter your message
Terminating CLI Sessions
Find the CLI ID number associated with the login session
To terminate a CLI session, follow these steps
Terminate the CLI session of jsmith
17-20
Configuring Events
Modifying Terminal Properties
17-21
17-22
17-23
Clearing Events from the Event Store
Displaying the System Clock
Configuring the System Clock
17-24
Sensor# show clock detail
17-25
Manually Setting the System Clock
Clearing the Denied Attackers List
17-26
17-27
Displaying Policy Lists
Display the list of policies for event action rules
Displaying Statistics
Display the list of policies for signature definition
17-28
17-29
Administrative Tasks for the Sensor
17-30
Sensor# show statistics authentication
Display the statistics for authentication
Display the statistics for anomaly detection
17-31
Display the statistics for the Event Store
Display the statistics for the Event Server
17-32
Sensor# show statistics event-server General
Show statistics host
Display the statistics for the host
17-33
Display the statistics for the ARC
Display the statistics for the logging application
17-34
Sensor# show statistics logger
17-35
17-36
17-37
Statistics web-server
Display the statistics for the web server
17-38
Sensor# show statistics logger clear
17-39
Varlog Files
Displaying Tech Support Information
Displaying Tech Support Information
17-40
View version information
Displaying Version Information
17-41
Sensor# show version
17-42
Cancel the output and get back to the CLI prompt
View configuration information
17-43
Diagnosing Network Connectivity
Enter yes to continue the reset
Resetting the Appliance
Following example shows a successful ping
Following example shows an unsuccessful ping
Stop all applications and power down the appliance
Displaying Command History
Enter yes to continue with the reset and power down
17-45
Sensor# show inventory
Displaying Hardware Inventory
17-46
PID IPS-4360-PWR-AC
17-47
Display the route of IP packet you are interested
Tracing the Route of an IP Packet
17-48
Inventory
Show the current configuration for ARC submode
Displaying Submode Settings
Sensor config# service network-access
17-49
17-50
17-51
Show the ARC settings in terse mode
17-52
18-1
Configuring the ASA 5500-X IPS SSP
18-2
Configuration Sequence for the ASA 5500-X IPS SSP
Obtain the details about the ASA 5500-X IPS Ssps
Verifying Initialization for the ASA 5500-X IPS SSP
Confirm the information
18-3
ASA 5500-X IPS SSP and Virtualization
Creating Virtual Sensors for the ASA 5500-X IPS SSP
Creating Virtual Sensors
18-4
18-5
Creating Virtual Sensors
18-6
Sensorconfig-ana-vir#physical-interface PortChannel0/0
Asa# show ips
Assigning Virtual Sensors to Contexts
18-7
Add three context modes to multiple mode
Enter multiple mode
Assign virtual sensors to the security contexts
18-8
Configure MPF for each context
ASA 5500-X IPS SSP and Bypass Mode
Confirm the configuration
SensorApp Fails
18-10
SensorApp is Reconfigured
ASA 5500-X IPS SSP and the Normalizer Engine
18-11
ASA 5500-X IPS SSP and Jumbo Packets
ASA 5500-X IPS SSP and Memory Usage
18-12
Health and Status Information
18-13
Asa-ips#debug module-boot
18-14
Early reservations == bootmem 0000000000
18-15
18-16
18-17
18-18
IRQ
18-19
Single ASA in Fail-Close Mode
Single ASA in Fail-Open Mode
Two ASAs in Fail-Open Mode
ASA 5500-X IPS SSP Failover Scenarios
Two ASAs in Fail-Close Mode
New and Modified Commands
Configuration Examples
18-21
Firewall Mode Security Context Multiple Command Mode Routed
Defaults
Allocate-ips
Single Context System
Related Commands Description
Command History Release Modification
Examples
18-23
18-24
19-1
ASA 5585-XIPS SSP Notes and Caveats
19-2
Configuration Sequence for the ASA 5585-X IPS SSP
Obtain the details about the ASA 5585-X IPS SSP
Verifying Initialization for the ASA 5585-X IPS SSP
19-3
Asa# show module 1 details
19-4
Creating Virtual Sensors for the ASA 5585-X IPS SSP
ASA 5585-X IPS SSP and Virtualization
19-5
ASA 5585-X IPS SSP Virtual Sensor Configuration Sequence
Example, rules1
Command, for example sig1
Virtual sensor that you create
19-6
19-7
19-8
Asaconfig-ctx#
Asaconfig-ctx# Config-url disk0/c2.cfg
19-9
19-10
ASA 5585-X IPS SSP and Bypass Mode
ASA 5585-X IPS SSP and the Normalizer Engine
19-11
ASA 5585-X IPS SSP and Jumbo Packets
19-12
Ips-ssp#hardware-module module 1 recover configure
Module 1 details
Asa# hw-module module 1 reset
19-13
19-14
Ips-ssp#hw-module module 1 recover configure
19-15
Traffic Flow Stopped on IPS Switchports
Asaconfig# debug module-boot
19-16
Failover Scenarios
19-17
19-18
20-1
IPS 7.2 File List
Obtaining Cisco IPS Software
IPS Software Versioning
Enter your username and password
Downloading Cisco IPS Software
20-2
Minor Update
Major Update
Service Pack
Patch Release
20-4
Signature Update
Signature Engine Update
20-5
Recovery and System Image Files
20-6
IPS Software Release Examples
20-7
Accessing IPS Documentation
20-8
Cisco Security Intelligence Operations
21-1
Upgrade Notes and Caveats
21-2
Upgrades, Downgrades, and System Images
Upgrading the Sensor
Supported FTP and HTTP/HTTPS Servers
IPS 7.21E4 Files
21-3
21-4
Upgrade Notes and Caveats
Manually Upgrading the Sensor
Enter the password when prompted
Upgrade the sensor
Sensorconfig# upgrade url/IPS-SSP10-K9-7.2-1-E4.pkg
Upgrading the Sensor
21-6
Working With Upgrade Files
21-7
Upgrading the Recovery Partition
Configuring Automatic Updates
Configuring Automatic Upgrades
Enter the server password. The upgrade process begins
21-8
21-9
21-10
Configuring Automatic Upgrades
Specify the password of the user
Specify the username for authentication
Exit automatic upgrade submode
21-11
Sensor# autoupdatenow
Applying an Immediate Update
21-12
Sensor# show statistics host
21-13
Recovering the Application Partition
Downgrading the Sensor
Recovering the Application Partition Image
Installing System Images
Recover the application partition image
Sensorconfig# recover application-partition
21-15
Connecting an Appliance to a Terminal Server
Tftp Servers
21-16
Installing the System Image for the IPS 4345 and IPS
PCI
21-17
If necessary, assign the gateway IP address
Assign the Tftp server IP address
21-18
Rommon ping server
21-19
Installing the System Image for the IPS 4510 and IPS
Rommon
21-20
21-21
If necessary, assign the Tftp server IP address
Periodically check the recovery until it is complete
Installing the System Image for the ASA 5500-X IPS SSP
Image the ASA 5500-X IPS SSP
21-22
21-23
Installing the System Image for the ASA 5585-X IPS SSP
21-24
To enable debugging of the software installation process
Specify the default gateway of the ASA 5585-X IPS SSP
Asa# hw-module module 1 recover boot
Leave the Vlan ID at
21-26
Installing the ASA 5585-X IPS SSP System Image Using Rommon
Rommon #0 set
21-27
21-28
21-29
21-30
IPS System Design
Understanding the IPS System Architecture
Figure A-1illustrates the system design for IPS software
Figure A-2 System Design for IPS 4500 Series Sensors
System Applications
Appendix a System Architecture System Applications
For detailed information about SDEE, see SDEE, page A-33
Security Features
Understanding the MainApp
MainApp
MainApp Responsibilities
ARC
Understanding the Event Store
Event Store
Stamp Value Meaning
Event Data Structures
Table A-1shows some examples
IPS Events
NotificationApp
Vlan
PEP
CtlTransSource
Figure A-3
Attack Response Controller
Figure A-4illustrates the ARC
Understanding the ARC
ARC Features
Supported Blocking Devices
Fwsm
ACLs and VACLs
Maintaining State Across Restarts
Scenario
Connection-Based and Unconditional Blocking
To unblock an IP address
Blocking with Cisco Firewalls
To clear all blocks
No shun ip
Logger
Blocking with Catalyst Switches
Understanding the AuthenticationApp
AuthenticationApp
Authenticating Users
Configuring Authentication on the Sensor
Managing TLS and SSH Trust Relationships
Web Server
SensorApp
Understanding the SensorApp
Inline, Normalization, and Event Risk Rating Features
Packet Flow
SensorApp New Features
Signature Event Action Processor
CollaborationApp
Update Components
Error Events
SwitchApp
User Roles
CLI
Communications
Service Account
Idapi
Idconf
Cidee
Cisco IPS File Structure
Summary of Cisco IPS Applications
Using the Idapi
Application Description
CLI
Java applet that provides an Html IPS management interface
IDM
IME
Events
Understanding Signature Engines
Signature Engines
Appendix B Signature Engines Understanding Signature Engines
Appendix B Signature Engines Understanding Signature Engines
General Parameters
Master Engine
Parameter Description Value
Signature-id Specifies the ID of this signature
Sig-name
Promiscuous Delta
Vulnerable OS List
Alert Frequency
Obsoletes
Event Actions
Name Description
To Match Regular Expression
AIC Engine
\NNN
AIC Engine Parameters
Understanding the AIC Engine
AIC Engine and Sensor Performance
Parameter Description
Alarm-on-non-http-traffic
Table B-6 AIC FTP Engine Parameters
Atomic ARP Engine
Atomic Engine
Atomic IP Advanced Engine
Atomic IP Advanced Engine Restrictions
Isatap
String
IPv6
Parameter Description Value
OL-29168-01
IPV4
L4 Protocol ICMPv6
Icmp ID
L4 Protocol TCP and UDP
OL-29168-01
Atomic IP Engine
Parameter Description Value
Appendix B Signature Engines
OL-29168-01
Atomic IPv6 Signatures
Atomic IPv6 Engine
Fixed Engine
Table B-11 Fixed TCP Engine Parameters
Flood Engine
Flood Net Engine Parameters
Meta Engine
Protocol Specifies which kind of traffic to inspect
Name1
Component-list Specifies the Meta engine component
Multi String Engine
Normalizer Engine
IPv6 Fragments
IP Fragmentation Normalization
TCP Normalization
ASA IPS Modules and the Normalizer Engine
Service Engines
Service DNS Engine
Understanding the Service Engines
Service FTP Engine
Service Generic Engine
Table B-20 Service Generic Engine Parameters
Service H225 Engine
Setup
Setup
ASN.1-PER
Tpkt
Service Http Engine
Crlfcrlf
Service Ident Engine
Service Msrpc Engine
Smbcomtransaction
Service Mssql Engine
Service NTP Engine
Service RPC Engine
Service P2P Engine
Parameter Description Value
Service SMB Advanced Engine
Msrpc Uuid
Service Snmp Engine
Specify-object-id-Enables
Service SSH Engine
Service TNS Engine
State Engine
Table B-32lists the parameters specific to the State engine
String Engines
Table B-33 String Icmp Engine Parameters
Table B-35 String UDP Engine
String XL Engines
Parameter Description Value
Unsupported String XL Parameters
Data Nodes
Sweep Engines
Sweep Engine
Type
Sweep Other TCP Engine
Sweep Other TCP Engine Parameters
Traffic Anomaly Engine
Signature
Traffic Icmp Engine
Trojan Engines
Bug Toolkit
Troubleshooting
Creating and Using a Backup Configuration File
Preventive Maintenance
Understanding Preventive Maintenance
Sensor# copy current-config backup-config
Backing Up the Current Configuration to a Remote Server
Creating the Service Account
Disaster Recovery
Password Recovery
ASA 5500 series adaptive Adaptive security appliance CLI
Security appliance IPS modules Command
Using Rommon
Password-Reset issued for module ips
Recovering the Password for the ASA 5585-X IPS SSP
0123 21E4
Disabling Password Recovery
Verifying the State of Password Recovery
Synchronizing IPS Clocks with Parent Device Clocks
For the procedure for configuring NTP, see Configuring NTP,
Time Sources and the Sensor
Generate the hosts statistics again after a few minutes
Verifying the Sensor is Synchronized with the NTP Server
Generate the host statistics
Advantages and Restrictions of Virtualization
TFor More Information
To learn more about Worms, see Understanding Worms,
When to Disable Anomaly Detection
Command output
Reboot the sensor
Analysis Engine Not Responding
Enter show tech-support and save the output
External Product Interfaces Issues
Troubleshooting Loose Connections
Troubleshooting the Appliance
External Product Interfaces Troubleshooting Tips
Analysis Engine is Busy
Communication Problems
Cannot Access the Sensor CLI Through Telnet or SSH
More
Sensor# show configuration include access-list
Correcting a Misconfigured Access List
Make sure the sensor cabling is correct
Duplicate IP Address Shuts Interface Down
Make sure the IP address is correct
SensorApp and Alerting
SensorApp is Not Running
AnalysisEngine 20130410110072014 Release
Physical Connectivity, SPAN, or Vacl Port Issue
Sensor# show interfaces
Unable to See Alerts
Sensor# show interfaces FastEthernet0/1
Make sure you have Produce Alert configured
Check for alerts
Sensor# show interfaces GigabitEthernet0/1
Sensorconfig-int#physical-interfaces GigabitEthernet0/1
Sensor Not Seeing Packets
Exit the service account Log in to the sensor CLI
Cleaning Up a Corrupted SensorApp Configuration
Check to see that the interface is up and receiving packets
Replace the virtual sensor file
Start the IPS services
Troubleshooting Blocking
Blocking
Sensor# cids start
Verifying the ARC is Running
Make sure you have the latest software updates
If the ARC is not connecting, look for recurring errors
Sensor# show events error hhmmss month day year include nac
Sensor# show events error 000000 Apr 01 2011 include nac
For More Information
Verify the IP address for the managed devices
Device Access Issues
Start the manual block of the bogus host IP address
Sensorname Sensor Management Time-Based Actions Host Blocks
Blocking Not Occurring for a Signature
Enabling SSH Connections to the Network Device
Verifying the Master Blocking Sensor Configuration
Exit network access general submode
Enabling Debug Logging
Enable debug logging for all zones
Logging
View the zone names
Turn on individual zone control
Exit master zone control
Protected entry zone-name nac
Exit the logger submode
Turn on debugging for a particular zone
Press Enter to apply changes or type no to discard them
Zone Names
Table C-2lists the debug logger zone names
Zone Name Description
Directing cidLog Messages to SysLog
TCP Reset Not Occurring for a Signature
Upgrading Error
Software Upgrades
Make sure the correct alarms are being generated
Sensor# show events alert
Issues With Automatic Update
Which Updates to Apply and Their Prerequisites
Updating a Sensor with the Update Stored on the Sensor
Click the Advanced tab
Troubleshooting the IDM
Cannot Launch the IDM Loading Java Applet Failed
Delete the temp files and clear the history in the browser
Cannot Launch the IDM-The Analysis Engine Busy
Signatures Not Producing Alerts
Troubleshooting the IME
Time Synchronization on IME and the Sensor
Troubleshooting the ASA 5500-X IPS SSP
Not Supported Error Message
Health and Status Information
E1000 00000005.0 PCI INT a disabled
303
Appendix C Troubleshooting
Usb
CRS
IRQ
Failover Scenerios
ASA 5500-X IPS SSP and the Normalizer Engine
ASA 5500-X IPS SSP and Jumbo Packets
ASA 5500-X IPS SSP and Memory Usage
Hw-module module 1 reset command
Troubleshooting the ASA 5585-X IPS SSP
Reset issued for module in slot Asa# show
Mgmt IP addr 192.0.2.3
Failover Scenarios
ASA 5585-X IPS SSP and the Normalizer Engine
Traffic Flow Stopped on IPS Switchports
ASA 5585-X IPS SSP and Jumbo Packets
Gathering Information
Tech Support Information
Health and Network Security Information
Displaying Tech Support Information
Understanding the show tech-support Command
Sensor# show tech-support page System Status Report
Tech Support Command Output
= No
Displaying Version Information
Understanding the show version Command
Version Information
Version 29.1 Platform IPS4360 Serial Number
Service aaa
Displaying Statistics
Understanding the show statistics Command
Statistics Information
Percentage Thread Sec Min Average
Inspection Stats Inspector Active Call Create Delete
Display the statistics for anomaly detection
Sensor# show statistics event-store
Sensor# show statistics denied-attackers
Sensor# show statistics event-server
Threat
Multicast MTU1500 Metric1
Appendix C Troubleshooting Gathering Information
Display the statistics for the notification application
Name Current
OL-29168-01
Sensor# show statistics web-server listener-443
Interfaces Information
Understanding the show interfaces Command
Displaying Interface Traffic History
Interfaces Command Output
Avg Load Peak Load
GigabitEthernet0/1 Time Packets Received Bytes Received Mbps
Events Information
Displaying Events
Understanding the show events Command
Sensor Events
Displaying Events
100
101
CidDump Script
Clearing Events
Enter the following command
Uploading and Accessing Files on the Cisco FTP Site
102
Usr/cids/idsRoot/bin/cidDump
URI
CLI Error Messages
Reason Command
Error Message Reason Command
Packet-file but no packet-file has
System that has not been upgraded
Been captured
User attempted to downgrade a
Operator or viewer user attempted to Initial login
User attempted to cancel a CLI
Log in when the maximum number
Administrator user attempted to log Initial login
Appendix D CLI Error Messages
Reason/Location
CLI Validation Error Messages
Interface and optional sub-interface being
Detection configuration file that is currently in use
Added to the virtual sensor entry physical
Interface set has already been assigned to another
OL-29168-01
GL-1
GL-2
To detect worm-infected hosts
GL-3
GL-4
Certificate for one CA issued by another CA
Authoritative private key
GL-5
GL-6
A public outside network
Dual In-line Memory Modules
To the transmit line and reads data from the receive line
802.1q to be used
GL-8
GL-9
Procedures, and basic data transport methods
An ITU standard that governs H.245 endpoint control
GL-10
GL-11
GL-12
GL-13
Proprietary branches
Detailed information about signatures
GL-14
GL-15
GL-16
Quality and service availability
GL-17
Unauthorized activity
Network devices. Used with the IDS MC
Analysis Engine
GL-18
GL-19
GL-20
Network asset through its IP address
Authorization, and accounting
Local system. Telnet is defined in RFC
GL-21
GL-22
RFC
Through a switch. Also known as security ACLs
Version identifier. Part of the UDI
GL-23
GL-24
GL-25
Payload reassembly
Hosts
GL-26
IN-1
AIC FTP
AIC Http
IN-2
TACACS+
NAT
ARP
IN-3
IN-4
Asdm
SSP
IN-5
Radius
IN-6
BO2K
URL Cidee
IN-7
Exec
IN-8
IN-9
IN-10
IN-11
CSA MC
IN-12
TFN
IN-13
AIC FTP AIC Http
IN-14
IN-15
IN-16
Idapi
Idconf
IN-17
Idiom
ASA 5500-X IPS SSP ASA 5585-X IPS SSP
IN-18
Tcpdump
IN-19
IPS SSP
IN-20
SSH
Loki
IN-21
Snmp
IN-22
IN-23
IN-24
Sdee
RTT
Http A-33
IN-25
IN-26
IN-27
IN-28
AIC
IN-29
Cidee Idconf Idiom Sdee
Smtp
IN-30
TFN2K
TAC
TLS
IN-31
IN-32
BO2K Loki TFN2K
Sensor initialization Sensor setup Version display
Upgrade command
Sensing process not running
Viewer role privileges
IN-34