Instant Broadband® Series
•Any - If you select Any for the Remote Security Gateway, as shown in Figure
Figure
Encryption
Using Encryption also helps make your connection more secure. There are two different types of encryption: DES or 3DES (3DES is recommended because it is more secure). You may choose either of these, but it must be the same type of encryption that is being used by the VPN device at the other end of the tunnel. Or, you may choose not to encrypt by selecting Disable.
Authentication
Authentication acts as another level of security. There are two types of authen- tication: MD5 and SHA (SHA is recommended because it is more secure). As with encryption, either of these may be selected, provided that the VPN device at the other end of the tunnel is using the same type of authentication. Or, both ends of the tunnel may choose to Disable authentication.
EtherFast® Cable/DSL Firewall Router with
Key Management
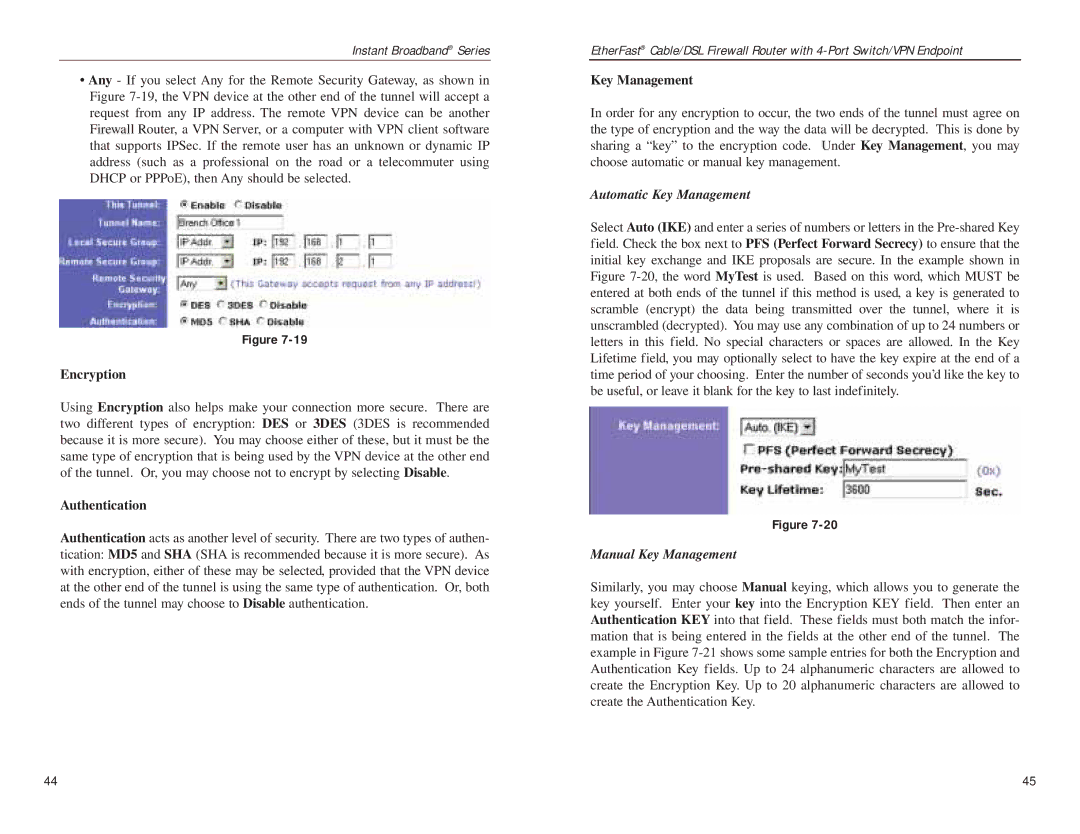
In order for any encryption to occur, the two ends of the tunnel must agree on the type of encryption and the way the data will be decrypted. This is done by sharing a “key” to the encryption code. Under Key Management, you may choose automatic or manual key management.
Automatic Key Management
Select Auto (IKE) and enter a series of numbers or letters in the
Figure
Manual Key Management
Similarly, you may choose Manual keying, which allows you to generate the key yourself. Enter your key into the Encryption KEY field. Then enter an Authentication KEY into that field. These fields must both match the infor- mation that is being entered in the fields at the other end of the tunnel. The example in Figure
44 | 45 |