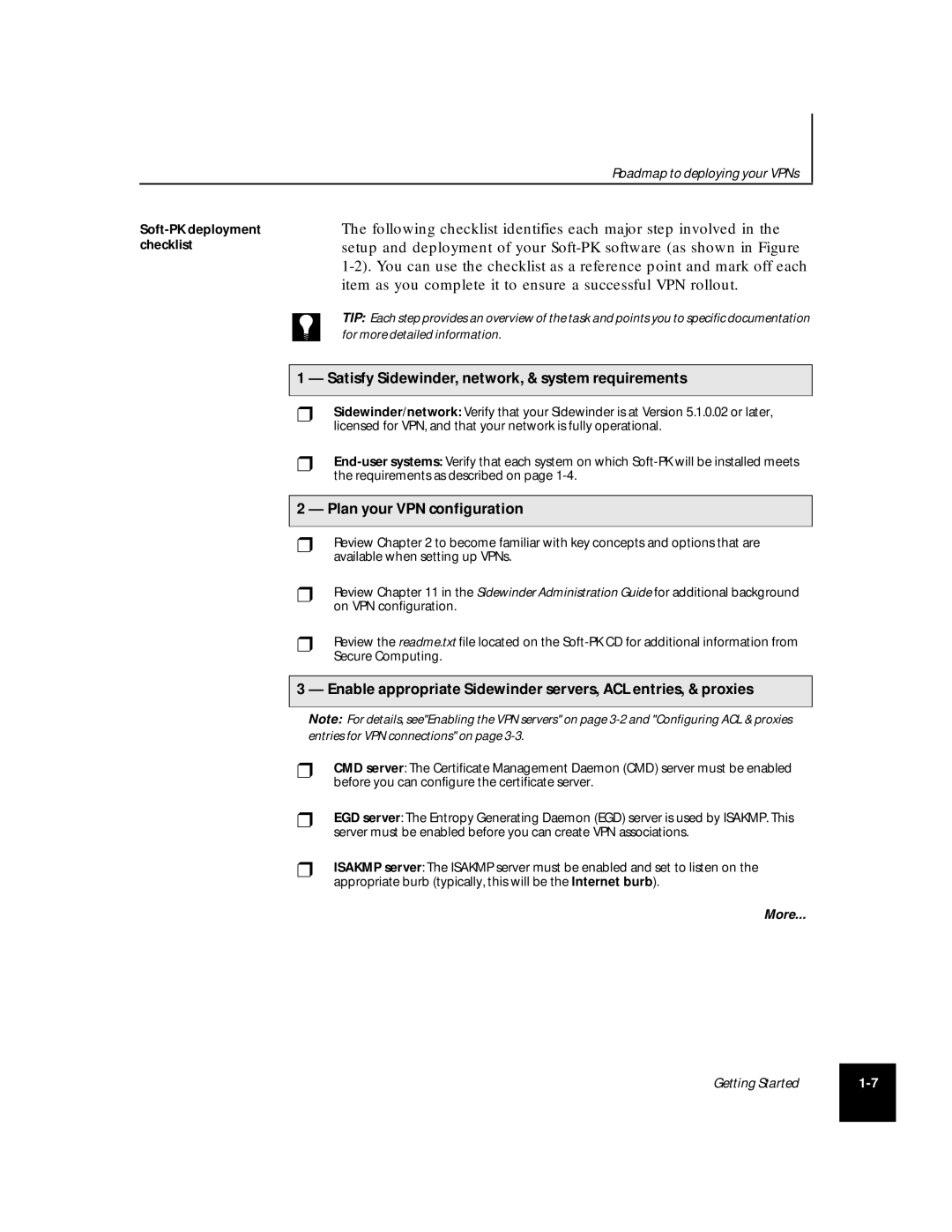
Roadmap to deploying your VPNs
The following checklist identifies each major step involved in the setup and deployment of your
TIP: Each step provides an overview of the task and points you to specific documentation
for more detailed information.
1 — Satisfy Sidewinder, network, & system requirements
❒Sidewinder/network: Verify that your Sidewinder is at Version 5.1.0.02 or later, licensed for VPN, and that your network is fully operational.
❒
2 — Plan your VPN configuration
❒Review Chapter 2 to become familiar with key concepts and options that are available when setting up VPNs.
❒Review Chapter 11 in the Sidewinder Administration Guide for additional background on VPN configuration.
❒Review the readme.txt file located on the
3 — Enable appropriate Sidewinder servers, ACL entries, & proxies
Note: For details, see"Enabling the VPN servers" on page
❒CMD server: The Certificate Management Daemon (CMD) server must be enabled before you can configure the certificate server.
❒EGD server: The Entropy Generating Daemon (EGD) server is used by ISAKMP. This server must be enabled before you can create VPN associations.
❒ISAKMP server: The ISAKMP server must be enabled and set to listen on the appropriate burb (typically, this will be the Internet burb).
More...
Getting Started | |
|
|