User Guide
10/100 Secure Network Interface Card
United States Government Legend
Contents
Installing and Configuring Data Encryption Offloads
Configuring the NIC
Running NIC Diagnostics
Installing and Connecting the NIC
Minimum Installation Requirements
Installation Overview
Safety Precautions
Preparing the NIC and the Computer
Network Environment Cable Required Maximum Cable Length
Installing and Connecting the NIC
3CR990B-97 NIC
Install without Diagnostic Program-installs the driver only
Installing the Network Driver
Verifying the Network Driver Installation
Double click Network Connections
Windows 2003 Server Driver Installation
Windows XP Driver Installation
Windows XP Driver Installation
Windows 2000 Driver Installation
Windows 2000 Driver Installation
Windows NT 4.0 Driver Installation
Click Have Disk
Verifying the Network Driver Installation
Windows 98 SE Driver Installation
Windows 98 SE Driver Installation
Novell NetWare Driver Installation
Installing the Driver in Novell NetWare Server 5.1
Installation During Novell OS Installation
Choose Select a driver
Installation with Novell Already Installed
Identifying the Slot Number
Select Save parameters and load driver
Verifying or Modifying NIC Parameters
Load ODINEB.NLM
Removing Drivers from Autoexec.ncf
Installing the Driver in Novell NetWare Server
Page
Linux 2.4 Driver Installation
Cd /tmp/3c990/3c990 make
Linux 2.4 Driver Installation
Overview
Offloading Encryption Processing
Selecting Basic or Strong Encryption Processing
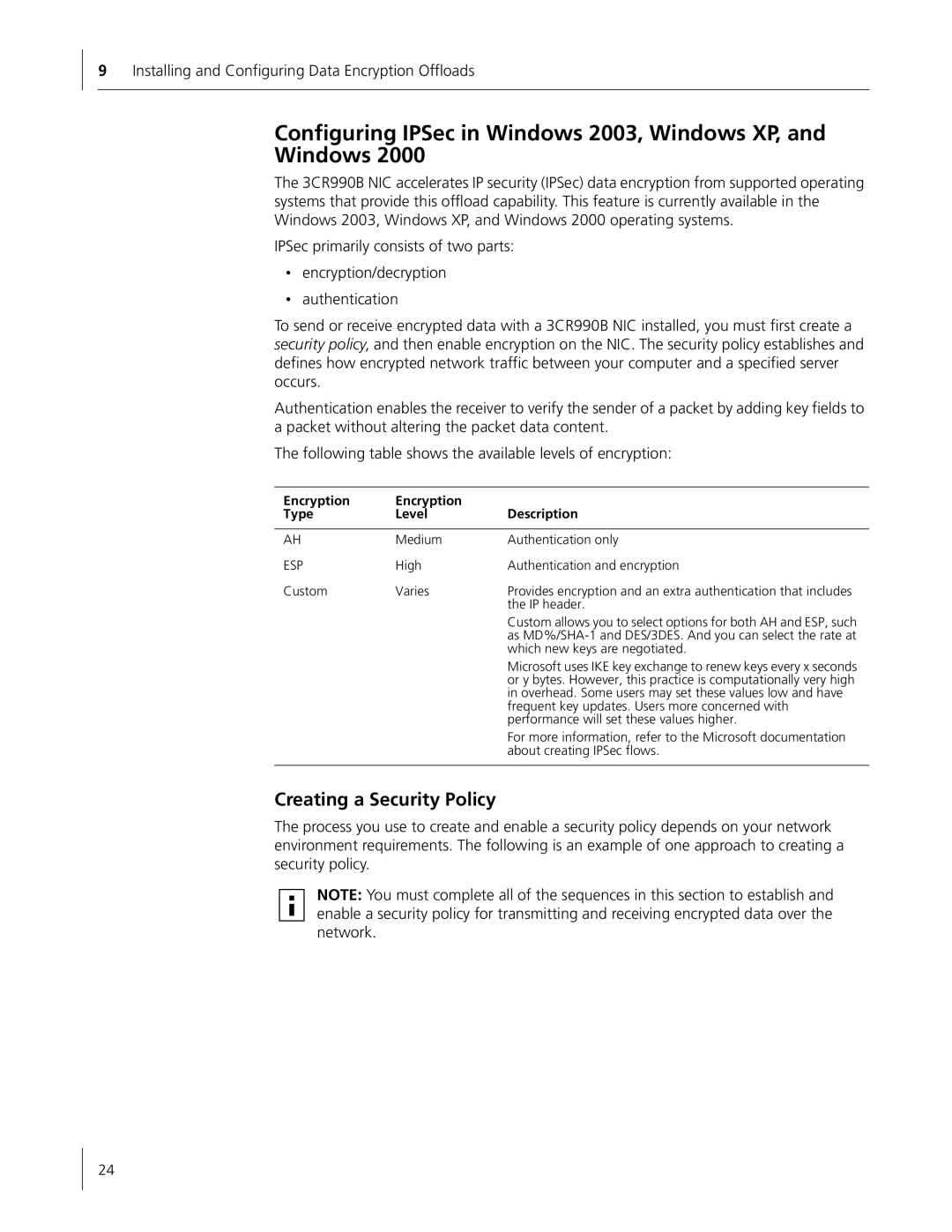
Configuring IPSec in Windows 2003, Windows XP, and Windows
Creating a Security Policy
Encryption Type Level Description
Creating the Policy
Clear the Activate the default response rule check box
Defining the Console
Select IP Security Policy Management, and then click Add
Creating a Filter
Binding the Filter
Creating the Filter Action
Disabling Encryption
Binding the Filter Action
Enabling Encryption
Select Un-assign
Installing and Configuring Data Encryption Offloads
Installing 3Com Advanced Server Features for Windows
About the Advanced Server Features
3Com DynamicAccess Advanced Server Features
Load Balancing
Failover
Server Features Using Other NICs
VLANs
Installing 3Com Advanced Server Software
Verifying the Installation
Configuring Groups and VLANs
Planning the Configuration
Working With Server Features
Number of VLANs
Creating a Group
Windows 2003, Windows XP, and Windows
Windows NT
Adding NICs to a Group
Specifying a Dedicated IP Address
Changing an IP Address
Click Configure
Creating a Vlan
Specifying Traffic Priorities
Changing the Primary NIC
Saving the Configuration
Disabling Load Balancing for a Group
Removing a NIC from a Group
Displaying NIC Properties
Troubleshooting a Load Balancing Configuration
SymptomTip
Displaying Group Properties
Double-clickNetwork Adapters
Value Offload Function Enables
Enabling Offloads
Configuring Offloads for a Group of Different NICs
Option Description Settings
Configuring the NIC
Default NIC Settings
Disabled
Configuring the NIC
All
Configuration Methods
Method Description Requirements
Changing General NIC Configuration Settings
Installing the 3Com NIC Diagnostics Program
Starting the 3Com NIC Diagnostics Program
Using the 3Com NIC Diagnostics Program
Using the 3Com DOS Configuration Program
Booting From the Network
Configuring the Managed PC Boot Agent MBA
Enabling or Disabling the Boot ROM Setting
BBS BIOS-Compatible PCs
Non-BBS BIOS-Compatible PCs
Disabling the 3Com Logo
3CR990B-97 NIC
Troubleshooting the NIC
Interpreting the NIC LEDs
State Meaning
Viewing the NIC LEDs in the Diagnostics Program
Troubleshooting Problems with the LEDs
3CR990B-FX-97 NIC
Accessing the 3Com NIC Help System
Accessing 3Com Support Databases
Accessing the 3Com Knowledgebase
Accessing Release Notes and Frequently Asked Questions
Troubleshooting the NIC Installation
Problems or Error Messages
Cleaning Up a Failed Installation
Troubleshooting the Network Connection
Tip Description
Troubleshooting Remote Wake-Up
Troubleshooting a Network Connection
Troubleshooting Hubs
RJ-45 Cabling Pinouts Copper NIC Only
Removing the Network Driver
Windows 2003, Windows XP, and Windows
Windows NT
Windows 98 SE
Removing 3Com DynamicAccess Advanced Server Features
From the Start menu, select Settings/Control Panel
NetWare
Running NIC Diagnostics
Running the 3Com DOS Diagnostics Program
Running the NIC Diagnostics Tests
Tab Description
Running the Network Test
Running the NIC Test
Click Perform NIC Test
Viewing the NIC LEDs in the 3Com Diagnostics Program
Using the 3Com Icon in the Windows System Tray
Viewing Network Statistics
Removing the 3Com NIC Diagnostics Program
Enabling the Icon
Displaying Network Statistics
Running NIC Diagnostics
Network Interface
3CR990B-97 NIC Specifications
Hardware
Standards Conformance
3CR990B-FX-97 NIC Specifications
Cabling Requirements
RJ-45 Connector Pin Assignments
Installing the 3Com DMI Agent
About the 3Com DMI Agent
System Requirements
Installing the 3Com DMI Agent
Click NIC Software Click Install 3Com DMI Agent Now
Network Management Requirements
Page
Installing the 3Com DMI Agent
Obtaining Support for your Product
Contact Us
Telephone Technical Support and Repair
Country Telephone Number Asia, Pacific Rim
Country Telephone Number
Europe, Middle East, and Africa
Latin America
Country
North America Telephone Support and Repair 1
FCC Class B Statement
Interference Handbook
MIC Class B Compliance Korea Safety Compliance Statement
FCC Declaration of Conformity