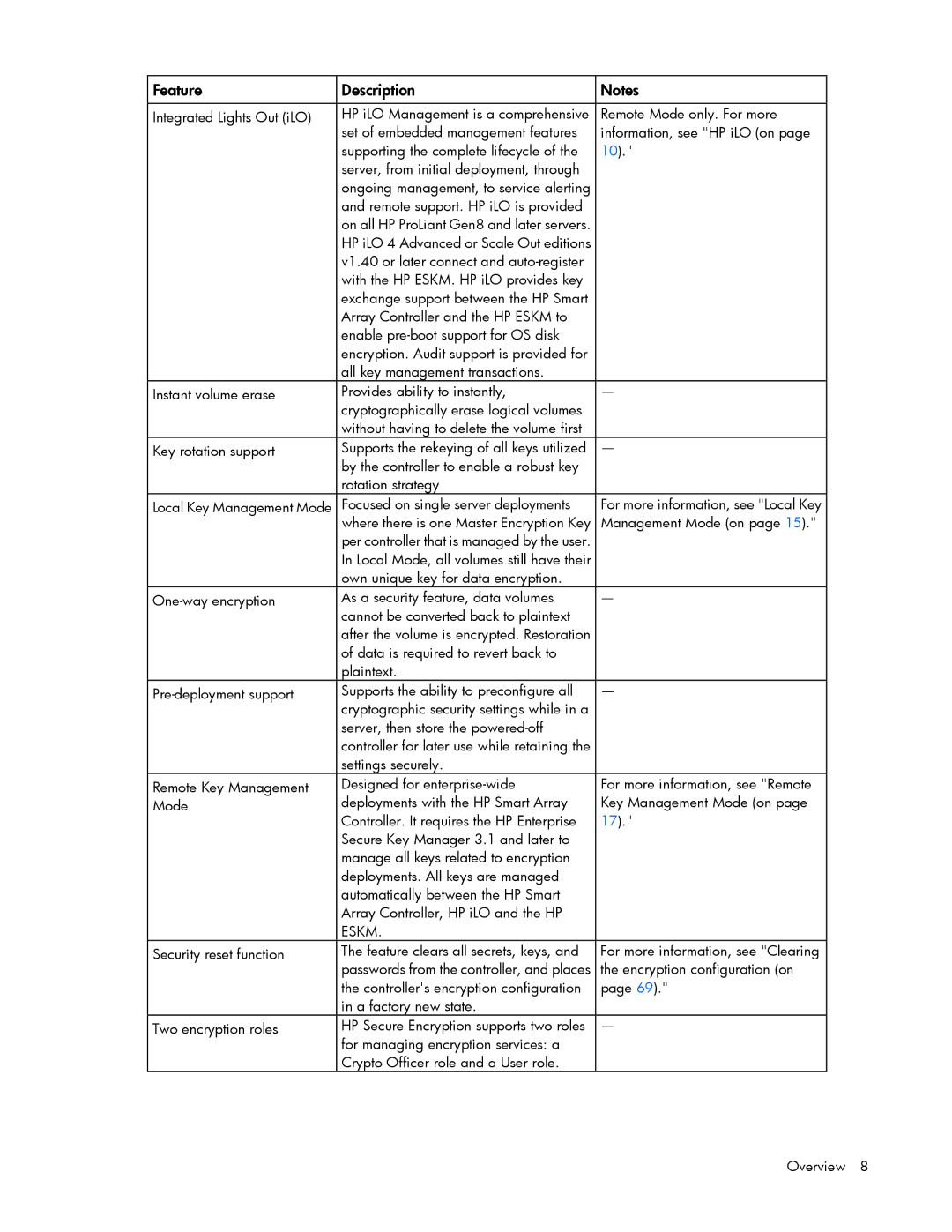
Feature | Description | Notes |
|
|
|
Integrated Lights Out (iLO) | HP iLO Management is a comprehensive | Remote Mode only. For more |
| set of embedded management features | information, see "HP iLO (on page |
| supporting the complete lifecycle of the | 10)." |
| server, from initial deployment, through |
|
| ongoing management, to service alerting |
|
| and remote support. HP iLO is provided |
|
| on all HP ProLiant Gen8 and later servers. |
|
| HP iLO 4 Advanced or Scale Out editions |
|
| v1.40 or later connect and |
|
| with the HP ESKM. HP iLO provides key |
|
| exchange support between the HP Smart |
|
| Array Controller and the HP ESKM to |
|
| enable |
|
| encryption. Audit support is provided for |
|
| all key management transactions. |
|
Instant volume erase | Provides ability to instantly, | — |
| cryptographically erase logical volumes |
|
| without having to delete the volume first |
|
Key rotation support | Supports the rekeying of all keys utilized | — |
| by the controller to enable a robust key |
|
| rotation strategy |
|
Local Key Management Mode | Focused on single server deployments | For more information, see "Local Key |
| where there is one Master Encryption Key | Management Mode (on page 15)." |
| per controller that is managed by the user. |
|
| In Local Mode, all volumes still have their |
|
| own unique key for data encryption. |
|
As a security feature, data volumes | — | |
| cannot be converted back to plaintext |
|
| after the volume is encrypted. Restoration |
|
| of data is required to revert back to |
|
| plaintext. |
|
Supports the ability to preconfigure all | — | |
| cryptographic security settings while in a |
|
| server, then store the |
|
| controller for later use while retaining the |
|
| settings securely. |
|
Remote Key Management | Designed for | For more information, see "Remote |
Mode | deployments with the HP Smart Array | Key Management Mode (on page |
| Controller. It requires the HP Enterprise | 17)." |
| Secure Key Manager 3.1 and later to |
|
| manage all keys related to encryption |
|
| deployments. All keys are managed |
|
| automatically between the HP Smart |
|
| Array Controller, HP iLO and the HP |
|
| ESKM. |
|
Security reset function | The feature clears all secrets, keys, and | For more information, see "Clearing |
| passwords from the controller, and places | the encryption configuration (on |
| the controller's encryption configuration | page 69)." |
| in a factory new state. |
|
Two encryption roles | HP Secure Encryption supports two roles | — |
| for managing encryption services: a |
|
| Crypto Officer role and a User role. |
|
Overview 8