Appendix B
Create VPN Wizard
|
| Related Topics | |||
|
| • Edit Endpoints Dialog Box, page | |||
|
| • Defining the Endpoints and Protected Networks, page | |||
|
| Field Reference | |||
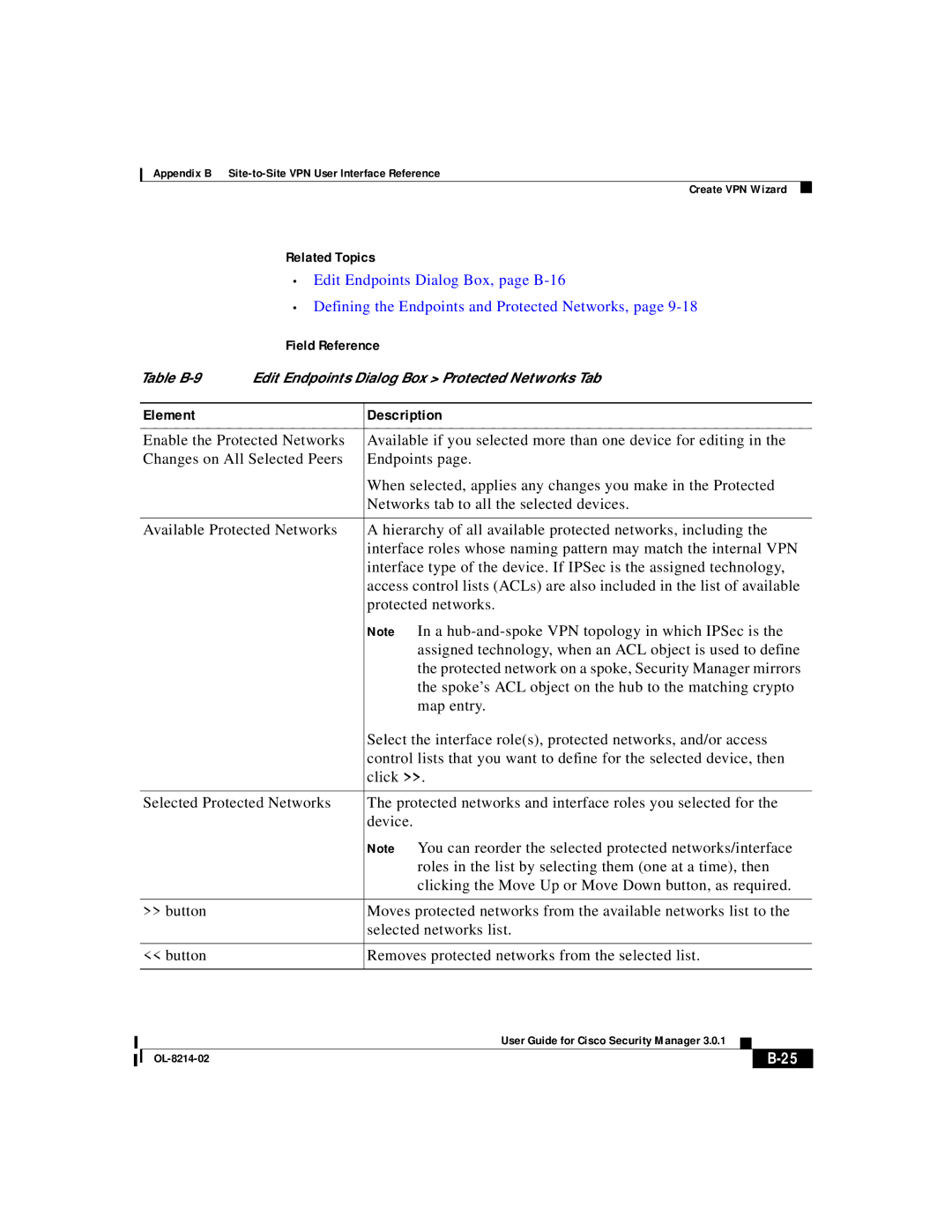
Table | Edit Endpoints Dialog Box > Protected Networks Tab | ||||
|
|
|
| ||
| Element |
| Description | ||
|
|
| |||
| Enable the Protected Networks | Available if you selected more than one device for editing in the | |||
| Changes on All Selected Peers | Endpoints page. | |||
|
|
| When selected, applies any changes you make in the Protected | ||
|
|
| Networks tab to all the selected devices. | ||
|
|
| |||
| Available Protected Networks | A hierarchy of all available protected networks, including the | |||
|
|
| interface roles whose naming pattern may match the internal VPN | ||
|
|
| interface type of the device. If IPSec is the assigned technology, | ||
|
|
| access control lists (ACLs) are also included in the list of available | ||
|
|
| protected networks. | ||
|
|
| Note In a | ||
|
|
| assigned technology, when an ACL object is used to define | ||
|
|
| the protected network on a spoke, Security Manager mirrors | ||
|
|
| the spoke’s ACL object on the hub to the matching crypto | ||
|
|
| map entry. | ||
|
|
| Select the interface role(s), protected networks, and/or access | ||
|
|
| control lists that you want to define for the selected device, then | ||
|
|
| click >>. | ||
|
|
| |||
| Selected Protected Networks | The protected networks and interface roles you selected for the | |||
|
|
| device. | ||
|
|
| Note You can reorder the selected protected networks/interface | ||
|
|
| roles in the list by selecting them (one at a time), then | ||
|
|
| clicking the Move Up or Move Down button, as required. | ||
|
|
|
| ||
| >> button |
| Moves protected networks from the available networks list to the | ||
|
|
| selected networks list. | ||
|
|
|
| ||
| << button |
| Removes protected networks from the selected list. | ||
|
|
|
|
|
|
|
|
| User Guide for Cisco Security Manager 3.0.1 |
|
|
|
|
|
| ||
|
|
|
| ||
|
|
|
| ||