Site-to-Site VPN User Interface Reference
Understanding VPN Topologies,
Working with VPN Topologies,
VPN Summary
B-3 and Peers Page, page B-7
B-37
Configuring an IKE Proposal,
Configuring High Availability in Your VPN Topology,
Configuring VRF-Aware IPSec Settings,
Configuring IPSec Proposals,
See IPSec Proposal Page, page B-39
Understanding IPSec Technologies and Policies,
Topology. See IKE Proposal Page, page B-37
B-53
See GRE Modes Page, page B-59
High Availability Page, page B-34
IPSec Tab, page B-28
Peers
Managing VPN Devices in Device View,
Create VPN Wizard
Topology. See Device Selection Page, page B-10
Name and Technology
Defining a Name and IPSec Technology,
Device Selection
Editing a VPN Topology,
B-10
Navigation Path
Page, page B-9
Endpoints
See VPN Interface Tab, page B-17
Tab, page B-24
See Edit Endpoints Dialog Box, page B-16
B-34
Edit Endpoints Dialog Box
VPN Interface Tab
Procedure for Configuring a Vpnsm or VPN SPA Blade,
Information, see Interface Roles Page, page C-126
IP Address for IPSec Termination -To enter manually the IP
More information, see Interface Roles Page, page C-126
More information, see Configuring Dialer Interfaces on
Cisco IOS Routers,
Defining VPN Services Module Vpnsm or VPN SPA Settings
Box, page B-32
VPN SPA Blade,
For more information, see Adding VPN SPA Slot Locations
Protected Networks Tab
IP Address for IPSec Termination-To enter manually the IP
Table B-9 Edit Endpoints Dialog Box Protected Networks Tab
More information, see Editing Interface Role Objects,
More information, see Editing Access Control List Objects
Fwsm Tab
Information, see Editing Network/Host Objects,
Table B-10 Edit Endpoints Dialog Box Fwsm Tab
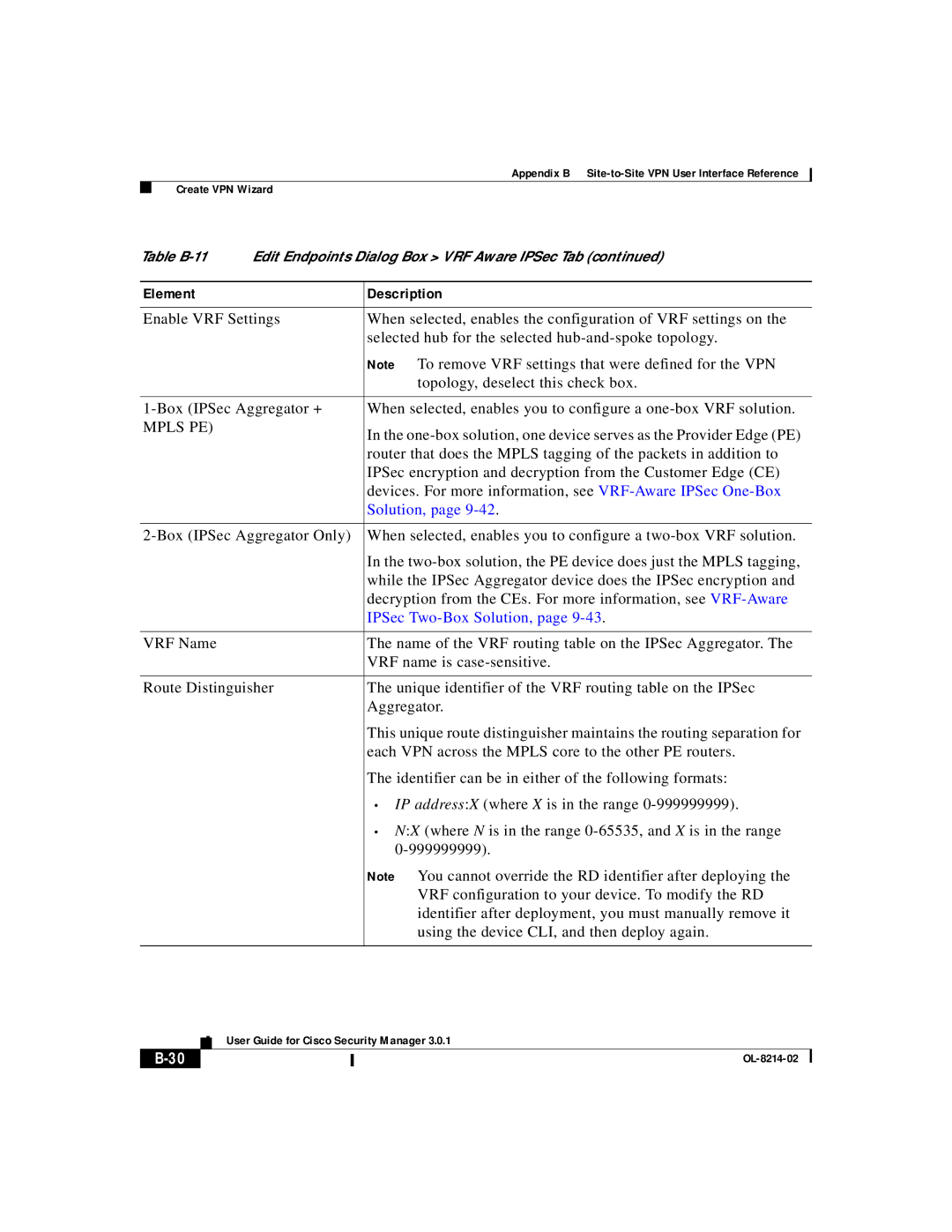
VRF Aware IPSec Tab
For more information, see Interface Roles Page, page C-126
Table B-11 Edit Endpoints Dialog Box VRF Aware IPSec Tab
Solution,
IPSec Two-Box Solution,
C-126
Routers
Dial Backup Settings Dialog Box
Summary page. See VPN Summary Page, page B-3
Table B-12 Dial Backup Settings Dialog Box
High Availability
Table B-13 Create VPN wizard High Availability
Policy configured. See VPN Summary Page, page B-3
For more information, see Enabling Stateful Failover,
Site to Site VPN Policies
IKE Proposal
Site-to-Site VPN Policies in Policy View,
Understanding Preshared Key Policies,
More information, see IKE Proposal Dialog Box, page C-123
IPSec Proposal
IKE,
C-123
Shared Site-to-Site VPN Policies in Policy View,
For more information, see About Crypto Maps,
IPSec Transform Sets Page, page C-130
For more information, see About Transform Sets,
To Use,
Element Description
VPN Global Settings
ISAKMP/IPSec Settings Tab
Configuring VPN Global Settings,
For more information, see About IKE Keepalive,
See Understanding IKE,
Appendix B Site-to-Site VPN User Interface Reference
NAT Settings Tab
VPN Global Settings Page, page B-44 Understanding NAT,
For more information, see About NAT Traversal,
NAT,
General Settings Tab
For more information, see Understanding Fragmentation
Select the required setting for the DF bit
Preshared Key
Table B-19 Preshared Key
Element Description
Negotiation Method
Public Key Infrastructure
Working with PKI Enrollment Objects,
C-140
Attributes,
FlexConfig see Working with FlexConfigs,
GRE Modes
Table B-21 GRE Modes Page GRE or GRE Dynamic IP Policy
GRE?,
OL-8214-02
Configuring Cisco IOS Router Interfaces,
OL-8214-02
Configuration of GRE,
For more information, see Prerequisites for Successful
Element Description
Preshared Key Policies,
For more information, see Configuring Cisco IOS Router
Interfaces,
Easy VPN IPSec Proposal
Understanding Easy VPN,
For more information, see Understanding NAT,
Device Access Policies,
Group Objects,
More information, see Working with AAA Server Group Objects
User Group Policy
Working with User Group Objects,
For more information, see Editing User Group Objects,
Tunnel Group Policy PIX 7.0/ASA
Tunnel Group Policy General Tab
For more information, see Working with ASA User Groups
Client Address Assignment
Tunnel Group Policy IPSec Tab
Network/Host Objects,
For more information, see Supported AAA Server Types
Tunnel Group Policy Advanced Tab
More information, see Working with Interface Role Objects
Tunnel Group Policy Client VPN Software Update Tab
Tunnel Group Policy PIX 7.0/ASA
Client Connection Characteristics
Table B-29 Easy VPN Remote Client Connection Characteristics
About Locking in Site-to-Site VPN Topologies,
Working with Site-to-Site VPN Policies,
See Site to Site VPN Policies, page B-37
For more information, see About Editing a VPN Topology
For more information, see Deleting a VPN Topology,
OL-8214-02
OL-8214-02