User’s Guide
Disclaimer
Trademarks
Table of Contents
Settings
Communications
Wireless PAN Wpan Communications with Bluetooth
Applications
Dolphin Mobile Base
Customer Support
Dolphin 9500 Series User’s Guide
Ergonomics
Introduction
Laser Safety Label Text Embedded Safety Information Text
Required Safety Labels
Locations
Dolphin
Dolphin 9500 Series Batch Terminal
Parameter Specification
Dolphin 9500 Series Wlan or Wpan Radio
802.11b
Bluetooth
Dolphin 9500 Wwan Radio
802.11b and Bluetooth
GSM and 802.11b
GSM, Bluetooth, and 802.11b
GSM and Bluetooth
FCC Compliance
Dolphin 9500 Series Batch Terminal
Canadian Compliance
RF, Regulatory, and Safety Agency Approvals for GSM
Dolphin 9500 Terminal GSM R&TTE Compliance Statement
Parameter
Microwaves
Care and Cleaning of Dolphin 9500 Series Terminals
For European Community Users
Waste Electrical and Electronic Equipment Information
Overview
Getting Started
Dolphin 9500 Series Models and Options
Dolphin 9500 Series Terminals
Dolphin 9500 Series Peripherals
Dolphin 9500 Series Accessories
Dolphin 9500/9550 Terminals
Image Engine Options and Specifications
Dolphin 9501/9551 Terminals
Bar Code Symbologies Supported
Unpack the Carton and Verify its Contents
Using the Dolphin Terminal for the First Time
Before Initial Use
Charging with Dolphin Peripherals
Time to Charge
Align the Screen
Verify Decoding
Verify Imaging
Sample Bar Codes
Tap Start Demos Scan Demo
Suspend Mode
Resetting the Terminal
Soft Reset Warm Boot
Hard Reset Cold Boot
Rev C
Wireless Radio Options
System Features
Hardware Overview
Processor
Front Panel Features
Display
LEDs
Scan Key
Navigation Keys
Dolphin
Back Panel Features
Image Engine Window
Battery/Battery Well
Speaker
Hand Strap Attachment
Pistol Grip Handle
Scan Trigger
Wrist Lanyard Fastener
Stylus
Rubber Bumpers
IrDA Port
Side Panel Features
SD Memory
Audio Jack
Mechanical Connector
Bottom Panel Features
Powering Out
Dolphin 9501 and Dolphin
Internal Backup Battery
Main Battery Pack
Managing Battery Power
Batteries
Setting Critical and Low Battery Points
Default Critical and Low Battery Points
Status Notifications
Guidelines for Battery Use and Disposal
Checking Battery Power
Storing Batteries
Dolphin 9500 Series Technical Specifications
Temperature
Weight
Temperature Humidity
Resistance Power
Entering Data
Using Dolphin Mobile Computers
Touch Screen
Today Screen
Command Bar
Navigation Bar and Start Menu
Selecting Programs
Pop-Up Menus
Decoding
Using the Image Engine
To Decode a Bar Code
Full-Area Imaging
Dolphin 9501/9551 Scanning Position Options
Dolphin 9500/9550 Scanning Position Options
Taking an Image
Capturing Images
High-Vis Aiming Pattern
Uploading Images
Using the Keyboards
Using the Navigation Keys
Using the Function Keys
Name & Key Function Shift
Using the Modifier Keys
Ctrl and ALT
Blue and Red
Alpha Lock Key Alpha
Key Numeric/Alpha Keyboard
Number Lock NUM
Key Alpha/Numeric Keyboard
Key Combinations
Key Full Alpha/Numeric Keyboard
Keyboard
Adjusting the Backlight
Display
Communication Options
Wireless Radios
IrDA Port
Software Communication Programs
Using the Radio Manager
Radio Driver Installation
Radio Options
Radio Combinations
Radio Manager Window
To Disable Radios
Radio Modes
Using the SIP Keyboard
Using the Soft Input Panel SIP
Using the Letter Recognizer
Using the Block Recognizer
Input Panel Options
Selecting Text
Input Method tab Word Completion tab Options tab
Drawing on the Screen
Writing on the Screen
To Select Writing
Selecting a Drawing
Status Icons
Status Icon Meaning
Notifications
Finding and Organizing Information
Personal Tab System Tab Connections Tab
Settings
System
Connections
Personal Tab
Buttons
To Enable HotKeys
Button Assignments
Available Applications
Headset Volume
Mic Volume
Headset Control
Stereo headphone
Using File Explorer
Using System Settings
Using ActiveSync on the Desktop
Tap Start Settings Personal tab Menus Start Menu tab
Tap ActiveSync Explore
About
System Tab
Backlight
ClearType Tuner
Main Tab
CPU Speed
Total storage card
Storage Card Tab
Storage Card
Battery Tab
Power
Links at the Bottom of the Memory Tabs
Running Programs Tab
Wireless Tab
Regional Settings
Advanced Tab
Options below the tabs
Rev C
Tap the Remove Programs icon
Remove Programs
Alignment Tab
Screen
ClearType Tab
Default Font Size Largest Font Size
UPhone Settings
Text Size Tab
Creating a Wireless Network Connection
Zero-Config Wi-Fi
Connections Tab
Server-Assigned IP Addresses
Opening the Connections Manager
Tap Start Settings Connections tab Connections Task tab
Creating an External Modem Connection to an ISP
Task Tab
Enter a name for the connection, such as My Connection
Port Settings Tab
Advanced Settings
General Tab
TCP/IP Tab
Creating an External Modem Connection to Your Work
Connecting to Your ISP
Establishing Exceptions for Work URLs
Servers Tab
Tap Start Settings Connections tab Connections
Setting up a Proxy Server Connection for Work Connections
Setting Up a VPN Connection for Work Connections
Connecting to a VPN Server
Establishing Dialing Rules
Dolphin 9500 Series User’s Guide Rev C
Configuring Network Cards
Connecting
Using ActiveSync
Installing Additional Software
Communications
Requirements
Setting Up Your Desktop Computer
Synchronizing from Your Desktop Computer
Synchronizing from the Terminal
If the File is an Installer
Adding Programs to the Terminal Using ActiveSync
Exploring Your Terminal from the Desktop Computer
If the File is Not an Installer
Verify That the IrDA Port is Enabled
Using Infrared
IrDA Port Location on the Terminal
Troubleshooting
Verify That Beam Settings Are Set to Receive
Sending Information
Receiving Information
Dolphin 9500 Series User’s Guide Rev C
Adding Programs Directly from the Internet
Using an ISP
Configuration Utilities
Wireless LAN Wlan Communications with 802.11b
802.11b Wireless Security Supplement
Enabling the 802.11b Radio Driver
Tap Start Settings System tab 802.11b Settings
802.11b Settings
Status Icons
Icon This icon means…
Status Tab
Config Tab
To Add an Active Ssid to the Preferred Profile Table
To Create a New Profile
Field Description Authentication
Authentication Tab
Enable
Algorithm
Preamble Mode
Field Description Power Save Mode
To Delete a Profile
Advanced Tab
Field Description Defaults
Using the Status Icon
802.11b Settings in the future
About Tab
Rev C
Required Network Configuration Information Worksheets
802.11b Wireless Security Supplement
Platforms Supported
802.1X Supplicant Protocol Support
Leap Worksheet
MD5 Worksheet
TLS/SmartCard Worksheet
Ttls Worksheet
Peap Worksheet
Opening the Client
Icon Indicators
Gray
Orange
Port Status Icon
Main Screen
Client Menu
Menu Item Tapping this item… Close
View Menu
Install Protocol
Exit
Status Bar
Help Menu
Menu Item Tapping this item…
Menu Item Description Enable
Configuring the Client
Disable
Port Menu
Client Configuration Area
Configuration Screens
Accessing the Client Configuration Area
On this tab You…
Field Description Profile
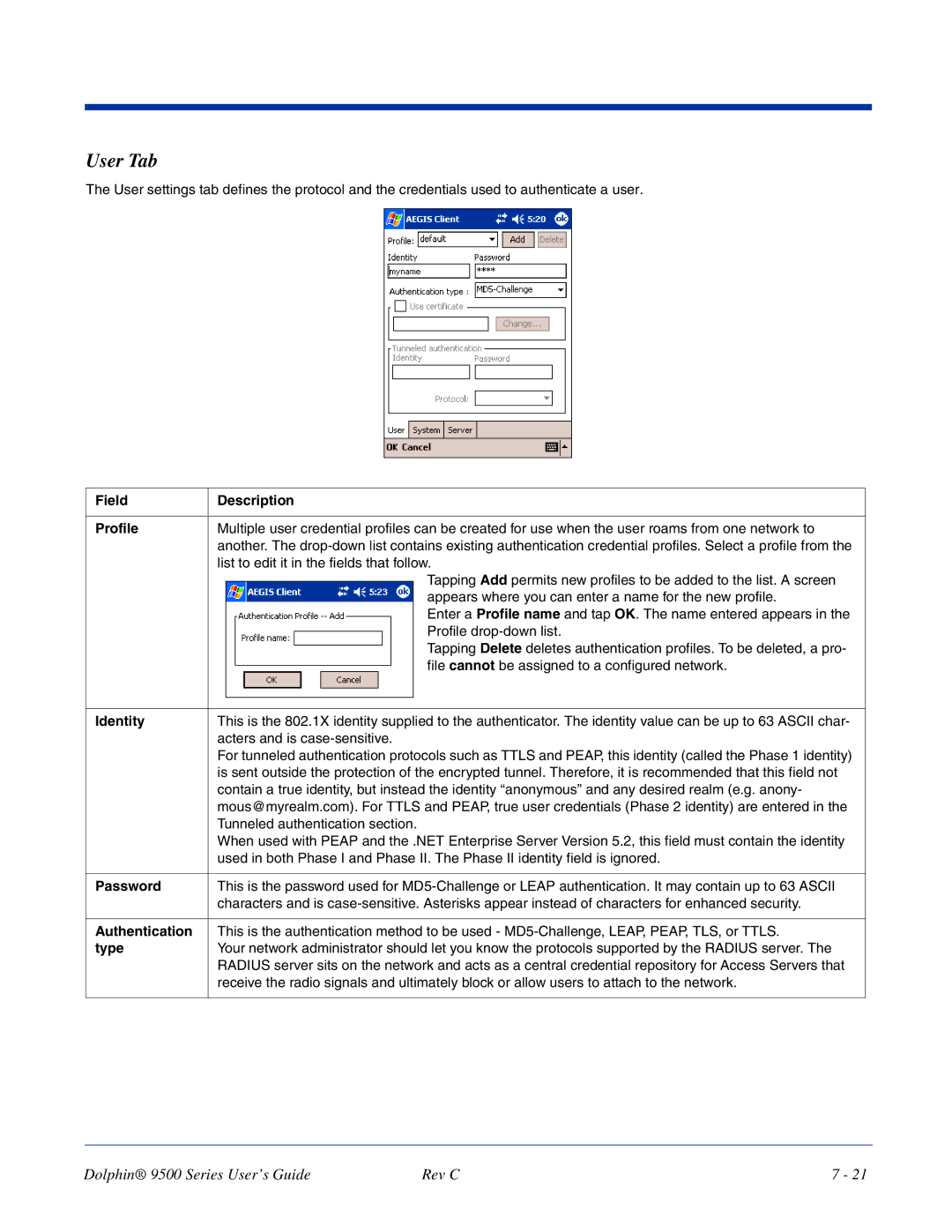
User Tab
Identity
Field Description Use certificate
Tunneled authentication area
Protocol
System Tab
Server Tab
Port Settings Area
Wireless Networks Tab
Protocol Tab
Field Description Protocol Settings
Display EAP
Renew IP address
Profile Info Tab
Adding a Wireless Network Configuration
WEP Mgmt Tab
Field Description WPA Mode
WPA Settings Tab
Logging
PSK pass-phrase
Installing Certificates
Installing Certificates with CertAdd
Advice and Workarounds
Select Peer-to-Peer Group ad hoc mode and Do active scan
Key to authenticate with AP
How 802.1X Works
Typical Message Exchange Using MD5 or TLS
Central User Administration
Typical Message Exchange Using Ttls and Peap
Benefits
Dynamic Session Specific Wireless Encryption Keys
Relative Merits of Authentication Protocols
Cisco Leap
Additional Advantages of Ttls and Peap
Differences Between Protocols
Rev C
Enabling the Bluetooth Radio
Wireless PAN Wpan Communications with Bluetooth
Setting Up Your Bluetooth Card
Assign COM Ports
Discover Bluetooth Devices
Bond With Discovered Devices
Rev C
View Device Properties
Set Up Your Favorite Device
Tap Tools My Favorites
Delete a Device From the Folder
Change Views
Turn Radio Transmitter ON/OFF
Bluetooth ActiveSync
Rev C
Bluetooth LAN Access
Rev C
Exchange Business Cards
Obex
Send a Contact
Send a File
Prepare for File Transfer
Browse Remote Device
Dolphin 9500 Series User’s Guide Rev C
Create a Folder
Send/Receive Files or Folders
Refresh Remote View
Delete Files or Folders
Connect/Disconnect
Tap Device Connect
Enable File Sharing
Using the Dialer
Exit Bluetooth File Explorer
Receive Contact or File
Tap Start Settings System tab Dialer
Using the Dialer
Assign a Dialing Prefix
Tap Start Contacts
Ericcson, Nokia 6210, NTT DoCoMo, Sony Phones
Get Connected Wizard
Motorola Timeport 270C, Nokia 3650/6310/7650/8910/8910i
Accept
Dial Up Connection
Automatic Connections for Motorola Timeport 270C
Uncheck Wait for dial tone before dialing. Tap Finish
Automatic Connections for Nokia 3650/7650
Automatic Connections for Nokia 6310/8910/8910i
Enabling the GSM/GPRS Radio
Wireless WAN Wwan Communications with GSM/GPRS
Tri-Band Antenna
Capabilities
To Install a SIM Card
SIM Card Installation
SIM Card Requirements
Audio Modes
Volume Control
Keyboard Combinations for Calls
Handset
Accessing uPhone
Using uPhone
Navigation Bar Icons
Icons and Bubble Messages
Tap Call Answerphone to dial
Making a Call
Using the Dialler
Entering a Phone Number
Sending a Call
Answering a Call
Receiving a Call
Rejecting a Call
Call Waiting
Call Waiting
Ending a Call
Placing the Current Call on Hold
Making Conference Calls
Touchtones
Dialler Menus
Tools Menu
Phonebook
Settings Menu
Speakerphone
Mic mute
Tap Start Settings Personal tab Ringtones icon or
Ringtone Configuration
WAV Files
Previewing Tones
Charging
Ussd
Tap Start Programs uPhone Call Log or
Call Log
Dialed
Exit Closes the Call Log
Accessing uPhone Configuration
UPhone Configuration
Tap Start Settings System tab uPhone icon
Tab Windows
Network Tab
General Tab
Not Diverted
Divert Tab
Card can be made
Bar Tab
All outgoing calls Bar all outgoing calls
Not barred
Request Delivery Reports
Messaging Tab
Opening the SMS Manager
SMS Manager
Inbox
Tap Start Programs uPhone SMS Manager, or
Outbox Folder
Sent Folder
Sending an SMS Message
Edit Menu
Icons at the Top of the Message Screen
Icon Description
Select All
Configuring the Gprs Connection
Gprs Settings
Service Provider Information
No ActiveSync
Tap Manage existing connections
Dolphin 9500 Series User’s Guide Rev C
Rev C
Calendar
Applications
To Create an Appointment
Creating Meeting Requests
Using the Summary Screen
To Schedule a Meeting
Contacts
To Create a Contact
To Search for Contacts
Tasks
To Create a Task
To Create a Note
Inbox
Synchronizing E-mail Messages
Using the Message List
Connecting Directly to an E-mail Server
Receiving Messages
Managing E-mail Messages and Folders
Composing Messages
ActiveSync
Pocket Internet Explorer
Accessing Pocket Internet Explorer
Browse the Internet on Your Terminal
Mobile Favorites Folder
View Options
Creating and Synchronizing Mobile Favorites
View Mobile Favorites and Channels on the Terminal
Using AvantGo Channels
To Sign Up for AvantGo
Tap the AvantGo Channels link
Pocket Word
Using Pocket Word
Creating a Word File
Drawing Mode
Typing Mode
Creating an Excel File
Pocket Excel
Tips for Working in Pocket Excel
Windows Media Player for Pocket PC
MSN Messenger
Setting Up an Account
Dolphin 9500 Series User’s Guide Rev C
To begin, tap Start Programs Pictures
Pictures
Supported Bar Code Symbologies
Laser Engine Specifications
Dolphin 9501 and Dolphin
Aiming Options
Keyboard Options
Peripherals and Accessories
Dolphin 9501 Side Panel
Dolphin 9501 Hardware
Dolphin 9501 Back Panel
Dolphin 9501 Hand Strap and Stylus
Dolphin 9551 Side Panel
Dolphin 9551 Hardware
Dolphin 9551 Back Panel
Rev C
Communications
Dolphin HomeBase
Convenient Storage
Capacity
AUX Battery LED
Auxiliary Battery Well
Dolphin HomeBase Parts and Functions
Front Panel
DC Power Jack
If using the serial port This color Means… Red
Rear Panel
USB Port
HomeBase Serial Connector
Powering the HomeBase
To Power a Terminal and Charge its Main Battery
Charging the Main Battery
Charging a Spare Battery in the Auxiliary Battery Well
To Install the HomeBase Using USB
Setting up the HomeBase for USB Communication
Communications
Equipment Requirements
Setting up the Terminal for ActiveSync Communications
Connecting the Cables
Setting up the HomeBase for RS-232 Communications
Setting up the Terminal for ActiveSync Communications
Verifying Communication
Communicating with the Dolphin Terminal
Verifying Data Transfer
Desk Mounting
Mounting the HomeBase
Wall Mounting
Mobile Base holds one terminal
Dolphin Mobile Base
Mounting Brackets
Mobile Base Parts and Functions
Comm LED color Indicates that… Red
Orange Data is being sent at high data rates
Bottom Panel
Power Supply Connector
RS-232 Communications Port
Charging the Dolphin Terminal
Powering the Dolphin Terminal
Mounting the Mobile Base
Installing the Dolphin Mobile Base
Back Panel and Brackets
Back Panel
Brackets
Powering the Dolphin Mobile Base
Connecting the Cables
Setting the Mobile Base Up for Communications
RS-232 Pin Configuration Mobile Base /Host Port
Modem DB25
Configuring the Terminal for ActiveSync Communications
Mobile Base Serial Connector
Dolphin 9500 Series User’s Guide Rev C
Rev C
Dolphin ChargeBase Parts and Functions
Dolphin ChargeBase
Terminal Wells
Dock LED
Back Panel
Power Supply
Charge LEDs
Inserting and Removing Terminals
Supplying Power to the ChargeBase
Mounting the ChargeBase
Charging Terminals in the ChargeBase
Using the DIN Rail
Using the Wall Mount Kit
Dolphin 9500 Series User’s Guide Rev C
Rev C
Compatibility
Dolphin QuadCharger
Charging Process
Top Panel
Dolphin QuadCharger Parts and Functions
Power Switch
Supplying Power to the QuadCharger
Charging Batteries in the QuadCharger
Inserting and Removing Battery Packs
Recommendations
To Analyze a Battery
Using the Battery Analyzer
Mounting the QuadCharger
Following graphic displays how mount a QuadCharger to a wall
Problem Issue
Troubleshooting
Customer Support
Product Service and Repair
Technical Assistance
Online Product Service and Repair Assistance
Online Technical Assistance
North America/Canada
How to Extend Your Warranty
Limited Warranty
Rev C
General Windows Keyboard Shortcuts
Keyboard Combinations
Press these keys To…
Blue Key Combinations
Key Alpha/Numeric Keyboard
Key Combination Function/Special Character
Num Lock Key Combinations
Red Key Combinations
Key/Key Combination Function/Special Character
Key Numeric/Alpha Keyboard
Alpha + SFT +
Alpha Mode Key Combinations
Key Full Alpha/Numeric
Red Key Combinations
SFT Key Combinations
Com Port Assignment Table
Page
Hand Held Products, Inc