Wireless-G ADSL Gateway with 2 Phone Ports
Remote Security Gateway. The Remote Security Gateway is the VPN device, such as a second VPN Gateway, on the remote end of the VPN tunnel. Enter the IP Address or Domain of the VPN device at the other end of the tunnel. The remote VPN device can be another VPN Gateway, a VPN Server, or a computer with VPN client software that supports IPSec. The IP Address may either be static (permanent) or dynamic (changing), depending on the settings of the remote VPN device. Make sure that you have entered the IP Address correctly, or the connection cannot be made. Remember, this is NOT the IP Address of the local VPN Gateway, but the IP Address of the remote VPN Gateway or device with which you wish to communicate. If you enter an IP address, only the specific IP Address will be able to acess the tunnel. If you select Any, any IP Address can access the tunnel.
•Encryption. Using Encryption also helps make your connection more secure. There are two different types of encryption: DES or 3DES (3DES is recommended because it is more secure). You may choose either of these, but it must be the same type of encryption that is being used by the VPN device at the other end of the tunnel. Or, you may choose not to encrypt by selecting Disable. DES is selected by default.
•Authentication. Authentication acts as another level of security. There are two types of authentication: MD5 and SHA (SHA is recommended because it is more secure). As with encryption, either of these may be selected, if the VPN device at the other end of the tunnel is using the same type of authentication. Or, both ends of the tunnel may choose to Disable authentication. In the Manual Key Management screen, MD5 (the default) has been selected.
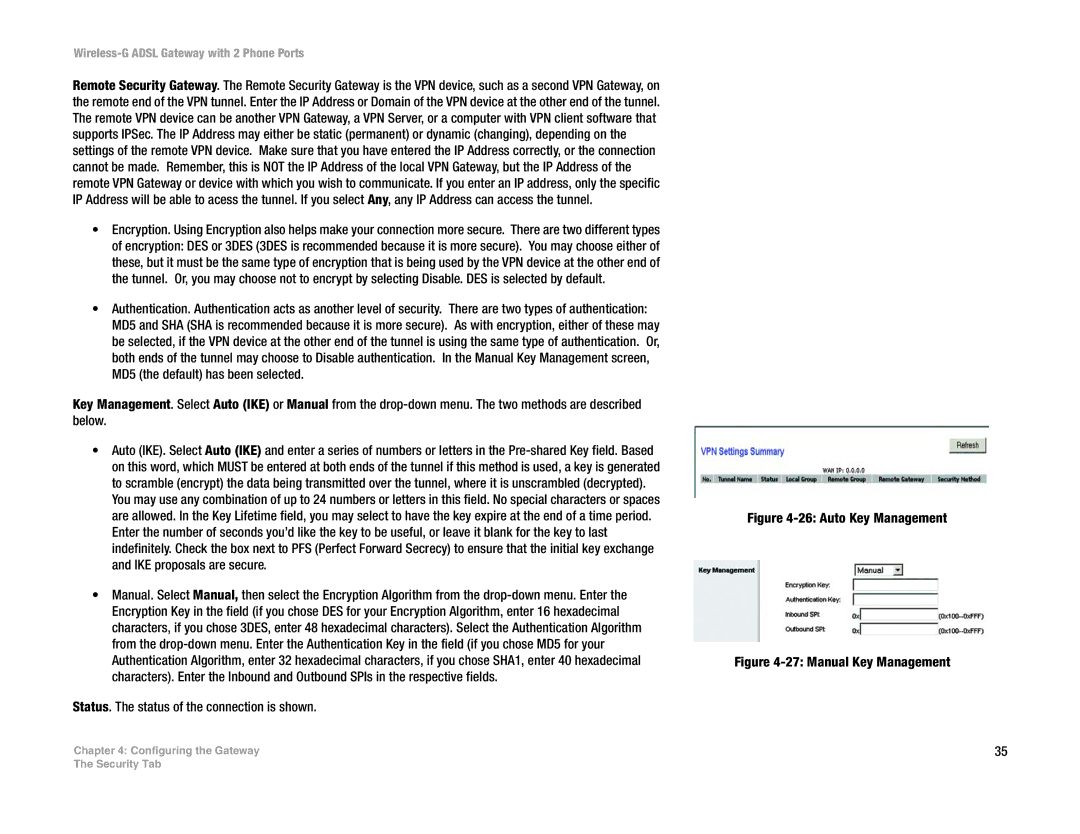
Key Management. Select Auto (IKE) or Manual from the
•Auto (IKE). Select Auto (IKE) and enter a series of numbers or letters in the
•Manual. Select Manual, then select the Encryption Algorithm from the
Status. The status of the connection is shown.
Chapter 4: Configuring the Gateway
Figure 4-26: Auto Key Management
Figure 4-27: Manual Key Management
35
The Security Tab