Filters and QoS Configuration for ERS 5500 |
|
|
Technical Configuration Guide | v2.0 |
|
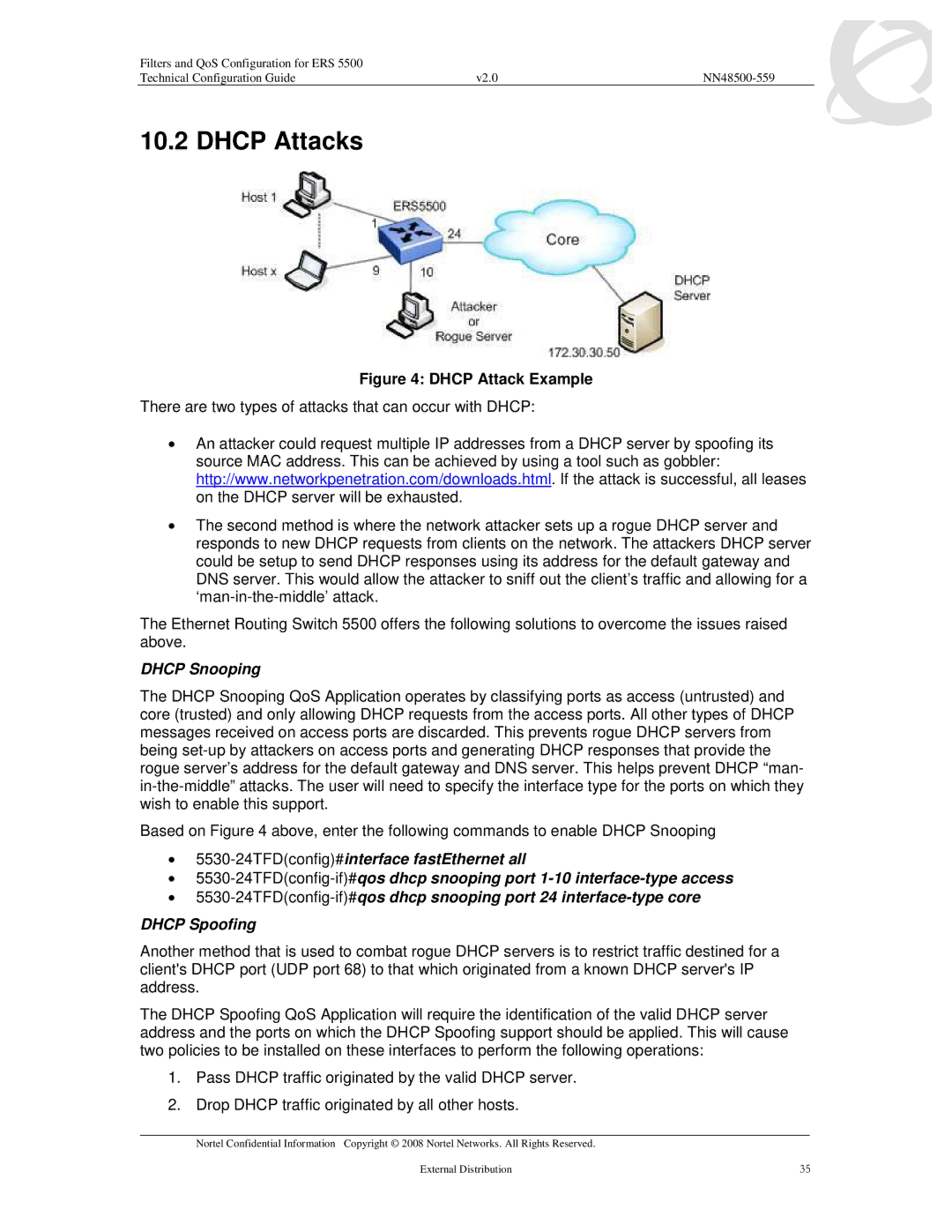
10.2 DHCP Attacks
Figure 4: DHCP Attack Example
There are two types of attacks that can occur with DHCP:
•An attacker could request multiple IP addresses from a DHCP server by spoofing its source MAC address. This can be achieved by using a tool such as gobbler: http://www.networkpenetration.com/downloads.html. If the attack is successful, all leases on the DHCP server will be exhausted.
•The second method is where the network attacker sets up a rogue DHCP server and responds to new DHCP requests from clients on the network. The attackers DHCP server could be setup to send DHCP responses using its address for the default gateway and DNS server. This would allow the attacker to sniff out the client’s traffic and allowing for a
The Ethernet Routing Switch 5500 offers the following solutions to overcome the issues raised above.
DHCP Snooping
The DHCP Snooping QoS Application operates by classifying ports as access (untrusted) and core (trusted) and only allowing DHCP requests from the access ports. All other types of DHCP messages received on access ports are discarded. This prevents rogue DHCP servers from being
Based on Figure 4 above, enter the following commands to enable DHCP Snooping
•
•
•
DHCP Spoofing
Another method that is used to combat rogue DHCP servers is to restrict traffic destined for a client's DHCP port (UDP port 68) to that which originated from a known DHCP server's IP address.
The DHCP Spoofing QoS Application will require the identification of the valid DHCP server address and the ports on which the DHCP Spoofing support should be applied. This will cause two policies to be installed on these interfaces to perform the following operations:
1.Pass DHCP traffic originated by the valid DHCP server.
2.Drop DHCP traffic originated by all other hosts.
___________________________________________________________________________________________________________________________
Nortel Confidential Information Copyright © 2008 Nortel Networks. All Rights Reserved. |
|
External Distribution | 35 |