Filters and QoS Configuration for ERS 5500 | | |
Technical Configuration Guide | v2.0 | NN48500-559 |
10.1 ARP Spoofing
Figure 3: Arp Spoofing Example
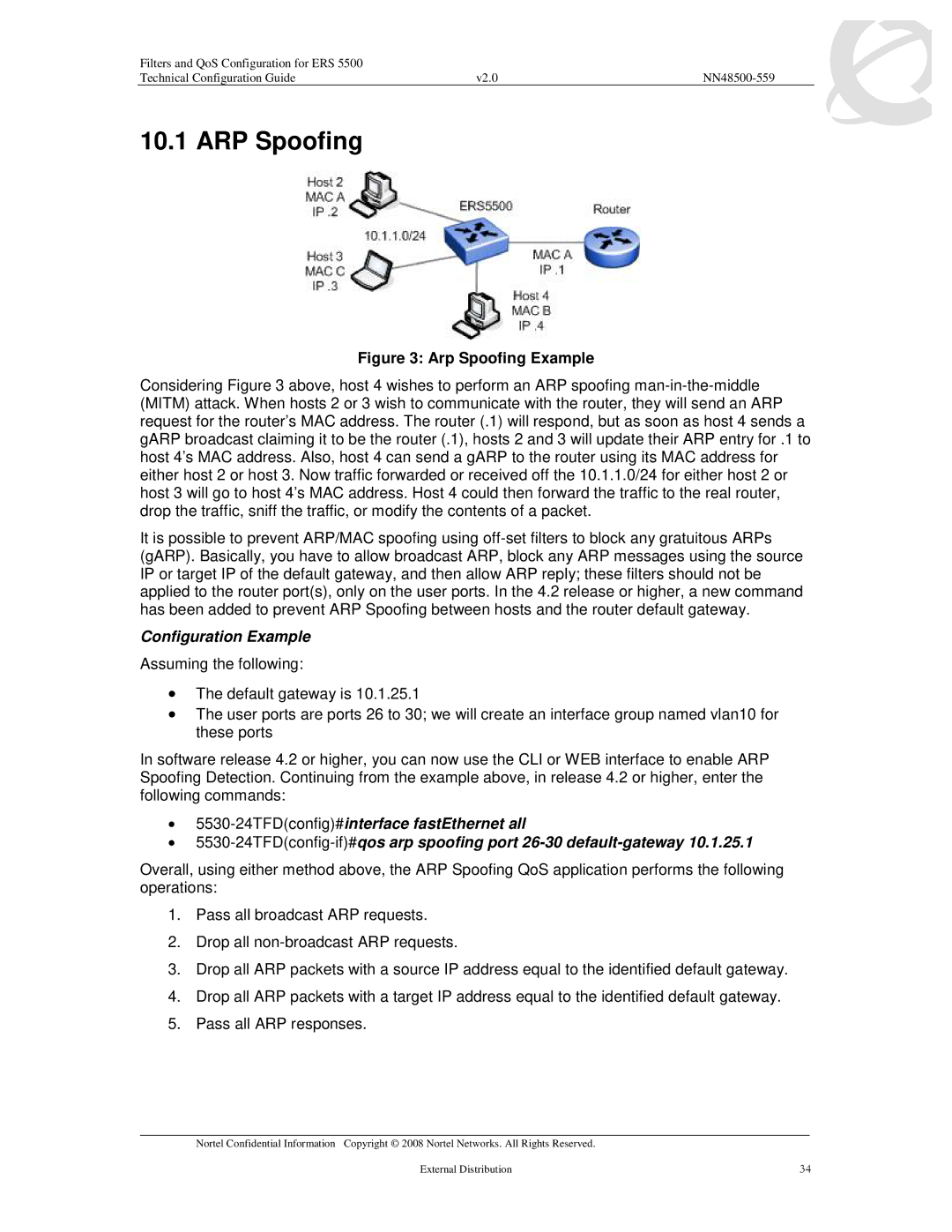
Considering Figure 3 above, host 4 wishes to perform an ARP spoofing man-in-the-middle (MITM) attack. When hosts 2 or 3 wish to communicate with the router, they will send an ARP request for the router’s MAC address. The router (.1) will respond, but as soon as host 4 sends a gARP broadcast claiming it to be the router (.1), hosts 2 and 3 will update their ARP entry for .1 to host 4’s MAC address. Also, host 4 can send a gARP to the router using its MAC address for either host 2 or host 3. Now traffic forwarded or received off the 10.1.1.0/24 for either host 2 or host 3 will go to host 4’s MAC address. Host 4 could then forward the traffic to the real router, drop the traffic, sniff the traffic, or modify the contents of a packet.
It is possible to prevent ARP/MAC spoofing using off-set filters to block any gratuitous ARPs (gARP). Basically, you have to allow broadcast ARP, block any ARP messages using the source IP or target IP of the default gateway, and then allow ARP reply; these filters should not be applied to the router port(s), only on the user ports. In the 4.2 release or higher, a new command has been added to prevent ARP Spoofing between hosts and the router default gateway.
Configuration Example
Assuming the following:
•The default gateway is 10.1.25.1
•The user ports are ports 26 to 30; we will create an interface group named vlan10 for these ports
In software release 4.2 or higher, you can now use the CLI or WEB interface to enable ARP Spoofing Detection. Continuing from the example above, in release 4.2 or higher, enter the following commands:
•5530-24TFD(config)#interface fastEthernet all
•5530-24TFD(config-if)#qos arp spoofing port 26-30 default-gateway 10.1.25.1
Overall, using either method above, the ARP Spoofing QoS application performs the following operations:
1.Pass all broadcast ARP requests.
2.Drop all non-broadcast ARP requests.
3.Drop all ARP packets with a source IP address equal to the identified default gateway.
4.Drop all ARP packets with a target IP address equal to the identified default gateway.
5.Pass all ARP responses.
___________________________________________________________________________________________________________________________
Nortel Confidential Information Copyright © 2008 Nortel Networks. All Rights Reserved. | |
External Distribution | 34 |