A
3 – Planning Fabric Security
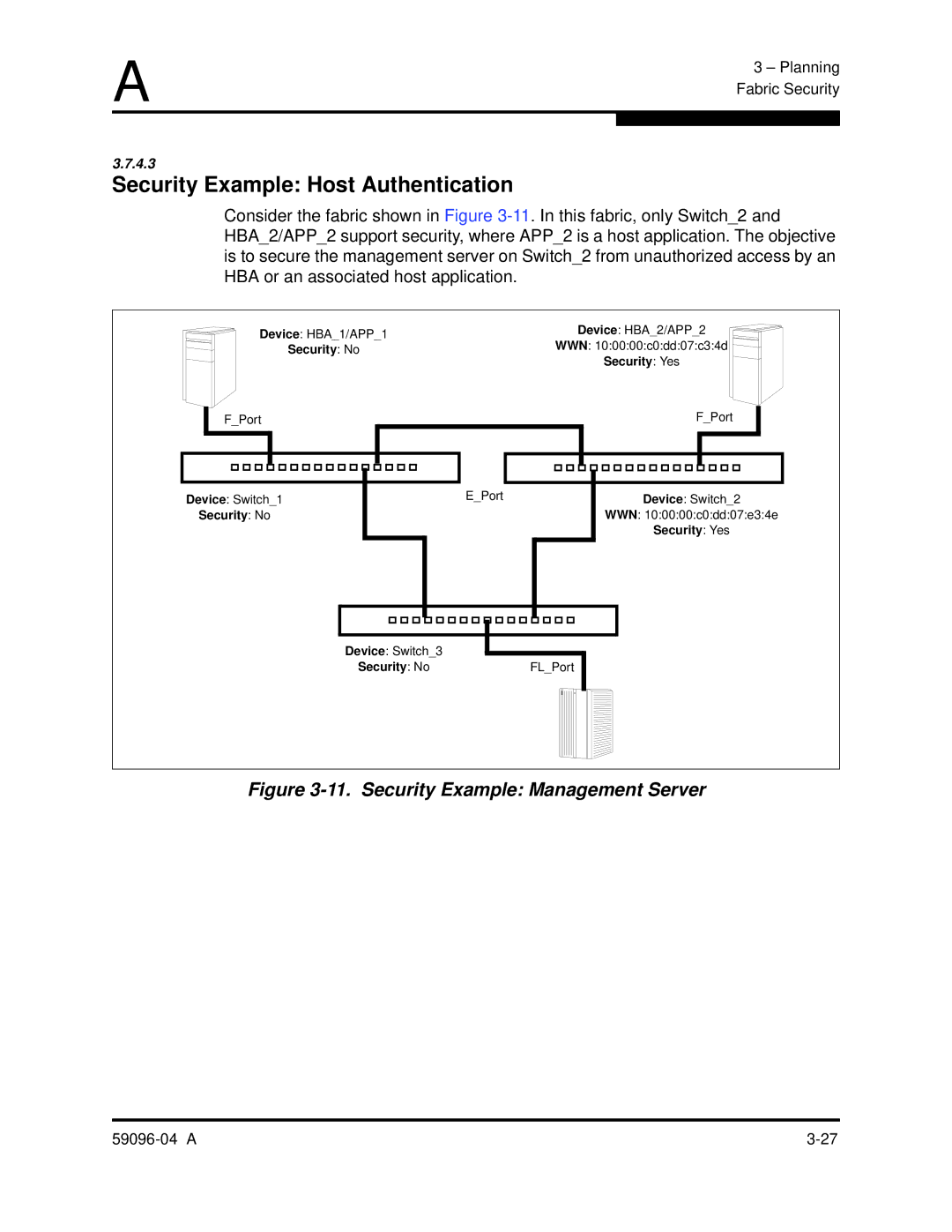
3.7.4.3
Security Example: Host Authentication
Consider the fabric shown in Figure
HBA_2/APP_2 support security, where APP_2 is a host application. The objective is to secure the management server on Switch_2 from unauthorized access by an HBA or an associated host application.
Device: HBA_1/APP_1 | Device: HBA_2/APP_2 |
Security: No | WWN: 10:00:00:c0:dd:07:c3:4d |
| Security: Yes |
F_Port |
Device: Switch_1
Security: No
E_Port
F_Port |
Device: Switch_2
WWN: 10:00:00:c0:dd:07:e3:4e
Security: Yes
Device: Switch_3
Security: NoFL_Port