ESP Encryption
List of IPsec Policy IPsec
In this table, you can view the information of IPsec policies and edit them by the action buttons.
The first entry in Figure
Tips:
●0.0.0.0.0/32 indicates all IP addresses.
●Refer to Appendix Troubleshooting 5 for the configuration of subnet.
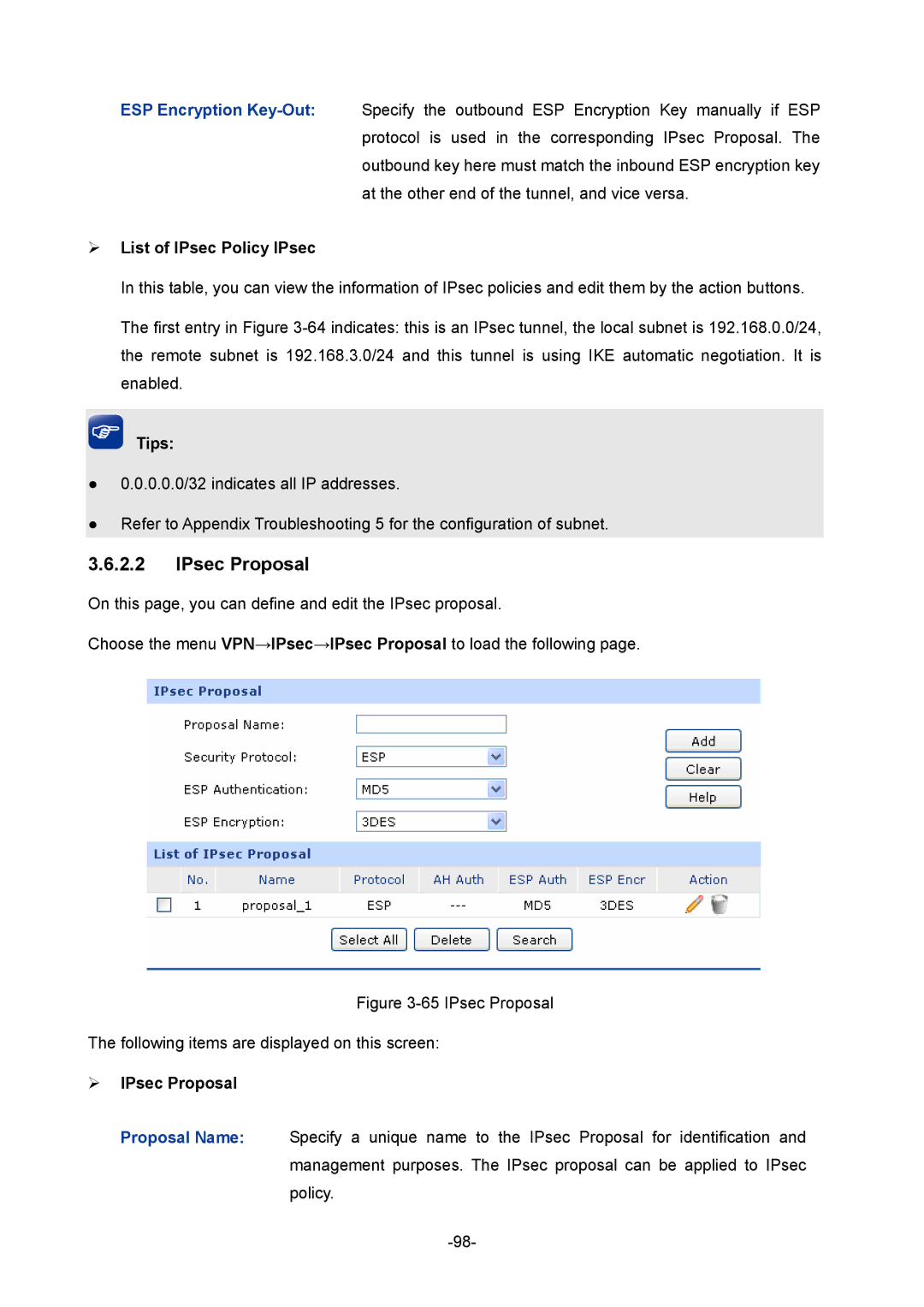
3.6.2.2IPsec Proposal
On this page, you can define and edit the IPsec proposal.
Choose the menu VPN→IPsec→IPsec Proposal to load the following page.
Figure 3-65 IPsec Proposal
The following items are displayed on this screen:
IPsec Proposal
Proposal Name: Specify a unique name to the IPsec Proposal for identification and
management purposes. The IPsec proposal can be applied to IPsec policy.