Foundry AR-Series Router User Guide
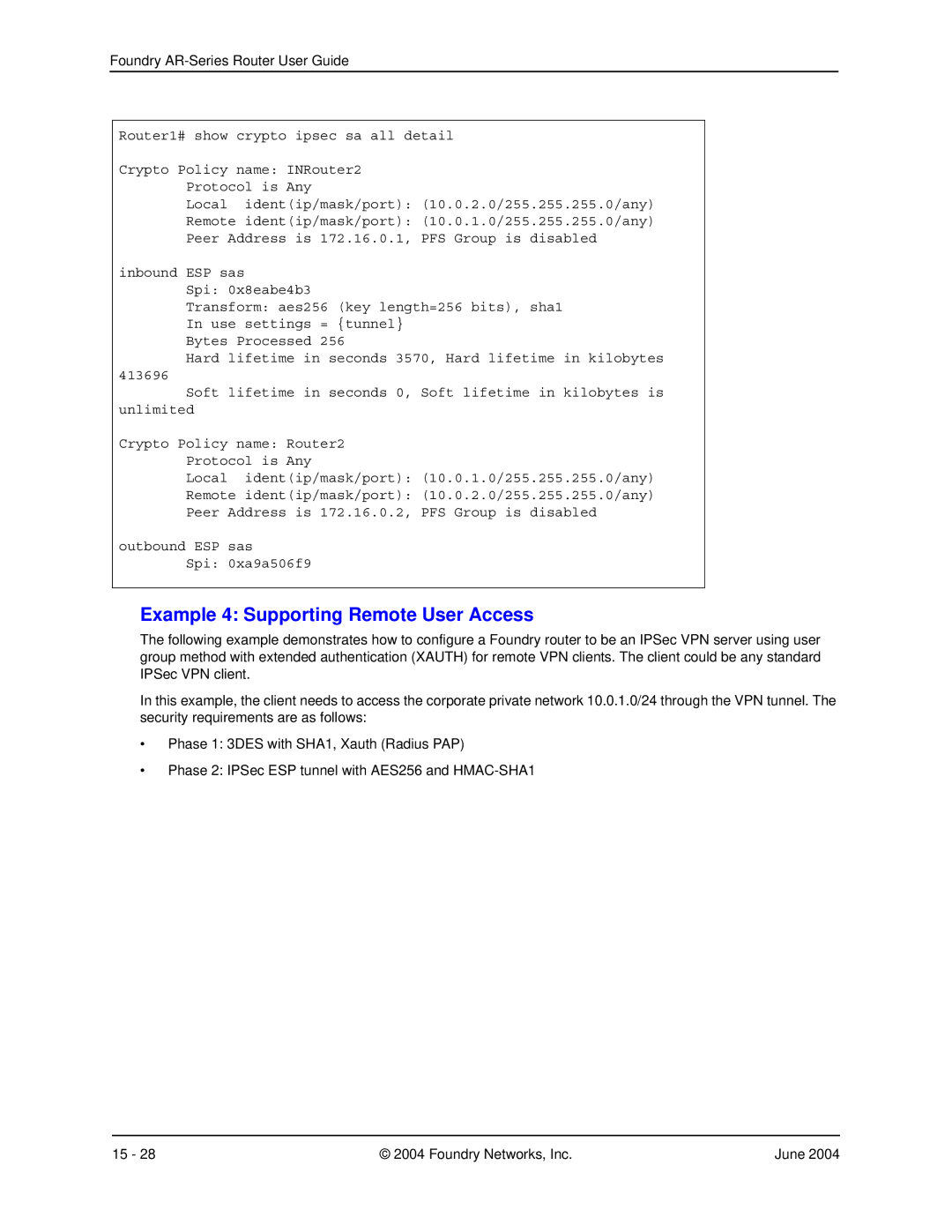
Router1# show crypto ipsec sa all detail
Crypto Policy name: INRouter2
Protocol is Any
Local ident(ip/mask/port): (10.0.2.0/255.255.255.0/any)
Remote ident(ip/mask/port): (10.0.1.0/255.255.255.0/any)
Peer Address is 172.16.0.1, PFS Group is disabled
inbound ESP sas
Spi: 0x8eabe4b3
Transform: aes256 (key length=256 bits), sha1 In use settings = {tunnel}
Bytes Processed 256
Hard lifetime in seconds 3570, Hard lifetime in kilobytes
413696
Soft lifetime in seconds 0, Soft lifetime in kilobytes is unlimited
Crypto Policy name: Router2
Protocol is Any
Local ident(ip/mask/port): (10.0.1.0/255.255.255.0/any)
Remote ident(ip/mask/port): (10.0.2.0/255.255.255.0/any)
Peer Address is 172.16.0.2, PFS Group is disabled
outbound ESP sas
Spi: 0xa9a506f9
Example 4: Supporting Remote User Access
The following example demonstrates how to configure a Foundry router to be an IPSec VPN server using user group method with extended authentication (XAUTH) for remote VPN clients. The client could be any standard IPSec VPN client.
In this example, the client needs to access the corporate private network 10.0.1.0/24 through the VPN tunnel. The security requirements are as follows:
•Phase 1: 3DES with SHA1, Xauth (Radius PAP)
•Phase 2: IPSec ESP tunnel with AES256 and
15 - 28 | © 2004 Foundry Networks, Inc. | June 2004 |