1.5.10 802.1X Port-Based Network Access Control
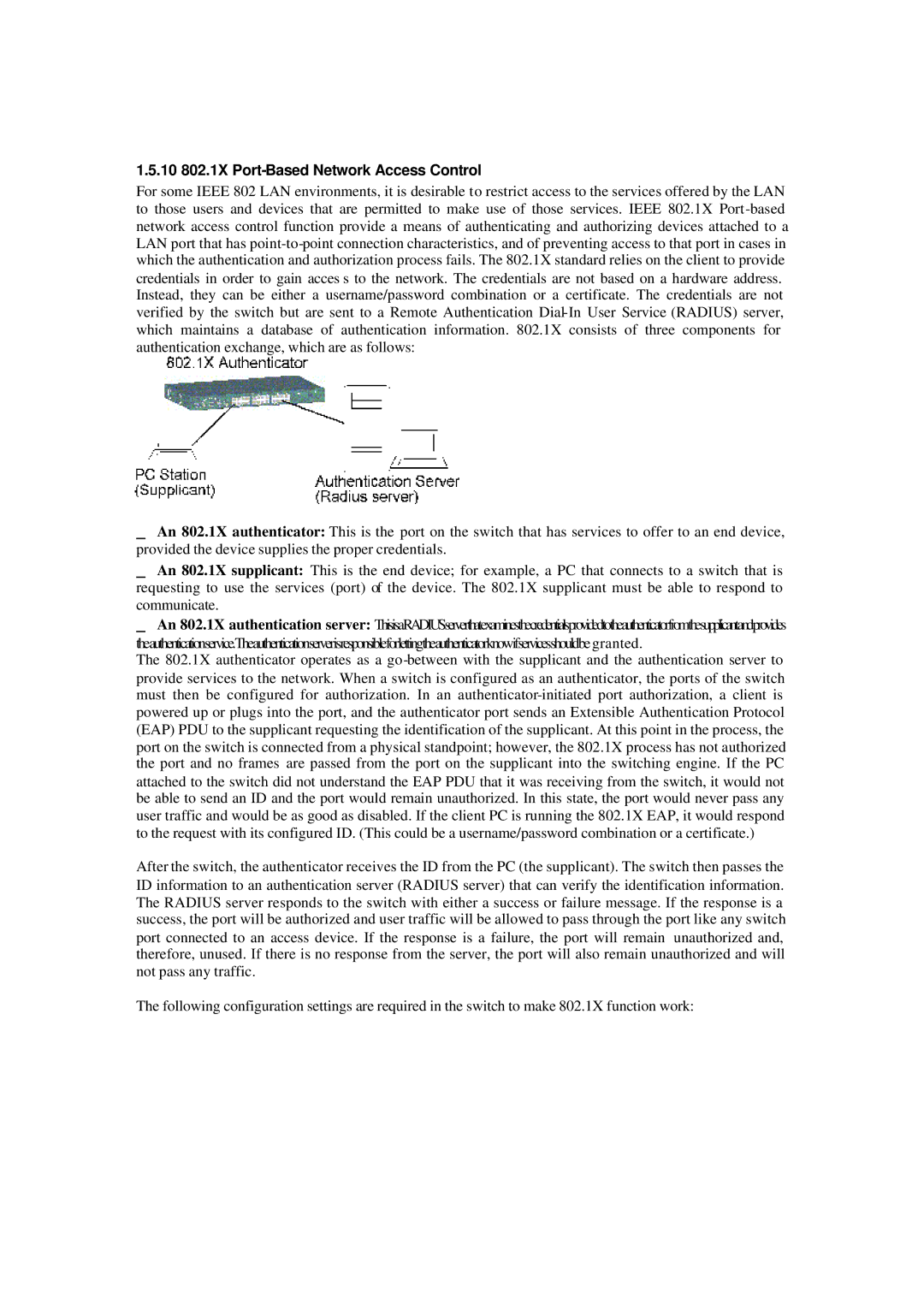
For some IEEE 802 LAN environments, it is desirable to restrict access to the services offered by the LAN to those users and devices that are permitted to make use of those services. IEEE 802.1X
Instead, they can be either a username/password combination or a certificate. The credentials are not verified by the switch but are sent to a Remote Authentication
_ An 802.1X authenticator: This is the port on the switch that has services to offer to an end device, provided the device supplies the proper credentials.
_ An 802.1X supplicant: This is the end device; for example, a PC that connects to a switch that is requesting to use the services (port) of the device. The 802.1X supplicant must be able to respond to communicate.
_ An 802.1X authentication server: ThisisaRADIUSserverthatexaminesthecredentialsprovidedtotheauthenticatorfromthesupplicantandprovides theauthenticationservice.Theauthenticationserverisresponsibleforlettingtheauthenticatorknowifservicesshouldbe granted.
The 802.1X authenticator operates as a go
After the switch, the authenticator receives the ID from the PC (the supplicant). The switch then passes the ID information to an authentication server (RADIUS server) that can verify the identification information. The RADIUS server responds to the switch with either a success or failure message. If the response is a success, the port will be authorized and user traffic will be allowed to pass through the port like any switch port connected to an access device. If the response is a failure, the port will remain unauthorized and, therefore, unused. If there is no response from the server, the port will also remain unauthorized and will not pass any traffic.
The following configuration settings are required in the switch to make 802.1X function work: