13-132 User’s Reference Guide
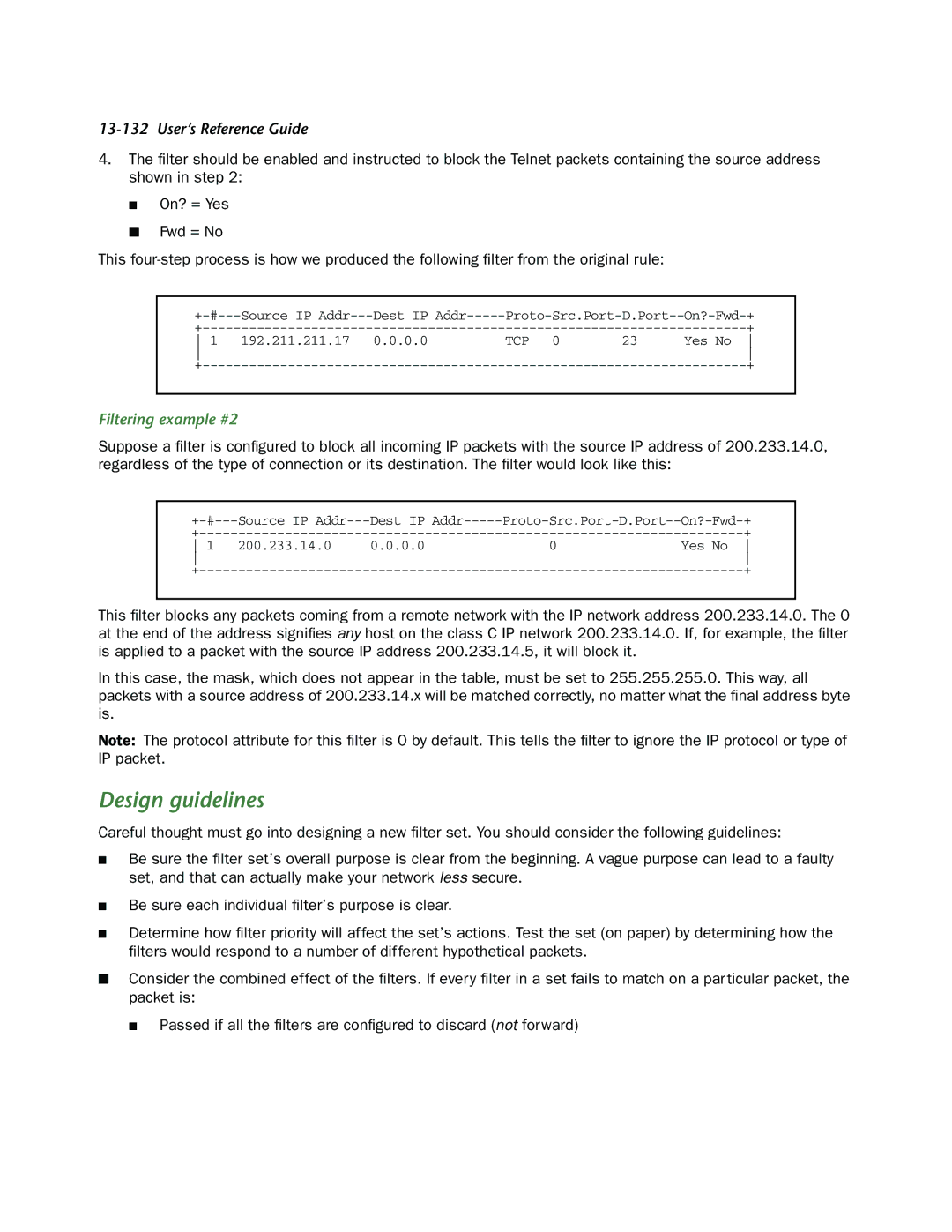
4.The filter should be enabled and instructed to block the Telnet packets containing the source address shown in step 2:
■On? = Yes
■Fwd = No
This
Source IP | Dest IP | ||||
|
|
| + | ||
1 | 192.211.211.17 | 0.0.0.0 | TCP 0 | 23 | Yes No |
|
|
|
| ||
|
|
| + | ||
Filtering example #2
Suppose a filter is configured to block all incoming IP packets with the source IP address of 200.233.14.0, regardless of the type of connection or its destination. The filter would look like this:
Source IP | Dest IP | |||
|
| + | ||
1 | 200.233.14.0 | 0.0.0.0 | 0 | Yes No |
|
|
| ||
|
| + | ||
This filter blocks any packets coming from a remote network with the IP network address 200.233.14.0. The 0 at the end of the address signifies any host on the class C IP network 200.233.14.0. If, for example, the filter is applied to a packet with the source IP address 200.233.14.5, it will block it.
In this case, the mask, which does not appear in the table, must be set to 255.255.255.0. This way, all packets with a source address of 200.233.14.x will be matched correctly, no matter what the final address byte is.
Note: The protocol attribute for this filter is 0 by default. This tells the filter to ignore the IP protocol or type of IP packet.
Design guidelines
Careful thought must go into designing a new filter set. You should consider the following guidelines:
■Be sure the filter set’s overall purpose is clear from the beginning. A vague purpose can lead to a faulty set, and that can actually make your network less secure.
■Be sure each individual filter’s purpose is clear.
■Determine how filter priority will affect the set’s actions. Test the set (on paper) by determining how the filters would respond to a number of different hypothetical packets.
■Consider the combined effect of the filters. If every filter in a set fails to match on a particular packet, the packet is:
■ Passed if all the filters are configured to discard (not forward)