DGS-3024 Gigabit Ethernet Switch Manual
RADIUS
Server
Ethernet Switch
|
|
|
|
|
|
|
| … |
802.1X | 802.1X | 802.1X | 802.1X | 802.1X | 802.1X | 802.1X | 802.1X | 802.1X |
Client | Client | Client | Client | Client | Client | Client | Client | Client |
Network access controlled port
Network access uncontrolled port
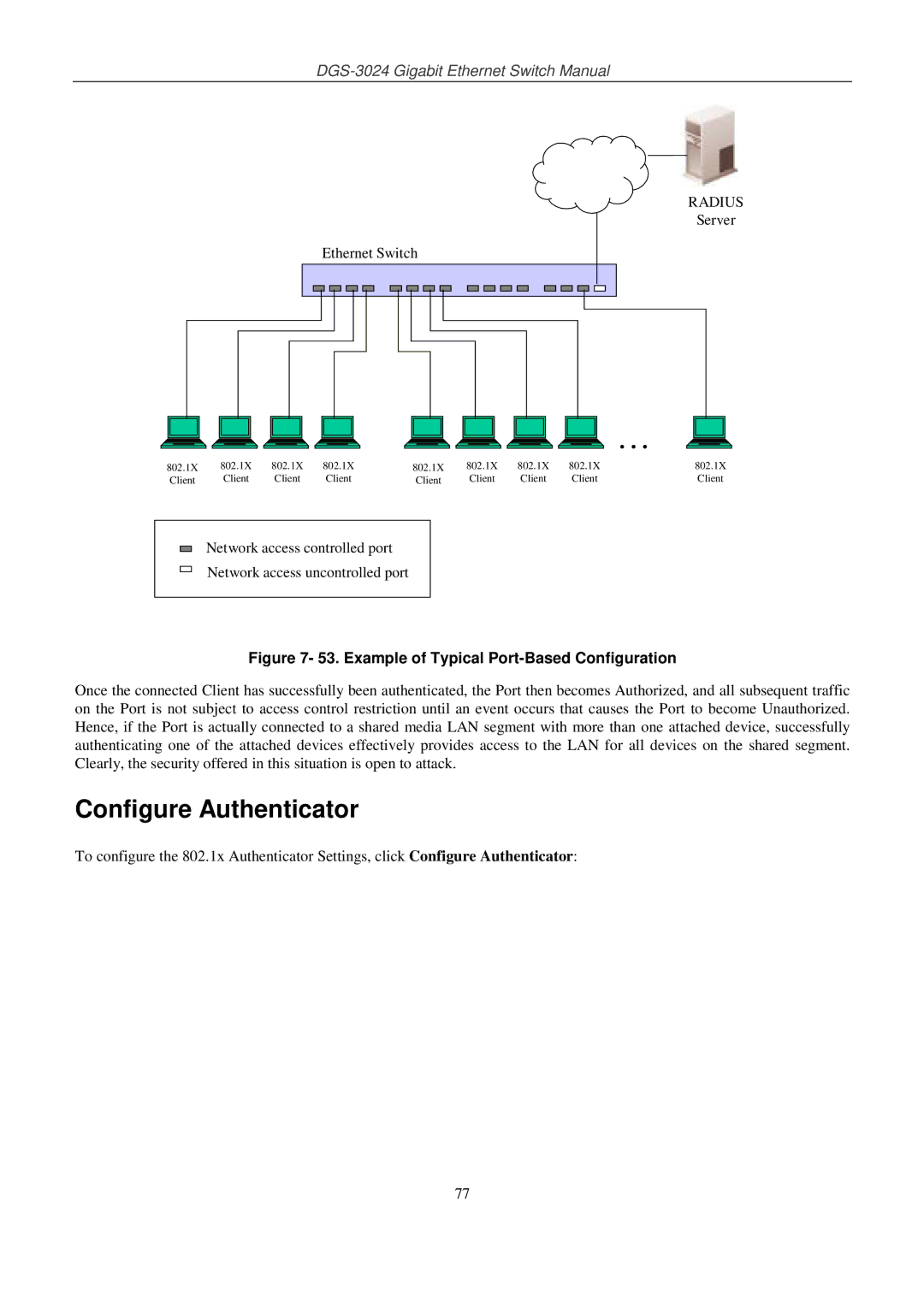
Figure 7- 53. Example of Typical Port-Based Configuration
Once the connected Client has successfully been authenticated, the Port then becomes Authorized, and all subsequent traffic on the Port is not subject to access control restriction until an event occurs that causes the Port to become Unauthorized. Hence, if the Port is actually connected to a shared media LAN segment with more than one attached device, successfully authenticating one of the attached devices effectively provides access to the LAN for all devices on the shared segment. Clearly, the security offered in this situation is open to attack.
Configure Authenticator
To configure the 802.1x Authenticator Settings, click Configure Authenticator:
77