HP Deskjet 6800 series printer |
|
|
|
| ||
|
|
|
|
|
|
|
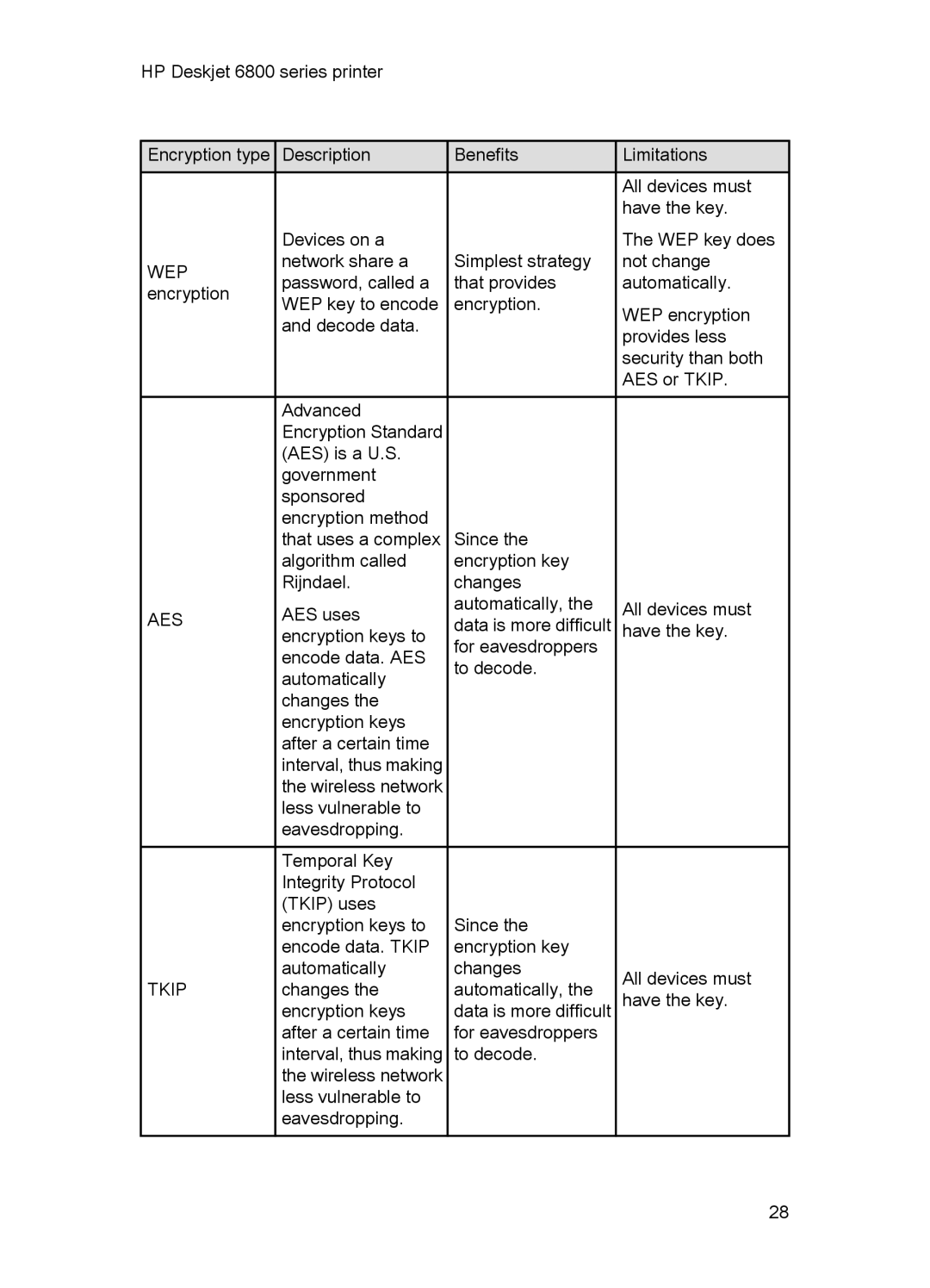
Encryption type | Description | Benefits | Limitations | |||
|
|
|
|
|
| All devices must |
|
|
|
|
|
| have the key. |
WEP encryption
AES
TKIP
Devices on a network share a password, called a WEP key to encode and decode data.
Advanced Encryption Standard (AES) is a U.S. government sponsored encryption method that uses a complex algorithm called Rijndael.
AES uses encryption keys to encode data. AES automatically changes the encryption keys after a certain time interval, thus making the wireless network less vulnerable to eavesdropping.
Temporal Key Integrity Protocol (TKIP) uses encryption keys to encode data. TKIP automatically changes the encryption keys after a certain time interval, thus making the wireless network less vulnerable to eavesdropping.
Simplest strategy that provides encryption.
Since the encryption key changes automatically, the data is more difficult for eavesdroppers to decode.
Since the encryption key changes automatically, the data is more difficult for eavesdroppers to decode.
The WEP key does not change automatically.
WEP encryption provides less security than both AES or TKIP.
All devices must have the key.
All devices must have the key.
28