Grey Headline (continued)
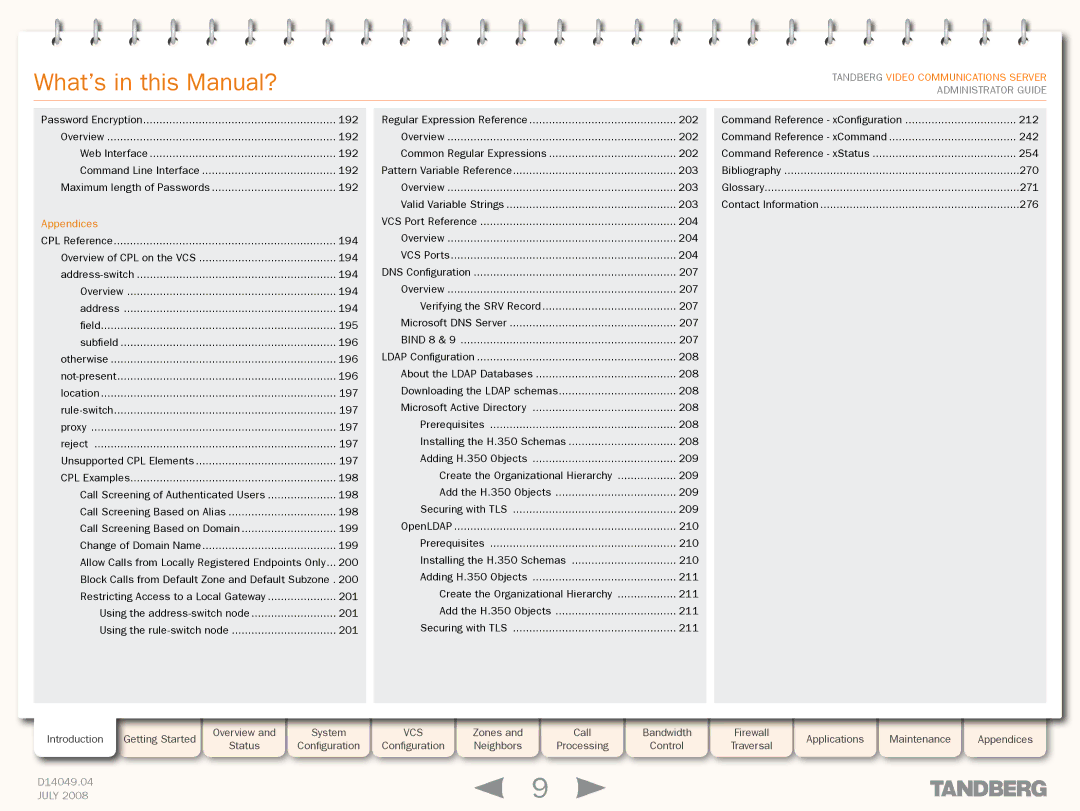
What’s in this Manual?
TANDBERG VIDEO COMMUNICATIONS SERVER ADMINISTRATOR GUIDE
Password Encryption | 192 |
Overview | 192 |
Web Interface | 192 |
Command Line Interface | 192 |
Maximum length of Passwords | 192 |
Appendices |
|
CPL Reference | 194 |
Overview of CPL on the VCS | 194 |
194 | |
Overview | 194 |
address | 194 |
field | 195 |
subfield | 196 |
otherwise | 196 |
196 | |
location | 197 |
197 | |
proxy | 197 |
reject | 197 |
Unsupported CPL Elements | 197 |
CPL Examples | 198 |
Call Screening of Authenticated Users | 198 |
Call Screening Based on Alias | 198 |
Call Screening Based on Domain | 199 |
Change of Domain Name | 199 |
Allow Calls from Locally Registered Endpoints Only... | 200 |
Block Calls from Default Zone and Default Subzone.. 200 | |
Restricting Access to a Local Gateway | 201 |
Using the | 201 |
Using the | 201 |
Regular Expression Reference | 202 |
| ...................................Command Reference - xConfiguration | 212 |
Overview | 202 |
| Command Reference - xCommand | 242 |
Common Regular Expressions | 202 |
| Command Reference - xStatus | 254 |
Pattern Variable Reference | 203 |
| Bibliography | 270 |
Overview | 203 |
| Glossary | 271 |
Valid Variable Strings | 203 |
| Contact Information | 276 |
VCS Port Reference | 204 |
|
|
|
Overview | 204 |
|
|
|
VCS Ports | 204 |
|
|
|
DNS Configuration | 207 |
|
|
|
Overview | 207 |
|
|
|
Verifying the SRV Record | 207 |
|
|
|
Microsoft DNS Server | 207 |
|
|
|
BIND 8 & 9 | 207 |
|
|
|
LDAP Configuration | 208 |
|
|
|
About the LDAP Databases | 208 |
|
|
|
Downloading the LDAP schemas | 208 |
|
|
|
Microsoft Active Directory | 208 |
|
|
|
Prerequisites | 208 |
|
|
|
Installing the H.350 Schemas | 208 |
|
|
|
Adding H.350 Objects | 209 |
|
|
|
Create the Organizational Hierarchy | 209 |
|
|
|
Add the H.350 Objects | 209 |
|
|
|
Securing with TLS | 209 |
|
|
|
OpenLDAP | 210 |
|
|
|
Prerequisites | 210 |
|
|
|
Installing the H.350 Schemas | 210 |
|
|
|
Adding H.350 Objects | 211 |
|
|
|
Create the Organizational Hierarchy | 211 |
|
|
|
Add the H.350 Objects | 211 |
|
|
|
Securing with TLS | 211 |
|
|
|
|
|
|
|
|
Introduction | Getting Started |
| Overview and |
| System |
| VCS |
| Zones and |
| Call |
| Bandwidth |
| Firewall |
| Applications |
| Maintenance |
| Appendices |
| Status |
| Configuration |
| Configuration |
| Neighbors |
| Processing |
| Control |
| Traversal |
|
|
| |||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
| |||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
D14049.04 |
|
|
|
|
|
|
|
|
| 9 |
|
|
|
|
|
|
|
|
|
|
|
JULY 2008 |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|