Corporate Headquarters
Text Part Number OL-2159-05
Copyright 2001-2003, Cisco Systems, Inc All rights reserved
N T E N T S
Iii
Navigating Using the Map Windows
Native Vlan ID
WEP Not Set on the Wireless Phone
Settings on the Authenticator Configuration
Vii
Event Notifications Setup
Viii
Setting Up Administrator Authorization
Snmp Setup
Ssid
Xii
Organization
Audience and Scope
Xiii
Tip Means the following are useful tips
Conventions
Xiv
Obtaining Documentation
Related Publications
Cisco.com
Documentation Feedback
Documentation CD-ROM
Ordering Documentation
Xvi
TAC Case Priority Definitions
Obtaining Technical Assistance
Cisco TAC Website Opening a TAC Case
Xvii
Obtaining Additional Publications and Information
Xviii
Overview
A P T E R
Key Features
Management Options
Quality of Service Support
Roaming Client Devices
Related Documents
What is QoS?
Limitations and Restrictions
These documents are available on Cisco.com
What is a VLAN?
Vlan Support
Incorporating Wireless Devices into VLANs
Level of Access
Vlan Example
Network Configuration Examples
Root Unit on a Wired LAN
Repeater Unit that Extends Wireless Range
Access Points as Root Units on a Wired LAN
Central Unit in an All-Wireless Network
Access Point as Repeater
Using the Management Interfaces
Using the Management Pages in the Web-Browser Interface
Using the Web-Browser Interface
Using the Web-Browser Interface for the First Time
Button/Link Description
Navigating Using the Map Windows
Map Window with Network Ports Pages Expanded
Using the Command-Line Interface
Preparing to Use a Terminal Emulator
Connecting the Serial Cable
Changing Settings with the CLI
Setting Up the Terminal Emulator
Selecting Pages and Settings
Function Description
Using a Telnet Session
Using Snmp
Applying Changes to the Configuration
Supported MIBs
Radio Configuration and Basic Settings
Basic Settings
Express Setup
System Name
Entering Basic Settings
Express Setup page contains the following settings
MAC Address
Default IP Subnet Mask
Configuration Server Protocol
Default IP Address
Default Gateway
Root-Unit Access Points
Security Setup Link
Radio Network Optimization Optimize Radio Network For
Snmp Admin. Community
Radio Configuration
Radio Network Compatibility Ensure Compatibility With
Settings on the AP Radio Identification
Entering Identity Information
Default IP Subnet Mask
Primary Port Settings
Default IP Address
Service Set ID Ssid
Leap Password
Entering Radio Hardware Information
AP Radio Hardware page contains the following settings
Settings on the AP Radio Hardware
Allow Broadcast Ssid to Associate?
Enable World Mode
Data Rates
RTS Threshold
Transmit Power
Frag. Threshold
Max. RTS Retries
Search for Less-Congested Radio Channel
Default Radio Channel
Restrict Searched Channels
Entering Advanced Configuration Information
Receive Antenna and Transmit Antenna
AP Radio Advanced Page for Internal Radio
Requested Status
Settings on the AP Radio Advanced
AP Radio Advanced pages contain the following settings
Packet Forwarding
Radio Cell Role
Default Multicast Address Filters
Maximum Multicast Packets/Second
Ssid For Use By Infrastructure Stations
Use Aironet Extensions
Classify Workgroup Bridges as Network Infrastructure
Require Use of Radio Firmware
Quality of Service Setup Link
Vlan Setup Link
Ethernet Encapsulation Transform
Temporal Key Integrity Protocol
Advanced Primary Ssid Setup Link
Preferred Access Points
Broadcast WEP Key rotation interval sec
Radio Modulation
Radio Preamble
Ethernet Configuration
Non-Root Mobility
Settings on the Ethernet Identification
Entering Ethernet Hardware Information
Ethernet Hardware page contains the following settings
Settings on the Ethernet Hardware
Speed
Loss of Backbone Connectivity Action
Loss of Backbone Connectivity # of Secs
Loss of Backbone Connectivity Ssid
Settings on the Ethernet Advanced
Ethernet Advanced page contains the following settings
Default Unicast and Multicast Address Filters
Always Unblock Ethernet When STP is Disabled
Default Unicast Address Filter
Optimize Ethernet for
OL-2159-05
Configuring VLANs
Vlan setup page contains the following settings
Settings on the Vlan Setup
Entering Vlan Information
Vlan Summary Status Link
802.1Q Encapsulation Mode
Maximum Number of Enabled Vlan IDs
Vlan 802.1Q Tagging
Optionally allow Encrypted packets on the unencrypted Vlan
Vlan Security Policy
Single Vlan ID which allows Unencrypted packets
Vlan Name
Parameter
Native Vlan Configuration
Broadcast Domain Segmentation
TKIP/MIC
Primary and Secondary SSIDs
Deployment of Infrastructure and Non infrastructure Devices
RADIUS-Based Vlan Access Control
Vlan ID
Criteria for Deploying Wireless VLANs
Vlan
Wireless Vlan Deployment Example
5shows the wireless Vlan deployment scenario described above
Creating and Configuring VLANs on the Access Point
Using the Configuration Screens
Obtaining and Recording Vlan ID and Setup Information
Creating the Native Vlan
Vlan Setup
Vlan ID #1 Setup
Creating the Full- and Part-Time VLANs
Creating the Maintenance Vlan
Creating the Guest Vlan
Creating and Configuring the SSIDs
AP Radio Internal Service Sets
Configuring VLANs Wireless Vlan Deployment Example
Enabling Vlan 802.1Q Tagging and Identifying the Native Vlan
11 AP Radio Service Sets
Guidelines for Wireless Vlan Deployment
Creating an Ssid for Infrastructure Devices
OL-2159-05
Configuring Filters and QoS
Filter Setup
Protocol Filtering
Creating a Protocol Filter
Enter a descriptive filter set name in the Set Name field
Filter Set
Enabling a Protocol Filter
MAC Address Filtering
Address Filters
Creating a MAC Address Filter
AP Radio Advanced
AP Radio Primary Ssid
QoS Configuration
Use Symbol Extensions
Settings on the Quality of Service Setup
Generate Qbss Element
Send Igmp General Query
Applying QoS
By Station
Traffic Category
10 Protocol Filters Setup
By Vlan
12 Vlan ID
13 Filters Priority Setting
By Filter
By CoS Value
By Dscp Value
Wireless QoS Deployment Example
17 Vlan Setup
18 Vlan ID #xx
WEP Set on the Wireless Phone
WEP Not Set on the Wireless Phone
20 AP Radio Internal Service Sets
21 AP Radio Internal Service Sets
OL-2159-05
Configuring Proxy Mobile IP
Proxy Mobile IP
Introduction to Mobility in IP
Mobile Approach
Nomadic Approach
Mobile IP Explained
Mobile IP Environment
Proxy Mobile IP Explained
Mobile IP Traffic Pattern
Before Deploying Proxy Mobile IP
Issues to Consider While Deploying Proxy Mobile IP
Components of a Proxy Mobile IP Network
How Proxy Mobile IP Works
Agent Discovery
Subnet Map Exchange
Home Agent Subnet Mask
Registration
Tunneling
Proxy Mobile IP Setup
Proxy Mobile IP Security
Proxy Mobile IP Setup
General
Enable Proxy Mobile IP
Authentication Server
Settings on the Proxy Mobile IP General
Authoritative AP n
Settings on the Authenticator Configuration
Settings on the Local SA Bindings
Local SA Bindings
Settings on the Proxy Mobile IP Statistics
Statistics
Active AAP
Authentication Failures for HA
Authentication Failures for FA
MN IP Addresses
Settings on the Subnet Map Table
Configuring Proxy Mobile IP
View Subnet Map Table
Configuring Proxy Mobile IP on Your Wired LAN
11 a Sample Network
13 AP Radio Internal Service Sets
15 Proxy Mobile IP General
17 Subnet Map Table
18 Authenticator Configuration
20 Network Configuration Screen for an Access Point Client
22 Passed Authentication Screen
Configuring Other Settings
Server Setup
Entering Time Server Settings
Settings on the Time Server Setup
Settings on the Boot Server Setup
Entering Boot Server Settings
Boot Server Setup page contains the following settings
Bootp Server Timeout sec
Configuration Server Protocol
Use Previous Configuration Server Settings
Dhcp Multiple-Offer Timeout sec
Dhcp Client Identifier Type
Dhcp Requested Lease Duration min
Dhcp Minimum Lease Duration min
Option Definition
Dhcp Client Identifier Value
Settings on the Web Server Setup
Web Server Setup page contains the following settings
Dhcp Class Identifier
Allow Non-Console Browsing
Default Help Root URL
Default Web Root URL
Http Port
Default Domain
Entering Name Server Settings
Settings on the Name Server Setup
Domain Name System
FTP Setup page contains the following settings
Entering FTP Settings
Settings on the FTP Setup
Domain Name Servers
Routing Setup
New Network Route Settings
Entering Routing Settings
Routing Setup page contains the following settings
Installed Network Routes list
Association Table Display Setup
Association Table Filters
Configuring Other Settings Association Table Display Setup
Stations to Show
Settings on the Association Table Filters
Fields to Show
Bytes To/From Station
Association Table Advanced
Packets To/From Station
Primary Sort
Settings on the Association Table Advanced
Association Table Advanced
Maximum number of bytes stored per Station Alert packet
Rogue AP Alert Timeout minutes
Handle Station Alerts as Severity Level
Maximum Number of Forwarding Table Entries
Settings on the Event Display Setup
Event Notification Setup
Event Display Setup
Default Activity Timeout seconds Per Device Class
Severity Level at which to display events
How should time generally be displayed?
How should Event Elapsed non-wall-clock Time be displayed?
Severity Level Description
Event Handling Setup
10 The Event Handling Setup
Handle Station Events as Severity Level
Settings on the Event Handling Setup
Disposition of Events
Maximum number of bytes stored per Alert packet
Clear Alert Statistics
Event Notifications Setup
Purge Trace Buffer
Snmp Trap Destination
Settings on the Event Notifications Setup
Should Notify-Disposition Events generate Snmp Traps?
Snmp Trap Community
Syslog Facility Number
Should Syslog Messages use the Cisco Emblem Format?
Syslog Destination Address
Ieee Snmp Traps Should Generate the Following Notifications
Security Setup
Security Overview
Encrypting Radio Signals with WEP
Levels of Security
Additional WEP Security Features
Network Authentication Types
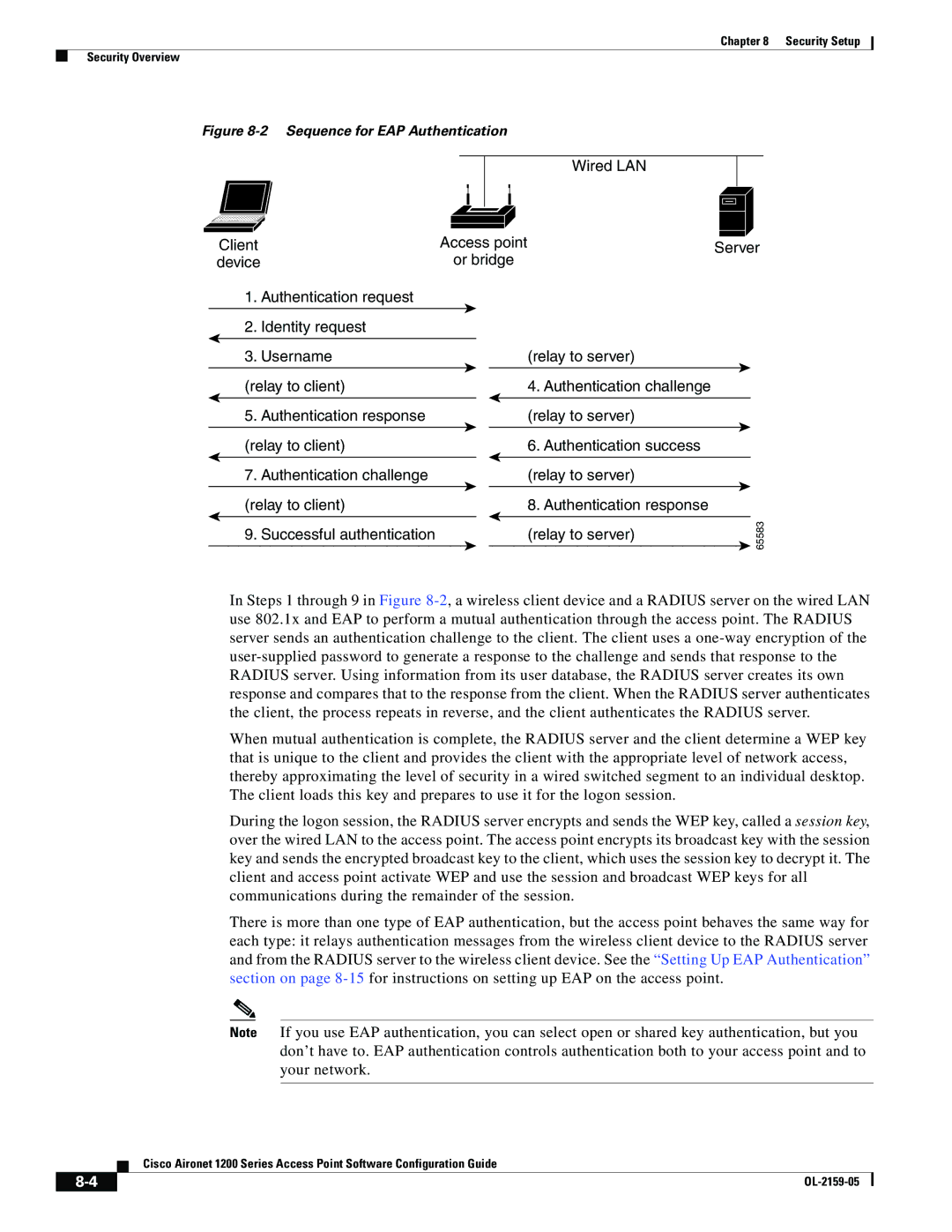
Sequence for EAP Authentication
Wired LAN Client
Combining MAC-Based, EAP, and Open Authentication
Sequence for Open Authentication
Setting Up WEP
Protecting the Access Point Configuration with User Manager
Key Access Point Associated Device
Transmit? Key Contents
Not set
Enabling Message Integrity Check MIC
Enabling Additional WEP Security Features
Using Snmp to Set Up WEP
Snmp Variable WEP Full WEP Off
AP Radio Advanced Page for Internal Radio
Enabling Temporal Key Integrity Protocol Tkip
Enabling Broadcast WEP Key Rotation
Setting Up Open or Shared Key Authentication
Setting Up EAP Authentication
Enabling EAP on the Access Point
Firmware Version Draft 802.1x-2001
Access Point EAP Settings for Various Client Configurations
Click Add New Access Server
Enabling EAP in Cisco Secure ACS
Setting Up a Repeater Access Point As a Leap Client
Setting a Session-Based WEP Key Timeout
AP Radio Identification Page for Internal Radio
Setting Up MAC-Based Authentication
Enabling MAC-Based Authentication on the Access Point
11 Authenticator Configuration
Security Setup Setting Up MAC-Based Authentication
12 AP Radio Advanced
Authenticating Client Devices Using MAC Addresses or EAP
Enabling MAC-Based Authentication in Cisco Secure ACS
Authentication Types Required Settings
Summary of Settings for Authentication Types
Leap
EAP-TLS, EAP-MD5
Radius Attributes Sent by the Access Point
Attribute ID Description
Acct-Authentic
Acct-Delay-Time
Acct-Session-Id
VSA attribute Nas-location Vlan-id Auth-algo-type
Setting Up Backup Authentication Servers
Acct-Terminate-Cause
Setting Up Administrator Authorization
14 Security Setup
Creating a List of Authorized Management System Users
16 User Management Window
Click Add New User. The User Management window appears
Setting up Centralized Administrator Authentication
Click User Information. The User Information page appears
Click Apply. You are returned to the User Information
18 Authenticator Configuration
System Flow Notes
Authorization Parameters
Network Management
Setting the Display Options
Using the Association Table
Browsing to Network Devices
Using Station Pages
Station
Information on Station Pages
Station Identification and Status
To Station Information
Rate, Signal, and Status Information
From Station Information
Hops and Timing Information
Performing Pings and Link Tests
Performing a Ping
Performing a Link Test
Click Link Test
Deauthenticating and Disassociating Client Devices
Using the Network Map Window
Clearing and Updating Statistics
Using Cisco Discovery Protocol
Settings on the CDP Setup
MIB for CDP
Assigning Network Ports
Port Assignments
Enabling Wireless Network Accounting
Settings on the Port Assignments
Settings on the Accounting Setup
Accounting Setup
Accounting Attributes
Attribute Definition
Radiusipadr
OL-2159-05
Managing Firmware and Configurations
10-1
Updating with the Browser from a Local Drive
Full Update of the Firmware Components
Updating Firmware
10-2
Selective Update of the Firmware Components
10-3
Updating from a File Server
10-4
Update All Firmware From File Server
10-5
Update Firmware From File Server
10-6
Retrieving Firmware and Web Page Files
10-7
Distributing Firmware
10-8
Distributing a Configuration
10-9
Limiting Distributions
10-10
Downloading the Current Configuration
10-11
Uploading from a File Server
Uploading a Configuration
Uploading from a Local Drive
10-12
Resetting the Configuration
10-13
Restarting the Access Point
10-14
Management System Setup
11-1
Settings on the Snmp Setup
Snmp Setup
11-2
Settings on the Database Query
Using the Database Query
11-3
Changing Settings with the Database Query
Console and Telnet Setup
11-4
Using Secure Shell
Settings on the Console/Telnet
11-5
11-6
Special Configurations
12-1
Setting Up a Repeater Access Point
12-2
12-3
12-4
Using Hot Standby Mode
12-5
12-6
12-7
12-8
Sections in this chapter include
13-1
Selections on the Network Diagnostics
Using Diagnostic Pages
Network Diagnostics
13-2
Radio Diagnostics Tests
13-3
SSIDs Int, Mod
Vlan Summary Status
13-4
Network Ports
13-5
Data Received
Identifying Information and Status
13-6
Ethernet Port
Data Transmitted
13-7
Receive Statistics
Configuration Information
13-8
Transmit Statistics
AP Radio
13-9
13-10
AP Radio Port
13-11
Display Options
13-12
Event Log
Display Settings
13-13
Event Log Summary
Log Headings
Saving the Log
13-14
Command Information Displayed
Using Command-Line Diagnostics
13-15
Entering Diagnostic Commands
13-16
Eapdiag1on
Diagnostic Command Results
13-17
Vxdiagarpshow
Eapdiag2on
13-18
13-19
Vxdiagcheckstack
13-20
Vxdiaghostshow
13-21
Vxdiagi
13-22
Vxdiagipstatshow
13-23
Vxdiagmemshow
13-24
Vxdiagmuxshow
13-25
Vxdiagrouteshow
13-26
Vxdiagtcpstatshow
13-27
Vxdiagudpstatshow
Reserving Access Point Memory for a Packet Trace Log File
Tracing Packets
13-28
Tracing Packets for Specific Devices
13-29
Packets Stored in a Log File
Tracing Packets for Ethernet and Radio Ports
Viewing Packet Trace Data
13-30
Packets Displayed on the CLI
Checking the Top Panel Indicators
13-31
Message Ethernet Status Radio Meaning Type Indicator
13-32
Finding an Access Point by Blinking the Top Panel Indicators
13-33
WEP Keys
Checking Basic Settings
EAP Authentication Requires Matching 802.1x Protocol Drafts
13-34
Firmware Version Draft
13-35
Resetting to the Default Configuration
13-36
13-37
13-38
Channels, Power Levels, and Antenna Gains
Ieee 802.11a
Channels
Regulatory Domains
Maximum Power Levels and Antenna Gains
Ieee 802.11b
Regulatory Domain With 6-dBi Antenna Gain
Maximum Power Level mW
Regulatory Domain Antenna Gain dBi Maximum Power Level mW
Americas -A 100 Eirp maximum 13.5 Emea -E MW Eirp maximum
Regulatory Domain Antenna Gain dBi Maximum Power Level mW
OL-2159-05
Protocol Filter Lists
Protocol
ISO Designator
SVP
UDP XNS-IDP ISO-TP4 ISO-CNLP Cnlp
Vines
Smtp
Tsap
Tftp
Http
POP2
IRC
Cmot
BGP
RIP
CVS
Radius
RFE
Event Log Messages
Cisco Emblem Format
Default Format
Message Formats
With a timestamp, messages look like this example
Logemerg
Loginfo
Syslog Severity Emblem Severity
Logalert
Severity Event Description Mnemonic Recommended Action
Message Descriptions
Possible Cause or
Reason
Device
Host
Srchost
Newaddr
IfDescr
Desthost length pktLen
Srchost to port ifDescr
Reqlen bytes
Packet from srchost to desthost
IfDescr error= errornum
Desthost on port ifDescr
Srchost to desthost on port
IfDescr error=erronum
For procedure on port ifDescr
From srchost to desthost on port
Srchost on port ifDescr
Srchost to desthost of unknown
Version
Desthost
Admin
Sysreboot
Rebootinf
Prtrarpip
Port device
Status
IfDescr errno=errno
PktLen
Xidexp
ENC WEP
Unenc
Ethercon
Media port
Frame bytes
Frame
Port devName unit
Username Failed
Username
Unit
Assoclost
1XVER
Hstndbyen
Hstndbyeth
Amngrreq
Instkey
Acctcon
Nulses
Noaserv
Norbuf
Nosbuf
Open
VlanID
IfIndex MIB
IfIndex Awcmib
Taskfailed
Nomibdkey
Badsize
Taskstarted
SsidIdx
Statuses and Reasons
Appendix C Event Log Messages Statuses and Reasons
OL-2159-05
Numerics
IN-1
CLI
CDP MIB
Dhcp
Dtim
IN-3
Radio traffic
Ethernet Locate unit by flashing LEDs
IN-4
Pspf
IN-5
Vlan
SSH
IN-6
Warm restart
IN-7
IN-8