Web/Installation Guide
Table of Contents
Managing Device Information
Configuring Ports 115
Configuring IP Information 171
Configuring Quality of Service 237
Configuring System Time 281
DXS/DWS-3227/3227P, DXS/DWS-3250 User Guide Overview
Preface
DXS/DWS-3227/3227P, DXS/DWS-3250 User Guide Overview
Intended Audience
DXS/DWS 3200 Series User Guide
Device Description
Viewing the Device
DXS-3250/DWS Front Panel
Viewing the Device
DXS/DWS-3227 Front Panel
DXS/DWS-3227P Front Panel
Back Panels
DXS/DWS-3227P Front Panel
Ports Description
1000Base-T Gigabit Ethernet Ports
10G XFP Fiber port
Optional Modules
10G XFP Fiber port
SFP Ports
Ports Description
RS-232 Console Port
Stacking Ports
Stacking Kit Optional
Cable Specifications
LED Definitions
Port LEDs
1000Base-T Gigabit Ethernet RJ-45 Port LEDs
1000Base-T Gigabit Ethernet RJ-45 Port LED Indications
LED Definitions
Port Description LED Indication
System LEDs
SFP LEDs
SFP LED Indications Description
System’s LED Indications LED Description
Indication
Pin Connections for the 10/100/1000 Ethernet Interface
Cable, Port, and Pinout Information
RJ-45 Pin Connections for 10/100/1000 Base-TX Use
CX-4 Port Pin Connections
Cable, Port, and Pinout Information
Pin Use
Physical Dimensions
DXS/DWS 3250 / DXS/DWS 3227P
DXS/DWS
DB-9 Port Pin Connections Use
Physical Dimensions
DXS/DWS 3200 Series User Guide
Preparing for Installation
Installation Precautions
Preparing for Installation
Mounting Device
Package Contents
Site Requirements
Unpacking
Unpacking Essentials
Installing the Device
Desktop or Shelf Installation
Rack Installation
Installing the Device
Attaching the Mounting Brackets
Mounting Device in a Rack
Connecting the Switch to a Terminal
Connecting the Device
AC Power Connection
Initial Configuration
General Configuration Information
General Configuration Information
Auto-Negotiation
Device Port Default Settings
Booting the Switch
Device Port Default Settings Function
Booting the Switch
Configuration Overview
Configuration Overview
Initial Configuration
Static IP Address and Subnet Mask
User Name
Snmp Community Strings
Following screen displays the default device configuration
Advanced Configuration
Retrieving an IP Address From a Dhcp Server
Receiving an IP Address From a Bootp Server
Advanced Configuration
Configuring Security Passwords Introduction
Security Management and Password Configuration
Configuring an Initial Console Password
Configuring an Initial Telnet Password
Configuring an Initial SSH password
Configuring an Initial Http Password
Configuring an initial Https Password
Software Download through XModem
Software Download and Reboot
Software Download Through Tftp Server
Boot Image Download
Software Download and Reboot
Configuring Stacking
Configuring Stacking
Startup Menu Functions
Download Software
Erase Flash Sectors
Erase Flash File
Startup Menu Functions
Password Recovery
Wlan Licence Key
Press Enter
Press Escape
This page is left blank intentionally
Getting Started
Starting the D-Link Embedded Web Interface
Click . The D-Link Embedded Web Interface Home Page opens
Link Embedded Web Interface Home
Starting the D-Link Embedded Web Interface
Interface Components
Understanding the D-Link Embedded Web Interface
View Description
Device Representation
Understanding the D-Link Embedded Web Interface
Using the D-Link Embedded Web Interface Management Buttons
Using Screen and Table Options
Adding Configuration Information
Modifying Configuration Information
Using Screen and Table Options
Deleting Configuration Information
IP Interface Settings
Resetting the Device
Resetting the Device
Click System General Reset. The Reset page opens
Logging Off from the Device
Click . The D-Link Embedded Web Interface Home Page closes
Defining the System Description
Managing Device Information
Defining the System Description
DXS/DWS 3200 Series User Guide
Defining Advanced System Settings
Defining Advanced System Settings
Click System General Mode. The Mode Page opens
Check the Enable Jumbo Frames field
This page is left blank intentionally
Managing Power over Ethernet Devices
Modify the Unit No., Power Status, and Powered Device fields
Defining PoE System Information
Defining PoE System Information
Define the Unit No. and the System Usage Threshold field
Displaying and Editing PoE System Information
PoE Interface
Displaying and Editing PoE System Information
Click . The PoE Interface Edit Page opens
DXS/DWS 3200 Series User Guide
Managing Stacking
Stacking Failover Topology
Understanding the Stack Topology
Stacking Members and Unit ID
Removing and Replacing Stacking Members
Stacking Failover Topology
Switching the Stacking Master
Exchanging Stacking Members
Stack Page contains the following fields
Click System General tab. The Stack Page opens
This page is left blank intentionally
Configuring Device Security
Configuring Management Security
Configuring Authentication Methods
Defining Access Profiles
Configuring Management Security
Add Access Profile
Click . The Add Access Profile Page opens
Configuring Device Security
Defining Profile Rules
Profile Rules
Add Profile Rule
Click . The Add Profile Rule Page opens
Click . The Profile Rules Setting Page opens
Defining Authentication Profiles
Authentication Profile
Add Authentication Profile
Click . The Add Authentication Profile Page opens
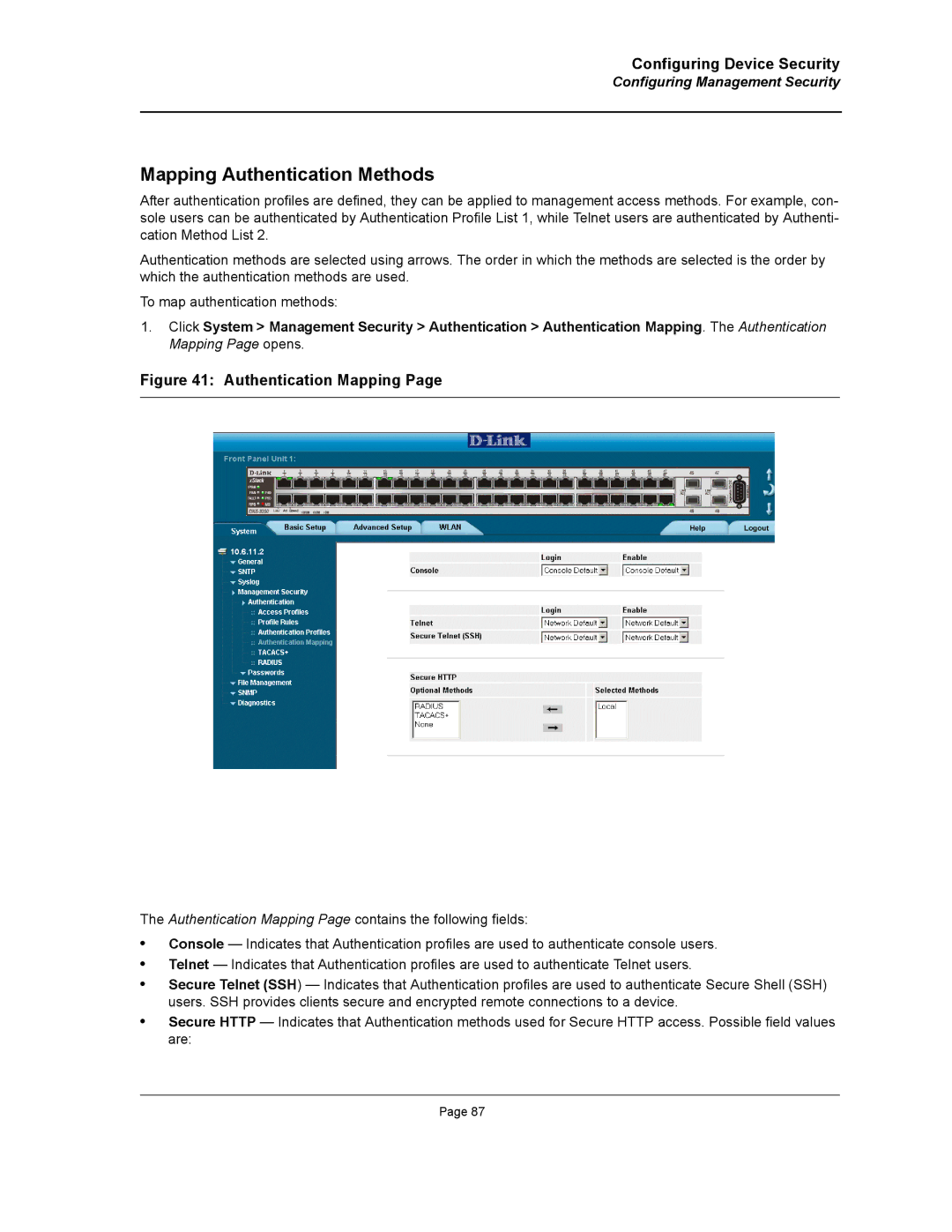
Mapping Authentication Methods
Authentication Mapping
Define the Console, Telnet, and Secure Telnet SSH fields
Defining Radius Settings
Radius
Add Radius Server
Click . The Add Radius Server Page opens
Radius Server Settings
Click . The Radius Server Settings Page opens
Defining TACACS+ Authentication
TACACS+
Add TACACS+ Host
TACACS+ Host Settings
Defining Local Users
Configuring Passwords
Click . The Add Local User Page opens
Local User Settings
Click . The Local User Settings Page opens
Defining Line Passwords
Line Password
Defining Enable Passwords
Enable Password
Configuring Network Security
Port-Based Authentication
Advanced Port-Based Authentication
Configuring Network Security
DXS/DWS 3200 Series User Guide
Defining Network Authentication Properties
Network Authentication Properties
DXS/DWS 3200 Series User Guide
Defining Port Authentication
Port Authentication
Supplicant Timeout Server Timeout
Click . The Port Authentication Settings Page opens
Configuring Multiple Hosts
Multiple Host
Multiple Host Settings
Defining Authentication Hosts
Authenticated Host
Configuring Traffic Control
Managing Port Security
Port Security
Port Security Settings
Click . The Port Security Settings Page opens
Enabling Storm Control
Storm Control
Storm Control Settings
Click . The Storm Control Settings Page opens
Defining DOS Protection Security
Defining DOS Protection Security
Add Martian Addresses
Click . The Add Martian Addresses Page opens
Configuring Ports
Interface Configuration
Port Configuration Settings
Click . The Port or LAG Interface Settings Page opens
Configuring Ports
Viewing Port Properties
Interface Properties
Port Properties
Viewing Port Properties
This page is left blank intentionally
Aggregating Ports
Configuring Lacp
Click . The Lacp Parameters Settings Page opens
Configuring Lacp
Edit the Port Priority and Lacp Timeout fields
Defining LAG Members
LAG Membership
Configuring VLANs
Defining Vlan Properties
Vlan Properties
Add Vlan
Defining Vlan Properties
Defining Vlan Membership
Vlan Membership
Defining Vlan Membership
Defining Vlan Interface Settings
Vlan Interface Settings
Defining Vlan Interface Settings
Click . The Vlan Interface Settings Page opens
Configuring Garp
Defining Garp
Configuring Garp
Click . The Garp Parameters Settings Page opens
Defining Gvrp
Gvrp Parameters
Gvrp Parameters Settings
Click . The Gvrp Parameters Settings Page opens
Configuring Multicast VLANs
Defining Protocol Based VLANs
Defining Vlan Groups
Defining Vlan Groups
Add Protocol Group
Click . The Vlan Protocol Port Setting Page opens
Defining Vlan Protocol Ports
Vlan Protocol Port Setting
Click . The Protocol Group Settings Page opens
Defining Wlan
Defining Wlan System Properties
Enabling Wlan
Defining Wlan System Properties
Defining Wlan Security
Click Wlan System ESS/Security. The ESS Security Page opens
Create ESS Configuration
Click . The Create ESS Configuration Page opens
ESS Settings
DXS/DWS 3200 Series User Guide
Viewing Wlan Rogues
Click Wlan System Rogues. The Wlan Rogues Page opens
DXS/DWS 3200 Series User Guide
Viewing Wlan Stations
Monitor Wlan Stations
Defining Wlan Access Points
Defining Wlan Access Point Properties
Defining Wlan Access Points
Adding a New Access point
WTP Edit Screen
Configuring Wlan VLANs
Wlan Access Point VLANs
Configuring Wlan Template Settings
Click . The Create Wlan Template Page opens
Create Wlan Template
Configuring Wlan Radio Settings
Defining Wlan Radio Settings
Configuring Wlan Radio Settings
Click . The Modify Radio Setting Page opens
Defining BSS Settings
Click Wlan Radio BSS Settings. The BSS Settings Page opens
Click . The Create AP BSS Configuration Page opens
Create AP BSS Configuration
Click . The Edit BSS Settings Page opens
Edit BSS Settings
Defining Wlan Power Settings
Wlan Radio Power Settings
Defining Wlan
Viewing Access Point Statistics
Viewing Wlan Statistics
Viewing Wlan Statistics
Viewing Radio Interfaces Statistics
Wlan Radio Interface Statistics
Defining Wlan
Viewing BSS Statistics
Click Wlan Monitor BSS. The BSS Information Page opens
Wlan Stations Statistics
DXS/DWS 3200 Series User Guide
Configuring IP Interfaces
Configuring IP Information
Configuring IP Interfaces
Defining IP Addresses
Click . The Add IP Interface Page opens
Click . The IP Interface Settings Page opens
Add IP Interface
Defining Default Gateways
Default Gateway
Configuring Dhcp
Click . The Add Dhcp IP Interface Page opens
Add Dhcp IP Interface
Configuring ARP
ARP
ARP Settings
Configuring Domain Name Servers
Configuring Domain Name Servers
Defining DNS Servers
Remove
Click . The Add DNS Server Page opens
Defining DNS Host Mapping
DNS Host Mapping
Add DNS Host
Defining the Forwarding Database and Static Routes
Defining Static Forwarding Database Entries
Forwarding Database Static Addresses
Add Forwarding Database
Defining Static Forwarding Database Entries
Defining Dynamic Forwarding Database Entries
Dynamic Addresses
Defining Dynamic Forwarding Database Entries
Configuring Routing
IP Static Route
Configuring Routing
DXS/DWS 3200 Series User Guide
Configuring Spanning Tree
Defining Classic Spanning Tree
STP Properties
Select Enable in the Spanning Tree State field
Defining Classic Spanning Tree
Defining STP on Interfaces
STP Interface
Click . The STP Interface Settings Page opens
Defining STP on Interfaces
DXS/DWS 3200 Series User Guide
Defining Rapid Spanning Tree
Defining Rapid Spanning Tree
Click . The Rstp Settings Page opens
Defining Multiple Spanning Tree
Defining Multiple Spanning Tree
Define the Region Name, Revision, and Max Hops fields
Defining Mstp Instance Settings
Click . The Mstp Instance Configuration Table opens
Mstp Instance Configuration Table
Defining Mstp Interface Settings
Mstp Interface Settings Page contains the following fields
Click . The Mstp Interface Table opens
This page is left intentionally
Configuring Multicast Forwarding
Defining Igmp Snooping
Igmp Snooping
Multicast Global Parameters Settings
Defining Igmp Snooping
Defining Multicast Bridging Groups
Multicast Group
Defining Multicast Bridging Groups
Click . The Add Multicast Group Page opens
Defining Multicast Forward All Settings
Multicast Forward All
Forbidden
Configuring Multicast TV
Defining Igmp Snooping for Multicast TV
Configuring Multicast TV
Click . The Add Igmp Snooping Mapping Page opens
Viewing Multicast TV Members
Multicast TV Membership
Configuring Snmp
Configuring Snmp Security
Snmp v1 and v2c
Snmp
Define the Local Engine ID and Use Default fields
Defining Snmp Security
Configuring Snmp Security
Defining Snmp Views
Add Snmp View
Defining Snmp Group Profiles
Snmp Group Profile
Click . The Snmp Group Profile Settings Page opens
Click . The Add Snmp Group Profile Page opens
Snmp Group Profile Settings
Defining Snmp Group Members
Snmp Group Membership
Click . The Snmp Group Membership Settings Page opens
Click . The Add Snmp Group Membership Page opens
Snmp Group Membership Settings
Defining Snmp Communities
Snmp Communities Basic Table
Snmp Communities Advanced Tables
Click . The Add Snmp Community Page opens
Configuring Snmp Notifications
Configuring Snmp Notifications
Click . The Snmp Community Settings Page opens
Defining Snmp Notification Global Parameters
Snmp Notification Properties
Defining Snmp Notification Filters
Click . The Add Snmp Notification Filter Page opens
Add Snmp Notification Filter
Defining Snmp Notification Recipients
Snmp Notification Receiver
SNMPv1,2c Notification Recipient
SNMPv3 Notification Recipient
Click . The Add Snmp Notification Receiver Page opens
Click . The Snmp Notification Receiver Settings Page opens
Add Snmp Notification Receiver
Snmp Notification Receiver Settings
This page is left blank intentionally
Configuring Quality of Service
Quality of Service Overview
Defining General QoS Settings
CoS Services
Configuring QoS General Settings
Defining General QoS Settings
CoS
Select Enable in the Quality of Service field
Restoring Factory Default QoS Interface Settings
Configure Bandwidth Settings
Bandwidth Settings Edit
Click . The Bandwidth Settings Edit Page opens
Defining Queues
Select Strict Priority or WRR Fields
Configuring QoS Mapping
Mapping CoS Values to Queues
Configuring QoS Mapping
Mapping Dscp Values to Queues
Configuring Advanced QoS Settings
Defining Policy Properties
Configuring Advanced QoS Settings
Mapping Dscp Values
Defining Tail Dropping
Tail Drop
Creating Class Maps
Class maps
Add Class Map
Aggregating Policiers
Click . The Add Aggregated Policier Page opens
Add Aggregated Policier
Defining Policy Profiles
Defining Policies
Add QoS Policy Profile
Click . The Add QoS Policy Profile Page opens
Attaching Policies to Interfaces
Policy Binding
DXS/DWS 3200 Series User Guide
File Management Overview
Managing System Files
File Management Overview
Downloading System Files
Firmware Download
Configuration Download
Downloading System Files
Open the File Download
Define the Source File Name and Destination File fields
Uploading System Files
Upload Type
Configuration Upload
Software Image Upload
Uploading System Files
Open the File Upload
Activating Image Files
Active Image
Restoring the Default Configuration File
Select Copy Configuration
Select Restore Configuration Factory Defaults
Copying Files
Managing System Files
File System
Managing System Logs
System Log Severity Levels Message
Enabling System Logs
Syslog Properties
Enabling System Logs
Viewing the Device Memory Logs
Clearing Device Memory Logs
Clearing Flash Logs
Viewing the Flash Logs
Viewing the Flash Logs
Defining Servers Log Parameters
Click . The Add Syslog Server Page opens
Add Syslog Server
Defining Servers Log Parameters
This page is left blank intentionally
Managing Device Diagnostics
Configuring Port Mirroring
Port Mirroring
Configuring Port Mirroring
Click . The Add Port Mirroring Page opens
Port Mirroring Settings
Click . The Port Mirroring Settings Page opens
Viewing Integrated Cable Tests
Viewing Integrated Cable Tests
DXS/DWS 3200 Series User Guide
Viewing Optical Transceivers
Viewing Optical Transceivers
Optical Transceivers Page contains the field
Viewing the CPU Utilization
CPU Utilization
Configuring Daylight Savings Time
Configuring System Time
Configuring Daylight Savings Time
Click System General Time. The Time Page opens
Time
Define the Date, Local Time and Time Zone Offset fields
Configuring Sntp
Configuring Sntp
Polling for Unicast Time Information
Polling for Anycast Time Information
Defining Sntp Global Settings
Sntp Properties
Defining Sntp Global Settings
Defining Sntp Authentication
Sntp Authentication
Defining Sntp Authentication
Click . The Section Add Sntp Authentication page opens
Defining Sntp Servers
Click System Sntp Servers. The Sntp Servers Page opens
Defining Sntp Servers
Click . The Add Sntp Server Page opens
Defining Sntp Interface Settings
Click . The Add Sntp Interface Page opens
Defining Sntp Interface Settings
Define the Interface and Receive Server Updates fields
This page is left blank intentionally
Viewing Interface Statistics
Viewing Statistics
Viewing Interface Statistics
Viewing Device Interface Statistics
Receive Statistics
Transmit Statistics
Resetting Interface Statistics Counters
Open the Interface Statistics
Viewing Port Utilization Statistics
Port Utilization
Viewing Etherlike Statistics
Etherlike Statistics
Resetting Etherlike Statistics Counters
Open the Etherlike Statistics
Viewing Gvrp Statistics
Gvrp Statistics
Resetting Gvrp Statistics Counters
Open the Gvrp Statistics
Viewing EAP Statistics
EAP Statistics
DXS/DWS 3200 Series User Guide
Managing Rmon Statistics
Managing Rmon Statistics
Viewing Rmon Statistics
Rmon Statistics
Resetting Rmon Statistics Counters
Open the Rmon Statistics
Configuring Rmon History
Defining Rmon History Control
Rmon History Control Settings
Click . The Rmon History Control Settings Page opens
Viewing the Rmon History Table
Rmon History Table
Viewing Statistics
Configuring Rmon Events
Defining Rmon Events Control
Viewing Statistics
Viewing the Rmon Events Logs
Rmon Events Logs
Defining Rmon Alarms
Click Advanced Setup Rmon Alarm. The Rmon Alarm Page opens
Add Alarms Entry
Appendix A, Wlan Country Settings
Cyprus
Czech
Republic
Germany
Appendix A, Wlan Country Settings
E q u e n c y R a n g e Ireland
Israel
India
Iceland
E q u e n c y R a n g e
Korea
Lithuania
Luxembourg
Norway
New Zealand
Philippines
Poland
E q u e n c y R a n g e Sweden
Singapore
Slovenia
Slovak
America
E q u e n c y R a n g e United States
South Africa
Hardware Specifications
Appendix B, Device Specifications & Features
Appendix B, Device Specifications & Features
DXS-3227, DXS-3227P, and DXS-3250 Features
A t u r e S c r i p t i o n
Active underlying Spanning Tree Protocol Features topology
Lacp
MDI/MDIX Support
Media-Dependent Interface with Crossover Mdix
Security Global Parameters
Simple Network Management Protocol Snmp over the UDP/IP
Sntp
Based on either the Vlan tag or based on a combination
This page is left blank intentionally
Appendix B, Troubleshooting
Appendix B, Troubleshooting
Troubleshooting Solutions
Problem Management
Problems Possible Cause Solution
Troubleshooting Solutions
Console #reload
Contacting D-Link Technical Support
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Contacting D-Link Technical Support
DXS/DWS 3200 Series User Guide
Warranty
Warranty
DXS/DWS 3200 Series User Guide
Warranty
DXS/DWS 3200 Series User Guide
Product Registration
Product Registration
DXS/DWS 3200 Series User Guide
International Offices
International Offices