| Prestige 100L IDSL Router |
| standards, denoted as NI2 and NI3, are currently being developed. |
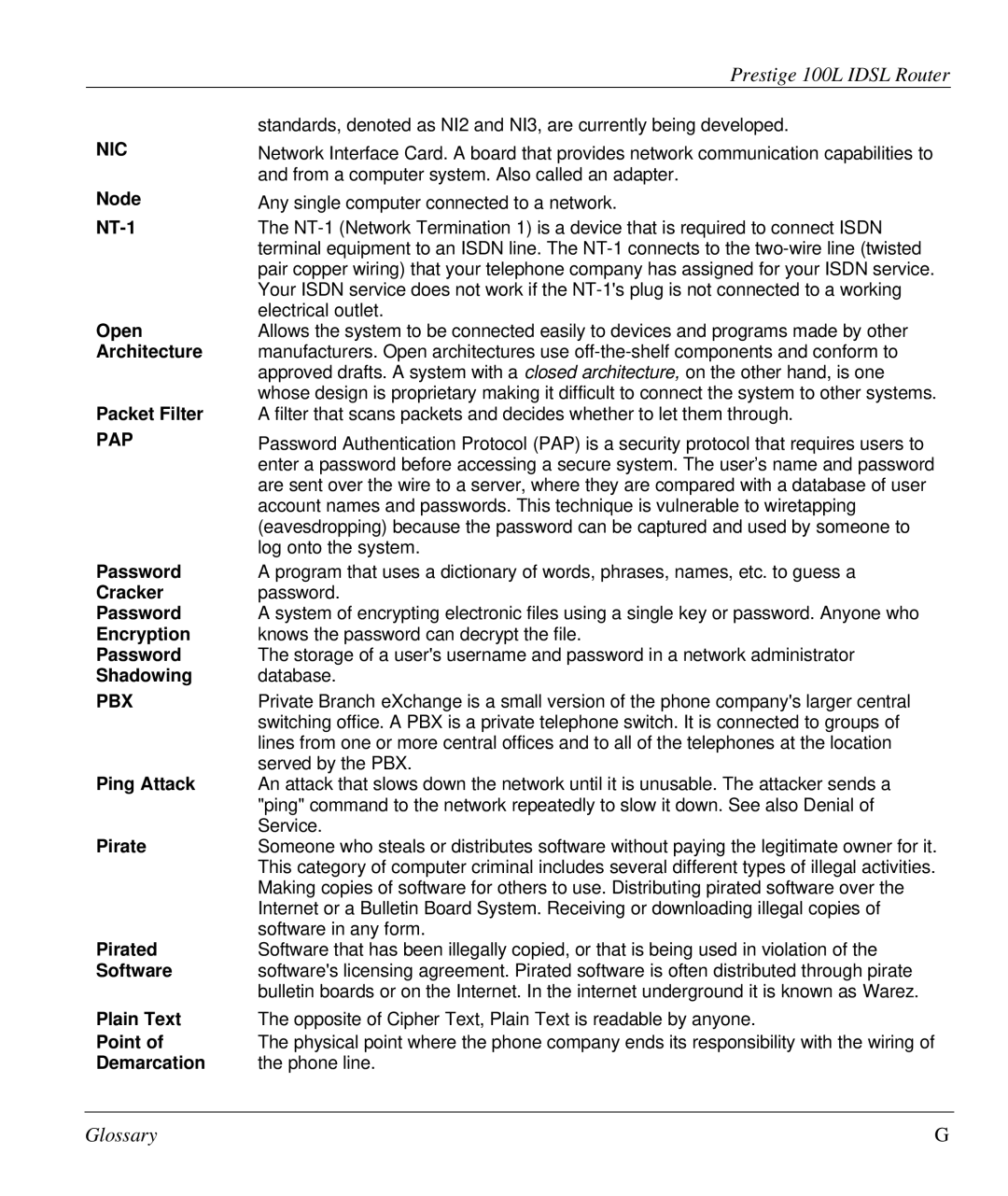
NIC | Network Interface Card. A board that provides network communication capabilities to |
| and from a computer system. Also called an adapter. |
Node | Any single computer connected to a network. |
| The |
| terminal equipment to an ISDN line. The |
| pair copper wiring) that your telephone company has assigned for your ISDN service. |
| Your ISDN service does not work if the |
Open | electrical outlet. |
Allows the system to be connected easily to devices and programs made by other | |
Architecture | manufacturers. Open architectures use |
| approved drafts. A system with a closed architecture, on the other hand, is one |
| whose design is proprietary making it difficult to connect the system to other systems. |
Packet Filter | A filter that scans packets and decides whether to let them through. |
PAP | Password Authentication Protocol (PAP) is a security protocol that requires users to |
| enter a password before accessing a secure system. The user’s name and password |
| are sent over the wire to a server, where they are compared with a database of user |
| account names and passwords. This technique is vulnerable to wiretapping |
| (eavesdropping) because the password can be captured and used by someone to |
| log onto the system. |
Password | A program that uses a dictionary of words, phrases, names, etc. to guess a |
Cracker | password. |
Password | A system of encrypting electronic files using a single key or password. Anyone who |
Encryption | knows the password can decrypt the file. |
Password | The storage of a user's username and password in a network administrator |
Shadowing | database. |
PBX | Private Branch eXchange is a small version of the phone company's larger central |
| switching office. A PBX is a private telephone switch. It is connected to groups of |
| lines from one or more central offices and to all of the telephones at the location |
Ping Attack | served by the PBX. |
An attack that slows down the network until it is unusable. The attacker sends a | |
| "ping" command to the network repeatedly to slow it down. See also Denial of |
Pirate | Service. |
Someone who steals or distributes software without paying the legitimate owner for it. | |
| This category of computer criminal includes several different types of illegal activities. |
| Making copies of software for others to use. Distributing pirated software over the |
| Internet or a Bulletin Board System. Receiving or downloading illegal copies of |
Pirated | software in any form. |
Software that has been illegally copied, or that is being used in violation of the | |
Software | software's licensing agreement. Pirated software is often distributed through pirate |
| bulletin boards or on the Internet. In the internet underground it is known as Warez. |
Plain Text | The opposite of Cipher Text, Plain Text is readable by anyone. |
Point of | The physical point where the phone company ends its responsibility with the wiring of |
Demarcation | the phone line. |
Glossary | G |