North Mathilda Avenue Sunnyvale, California
Administration Guide
Series Services Router Administration Guide
End User License Agreement
Iii
Page
Abbreviated Table of Contents
Series Services Router Administration Guide
Table of Contents
Modifying USB Modem Initialization Commands
Using the telnet Command Using the ssh Command
Viii Table of Contents
Management Information Base
Configuring Autoinstallation with a Configuration Editor
Verifying Autoinstallation Status
Event Policy Overview Configuring Event Policies
Part Monitoring a Services Router
Part Managing Services Router Software
Part Diagnosing Performance and Network Problems
Xiii
Part Index
Objectives
About This Guide
Audience
Objectives
Xvi How to Use This Guide
How to Use This Guide
Location of J-series Information
Series Tasks Location of Instruction
Document Conventions
On page xvii defines the notice icons used in this guide
Text and Syntax Conventions
Web GUI Conventions
Related Juniper Networks Documentation
Series Guides and Related Junos Software Publications
Getting Started Guide for Your Router
Related Juniper Networks Documentation
Series Services Router Administration Guide
Chapter in a J-series Guide
Xx Related Juniper Networks Documentation
Documentation Feedback
Requesting Technical Support
Documentation Feedback
Xxii Requesting Technical Support
Opening a Case with Jtac
Configuring a Services Router for Administration
Configuring a Services Router for Administration
Page
Managing User Authentication and Access
User Authentication Terms
System Management Terms
User Authentication
User Authentication Overview
User Authentication Overview
User Accounts
Login Classes
Predefined Login Classes
Permission Bits
Permission Bits for Login Classes
Template Accounts
Denying or Allowing Individual Commands
Adding a Radius Server for Authentication
Managing User Authentication with Quick Configuration
To configure a Radius server with Quick Configuration
Before You Begin
To configure a TACACS+ server with Quick Configuration
Adding a TACACS+ Server for Authentication
Users Quick Configuration for Radius Servers Summary
Radius Server
To configure system authentication with Quick Configuration
Configuring System Authentication
Users Quick Configuration for TACACS+ Servers Summary
TACACS+ Server
Add a User Quick Configuration Page Summary
To configure users with Quick Configuration
Adding New Users
User Information
Managing User Authentication with a Configuration Editor
Setting Up Radius Authentication
Managing User Authentication with a Configuration Editor
Setting Up Radius Authentication
Setting Up TACACS+ Authentication
172.16.98.24
Setting Up TACACS+ Authentication
Set tacplus-server address
Tacacssecret1
Configuring Authentication Order
Configuring Authentication Order
Insert system authentication-order radius
After password
Defining Login Classes
Controlling User Access
Defining Login Classes
EditEdit Configuration
Operator-and-boot
Operator-and-boot with
Request system reboot
Creating User Accounts
ConfigurationView
Setting Up Template Accounts
Creating User Accounts
Set user cmartin class superuser
Creating a Remote Template Account
Creating a Remote Template Account
Creating a Local Template Account
Creating a Local Template Account
Recovering the Root Password
Recovering the Root Password
Ok boot -s
Securing the Console Port
Securing the Console Port
Accessing Remote Devices with the CLI
Using the telnet Command
Securing the Console Port
Using the ssh Command
CLI telnet Command Options
CLI ssh Command Options
Configuring Password Retry Limits for Telnet and SSH Access
Configuring Password Retry Limits for Telnet and SSH Access
ConfigurationView and EditEdit Configuration
Configuring Password Retry Limits for Telnet and SSH Access
Edit system login retry-options
Set backoff-threshold
Page
Setting Up USB Modems for Remote Management
USB Modem Terms
USB Modem Terms
USB Modem Overview
USB Modem Interfaces
USB Modem Terminology
Series Default Modem Initialization Commands
How a Services Router Initializes USB Modems
Setting Up USB Modems for Remote Management
Modem Command Description S7=45
USB Modem Connection and Configuration Overview
USB Modem Connection and Configuration Overview
On the Services Router
At the User End
Connecting the USB Modem to the Services Routers USB Port
Configuring a USB Modem Interface Required
To configure a USB modem interface for the Services Router
ConfigurationView EditEdit Configuration
Configuring a USB Modem Interface
Edit interfaces umd0
S0=0 V1 X4 &C1 E0 Q0 &Q8 %C0
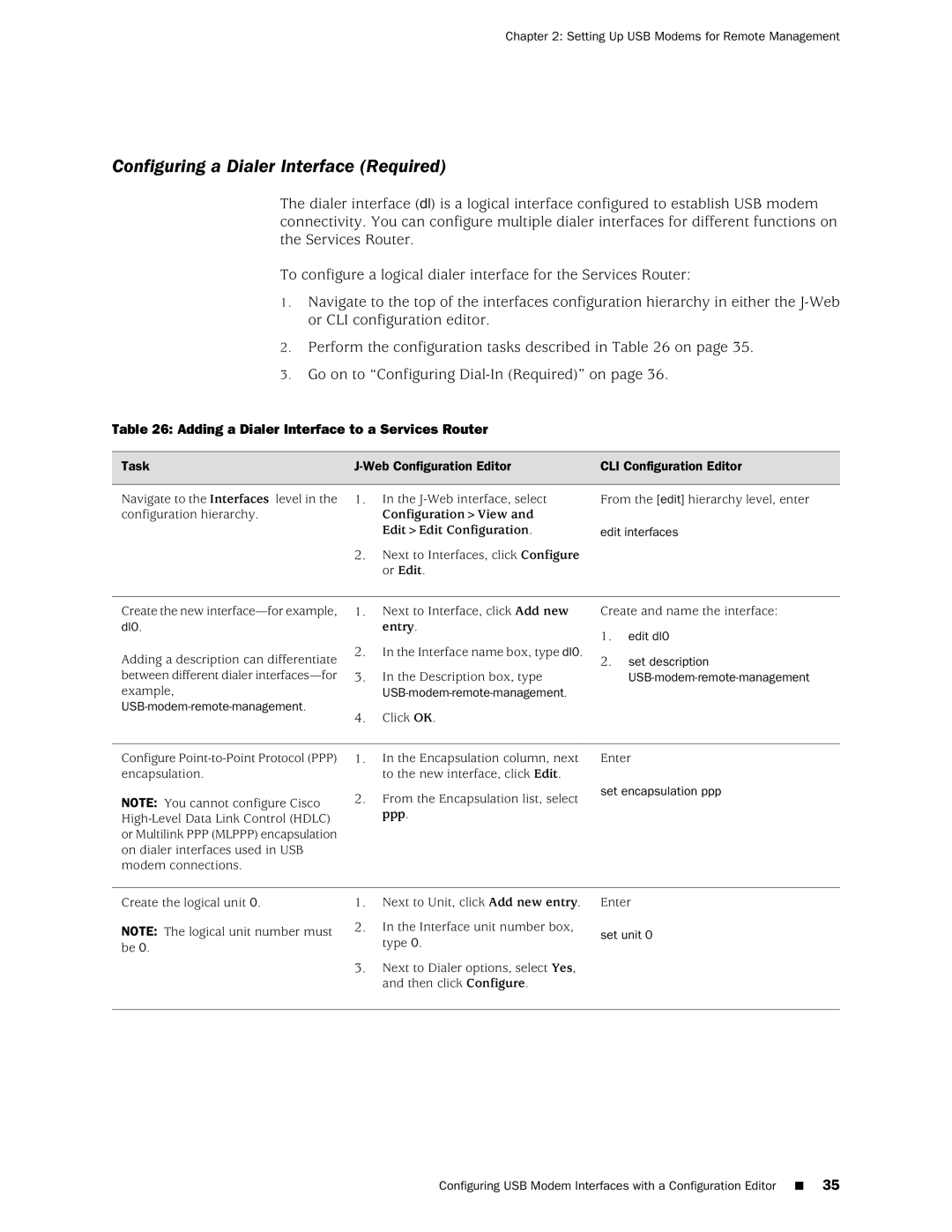
Adding a Dialer Interface to a Services Router
Configuring a Dialer Interface Required
Edit unit
Configuring Dial-In Required
172.20.10.2
172.20.10.1
Configuring Chap on Dialer Interfaces Optional
To configure Chap on the dialer interface
Configuring the Dialer Interface for Dial-In
Ppp-options chap hierarchy level Web Configuration Editor
Configuring Chap on Dialer Interfaces
Edit access
Edit interfaces dl0 unit
Configuring a Dial-Up Modem Connection at the User End
Connecting to the Services Router from the User End
Connecting to the Services Router from the User End
USB-modem-connect-and then click Next
Administering USB Modems
Connecting to the Services Router from the User End
Advanced TCP/IP Settings page appears
Administering USB Modems
Modifying USB Modem Initialization Commands
Modifying USB Modem Initialization Commands
Verifying the USB Modem Configuration
Resetting USB Modems
Modifying USB Modem Initialization Commands
Configure
Verifying a USB Modem Interface
Verifying a USB Modem Interface
Verifying Dialer Interface Configuration
Verifying Dialer Interface Configuration
Setting Up USB Modems for Remote Management
Series Services Router Administration Guide
Configuring Snmp for Network Management
Snmp Architecture
Snmp Architecture
Snmp Communities
Management Information Base
Snmp Traps
Configuring Snmp for Network Management
Spoofing Snmp Traps
Snmp Health Monitor
To configure Snmp features with Quick Configuration
Configuring Snmp with Quick Configuration
Identification
Snmp Quick Configuration Summary
Communities
Traps
Health Monitoring
Checks the following key indicators
Configuring Snmp with a Configuration Editor
Configuring Basic System Identification
Defining System Identification Information Required
Set description
Configuring Snmp Agents and Communities Required
Set name name
Select Engine id
Managing Snmp Trap Groups Required
Configuring Snmp Agents and Communities
Configuring Snmp Trap Groups
Controlling Access to MIBs Optional
Select the Authentication , Chassis ,
Click Categories
Verifying the Snmp Configuration
Verifying Snmp Agent Configuration
Configuring Snmp Views
Verifying Snmp Health Monitor Configuration
Verifying Snmp Health Monitor Configuration
Series Services Router Administration Guide
Configuring Snmp for Network Management
Page
Configuring the Router as a Dhcp Server
Dhcp Terms
Dhcp Terms
Dhcp Terms
Dhcp Overview
Conflict Detection and Resolution
Compatibility with Autoinstallation
Configuring the Router as a Dhcp Server
Dhcp Options
Configuring the Dhcp Server with Quick Configuration
Configuring the Dhcp Server with Quick Configuration
Dhcp Quick Configuration Main
Dhcp Quick Configuration Pool
Dhcp Quick Configuration Static Binding
To configure the Dhcp server with Quick Configuration
Dhcp Pool Information
Dhcp Server Quick Configuration Pages Summary
Lease Time
Server Information
Dhcp Static Binding Information
Boot Options
Sample Dhcp Server Configuration Settings
Configuring the Dhcp Server with a Configuration Editor
Settings Sample Value or Values
Dhcp Subnet Configuration
Dhcp MAC Address Configuration
Entry
Configuring the Dhcp Server
Verifying a Dhcp Server Configuration
Displaying a Dhcp Server Configuration
Ip address
Verifying the Dhcp Binding Database
Verifying the Dhcp Binding Database
Verifying Dhcp Server Operation
Verifying Dhcp Server Operation
User@host ping
Displaying Dhcp Statistics
Displaying Dhcp Statistics
Page
Autoinstallation Terms
Configuring Autoinstallation
Autoinstallation Terms
Autoinstallation
Autoinstallation Overview
Supported Autoinstallation Interfaces and Protocols
Host-specific configuration
Configuring Autoinstallation
Typical Autoinstallation Process on a New Services Router
Before You Begin
Configuring Autoinstallation with a Configuration Editor
Configuring Autoinstallation with a Configuration Editor
Verifying Autoinstallation Status
Verifying Autoinstallation
Configuring Autoinstallation
ConfigurationView and Edit Edit Configuration
Verifying Autoinstallation Status
Page
Commit Script Overview
Automating Network Operations and Troubleshooting
Var/db/scripts/commit directory
Enabling Commit Scripts
Commit the configuration
Disabling Commit Scripts
Enabling Commit Scripts
Operation Script Overview
Executing Operation Scripts
Enabling Operation Scripts
Var/db/scripts/op directory
Enabling Operation Scripts
Running Self-Diagnostics with Event Policies
Running Self-Diagnostics with Event Policies
Disabling Operation Scripts
Event Policy Overview
Configuring Event Policies
Configuring Destination for Uploading Files for Analysis
Configuring Event Policies
Configure or Edit
Configuring Event Policy
Set output-filename config.txt output-format text
Edit then execute-commands
Execute the show interfaces
Set then Set raise-trap
Page
Monitoring a Services Router
Monitoring a Services Router
Page
Monitoring Terms
Monitoring the Router and Routing Operations
Monitoring Overview
Series Monitoring Terms
Monitor Option Function
Monitoring Tools Overview
System
Chassis
Web Monitor Options and Corresponding CLI show Commands
Routing
CoS
Show services nat pool
Corresponding CLI Commands Interfaces-show mpls interface
IPSec
Rsvp Sessions-show rsvp session
Filtering Command Output
Show services rpm probe-results
PPPoE
User@host show configuration match address
Monitoring System Properties
Using the Monitoring Tools
Show system uptime Show system users Show system storage
Summary of Key System Properties Output Fields
Name-server command
Set system hostname command
Set system time-zone command
Users
CPU Usage
Monitoring System Process Information
Show system processes commands
Summary of System Process Information Output Fields
System Storage
Alarm Summary
Monitoring the Chassis
Summary of Key Chassis Output Fields
Environment Information
Field Values
Failed
Absent
FPC Summary
Monitoring the Interfaces
Summary of Key Interfaces Output Fields
Interface Summary
Down
MTU
Monitoring Routing Information
Monitoring Route Information
Show route terse Show route detail
Summary of Key Routing Information Output Fields
Show bgp summary Show bgp neighbor
Monitoring BGP Routing Information
Summary of Key BGP Routing Output Fields
BGP Summary
BGP Neighbors
Down to Up
Summary of Key Ospf Routing Output Fields
Monitoring Ospf Routing Information
Ospf Neighbors
Ospf Interfaces
Show rip statistics Show rip neighbors
Monitoring RIP Routing Information
Summary of Key RIP Routing Output Fields
Ospf Statistics
Summary of Key DLSw Routing Information Output Fields
Monitoring DLSw Routing Information
RIP Neighbors
DLSw Capabilities
DLSw Peers
DLSw Circuits
Show class-of-service
Monitoring Class-of-Service Performance
Show class-of-service interface interface
Monitoring CoS Interfaces
Monitoring CoS Classifiers
Show class-of-service classifier
Summary of Key CoS Interfaces Output Fields
Summary of Key CoS Classifier Output Fields
Monitoring CoS Value Aliases
Show class-of-service code-point-aliases
Monitoring CoS RED Drop Profiles
Show class-of-service drop-profile
Summary of Key CoS Value Alias Output Fields
Summary of Key CoS RED Drop Profile Output Fields
Monitoring CoS Forwarding Classes
Show class-of-service forwarding-class
Monitoring CoS Rewrite Rules
Show class-of-service rewrite-rules
Summary of Key CoS Forwarding Class Output Fields
Summary of Key CoS Rewrite Rules Output Fields
Show class-of-service scheduler-map
Monitoring CoS Scheduler Maps
Summary of Key CoS Scheduler Maps Output Fields
Monitoring Mpls Traffic Engineering Information
Monitoring Mpls LSP Information
Monitoring Mpls Interfaces
Show mpls interface
Show mpls lsp
Monitoring Mpls LSP Statistics
Show mpls lsp statistics
Transit
Show rsvp session
Monitoring Rsvp Session Information
Summary of Key Rsvp Session Information Output Fields
Summary of Key Mpls LSP Statistics Output Fields
Monitoring Mpls Rsvp Interfaces Information
Show rsvp interface
Summary of Key Rsvp Interfaces Information Output Fields
Static bandwidth X subscription factor
Monitoring Service Sets
Summary of Key Service Set Output Fields
Service Set Summary
Monitoring Firewalls
Summary of Key Stateful Firewall Statistics Output Fields
Monitoring Stateful Firewall Statistics
Monitoring Stateful Firewall Filters
Summary of Key Stateful Firewall Filters Output Fields
Bytes
Monitoring Firewall Intrusion Detection Services IDS
IDS Search-Narrowing Characteristics
Narrow Search Box Entry or Selection
On page 140 summarizes key output fields in IPSec displays
Monitoring IPSec Tunnels
Summary of Key Firewall IDS Output Fields
Summary of Key IPSec Output Fields
AH+ESP
IPSec Statistics
IKE Security
Hmac-sha1
Monitoring NAT Pools
Monitoring Dhcp
Show services nat pool
On page 143 summarizes key output fields in NAT displays
Summary of Key NAT Output Fields
Dhcp Statistics
Dhcp Conflicts
Monitoring RPM Probes
Show services rpm probe-results
On page 145 summarizes key output fields in RPM displays
Summary of Key RPM Output Fields
Round-Trip Time for a Probe
RTT
Cumulative Jitter for a Probe
Monitoring PPP
Monitoring PPPoE
Summary of Key PPPoE Output Fields
PPPoE Interfaces
PPPoE Statistics
PPPoE Version
Monitoring the TGM550 Media Gateway VoIP
Summary of Key Media Gateway Information Output Fields
Dynamic Call Admission Control Information
Telephony Gateway Module Information
DSP
Page
Monitoring Events and Managing System Log Files
System Log Message Terms
System Log Message Terms
System Log Messages Overview
System Log Message Destinations
System Log Facilities and Severity Levels
System Logging Facilities
System Logging Severity Levels
Regular Expressions
Regular Expression Operator Matching Terms
Common Regular Expression Operators and the Terms They Match
Sending System Log Messages to a File
Configuring System Log Messages with a Configuration Editor
Sending System Log Messages to a File
Edit system syslog
Archiving System Logs
Sending System Log Messages to a User Terminal
Sending Messages to a User Terminal
Set user frank any critical
Monitoring System Log Messages with the J-Web Event Viewer
Disabling System Logs
Filtering System Log Messages
Filtering System Log Messages
Installation and Upgrade Guide
CLI command-show system processes
Viewing System Log Messages
Viewing System Log Messages
Alarm Terms
Configuring and Monitoring Alarms
Alarm Types
Alarm Overview
Alarm Terms
Interface alarm
Alarm Conditions
Alarm Severity
Interface Alarm Conditions
Configuring and Monitoring Alarms
Interface Alarm Conditions
Pic-reset
Pic-hold-reset
Hw-down
Linkdown
Chassis Alarm Conditions and Corrective Actions
Chassis Alarm Conditions and Corrective Actions
Component Alarm Conditions
Corrective Action Alarm Severity
System Alarm Conditions and Corrective Actions
Configuring Alarms with a Configuration Editor
System Alarm Conditions and Corrective Actions
Alarm Type Alarm Condition Corrective Action
Configuring Interface Alarms
Show chassis alarms Show system alarms
Checking Active Alarms
On page 174 summarizes the output fields on the alarms
Summary of Key Alarm Output Fields
Displaying Alarm Configurations
Verifying the Alarms Configuration
To verify alarms configuration, perform the following task
Edit User@host# show chassis alarms t3
Displaying Alarm Configurations
Managing Services Router Software
Managing Services Router Software
Page
Performing Software Upgrades and Reboots
Upgrade and Downgrade Overview
Upgrade and Downgrade Overview
Recovery Software Packages
Upgrade Software Packages
Downloading Software Upgrades from Juniper Networks
Secondary Storage Devices for Backup
Performing Software Upgrades and Reboots
Installing Software Upgrades with the J-Web Interface
Installing Software Upgrades from a Remote Server
Installing Software Upgrades with the J-Web Interface
Installing Software Upgrades by Uploading Files
Install Remote Summary
Upload Package Summary
Installing Software Upgrades with the CLI
Installing Software Upgrades with the CLI
User@host request system software add unlink no-copy source
Var/tmp/junos-j-series8.5R2.1.tar.gz
Downgrading the Software with the J-Web Interface
Downgrading the Software
Downgrading the Software with the CLI
Downgrading the Software
User@host request system reboot
Configuring Boot Devices
Configuring Boot Devices
User@host request system software rollback
Snapshot Summary
Click OK
Partitions the boot medium
CLI request system snapshot Command Options
Configuring a Boot Device for Backup with the CLI
Option Description Partition
Root-size size
Swap-size size
Recovering Primary Boot Devices
Why Compact Flash Recovery Might Be Necessary
CLI set system dump-device Command Options
Configuring Internal Compact Flash Recovery
Recommended Recovery Hardware and Software
Recommended Recovery Hardware and Software
Recovery Hardware
\ physdiskwrite -u junos-jseries-7.0-20041028.0-export-cf512
Rebooting or Halting a Services Router
Rebooting or Halting a Services Router
Rebooting a Services Router with the CLI
CLI Request System Reboot Command Options
Option Description
CLI Request System Halt Command Options
Halting a Services Router with the CLI
This option is a synonym for the at + minutes option
Page
Cleaning Up Files
Managing Files
Managing Files with the J-Web Interface
Managing Files with the J-Web Interface
Downloading Files
Cleaning Up Files with the CLI
Deleting the Backup Software Image
Deleting the Backup Software Image
Managing Files
Managing Accounting Files
Managing Accounting Files
Encrypting and Decrypting Configuration Files
Encrypting and Decrypting Configuration Files
Gz.jc-for example, juniper.conf.gz.jc
Request system set-encryption-key Commands
Encrypting Configuration Files
CLI Command Description
For example
To begin the encryption process, commit the configuration
Decrypting Configuration Files
To begin the decryption process, commit the configuration
Modifying the Encryption Key
At the second prompt, reenter the new encryption key
Diagnosing Performance and Network Problems
Diagnosing Performance and Network Problems
Page
Using Services Router Diagnostic Tools
Diagnostic Terms
Series Diagnostic Terms
Diagnostic Tools Overview
Web Diagnostic Tools Overview
Web Interface Diagnose and Manage Options
Manage Options
CLI Diagnostic Commands Overview
Diagnosis and Troubleshooting
CLI Diagnostic Command Summary
Mpls Connection Checking
Command Function Start
Options for Checking Mpls Connections
Quit
Ping LSP to Layer Ping mpls l3vpn
Locate LSP using
VPN prefix
Interface name Instance to which this
General Preparation
Mpls Enabled
Ping Mpls Preparation
Loopback Address
Pinging Hosts from the J-Web Interface
Using the J-Web Ping Host Tool
Web Ping Host Field Summary
Pinging Hosts from the J-Web Interface
Ping Host Results
Web Ping Host Results and Output Summary
Ping Host Results and Output Summary
Ping Host Result
Icmpseq=0 Icmpseq=number
Using the J-Web Ping Mpls Tool
Checking Mpls Connections from the J-Web Interface
Checking Mpls Connections from the J-Web Interface
Locate LSP using interface name
Ping LDP-signaled LSP
Web Ping Mpls Field Summary
Ping LSP to Layer 3 VPN prefix
Locate LSP from interface name
Instance to which this connection belongs
Locate LSP from virtual circuit information
Ping end point of LSP
Web Ping Mpls Results and Output Summary
Ping Mpls Results and Output
Field Description
Time
Tracing Unicast Routes from the J-Web Interface
Using the J-Web Traceroute Tool
To use the traceroute tool
Tracing Unicast Routes from the J-Web Interface
Traceroute Field Summary
Traceroute
Web Traceroute Results and Output Summary
Traceroute Results and Output Summary
Capturing and Viewing Packets with the J-Web Interface
Using J-Web Packet Capture
To use J-Web packet capture
Capturing and Viewing Packets with the J-Web Interface
Packet Capture Field Summary
Ge-0/0/0
Advanced Options
Addresses Into hostnames in the packet headers displayed
Web Packet Capture Results and Output Summary
Packet Capture Results and Output Summary
To quit the ping command, press Ctrl-C
Using CLI Diagnostic Commands
CLI ping Command Options
Pinging Hosts from the CLI
Do-not-fragment
Checking Mpls Connections from the CLI
Following is sample output from a ping command
Following is sample output from a ping mpls command
Pinging RSVP-Signaled LSPs and LDP-Signaled LSPs
Following is sample output from a ping mpls l3vpn command
CLI ping mpls l3vpn Command Options
Pinging Layer 3 VPNs
Following is sample output from a ping mpls l2vpn command
CLI ping mpls l2vpn Command Options
Pinging Layer 2 VPNs
Pinging Layer 2 Circuits
CLI ping mpls l2circuit Command Options
To quit the traceroute command, press Ctrl-C
Using the traceroute Command
CLI traceroute Command Options
Tracing Unicast Routes from the CLI
Following is sample output from a traceroute command
Using the traceroute monitor Command
Gateway address
Inet6
To quit the traceroute monitor command, press Q
CLI traceroute monitor Command Options
On page 240 summarizes the output fields of the display
Tracing Multicast Routes from the CLI
CLI traceroute monitor Command Output Summary
Using the mtrace from-source Command
On page 243 summarizes the output fields of the display
CLI mtrace from-source Command Options
CLI mtrace from-source Command Output Summary
Using the mtrace monitor Command
Displaying Log and Trace Files from the CLI
CLI mtrace monitor Command Output Summary
Monitoring Interfaces and Traffic from the CLI
Using the monitor interface Command
CLI monitor interface Output Control Keys
CLI monitor interface traffic Output Control Keys
User@host monitor interface fe-0/0/0
Using the monitor traffic Command
CLI monitor traffic Command Options
Option Description Brief
CLI monitor traffic Match Conditions
Extensive
Match Condition Description
Directional
Arithmetic Operator
CLI monitor traffic Logical Operators
Binary Operator
Relational Operator
Following is sample output from the monitor traffic command
Page
Configuring Packet Capture
Packet Capture Terms
Packet Capture Terms
Packet Capture Terms
Packet Capture Overview
Configuring Packet Capture
Packet Capture on Router Interfaces
Firewall Filters for Packet Capture
Analysis of Packet Capture Files
Packet Capture Files
Enabling Packet Capture Required
Configuring Packet Capture with a Configuration Editor
Navigate to the Forwarding options
Enabling Packet Capture
Configuring a Firewall Filter for Packet Capture Optional
Configuring Packet Capture on an Interface Required
Configuring Packet Capture on an Interface
259
Configuring a Firewall Filter for Packet Capture
Edit firewall
192.168.1.1/32
Disabling Packet Capture
Enter set packet-capture disable
Deleting Packet Capture Files
261
User@host start shell
Return to the CLI operational mode
Cd /var/tmp
Rm pcap-file.fe.0.0.0
Verifying Packet Capture
Displaying a Packet Capture Configuration
Mv pcap-file.fe.0.0.0 pcap-file.fe.0.0.0.chdsl
Verifying Packet Capture
Verifying Captured Packets
Ftp lcd /var/tmp Local directory now /cf/var/tmp
Return to the CLI configuration mode
Ftp bye Goodbye Edit User@host#
Verifying Captured Packets
Meaning Verify that the output shows the intended packets
RPM Terms
Configuring RPM Probes
RPM Probes
RPM Overview
RPM target
RPM test
RPM Tests
Configuring RPM Probes
Probe and Test Intervals
Jitter Measurement with Hardware Timestamping
RPM Statistics
RPM Statistics
Round-Trip Times
Inbound and Outbound Times Icmp Timestamp Probes Only
Configuring RPM with Quick Configuration
RPM Thresholds and Traps
RPM for BGP Monitoring
RPM Quick Configuration Summary
Configuring RPM with Quick Configuration
Performance Probe Owners
Router Advanced WAN Access Configuration Guide
Maximum Probe Thresholds
Generates Snmp traps when the threshold for standard
Configuring Basic RPM Probes
Configuring RPM with a Configuration Editor
Configuring RPM with a Configuration Editor
Performance Probe Server
Edit services rpm
Configuring Basic RPM Probes
Click Configure
Set probe customerA
192.178.16.5
Edit services rpm probe customerA
Set test icmp-test probe-frequency
Set test icmp-test probe-type icmp-ping-timestamp
Configuring TCP and UDP Probes
Router a Configuration
Configuring TCP and UDP Probes
Router B Configuration
Tuning RPM Probes
Tuning RPM Probes
CustomerA
Set probe-limit
Configuring RPM Probes for BGP Monitoring
Configuring RPM Probes to Monitor BGP Neighbors
Configuring RPM Probes to Monitor BGP Neighbors
Directing RPM Probes to Select BGP Routers
Verifying an RPM Configuration
Directing RPM Probes to Select BGP Routers
Add new entry
Verifying RPM Services
Verifying RPM Services
Verifying RPM Statistics
Verifying RPM Statistics
Verifying RPM Probe Servers
Verifying RPM Probe Servers
Index
Index on
Index
Series Services Router Administration Guide Index
Symbols
112
Chassis
Dd utility, for compact flash recovery 192
Snmp health monitor System logs
Dhcp
Snmp
Junos Internet software
Diagnosing problems from 210 Monitoring from 102
See also Snmp
Permissions
Radius
CLI
See also RPM probes Preparation
Serial number Chassis components
BGP
TACACS+
Routing Engine, too warm
Upgrades
Version Hardware, displaying