MVP-8400i
AMX Limited Warranty and Disclaimer
AMX Software License and Warranty Agreement
FCC Information
Table of Contents
Upgrading MVP Firmware
EAP Security & Server Certificates
Commands
Text Effects Names 126 Button Query Commands 127
Panel Runtime Operations 137
Embedded codes 143 Panel Setup Commands 144
Appendix a Text Formatting 157
Appendix B Wireless Technology 163
Page
Overview
MVP-8400i Touch Panel
Specifications
MVP-8400i Specifications FG5965-04
MVP-8400i LCD
Weight
Specifications
Active Screen Area
Other AMX Equipment
Included Accessories
FG2255-07
MVP-BP Specifications
MVP-BP Power Pack
Installing MVP-BP Batteries
MVP-BP Specifications
If you are only using one battery, use Battery Slot #1
Optional Compact Flash Upgrades
Installing the NXA-CFSP Compact Flash Card
Accessing the MVP’s Internal Components
NXA-CFSP Compact Flash
Removing the Installed Card
Installing the Compact Flash Upgrade Card
Removing/installing a Compact Flash Memory card
Page
Panel Calibration
Calibrating the MVP Panels
Testing your Calibration
If Calibration Is Not Working
Modero Setup and System Settings
Configuring Communications
Wireless Settings Page Wireless Access Overview
Configure the Panel’s Wireless IP Settings
Configuring a Wireless Network Access
Wireless communication using a Dhcp Address
Wireless communication using a Static IP Address
Wireless Settings page IP Settings section
Simple versus Enterprise Configuration
Wireless Security Simple Mode window
Wireless Security Enterprise Mode window
Using the Site Survey tool
Wireless Site Survey
Configure the Card’s Wireless Security Settings
Configuration to a target WAP
Site Survey of available Waps Unsecured WAP shown selected
Automatically set Ssid
Manually set Ssid
Wireless Security Simple Mode window
WEP Key # Keyboard
Choose a Master Connection Mode
Protected Setup Select System Settings
System Settings page USB Connection
Configure a Virtual NetLinx Master using NetLinx Studio
Assigning Communication Settings for a Virtual Master
Master Connection to a Virtual Master via Ethernet
Mode Description Procedures
Ethernet
Connection Modes
These must match
Using G4 Web Control to Interact with a G4 Panel
G4 Web Control
Configuring Communications
Using your NetLinx Master to control the G4 panel
Web Control VNC installation and Password entry screens
Upgrading MVP Firmware
Upgrading the Modero Firmware via the USB port
Configure the panel for a USB Connection Type
Prepare Studio for communication via the USB port
Confirm and Upgrade the firmware via the USB port
Default Modero panel value is
Upgrading the Docking Station Firmware via USB
Prepare the Docking Station for firmware transfer via USB
Upgrade the Docking Station firmware via USB
Batteries
Device and System values
Upgrading MVP Firmware
Page
Setup Pages
Navigation Buttons
WiFi/Wired icon
Setup Pages
Setup
Navigation Buttons
Protected Settings
Information
Project Information
Project Information
Panel Information
Panel Information
RAM
Time Date Refresh/Set
Time & Date Settings
Time & Date Settings
Time Display fields
Audio Settings
Audio Settings
Set Date/Time
WAV files Supported sample rates
Supported WAV Sample Rates
Battery Settings
Battery Settings
Limit
Status Battery Dock 2 Charge
Low Battery Warning
Battery Dock 1 Charge
Battery Level Port
Protected Setup Pages
Protected Setup
Device Information
System Recovery
Reboot / Shutdown
Docking Station
Protected Setup Navigation Buttons
SIP
System Settings Page Elements
System Settings
Master Connection
System Settings
Wireless Settings
Wireless Settings
IP Settings
Network Name Ssid WAP names
Access Point MAC
Address
Simple/Enterprise
Wireless Security Simple Mode
Ssid
Identity
Wireless Security Enterprise Mode
Anon. Identity
Wireless Settings
Wireless Security Support
Open Settings
Open Settings
WEP Settings
WEP Settings
Generate Passphrase
Encryption key
WPA-PSK Settings
WPA-PSK Settings
EAP-LEAP Settings
EAP-LEAP Settings
Anonymous Identity
EAP-FAST Settings
EAP-FAST Settings
Automatic PAC
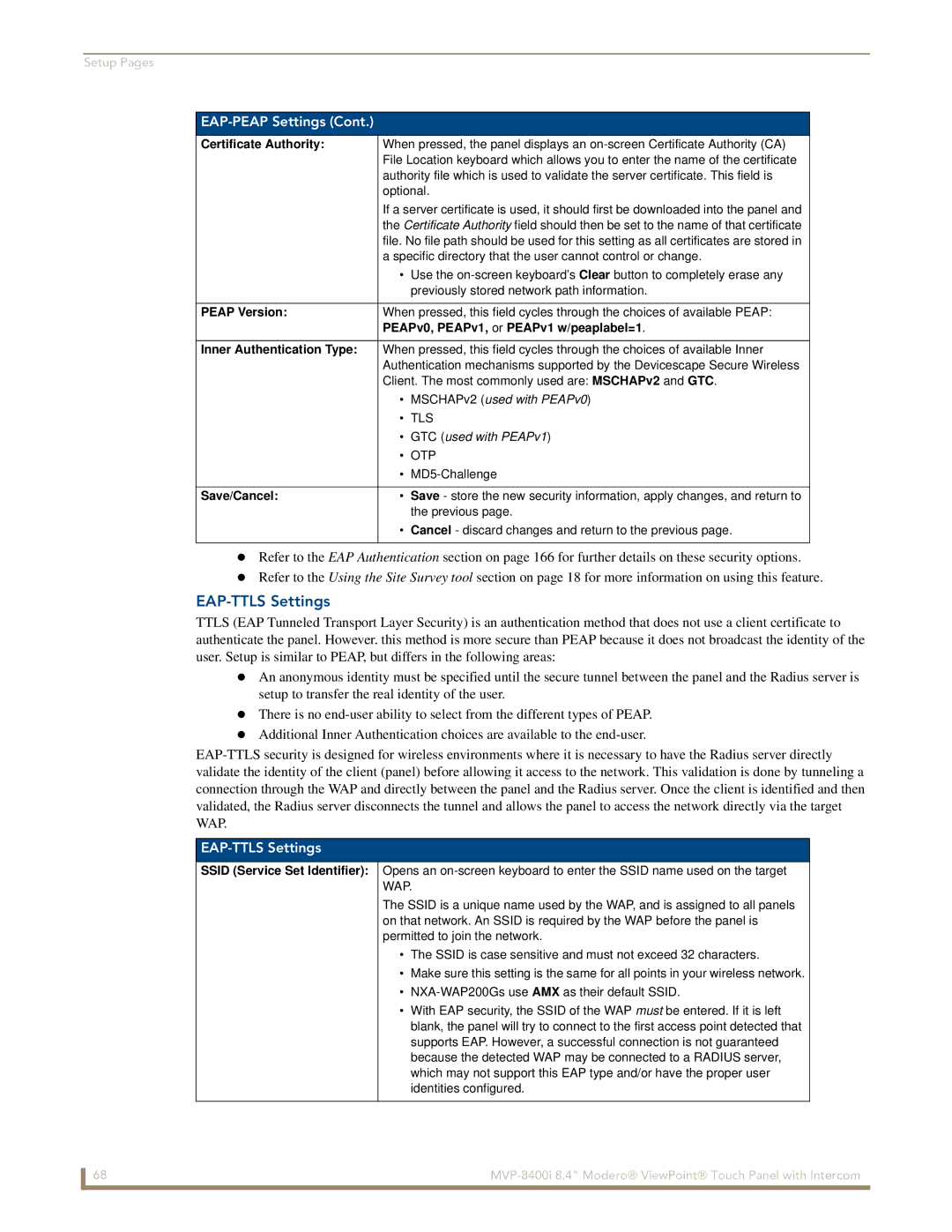
EAP-PEAP Settings
EAP-PEAP Settings
Been Disabled
Inner Authentication Type
EAP-TTLS Settings
EAP-TTLS Settings
Ssid Service Set Identifier
MSCHAPv2 default because its the most common
EAP-TLS Settings
EAP-TLS Settings
Certificates and their Extensions
Client certificate configuration
Client Certificate Configuration
Certificate Types Supported by the Modero Firmware
Calibrate
Calibration
G4 Web Control Settings
G4 Web Control Settings
G4 Web Control
Cache Settings
Other Settings
G4 Web Control Timeout
Cache Settings Page Elements
Image Cache Settings
Clearing the image cache
Setting the image cache
Checking image cache status
Panel Password
Password Settings
Password Settings
Change
SIP Settings
User Access
SIP Settings
Tools
Panel Connection Logs
Clearing the Panel Connections Log
Checking the Panel Connection Logs
Refreshing the Panel Connections Log
Panel Connection Logs
Panel Statistics
Panel Statistics
Clearing the Panel Statistics
Checking the Panel Statistics
Refreshing the Panel Statistics
Connection Utility
Connection Utility
Using the Connection Utility
WAP MAC
EAP Security & Server Certificates
EAP-TTLS EAP-TLS
Page
Setting the Intercom Session Timeout
Panel Intercom Configuration
Setup
Full Duplex Intercom
Advanced Setup
Setting Intercom Auto Answer
Allowing a panel to be monitored
Allowing a panel to monitor
Naming a panel
Sample Intercom
Sample Intercom
Name Description Channel Address Level PortCode
Panel Directory Room Name Name of a panel
Answering an incoming call
Answer Call
More Time Popup
Advanced Setup
Creating Intercom Pages
Answer Intercom Call Popup
Page
Programming
Commands
Commands
Button Assignments
@PHE
@DPG
@PDR
@PHP
@PPA
@PPT
@PPM
@PPN
@PPX
@PST
@PSP
Ppof
Ppog
Ppon
RGB Values for all 88 Basic Colors
Programming Numbers
RGB triplets and names for basic 88 colors
Index No Name Red Green Blue
102 MVP-8400i 8.4 Modero ViewPoint Touch Panel with Intercom
Font Styles and ID Numbers
Default Font Styles and ID Numbers
Font ID # Font type Size
TPD4 Border Styles by Name
Border Styles and Programming Numbers
Border Styles and Programming Numbers
Border styles
MVP-8400i 8.4 Modero ViewPoint Touch Panel with Intercom 105
ANI
Button Commands
Button Commands
APF
BAU
BAT
BCB
BCT
BCF
BDO
Entry is required
BFB
BIM
BLN
Sendcommand Panel,BMC-150,1,1,315,1,%BR%FT%TX%BM%IC%CF%CT
BMC
BMF
BMF-vt addr range,button states range,data
Cont
BML
BMI
BMP
BNP
BNC
BNN
BNT
BPP
BOR
BOS
BRD
BSO
BSF
BSM
BSP
BVT
BVN
BVP
BWW
ENA
DPF
DTO
FON
GLH
GDI
GIV
GLL
GSN
GRU
GSC
ICO
JSB
IRM
JSI
MDC
JST
MBT
RSS
STO
SKT
SHO
TEC
UNI
TOP
TXT
VTP
Miscellaneous MVP Strings back to the Master
MVP Panel Lock Passcode commands
MVP Panel Lock Passcode Commands
MVP Strings to Master
Text Effects Names
Text Effects
Button Query Commands
Custom Event Fields
?BCB
Button Query Commands
?BCF
?BCT
?BMP
?BRD
?BOP
?BRT
?DTO
?BWW
?CHR
?FBC
?FON
?ICO
?JSB
?JSI
?MAC
?JST
?LOG
?MUT
?STO
?STA
?TEC
?TEF
Send Command Panel,?TEF-529,1
Send Command Panel,?TXT-529,1
?TEF-vt addr range,button states range
Panel Runtime Operation Commands
Panel Runtime Operations
@AKR
Akeyr
@AKP
Beep
Pkeyp
Setup
@EKP
@PKP
@SST
@SOU
@SSL
@SWK
Input Commands
Input Commands
MPS
VKS
Embedded Codes
Embedded codes
Decimal numbers Hexidecimal values Virtual keystroke
Panel Setup Commands
Panel Setup Commands
ICM-TALK
Cfsm
CEX
ICM-LISTEN
MUT
ICM-SPEAKERLEVEL
ICM-MICLEVEL
@PWD
Dynamic Image Commands
Dynamic Image Commands
RMF
RAF, RMF Embedded Codes
RAF, RMF Embedded Codes
RSR
Escape Sequences
Escape Sequences
Intercom Commands
Intercom Commands
SIP Commands
SIP Commands
PHN-REDIAL
Msgwaiting
PHN-PRIVACY
Transferred
PHN-HANGUP
?PHN
PHN-DTMF
PHN-HOLD
SIP Setup Commands
’PHN-SETUP-USERNAME,username’
PHN-SETUP Username
Sendcommand Panel,’PHN-SETUP-USERNAME,6003’
Page
Bargraph Text Code Inputs
Appendix a Text Formatting
Text Formatting Codes for Bargraphs/Joysticks
Formatting Code Operations
Character Types
Text Area Input Masking
Input mask character types
Character Masking Rule
Input mask operations
Input mask ranges
Input mask next field characters
Input mask literals
Output Examples
Input mask output examples
Common Name Input Mask
URL Resources
Special escape sequences
Page
Overview of Wireless Technology
Appendix B Wireless Technology
Terminology
CERTIFICATES CA
MVP-8400i 8.4 Modero ViewPoint Touch Panel with Intercom 165
EAP Method Characteristics
EAP Authentication
EAP characteristics
Method Credential Type Authentication
AMX Certificate Upload Utility
Setup the Panel and PC for USB Communication
Configuring your G4 Touch Panel for USB Communication
Confirm the Installation of the USB Driver on the PC
How to Upload a Certificate File
Erasing All Certificates From the Touch Panel
Appendix C Troubleshooting
USB
Using USB for Virtual Master communication NetLinx Studio
Checking AMX Usblan Device Connections via NetLinx Studio
Connection Status
USB Driver
Panel Not in Listed as a Connected Device
Panel Doesn’t Respond to Touches
MVP Can’t Obtain a Dhcp Address
Batteries Will Not Hold or Take a Charge
Modero Panel Isn’t Appearing in The Online Tree Tab
My WEP Doesn’t Seem to Be Working
Can’t Connect to a NetLinx Master
NetLinx Studio Only Detects One of My Connected Masters
Only One Modero Panel in My System Shows Up
Panel Fails to Charge in MVP-WDS
Page
It’s Your World Take Control