NETGEAR, Inc
Bestätigung des Herstellers/Importeurs
Trademarks
Statement of Conditions
EU Regulatory Compliance Statement
Terms
Voluntary Control Council for Interference Vcci Statement
Additional Copyrights
AES
MD5
Product Name
Product and Publication Details
Model Number
Publication Date September Product Family
V1.0, September
Contents
Classical Routing UTM10 and UTM25
Configuring Secondary WAN Addresses
Chapter LAN Configuration
Chapter Content Filtering and Optimizing Scans
Chapter Virtual Private Networking Using SSL Connections
Changing Passwords and Administrator Settings
Features That Reduce Traffic
Features That Increase Traffic
Using QoS and Bandwidth Assignment to Shift the Traffic Mix
Configuring and Activating Firewall Logs
Configuring Logging, Alerts, and Event Notifications
Configuring the E-mail Notification Server
Configuring and Activating System, E-mail, and Syslog Logs
Problems with Date and Time
Testing the LAN Path to Your UTM
Testing the Path from Your PC to a Remote Device
Restoring the Default Configuration and Password
Appendix D Two Factor Authentication
Xvi
Conventions, Formats, and Scope
About This Manual
Revision History
How to Print This Manual
Chapter Introduction
Key Features and Capabilities
Advanced VPN Support for Both IPsec and SSL
Stream Scanning for Content Filtering
Powerful, True Firewall
Autosensing Ethernet Connections with Auto Uplink
Security Features
Extensive Protocol Support
Easy Installation and Management
Maintenance and Support
Service Registration Card with License Keys
Hardware Features
Package Contents
Right WAN LEDs LEDs
Power LED
USB port Left LAN LEDs
Active
WAN Ports
Object Activity Description LAN Ports
DMZ LED
Receptacle
Security lock Console port Reset button AC power Receptacle
Rear Panel
Bottom Panel With Product Label
4shows the product label for the UTM10
Choosing a Location for the UTM
Using the Rack-Mounting Kit
Understanding the Steps for Initial Connection
Using the Setup Wizard to Provision the UTM in Your Network
Qualified Web Browsers
Logging In to the UTM
V1.0, September
V1.0, September
Understanding the Web Management Interface Menu Layout
V1.0, September
Using the Setup Wizard to Perform the Initial Configuration
Setup Wizard of 10 LAN Settings
Dhcp
Setup Wizard LAN Settings
Setting Description or Subfield and Description
Setting Description or Subfield and Description DNS Proxy
Setup Wizard of 10 WAN Settings
ISP Type
Setup Wizard WAN Settings
Setting Description or Subfield and Description ISP Login
Get Automatically from ISP radio button
Internet IP Address
ISP
Domain Name Server DNS Servers
Setup Wizard of 10 System Date and Time
Adjust for Daylight Savings Time checkbox
Setup Wizard System Date and Time Settings
Setup Wizard of 10 Security Services
Peer-to-Peer P2P
Setup Wizard Security Services Settings
Web
Instant Messaging
Setting Description or Subfield and Description Action
Setup Wizard of 10 Email Security
Setup Wizard Email Security Settings
Scan Exceptions
Setup Wizard of 10 Web Security
See Performance Management on
Setup Wizard Web Security Settings
Setup Wizard of 10 Web Categories to Be Blocked
Blocked Categories Time of Day
Setup Wizard Content Filtering Settings
Blocked Categories Scheduled Days
Administrator Email Notification Settings
Setup Wizard Administrator Email Notification Settings
Setup Wizard of 10 Security Subscription Update Settings
Https Proxy Settings
Setup Wizard Security Subscription Update Settings
Update Settings
Update Frequency
Testing Http Scanning
Verifying Proper Installation
Setup Wizard of 10 Saving the Configuration
Testing Connectivity
Registering the UTM with Netgear
Click Register
What to Do Next
V1.0, September
Understanding the Internet and WAN Configuration Tasks
Manually Configuring Internet and WAN Settings
Automatically Detecting and Connecting
Configuring the Internet Connections
V1.0, September
Pptp
Internet connection methods
Connection Method Data Required
Manually Configuring the Internet Connection
Setting the UTM’s MAC Address
V1.0, September
Pptp and PPPoE Settings
Internet IP Address Settings
DNS Server Settings
Classical Routing UTM10 and UTM25
Network Address Translation UTM10 and UTM25
Configuring Auto-Rollover Mode UTM25 Only
Setting Description or Subfield and Description Port Mode
Auto-Rollover Mode Settings UTM25 Only
WAN2
Configuring the Internet Connections on
WAN1
V1.0, September
Using the Services menu see Services-Based Rules on
Protocol Binding Settings UTM25 Only
Destination
Configuring Secondary WAN Addresses
V1.0, September
Select Network Config Dynamic DNS from the menu
Configuring Dynamic DNS
V1.0, September
WAN2 Dynamic DNS Status
DNS Service Settings
Configuring Advanced WAN Options
Port Speed
Advanced WAN Settings
Setting Description or Subfield and Description MTU Size
Use Default Address radio button
Upload/Download Settings
Additional WAN-Related Configuration Tasks
Managing Virtual LANs and Dhcp Options
Chapter LAN Configuration
Managing the UTM’s Port-Based VLANs
V1.0, September
Dhcp Server
Vlan Dhcp Options
DNS Proxy
Dhcp Relay
Edit Add
Configuring a Vlan Profile
Ldap Server
V1.0, September
Vlan
Vlan Profile Settings
Vlan ID
Port Membership
Address Contiguous addresses in the IP address pool. Any
Settings below
Configuring Multi-Home LAN IPs on the Default Vlan
Managing Groups and Hosts LAN Groups
Managing the Network Database
V1.0, September
Adding PCs or Devices to the Network Database
Add Known PCs and Devices Settings
Setting Up Address Reservation on
Editing PCs or Devices in the Network Database
Changing Group Names in the Network Database
Setting Up Address Reservation
Configuring and Enabling the DMZ Port
V1.0, September
DMZ Setup Settings
Own LAN IP address as the primary DNS server IP address
Managing Routing
Configuring Static Routes
Static Route Settings
Configuring Routing Information Protocol RIP
Select Network Configuration Routing from the menu
Out Only .
RIP Configuration Settings
Authentication for RIP-2B/2M
Static Route Example
V1.0, September
About Firewall Protection
Chapter Firewall Protection
Administrator Tips
Number of Supported Firewall Rule Configurations
Using Rules to Block or Allow Specific Kinds of Traffic
Services-Based Rules
Outbound Rules Service Blocking
Hosts LAN Groups on
Customized Services on
Outbound Rules Overview
To Block or Allow Specific Traffic on
NAT IP
Inbound Rules Port Forwarding
V1.0, September
Inbound Rules Overview
By this rule. The options are
Order of Precedence for Rules
Setting LAN WAN Rules
LAN WAN Outbound Services Rules
LAN WAN Inbound Services Rules
Setting DMZ WAN Rules
V1.0, September
DMZ WAN Outbound Services Rules
DMZ WAN Inbound Services Rules
Setting LAN DMZ Rules
LAN DMZ Outbound Services Rules
Attack Checks
LAN DMZ Inbound Services Rules
Attack Checks Settings
L2TP
VPN Pass through
Setting Session Limits
Managing the Application Level Gateway for SIP Sessions
Session Limit Settings
Session Timeout
LAN WAN Inbound Rule Hosting a Local Public Web Server
Inbound Rules Examples
V1.0, September
V1.0, September
LAN WAN or DMZ WAN Inbound Rule Specifying an Exposed Host
LAN WAN Outbound Rule Blocking Instant Messenger
Outbound Rules Example
Adding Customized Services
Creating Services, QoS Profiles, and Bandwidth Profiles
V1.0, September
TCP
Services Settings
Creating Quality of Service QoS Profiles
V1.0, September
Default High Medium High Low
QoS Profile Settings
Creating Bandwidth Profiles
V1.0, September
Bandwidth Profile Settings
Setting a Schedule to Block or Allow Specific Traffic
Enabling Source MAC Filtering
V1.0, September
Setting up IP/MAC Bindings
IP/MAC Bindings
IP/MAC Binding Settings
Event Notifications on
Configuring Port Triggering
V1.0, September
10. Port Triggering Settings
Using the Intrusion Prevention System
V1.0, September
V1.0, September
Misc
11. IPS Less Familiar Attack Names
Attack Name Description or Subfield and Description Web
About Content Filtering and Scans
Content Filtering and Optimizing Scans
Default E-mail and Web Scan Settings
Default E-mail and Web Scan Settings
Scan Type Default Scan Setting Default Action if applicable
Configuring E-mail Protection
Customizing E-mail Protocol Scan Settings
Customizing E-mail Anti-Virus and Notification Settings
Performance see Performance Management on
E-mail Anti-Virus and Notification Settings
Notification Settings
Mail
Email Alert Settings
FILENAME%, %ACTION%, %VIRUSNAME%
Mail Content Filtering
TIME%, %PROTOCOL%, %FROM%, %TO%, %SUBJECT%
V1.0, September
Filter by Password-Protected Attachments ZIP, RAR, etc
E-mail Filter Settings
Protected Attachments ZIP, RAR, etc. section above
Password-Protected Attachments ZIP, RAR, etc. section above
Protecting Against E-mail Spam
Filter by File Name
Setting Up the Whitelist and Blacklist
V1.0, September
Whitelist/Blacklist Settings
Configuring the Real-time Blacklist
V1.0, September
Configuring Distributed Spam Analysis
Distributed Spam Analysis Settings
Block spam email
Anti-Spam Engine Settings
Low Medium-Low
Customizing Web Protocol Scan Settings and Services
Configuring Web and Services Protection
Setting Description or Subfield and Description Web
Web Protocol, Instant Messaging, and Peer-to-Peer Settings
Configuring Web Malware Scans
Malware Scan Settings
Html Scan
Configuring Web Content Filtering
V1.0, September
Content Filtering, screen 1
10 Content Filtering, screen 2
11 Content Filtering, screen 3
Block Web Objects
Content Filtering Settings
Performance Management on
Full-Text Search
Blocked Categories Scheduled Days
Netgear
Configuring Web URL Filtering
URL
V1.0, September
Blacklist
URL Filtering Settings
Setting Description or Subfield and Description Whitelist
URL%
Https Scan Settings
V1.0, September
V1.0, September
Specifying Trusted Hosts
10. Https Settings
11. Trusted Hosts Settings
Hosts
Configuring FTP Scans
12. FTP Scan Settings
Block Files with the Following Extensions
Setting Web Access Exceptions and Scanning Exclusions
Setting Web Access Exception Rules
To set Web access exception rules
Groups and Hosts LAN Groups on
13. Add and Edit Block Scanning Exception Settings
Setting Scanning Exclusions
14. Add Scanning Exclusion Settings
V1.0, September
Considerations for Dual WAN Port Systems UTM25 Only
Chapter Virtual Private Networking Using IPsec Connections
IP Addressing for VPNs in Dual WAN Port Systems
Creating Gateway-to-Gateway VPN Tunnels with the Wizard
V1.0, September
Connection Name and Remote IP Type
IPsec VPN Wizard Settings for a Gateway-to-Gateway Tunnel
End Point Information a
Secure Connection Remote Accessibility
Adding or Editing a VPN Policy on
V1.0, September
Creating a Client to Gateway VPN Tunnel
V1.0, September
Fqdn
IPsec VPN Wizard Settings for a Client-to-Gateway Tunnel
V1.0, September
V1.0, September
Status on
Security Policy Editor Remote Party Settings
Only Connect Manually checkbox
Gateway Tunnel
Security Policy Editor My Identity Settings
On page 7-9. In this example, the domain name is
Detection checkbox
Testing the Connections and Viewing Status Information
Testing the VPN Connection
Security Policy Editor Security Policy Settings
Netgear VPN Client Status and Log Information
V1.0, September
System Tray Icon Status Client policy is deactivated
Viewing the UTM IPsec VPN Connection Status
IPsec VPN Connection Status Information
Viewing the UTM IPsec VPN Log
Managing IPsec VPN Policies
IKE Policies Screen
Managing IKE Policies
List of IKE Policies Information
Manually Adding or Editing an IKE Policy
V1.0, September
General
10. Add IKE Policy Settings
Mode Config Record
IKE SA Parameters
Local
Remote
Dead Peer
Configuring Keepalives
Group 1 768 bit
Group 5 1536 bit
Extended Authentication
VPN Policies Screen
Managing VPN Policies
Remote
11. List of VPN Policies Information
Manually Adding or Editing a VPN Policy
V1.0, September
12. Add VPN Policy Settings
Manual Policy Parameters
Description or Subfield and Description Traffic Selection
Auto Policy Parameters
Group 1536 bit
Configuring Extended Authentication Xauth
Group 768 bit
Configuring Xauth for VPN Clients
Information, see Radius Client Configuration on
User Database Configuration
Radius Client Configuration
V1.0, September
Primary Radius Server
14. Radius Client Settings
Backup Radius Server
Connection Configuration
Configuring Mode Config Operation on the UTM
Assigning IP Addresses to Remote Users Mode Config
Mode Config Operation
V1.0, September
Client Pool
15. Add Mode Config Record Settings
Traffic Tunnel Security Level
V1.0, September
16. Add IKE Policy Settings for a Mode Config Configuration
Peer Detection on
Configuring
Menu, select Group 2 1024 bit
Keepalives and Dead
Configuring the ProSafe VPN Client for Mode Config Operation
192.168.1.0
Gateway Tunnel
18. Security Policy Editor My Identity, Mode Config Settings
Menu
Testing the Mode Config Connection
Configuring Keepalives and Dead Peer Detection
Configuring Keepalives
20. Keepalive Settings
Configuring Dead Peer Connection
21. Dead Peer Detection Settings
Configuring NetBIOS Bridging with IPsec VPN
Understanding the SSL VPN Portal Options
Chapter Virtual Private Networking Using SSL Connections
Using the SSL VPN Wizard for Client Configurations
SSL VPN Wizard of 6 Portal Settings
Screen as shown in -8 on
SSL VPN Wizard Portal Settings
Portal Layout and Theme Name
SSL VPN Portal Pages to Display
SSL VPN Wizard of 6 Domain Settings
Radius Client
SSL VPN Wizard Domain Settings
Domain Name
SSL VPN Wizard of 6 User Settings
SSL VPN Wizard User Settings
SSL VPN Wizard of 6 Client IP Address Range and Routes
Add Routes for VPN Tunnel Clients
SSL VPN Wizard Client IP Address Range and Routes Settings
Client IP Address Range
SSL VPN Wizard of 6 Port Forwarding
SSL VPN Wizard Port Forwarding Settings
Add New Host Name for Port Forwarding
SSH
SSL VPN Wizard of 6 Verify and Save Your Settings
Accessing the New SSL Portal Login Screen
V1.0, September
Viewing the UTM SSL VPN Log
Viewing the UTM SSL VPN Connection Status
Manually Configuring and Editing SSL Connections
Creating the Portal Layout
V1.0, September
V1.0, September
Add Portal Layout Settings
Configuring Applications for Port Forwarding
Configuring Domains, Groups, and Users
Adding Servers and Port Numbers
TCP Application Port Number
Adding a New Host Name
Port Forwarding Applications/TCP Port Numbers
Fully Qualified Domain Name. The full server name
Configuring the SSL VPN Client
Configuring the Client IP Address Range
Tunnel Clients on
Adding Routes for VPN Tunnel Clients
Using Network Resource Objects to Simplify Policies
Adding New Network Resources
Editing Network Resources to Specify Addresses
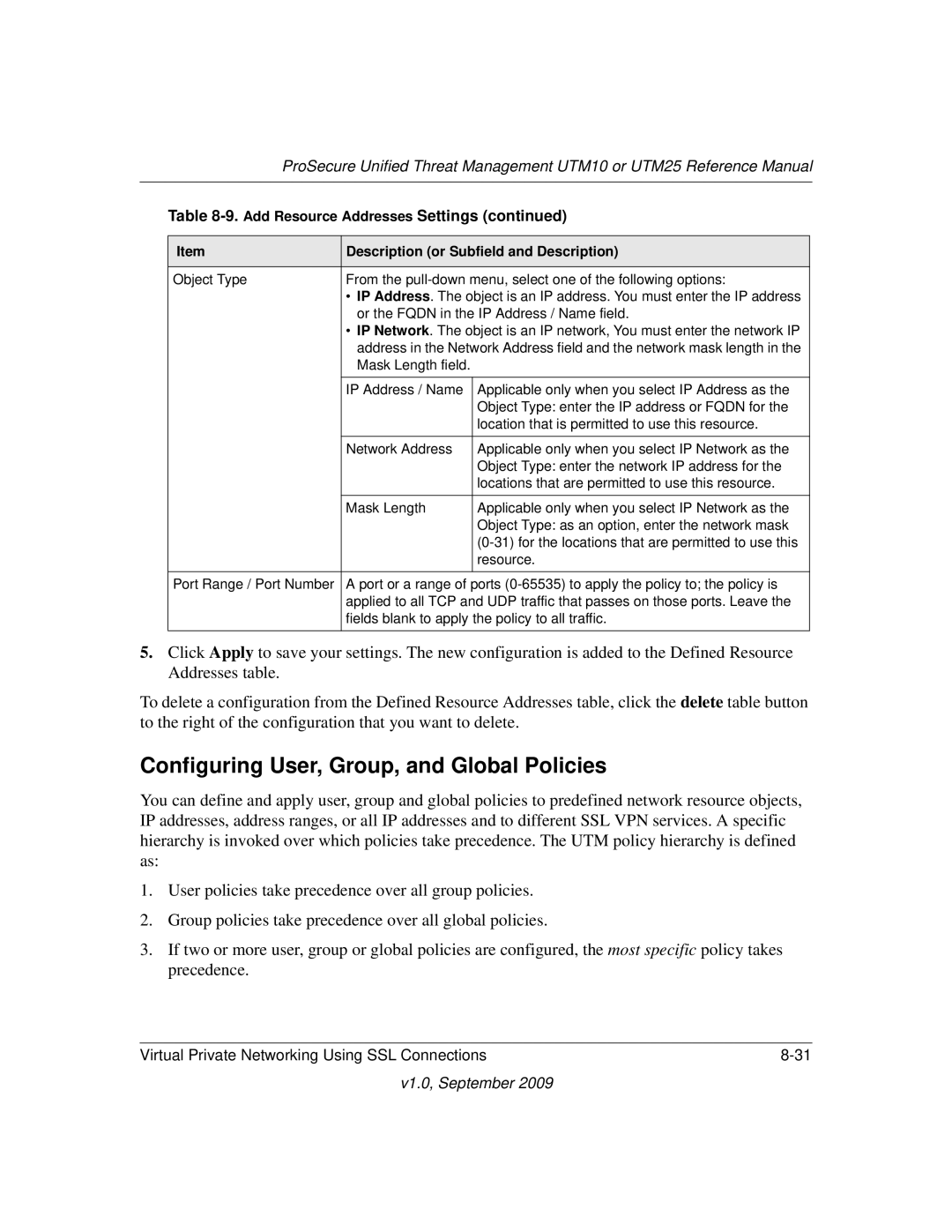
Add Resource Addresses Settings
Configuring User, Group, and Global Policies
Viewing Policies
Adding a Policy
Policy For
10. Add Policy Settings
Network Resource Objects to Simplify Policies on
Description or Subfield and Description Add SSL VPN Policies
10. Add Policy Settings
V1.0, September
V1.0, September
Configuring VPN Authentication Domains, Groups, and Users
Managing Users, Authentication, and Certificates
Authentication Protocols and Methods
Configuring Domains
Ldap
Add Domain Settings
Creating the Portal Layout on
Configuring Groups for VPN Policies
Creating and Deleting Groups
Editing Groups
VPN Group Settings
Configuring User Accounts
V1.0, September
Policies on
Add User Settings
See Configuring Extended Authentication Xauth on
Configuring Login Policies
Setting User Login Policies
Configuring Login Restrictions Based on IP Address
Add Defined Addresses Settings
Configuring Login Restrictions Based on Web Browser
Internet Explorer Opera Netscape Navigator
Changing Passwords and Other User Settings
Managing Digital Certificates
Edit User Settings
Enabled see Configuring Extended Authentication Xauth on
V1.0, September
11 Certificates, screen 1
Managing CA Certificates
Managing Self Certificates
Generating a CSR and Obtaining a Self Certificate from a CA
13 Certificates, screen 2
Setting
512 1024 2048
V1.0, September
Viewing and Managing Self Certificates
Managing the Certificate Revocation List
15Certificates, screen 3
Bandwidth Capacity
Performance Management
Features That Reduce Traffic
Network and System Management 10-3
Content Filtering
Source MAC Filtering
Features That Increase Traffic
10-6 Network and System Management
Port Triggering
Configuring the DMZ Port
Assigning QoS Profiles
Using QoS and Bandwidth Assignment to Shift the Traffic Mix
Configuring Exposed Hosts
Configuring VPN Tunnels
Assigning Bandwidth Profiles
Changing Passwords and Administrator Settings
System Management
Monitoring Tools for Traffic Management
10-10 Network and System Management
Network and System Management 10-11
Configuring Remote Management Access
Https//IPaddress or https//FullyQualifiedDomainName
Using an Snmp Manager
Trusted Snmp Hosts
Managing the Configuration File
Snmp Settings
Setting Description or Subfield and Description Settings
Backup Settings
Restore Settings
Updating the Firmware
Reverting to Factory Default Settings
Viewing the Available Firmware Versions
Upgrading the Firmware and Rebooting the UTM
Updating the Scan Signatures and Scan Engine Firmware
Rebooting Without Changing the Firmware
10-22 Network and System Management
Signatures & Scan Engine Settings
Configuring Automatic Update and Frequency Settings
System Date & Time Settings
Configuring Date and Time Service
Network and System Management 10-25
10-26 Network and System Management
Enabling the WAN Traffic Meter
Monitoring System Access and Performance
11-2 Monitoring System Access and Performance
Logging, Alerts, and Event Notifications on
WAN Traffic Meter Settings
Traffic Counter
Mail, and Syslog Logs on
Configuring the E-mail Notification Server
Configuring Logging, Alerts, and Event Notifications
Server requires authentication checkbox and enter
Configuring and Activating System, E-mail, and Syslog Logs
E-mail Notification Settings
Monitoring System Access and Performance 11-7
Email Logs to Administrator
E-mail and Syslog Settings
Send Logs via Syslog
Configuring and Activating Update Failure and Attack Alerts
Alerts Settings
ACTION%, %VIRUSNAME%
PROTOCOL%, %FROM%, %TO%, %SUBJECT%, %FILENAME%
Configuring and Activating Firewall Logs
Monitoring Real-Time Traffic, Security, and Statistics
Firewall Logs Settings
Dashboard, screen 1
System on
Settings on
Spam to configure, see Protecting Against E-mail Spam on
Total Threats
Total Traffic Bytes
Threats Counts
Prevention System on
Categories, see Using the Intrusion
Dashboard Most Recent 5 and Top 5 Information
Category Most Recent 5 Description Top 5 Description
Dashboard, screen 3
Dashboard Service Statistics Information
Viewing System Status
Viewing Status Screens
System Status Status and System Information
Setting Status
11 System Status, screen 2
Dhcp
NAT
LAN Port
11. System Status Interface Statistics
Viewing Active VPN Users
Viewing VPN Tunnel Connection Status
12. IPsec VPN Connection Status Information
Viewing Port Triggering Status
To view the status of the Port Triggering feature
13. Port Triggering Status Information
Viewing the WAN Ports Status
11-28 Monitoring System Access and Performance
Viewing Attached Devices
Configuring the Internet Connection on
Edit Vlan Profile screen see Configuring a Vlan Profile on
Viewing Attached Devices and the Dhcp Log
11-30 Monitoring System Access and Performance
Viewing the Dhcp Log
Querying the Logs
Querying Logs and Generating Reports
Monitoring System Access and Performance 11-33
15. Logs Query Settings
Following protocols can be selected
See Configuring and Activating Firewall Logs on
This field is available for the following logs
This field is available only for the Malware log
Following categories can be selected
Following reasons can be selected
This field is available only for the Spam log
This field is available only for the Content filters log
EMERG, ALERT, CRITICAL, ERROR, WARNING, Notice
This field is available only for the Service log
Log Management
Example Using Logs to Identify Infected Clients
Scheduling and Generating Reports
Generating Reports
System Reports
16. Generate Report Settings
Email Reports
Web Reports
Scheduling Reports
17. Schedule Report Settings
Report List
Using Diagnostics Utilities
Email Reports Web Reports System Reports
Sending a Ping Packet
Using the Network Diagnostic Tools
Looking up a DNS Address
Tracing a Route
Displaying the Routing Table
27 Diagnostics, screen 2
Using the Realtime Traffic Diagnostics Tool
Generating Network Statistics
Gathering Important Log Information
Rebooting and Shutting Down the UTM
Troubleshooting and Using Online Support
Test LED Never Turns Off
Power LED Not On
Basic Functioning
LAN or WAN Port LEDs Not On
Troubleshooting the Web Management Interface
When You Enter a URL or IP Address a Time-out Error Occurs
Troubleshooting the ISP Connection
Troubleshooting a TCP/IP Network Using a Ping Utility
Testing the Path from Your PC to a Remote Device
Testing the LAN Path to Your UTM
Restoring the Default Configuration and Password
Problems with Date and Time
Enabling Remote Troubleshooting
Using Online Support
Sending Suspicious Files to Netgear for Analysis
Malware Analysis Settings
Accessing the Knowledge Base and Documentation
Local Network LAN
Table A-1. UTM Default Configuration Settings
Feature Default behavior Router Login
Internet Connection
Table A-2. UTM Physical and Technical Specifications
Setting Specification
Table A-3. UTM IPsec VPN Specifications
Feature Specification Environmental Specifications
Interface Specifications
MD5, SHA-1, MAC-MD5/SHA-1, HMAC-MD5/SHA-1
Table A-4. UTM SSL VPN Specifications
What to Consider Before You Begin
Appendix B Network Planning for Dual WAN Ports UTM25 Only
Internet
WAN port Physical facility
Cabling and Computer Hardware Requirements
Computer Network Configuration Requirements
Internet Configuration Requirements
Internet Connection Information
Where Do I Get The Internet Configuration Information?
Overview of the Planning Process
Figure B-2
Inbound Traffic to a Single WAN Port System
Inbound Traffic
Inbound Traffic Dual WAN Ports for Load Balancing
Inbound Traffic to a Dual WAN Port System
Inbound Traffic Dual WAN Ports for Improved Reliability
To-Gateway Through a NAT
Virtual Private Networks VPNs
VPN Road Warrior Client
To-Gateway
Figure B-7
VPN Road Warrior Single Gateway WAN Port Reference Case
VPN Road Warrior Client-to-Gateway
Figure B-10
VPN Road Warrior Dual Gateway WAN Ports for Load Balancing
VPN Gateway-to-Gateway
Figure B-13
Figure B-15
VPN Telecommuter Single Gateway WAN Port Reference Case
VPN Telecommuter Client-to-Gateway Through a NAT Router
Figure B-18
Figure B-20
VPN Telecommuter Dual Gateway WAN Ports for Load Balancing
Term Description or Subfield and Description
Table C-1. Log Message Terms
System Startup
Reboot
Table C-3. System Logs Reboot
System Log Messages
Table C-5. System Logs NTP
Service Logs
Table C-4. System Logs Service
IPsec Restart
Login/Logout
Firewall Restart
ACTIVEWAN2
Auto-Rollover Mode
WAN Status
System Logs WAN Status, Auto Rollover
Table C-9. System Logs WAN Status, Load Balancing
Load-Balancing Mode
PPP Logs
Table C-10. System Logs WAN Status, PPPoE Idle-Timeout
Table C-12. System Logs WAN Status, PPP Authentication
Table C-11. System Logs WAN Status, Pptp Idle-Timeout
Icmp Redirect Logs
Traffic Metering Logs
Unicast Logs
Table C-17. System Logs Invalid Packets
Invalid Packet Logging
Multicast/Broadcast Logs
Table C-16. System Logs Multicast/Broadcast
Invalidshortpacketdrop SRC=192.168.20.10
Invalidbadchecksumdrop SRC=192.168.20.10
Invalidbadhwchecksumdrop SRC=192.168.20.10
Invalidmalformedpacketdrop SRC=192.168.20.10
Web Filtering and Content Filtering Logs
Content Filtering and Security Logs
Spam Logs
Table C-19. Content Filtering and Security Logs Spam
Virus Logs
Table C-20. Content Filtering and Security Logs Traffic
Table C-21. Content Filtering and Security Logs Virus
Traffic Logs
Port Scan Logs
Table C-23. Content Filtering and Security Logs IPS
Table C-24. Content Filtering and Security Logs Port Scan
IPS Logs
DMZ to WAN Logs
Routing Logs
LAN to WAN Logs
LAN to DMZ Logs
WAN to DMZ Logs
WAN to LAN Logs
DMZ to LAN Logs
V1.0, September
What are the benefits of Two-Factor Authentication?
Why do I need Two-Factor Authentication?
What is Two-Factor Authentication
Netgear Two-Factor Authentication Solutions
Figure D-1
Figure D-3
Document Link
Appendix E Related Documents
V1.0, September
Numerics
Index
Index-2
Index-3
Index-4
Index-5
Index-6
Index-7
Index-8
Index-9
Index-10
Index-11
Index-12
Index-13
Index-14
Index-15
Index-16