Setting Up Security for a Device
Switch Port Security
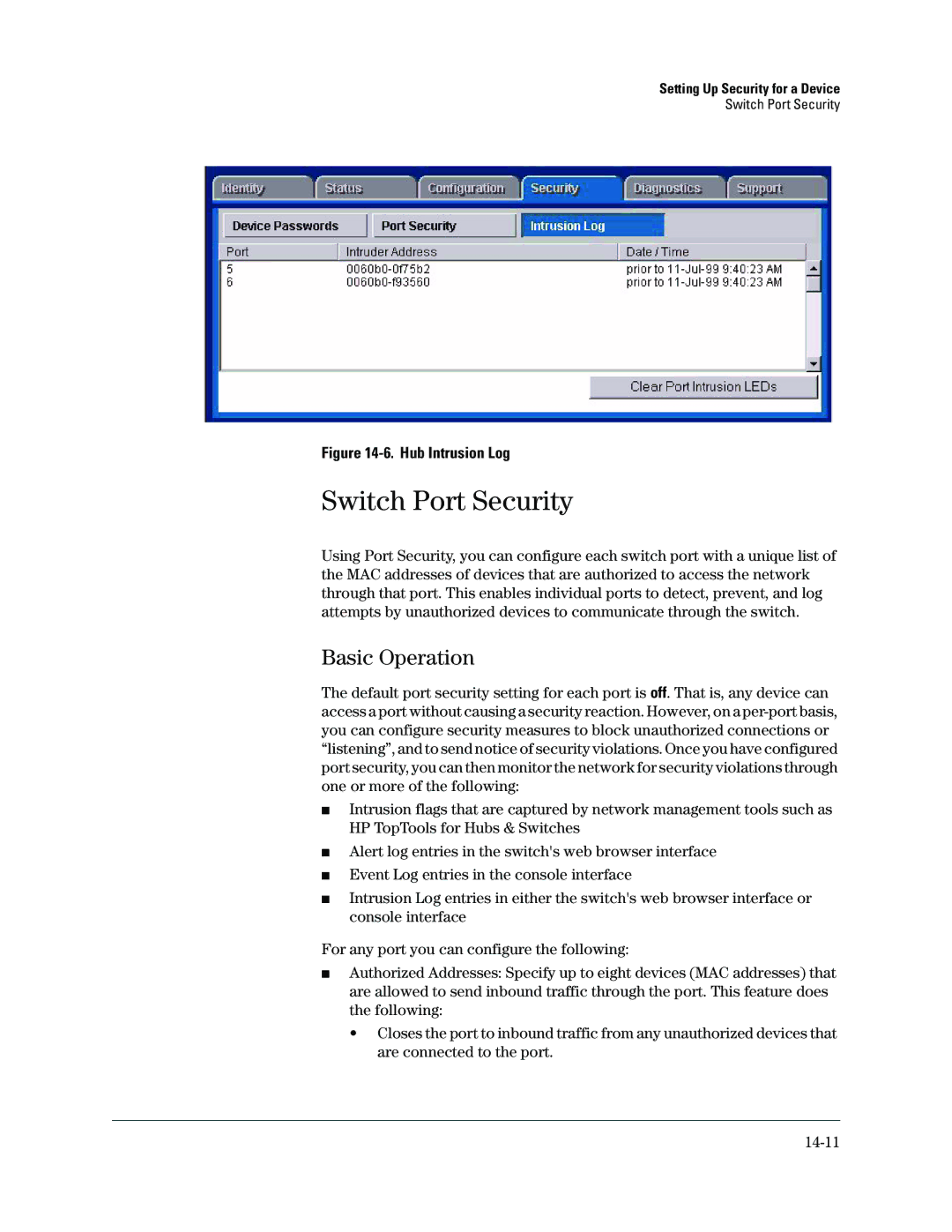
Figure 14-6. Hub Intrusion Log
Switch Port Security
Using Port Security, you can configure each switch port with a unique list of the MAC addresses of devices that are authorized to access the network through that port. This enables individual ports to detect, prevent, and log attempts by unauthorized devices to communicate through the switch.
Basic Operation
The default port security setting for each port is off. That is, any device can access a port without causing a security reaction. However, on a
■Intrusion flags that are captured by network management tools such as HP TopTools for Hubs & Switches
■Alert log entries in the switch's web browser interface
■Event Log entries in the console interface
■Intrusion Log entries in either the switch's web browser interface or console interface
For any port you can configure the following:
■Authorized Addresses: Specify up to eight devices (MAC addresses) that are allowed to send inbound traffic through the port. This feature does the following:
•Closes the port to inbound traffic from any unauthorized devices that are connected to the port.