Advanced Configuration |
|
SSID/VLAN/Security |
|
|
|
•
•PEAP - Protected EAP with
Different servers support different EAP types and each EAP type provides different features. See the documentation that came with your RADIUS server to determine which EAP types it supports.
NOTE: The AP supports the following EAP types when Security Mode is set to 802.1x, WPA, or 802.11i (WPA2):
Authentication Process
There are three main components in the authentication process. The standard refers to them as:
1.Supplicant (client PC)
2.Authenticator (Access Point)
3.Authentication server (RADIUS server)
When the Security Mode is set to 802.1x Station, WPA Station, or 802.11i Station you need to configure your RADIUS server for authentication purposes.
Prior to successful authentication, an unauthenticated client PC cannot send any data traffic through the AP device to other systems on the LAN. The AP inhibits all data traffic from a particular client PC until the client PC is authenticated. Regardless of its authentication status, a client PC can always exchange 802.1x messages in the clear with the AP (the client begins encrypting data after it has been authenticated).
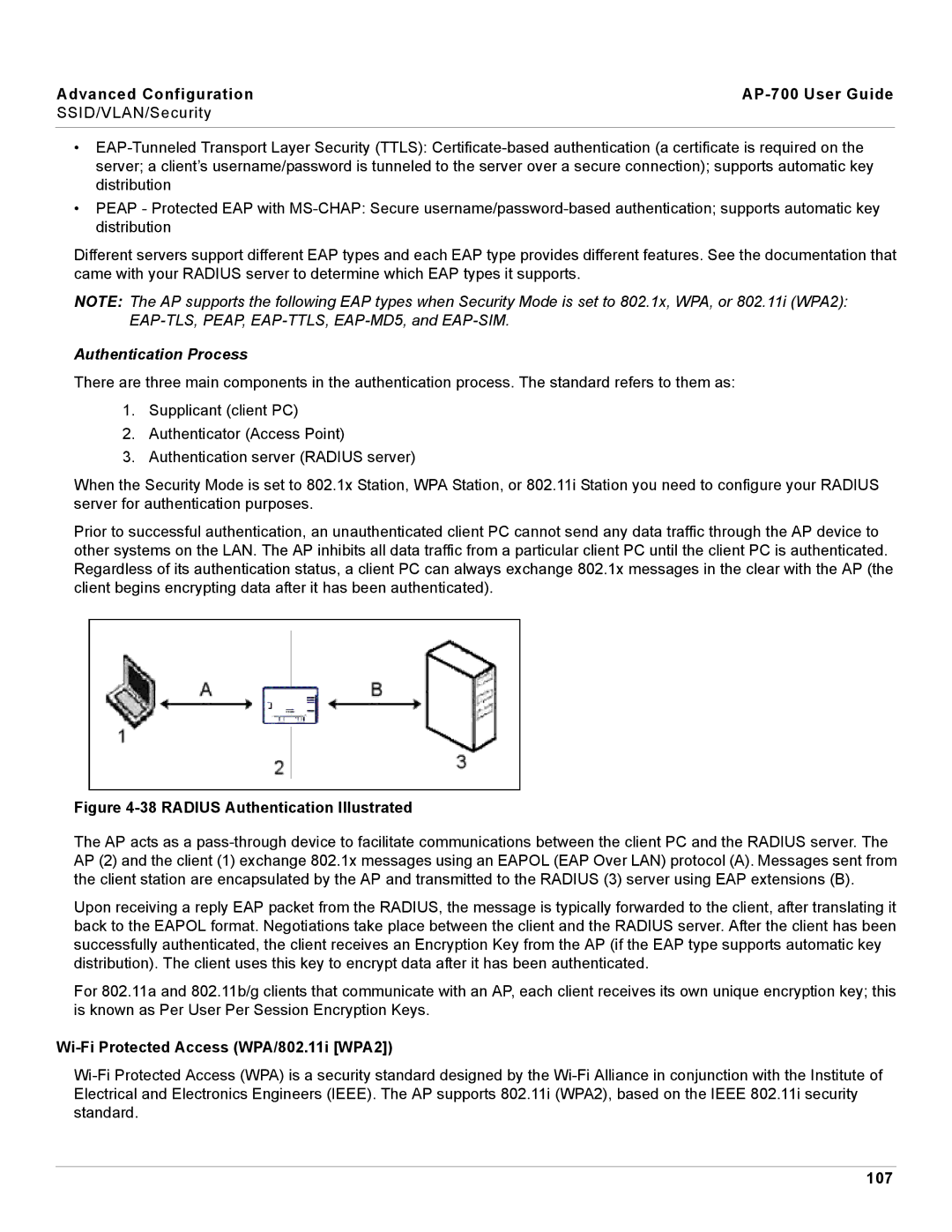
Figure 4-38 RADIUS Authentication Illustrated
The AP acts as a
Upon receiving a reply EAP packet from the RADIUS, the message is typically forwarded to the client, after translating it back to the EAPOL format. Negotiations take place between the client and the RADIUS server. After the client has been successfully authenticated, the client receives an Encryption Key from the AP (if the EAP type supports automatic key distribution). The client uses this key to encrypt data after it has been authenticated.
For 802.11a and 802.11b/g clients that communicate with an AP, each client receives its own unique encryption key; this is known as Per User Per Session Encryption Keys.