Grey Headline (continued)
LDAP Configuration
TANDBERG VIDEO COMMUNICATIONS SERVER ADMINISTRATOR GUIDE
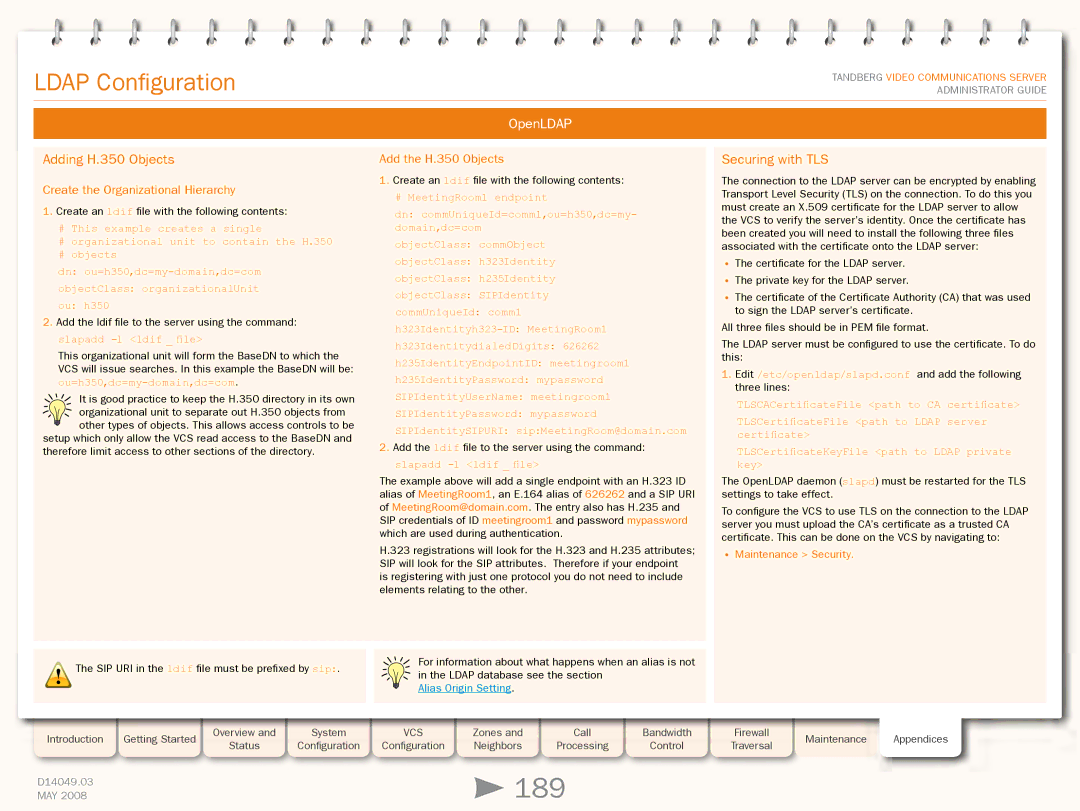
OpenLDAP
Adding H.350 Objects
Create the Organizational Hierarchy
1.Create an ldif file with the following contents:
#This example creates a single
#organizational unit to contain the H.350
#objects
dn:
objectClass: organizationalUnit
ou: h350
2.Add the ldif file to the server using the command: slapadd
This organizational unit will form the BaseDN to which the
VCS will issue searches. In this example the BaseDN will be:
It is good practice to keep the H.350 directory in its own
organizational unit to separate out H.350 objects from other types of objects. This allows access controls to be
setup which only allow the VCS read access to the BaseDN and therefore limit access to other sections of the directory.
!The SIP URI in the ldif file must be prefixed by sip:.
Add the H.350 Objects
1.Create an ldif file with the following contents:
#MeetingRoom1 endpoint
dn: commUniqueId=comm1,ou=h350,dc=my- domain,dc=com
objectClass: commObject
objectClass: h323Identity
objectClass: h235Identity
objectClass: SIPIdentity
commUniqueId: comm1
h323IdentitydialedDigits: 626262
h235IdentityEndpointID: meetingroom1
h235IdentityPassword: mypassword
SIPIdentityUserName: meetingroom1
SIPIdentityPassword: mypassword
SIPIdentitySIPURI: sip:MeetingRoom@domain.com
2.Add the ldif file to the server using the command:
slapadd -l <ldif _ file>
The example above will add a single endpoint with an H.323 ID alias of MeetingRoom1, an E.164 alias of 626262 and a SIP URI of MeetingRoom@domain.com. The entry also has H.235 and SIP credentials of ID meetingroom1 and password mypassword which are used during authentication.
H.323 registrations will look for the H.323 and H.235 attributes; SIP will look for the SIP attributes. Therefore if your endpoint is registering with just one protocol you do not need to include elements relating to the other.
For information about what happens when an alias is not in the LDAP database see the section
Alias Origin Setting.
Securing with TLS
The connection to the LDAP server can be encrypted by enabling Transport Level Security (TLS) on the connection. To do this you must create an X.509 certificate for the LDAP server to allow the VCS to verify the server’s identity. Once the certificate has been created you will need to install the following three files associated with the certificate onto the LDAP server:
•The certificate for the LDAP server.
•The private key for the LDAP server.
•The certificate of the Certificate Authority (CA) that was used to sign the LDAP server’s certificate.
All three files should be in PEM file format.
The LDAP server must be configured to use the certificate. To do this:
1.Edit /etc/openldap/slapd.conf and add the following three lines:
TLSCACertificateFile <path to CA certificate> TLSCertificateFile <path to LDAP server certificate>
TLSCertificateKeyFile <path to LDAP private key>
The OpenLDAP daemon (slapd) must be restarted for the TLS settings to take effect.
To configure the VCS to use TLS on the connection to the LDAP server you must upload the CA’s certificate as a trusted CA certificate. This can be done on the VCS by navigating to:
•Maintenance > Security.
Introduction | Getting Started |
| Overview and |
| System |
| VCS |
| Zones and |
| Call |
| Bandwidth |
| Status |
| Configuration |
| Configuration |
| Neighbors |
| Processing |
| Control | ||
|
|
|
|
|
|
|
| ||||||
|
|
|
|
|
|
|
|
|
|
|
|
|
|
D14049.03 |
|
|
|
|
|
|
|
| 189 |
|
| ||
MAY 2008 |
|
|
|
|
|
|
|
|
|
| |||
Firewall Maintenance Appendices Traversal