P-2602H(W)(L)-DxA Series User’s Guide
Table 66 Common IP Ports
21 | FTP | 53 | DNS |
|
|
|
|
23 | Telnet | 80 | HTTP |
|
|
|
|
25 | SMTP | 110 | POP3 |
|
|
|
|
13.4.2 Types of DoS Attacks
There are four types of DoS attacks:
1Those that exploit bugs in a TCP/IP implementation.
2Those that exploit weaknesses in the TCP/IP specification.
3
4IP Spoofing.
5"Ping of Death" and "Teardrop" attacks exploit bugs in the TCP/IP implementations of various computer and host systems.
•Ping of Death uses a "ping" utility to create an IP packet that exceeds the maximum 65,536 bytes of data allowed by the IP specification. The oversize packet is then sent to an unsuspecting system. Systems may crash, hang or reboot.
•Teardrop attack exploits weaknesses in the
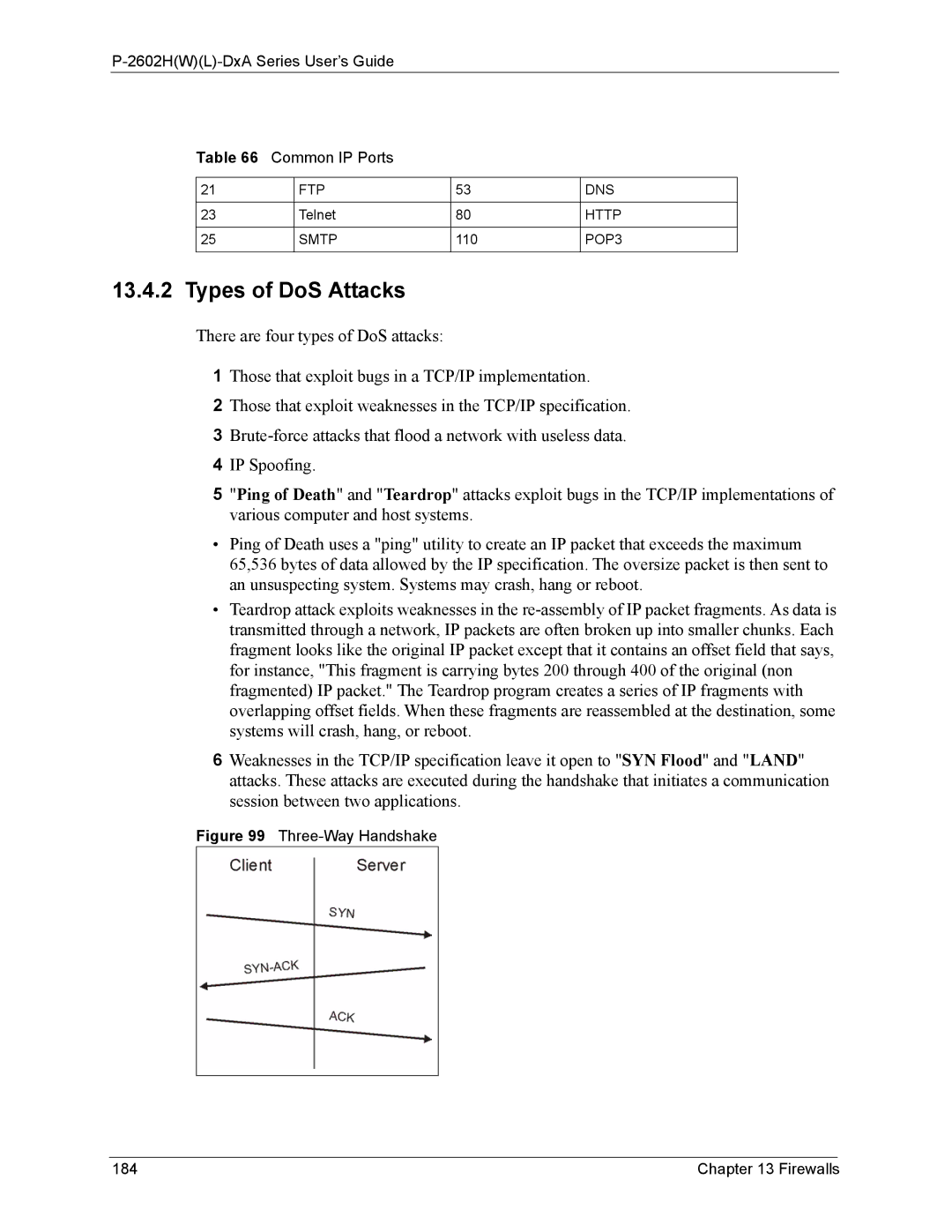
6Weaknesses in the TCP/IP specification leave it open to "SYN Flood" and "LAND" attacks. These attacks are executed during the handshake that initiates a communication session between two applications.
Figure 99 Three-Way Handshake
184 | Chapter 13 Firewalls |