P-2602H(W)(L)-DxA Series User’s Guide
The Message Integrity Check (MIC) is designed to prevent an attacker from capturing data packets, altering them and resending them. The MIC provides a strong mathematical function in which the receiver and the transmitter each compute and then compare the MIC. If they do not match, it is assumed that the data has been tampered with and the packet is dropped.
By generating unique data encryption keys for every data packet and by creating an integrity checking mechanism (MIC), TKIP makes it much more difficult to decrypt data on a
The encryption mechanisms used for WPA and
Security Parameters Summary
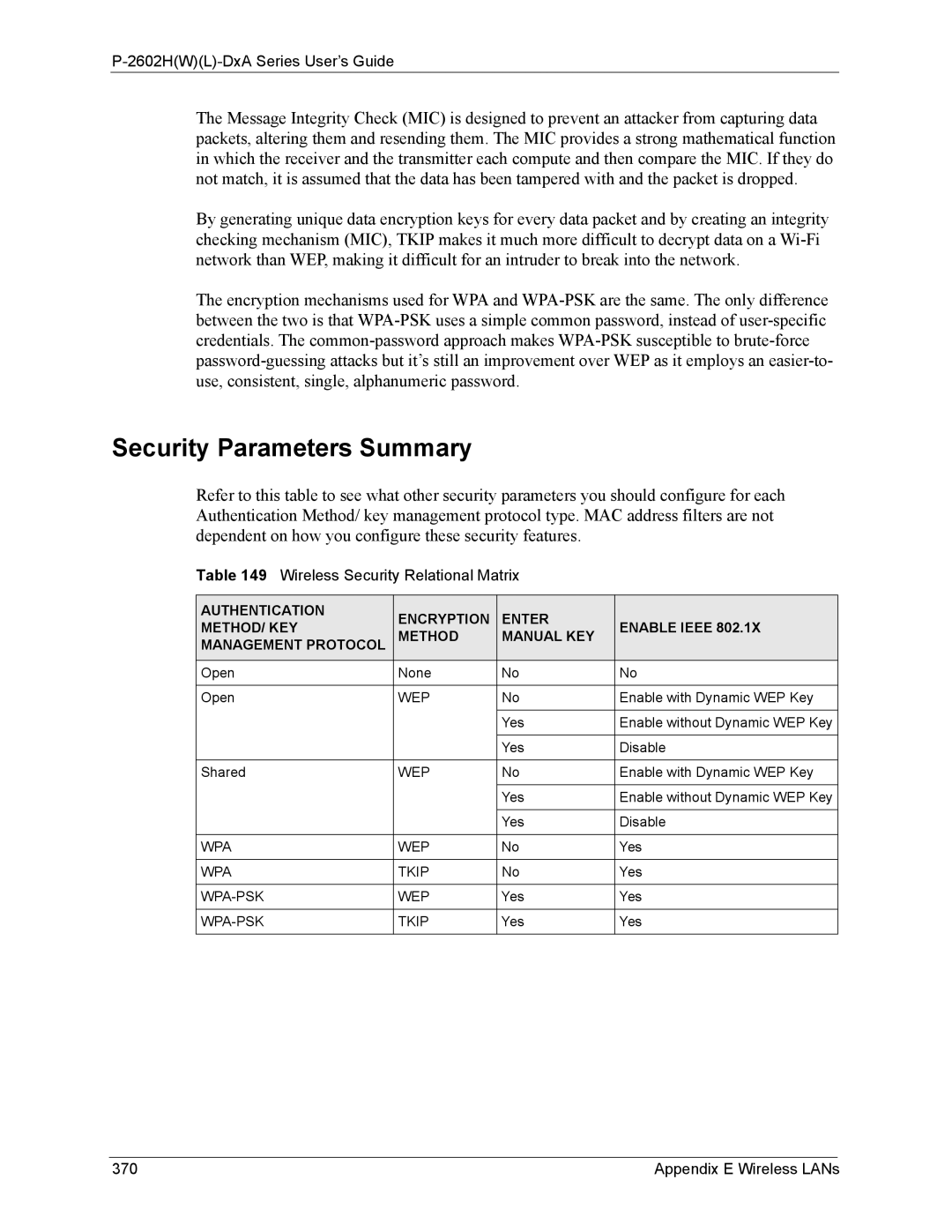
Refer to this table to see what other security parameters you should configure for each Authentication Method/ key management protocol type. MAC address filters are not dependent on how you configure these security features.
Table 149 Wireless Security Relational Matrix
AUTHENTICATION | ENCRYPTION | ENTER |
| |
METHOD/ KEY | ENABLE IEEE 802.1X | |||
METHOD | MANUAL KEY | |||
MANAGEMENT PROTOCOL |
| |||
|
|
|
| |
Open | None | No | No | |
|
|
|
| |
Open | WEP | No | Enable with Dynamic WEP Key | |
|
|
|
| |
|
| Yes | Enable without Dynamic WEP Key | |
|
|
|
| |
|
| Yes | Disable | |
|
|
|
| |
Shared | WEP | No | Enable with Dynamic WEP Key | |
|
|
|
| |
|
| Yes | Enable without Dynamic WEP Key | |
|
|
|
| |
|
| Yes | Disable | |
|
|
|
| |
WPA | WEP | No | Yes | |
|
|
|
| |
WPA | TKIP | No | Yes | |
|
|
|
| |
WEP | Yes | Yes | ||
|
|
|
| |
TKIP | Yes | Yes | ||
|
|
|
|
370 | Appendix E Wireless LANs |