P-2602H(W)(L)-DxA Series User’s Guide
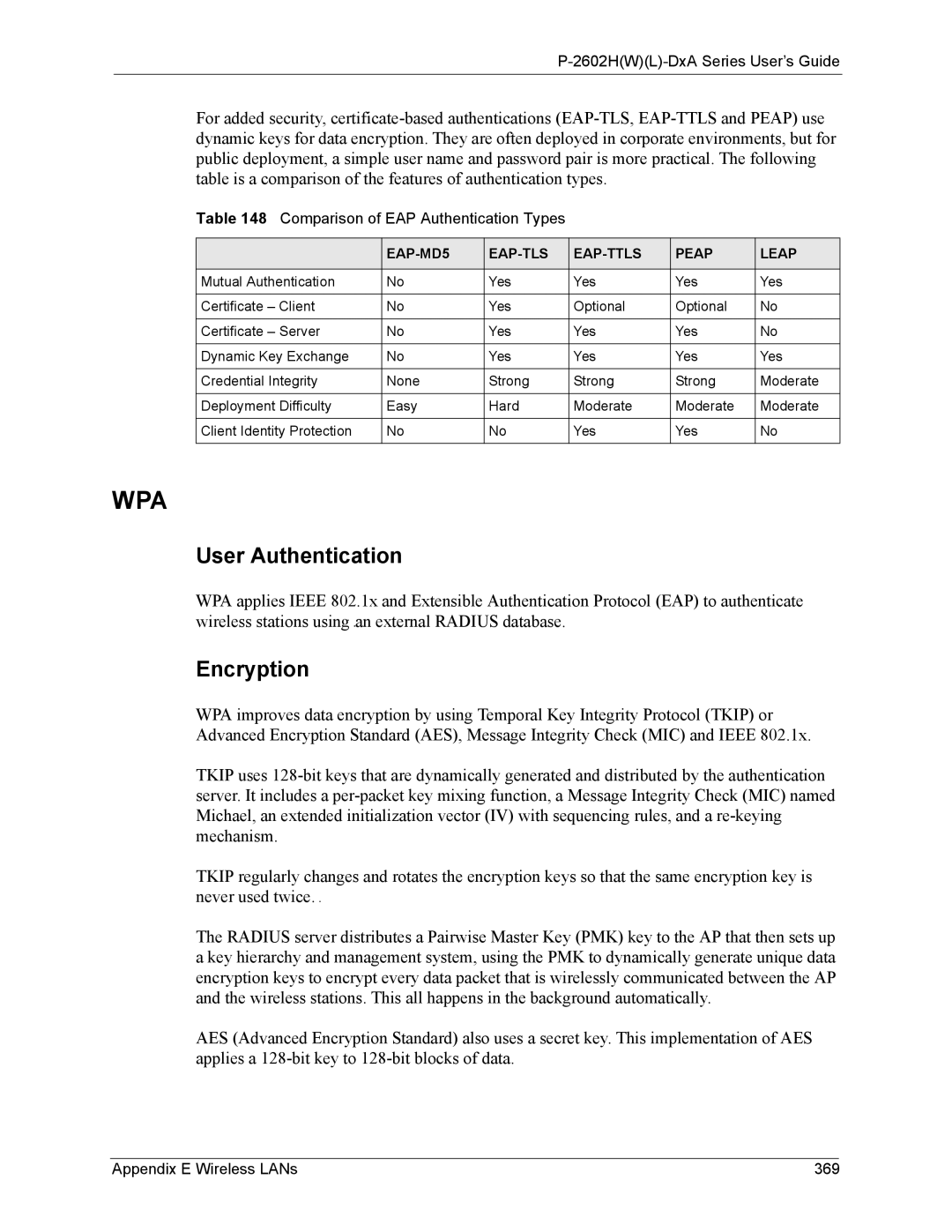
For added security,
Table 148 Comparison of EAP Authentication Types
|
|
|
| PEAP | LEAP |
|
|
|
|
|
|
Mutual Authentication | No | Yes | Yes | Yes | Yes |
|
|
|
|
|
|
Certificate – Client | No | Yes | Optional | Optional | No |
|
|
|
|
|
|
Certificate – Server | No | Yes | Yes | Yes | No |
|
|
|
|
|
|
Dynamic Key Exchange | No | Yes | Yes | Yes | Yes |
|
|
|
|
|
|
Credential Integrity | None | Strong | Strong | Strong | Moderate |
|
|
|
|
|
|
Deployment Difficulty | Easy | Hard | Moderate | Moderate | Moderate |
|
|
|
|
|
|
Client Identity Protection | No | No | Yes | Yes | No |
|
|
|
|
|
|
WPA
User Authentication
WPA applies IEEE 802.1x and Extensible Authentication Protocol (EAP) to authenticate wireless stations using an external RADIUS database.
Encryption
WPA improves data encryption by using Temporal Key Integrity Protocol (TKIP) or Advanced Encryption Standard (AES), Message Integrity Check (MIC) and IEEE 802.1x.
TKIP uses
TKIP regularly changes and rotates the encryption keys so that the same encryption key is never used twice.
The RADIUS server distributes a Pairwise Master Key (PMK) key to the AP that then sets up a key hierarchy and management system, using the PMK to dynamically generate unique data encryption keys to encrypt every data packet that is wirelessly communicated between the AP and the wireless stations. This all happens in the background automatically.
AES (Advanced Encryption Standard) also uses a secret key. This implementation of AES applies a
Appendix E Wireless LANs | 369 |