Manual Version 6W100
3Com WX3000 Series Unified Switches Switching Engine
Environmental Statement
Organization
Part Contents
About This Manual
Italic
Conventions
Convention Description Boldface
Manual Description
Related Documentation
Convention Description
Create Folder
Obtaining Documentation
Table of Contents
Introduction to the CLI
CLI Configuration
Command Hierarchy
Switching to a specific user level
Switching User Levels
Setting a user level switching password
Setting the level of a command in a specific view
Setting the Level of a Command in a Specific View
Configuration example
Quit or return
CLI Views
Display Execute Operation
Quit
Peer-public-key command
Gigabitethernet command
Vlan-interface command
Region-configuration
Execute the radius scheme
Public-key-c
Ode end
Public-key-code begin
Online Help
CLI Features
Vlan-vpn enable
Execute Command should be first
Press Ctrl+C
Command History
Terminal Display
Partial online help
Command Edit
Error Prompts
Tab
Press… To…
Table of Contents
Page
Supported User Interfaces
Logging In to the Switching Engine
Logging In to the Switching Engine
Introduction to the User Interface
User Interface Index
Common User Interface Configuration
Display web users
Display users all
Display user-interface
Type number number
OAP Overview
Logging In to the Switching Engine Through OAP
Press Enter to enter user view of the switching engine
Logging In Through OAP
Address of an OAP module
Configure the management IP
Not configured by default
Oap management-ip
Oap reboot slot
Resetting the OAP Software System
Reset the OAP software
Introduction
Common Configuration
Configuration Description
Logging In Through Telnet
Authentication Telnet configuration Description Mode
Telnet Configurations for Different Authentication Modes
Configuration Procedure
Telnet Configuration with Authentication Mode Being None
Network requirements
Configuration Example
Configuration procedure
User privilege level level
Password Set authentication
Password cipher
Auto-execute command
Commands by default
Set the history command buffer
Default history command
Command buffer can store up to
Telnet Configuration with Authentication Mode Being Scheme
Protocol inbound all ssh
Scheme command
Authorization
History-command max-size
Privilege
Service-type
User privilege level level command is Level level
# Create a local user named guest and enter local user view
Telnetting to the Switching Engine from a Terminal
Telnetting to the Switching Engine
Deviceoap connect slot Connected to OAP
Page
Device telnet
Logging In from the Web-Based Network Management System
Vlan interface of the switching engine is assigned an IP
User name and password for logging in to the Web-based
Network management system are configured
Setting Up a Web Configuration Environment
3The login page of the Web-based network management system
Configuring the Login Banner
Through Web Configured
Header login text
By default, no login banner is
Ip http shutdown
Follow these steps to enable/disable the WEB server
Enable the Web server
Enabling/Disabling the WEB Server
Related information
Connection Establishment Using NMS
Logging In from NMS
Configuration in system view
Configuring Source IP Address for Telnet Service Packets
Configuring Source IP Address for Telnet Service Packets
Configuration in user view
Interface-number
Displaying Source IP Address Configuration
Prerequisites
Login mode Control method Implementation Reference
User Control
Controlling Telnet Users
Acl acl-number inbound
Match-order config auto
Acl number acl-number
Rule rule-id deny permit
Permit rule-string
Controlling Telnet Users by Source MAC Addresses
Rule rule-id deny
Controlling Network Management Users by Source IP Addresses
Controlling Network Management Users by Source IP Addresses
Controlling Web Users by Source IP Address
2Network diagram for controlling Snmp users using ACLs
Free web-users all user-id
Disconnecting a Web User by Force
Controlling Web Users by Source IP Addresses
Ip http acl acl-number
Device ip http acl
Table of Contents
Format of configuration file
Configuration File Management
Introduction to Configuration File
Types of configuration
Modes in saving the configuration
Management of Configuration File
Saving the Current Configuration
Startup with the configuration file
Three attributes of the configuration file
Erasing the Startup Configuration File
Startup saved-configuration
Specifying a Configuration File for Next Startup
Assign main attribute to the startup configuration file
Assign backup attribute to the startup configuration file
Displaying and Maintaining Device Configuration
Table of Contents
Introduction to Vlan
Vlan Overview
Vlan Overview
Vlan tag
Advantages of VLANs
How Vlan Works
2Encapsulation format of traditional Ethernet frames
MAC address learning mechanism of VLANs
Vlan Classification
Port-Based Vlan
Vlan Interface
Ethernet II and 802.2/802.3 encapsulation
Protocol-Based Vlan
Introduction to Protocol-Based Vlan
Encapsulation Format of Ethernet Data
6802.3 raw encapsulation format
Extended encapsulation formats of 802.2/802.3 packets
Encapsulation Ethernet 802.3 raw 802.2 LLC Snap Protocol
Procedure for the Switch to Judge Packet Protocol
Encapsulation Formats
Implementation of Protocol-Based Vlan
Page
Basic Vlan Configuration
Vlan Configuration
Vlan Configuration
Configuration Task List
Displaying and Maintaining Vlan
Basic Vlan Interface Configuration
Configuration prerequisites
Port interface-list
Configuring a Port-Based Vlan
Configuring a Port-Based Vlan
Protocol-Based Vlan Configuration Example
# Create Vlan 201, and add GigabitEthernet 1/0/12 to Vlan
# Configure GigabitEthernet 1/0/10 of Switch B
# Create Vlan 201, and add GigabitEthernet 1/0/2 to Vlan
Configuring a Protocol Template for a Protocol-Based Vlan
Configuring a Protocol-Based Vlan
Vlan vlan-id protocol-index
Associating a Port with a Protocol-Based Vlan
Interface interface-type Interface-number
Port hybrid protocol-vlan
Display protocol-vlan vlan vlan id
Displaying and Maintaining Protocol-Based Vlan
Display vlan vlan-id to vlan-id all
Dynamic static
Vlan
Protocol-Type
Table of Contents
Introduction to the Auto Detect Function
Auto Detect Configuration
Auto Detect Basic Configuration
Auto Detect Configuration
Preference-value reject blackhole
Auto Detect Implementation in Vlan Interface Backup
Auto Detect Implementation in Static Routing
Ip route-static ip-address mask
Standby detect-group
Auto Detect Configuration Examples
Vlan -id
# Create auto detected group
# Configure a static route to Switch a
Is reachable
Table of Contents
How an IP Phone Works
Voice Vlan Configuration
Voice Vlan Overview
Agent
1Network diagram for IP phones
Number OUI address Vendor
Configuring Operation Mode for Voice Vlan
How the Device Identifies Voice Traffic
Support for Voice Vlan on Various Ports
Processing mode of tagged packets sent by IP voice devices
Port voice Voice
Security Mode of Voice Vlan
Port type Supported or not Traffic type Mode
Configuring a Voice Vlan to Operate in Automatic Mode
Voice Vlan Configuration
Configuration Prerequisites
Voice vlan security
Configuring a Voice Vlan to Operate in Manual Mode
Enable
Undo voice vlan mode
Port trunk pvid vlan
Port trunk permit vlan
Port hybrid vlan vlan-id
Tagged untagged
Displaying and Maintaining Voice Vlan
Voice Vlan Configuration Example
Voice Vlan Configuration Example Automatic Mode
# Enable the voice Vlan function on GigabitEthernet 1/0/1
Voice Vlan Configuration Example Manual Mode
# Enable the voice Vlan function globally
# Configure GigabitEthernet 1/0/1 as a hybrid port
# Display the status of the current voice Vlan
# Create Vlan 2 and configure it as a voice Vlan
# Configure GigabitEthernet 1/0/1 to operate in manual mode
Verification
Table of Contents
Introduction to Gvrp
Gvrp Configuration
Garp messages and timers
Garp packets are in the following format
Operating mechanism of Garp
Garp message format
Field Description Value
1Format of Garp packets
Enabling Gvrp
Gvrp Configuration
Protocol Specifications
Configuration Prerequisite
Gvrp
Configuring Gvrp Timers
Garp timer leaveall
Garp timer hold join
Displaying and Maintaining Gvrp
Configuring Gvrp Port Registration Mode
# Enable Gvrp on GigabitEthernet 1/0/1
Gvrp Configuration Example
Gvrp Configuration Example
Configure Switch a # Enable Gvrp globally
# Enable Gvrp on GigabitEthernet 1/0/3
SwitchE-GigabitEthernet1/0/1 gvrp registration fixed
Table of Contents
Combo Ports Mapping Relations
Basic Port Configuration
Ethernet Port Overview
Types and Numbers of Ethernet Ports
Link Types of Ethernet Ports
Configuring the Default Vlan ID for an Ethernet Port
Vlan tag
Configuring Ethernet Ports
Making Basic Port Configuration
Adding an Ethernet Port to Specified VLANs
Configuring Port Auto-Negotiation Speed
Broadcast-suppression
Setting the Ethernet Port Broadcast Suppression Ratio
Enabling Flow Control on a Port
Speed auto 10 100
Configuring Trunk Port Attribute
Configuring Access Port Attribute
Configuring Hybrid Port Attribute
Disabling Up/Down Log Output on a Port
Configuration tasks
Aggregation-group destination-agg-id
Copying Port Configuration to Other Ports
Configuring a Port Group
System-view Copy configuration source interface-type
Setting Loopback Detection for an Ethernet Port
Loopback detection only on VLANs for the trunk and hybrid
Configuring the Ethernet Port to Run Loopback Test
Configure the Ethernet port to run
Loopback-detection per-vlan
Flow-interval interval
Enabling the System to Test Connected Cable
Virtual-cable-test
Displaying and Maintaining Ethernet Ports
Ethernet Port Configuration Example
# Configure the default Vlan ID of GigabitEthernet 1/0/1 as
Troubleshooting Ethernet Port Configuration
Table of Contents
Introduction to Lacp
Link Aggregation Configuration
Introduction to Link Aggregation
Port status in manual aggregation group
Operation Key
Manual Aggregation Group
Introduction to manual aggregation group
Port status of static aggregation group
Static Lacp Aggregation Group
Introduction to static Lacp aggregation
Port status of dynamic aggregation group
Configuring system priority
Dynamic Lacp Aggregation Group
Introduction to dynamic Lacp aggregation group
Aggregation Group Categories
Configuring port priority
Configuring a Manual Aggregation Group
Link Aggregation Configuration
Agg-id
Configuring a Static Lacp Aggregation Group
Description agg-name
Port link-aggregation group
System-priority
Configuring a Dynamic Lacp Aggregation Group
Lacp system -priority
Displaying and Maintaining Link Aggregation
Link Aggregation Configuration Example
Switch a Link aggregation Switch B
Page
Table of Contents
Introduction to Port Isolation
Port Isolation Configuration
Port Isolation Configuration
Port Isolation Overview
Displaying and Maintaining Port Isolation
Port Isolation Configuration Example
Device-GigabitEthernet1/0/4 quit device
Table of Contents
Introduction
Port Security Configuration
Port Security Features
Port Security Overview
Neither
Security mode Description Feature
This mode
Port Security Modes
Security mode Description Feature
Enabling Port Security
Port Security Configuration
Complete the following tasks to configure port security
Follow these steps to enable port security
Count-value
Setting the Port Security Mode
Port-security oui OUI-value UserLoginWithOUI mode, a
Port-security max-mac-count
Configuring the NTK feature
Configuring Port Security Features
Configuring the Trap feature
Configuring intrusion protection
Configuring Security MAC Addresses
Port Security Configuration Example
Displaying and Maintaining Port Security Configuration
# Enter GigabitEthernet 1/0/1 port view
HostSwitch
# Enable port security
# Set the port security mode to autolearn
Port Binding Overview
Port Binding Configuration
Displaying and Maintaining Port Binding Configuration
Configuring Port Binding
Configure switch a as follows # Enter system view
Port Binding Configuration Example
Table of Contents
Dldp Overview
Dldp Configuration
Status Description
Dldp Fundamentals
Dldp status
Interval of sending advertisement packets, which can be
Dldp timers
Dldp works with the following timers 2DLDP timers
Timer Description
Entry aging Timer expire
Dldp operating mode
Enhanced timer then sends one probe packets every one
Mode During neighbor
Dldp status Packet types
Packet type Processing procedure
No Echo packet received from Processing procedure Neighbor
4Types of packets sent by Dldp
Dldp neighbor state
Dldp Configuration
Precautions During Dldp Configuration
Dldp Configuration Tasks
Resetting Dldp Status
Dldp Network Example
Reset the Dldp status of a port Dldp reset
This command only applies to the ports in Dldp down status
# Display the Dldp status
# Enable Dldp globally
# Configure Dldp to work in enhanced mode
# Set the interval of sending Dldp packets to 15 seconds
Table of Contents
Introduction to MAC Address Learning
MAC Address Table Management
Introduction to MAC Address Table
1MAC address learning diagram
Aging of MAC address table
Managing MAC Address Table
Entries in a MAC address table
Configuring MAC Address Table Management
System-view Mac-address static dynamic
Configuring a MAC Address Entry
Adding a MAC address entry in system view
Adding a MAC address entry in Ethernet port view
Age no-aging
Setting the Aging Time of MAC Address Entries
Mac-address timer aging
Max-mac-count
Disabling MAC Address learning for a Vlan
Mac-address
Max-mac-count count
Display mac-address
Configuration Example
Displaying and Maintaining MAC Address Table
Adding a Static MAC Address Entry Manually
Table of Contents
Page
STP Overview
Mstp Configuration
STP Overview
All the ports on the root bridge are designated ports
Classification Designated bridge Designated port
Step Description
How STP works
Step Description
Device Port name Bpdu of port
Device Comparison process Bpdu of port after
5Comparison process and result on each device
Device Comparison process Bpdu of port after
3The final calculated spanning tree
Disadvantages of STP and Rstp
Features of Mstp
Mstp Overview
Background of Mstp
MST region
Basic Mstp Terminologies
Port role
Vlan mapping table
Region root
Common root bridge
MSTP, a port can be in one of the following three states
Port state
Implement STP algorithm
Principle of Mstp
Calculate the Cist
Calculate an Msti
Mstp Implementation on the Device
Bpdu guard Loop guard TC-BPDU attack guard Bpdu packet drop
Configuring Root Bridge
Complete the following tasks to configure a root bridge
STP-related Standards
Configuring an MST Region
# Verify the above configuration
Stp instance instance-id root secondary
Centi-seconds
Stp instance instance-id
Configuring the Bridge Priority of the Current Device
Required Default bridge priority of a Current device
Set the bridge priority for
Auto dot1s legacy
Stp interface interface-type
Interface-number compliance
Legacy
Configuring the Mstp Operation Mode
Stp mode stp rstp mstp
Stp compliance auto dot1s
Stp max-hops hops
Configuring the Maximum Hop Count of an MST Region
Configuring the Network Diameter of the Switched Network
Stp timer max-age
Configuring the Mstp Time-related Parameters
Stp timer forward-delay
Stp timer hello
Configuring the Timeout Time Factor
Stp transmit-limit packetnum
Stp interface interface-list
Transmit-limit packetnum
Edged-port enable
Configuring the Current Port as an Edge Port
Configure a port as an edge port in system view
Configure a port as an edge port in Ethernet port view
Force-false auto
Point-to-point force-true
Stp point-to-point force-true
Stp enable
Disable
Enabling Mstp
Task Remarks
Configuring Leaf Nodes
Stp disable
Configuring a Port as an Edge Port
Configuring the MST Region
Dot1d-1998 dot1t legacy
Configuring the Path Cost for a Port
Standards for calculating path costs of ports
Stp pathcost-standard
Configuration example B
Configure the path cost for specific ports
Configuration example a
Instance instance-id port
Configuring Port Priority
Configure port priority in system view
Configure port priority in Ethernet port view
Stp interface interface-list mcheck
Performing mCheck Operation
Perform the mCheck operation in system view
Perform the mCheck operation in Ethernet port view
Stp mcheck
Configuring Guard Functions
Bpdu guard
Root guard
Bpdu dropping
Loop guard
TC-BPDU attack guard
Stp root-protection
Configuring Bpdu Guard
Configuring Root Guard
Root-protection
Stp tc-protection
Configuring Loop Guard
Configuring TC-BPDU Attack Guard
Stp loop-protection
Bpdu-drop any
Configuring Digest Snooping
Configuring Bpdu Dropping
Interface interface-name
Stp config-digest-snooping
Configuring Digest Snooping
Configuring Rapid Transition
6The Rstp rapid transition mechanism
Stp no-agreement-check
Configuring Rapid Transition
No-agreement-check
Vlan-vpn tunnel
Configuring VLAN-VPN Tunnel
Configuring VLAN-VPN tunnel
Portlog
STP Maintenance Configuration
Enabling Log/Trap Output for Ports of Mstp Instance
Stp instance instance id
Displaying and Maintaining Mstp
Enabling Trap Messages Conforming to 802.1d Standard
# Activate the settings of the MST region manually
Mstp Configuration Example
Configure Switch a # Enter MST region view
Configure Switch D # Enter MST region view
Configure Switch B # Enter MST region view
Configure Switch C # Enter MST region view
# Configure the MST region
Configure Switch C # Enable Mstp
VLAN-VPN tunnel Configuration Example
Configure Switch a # Enable Mstp
Configure Switch B # Enable Mstp
# Configure GigabitEthernet 1/0/1 as a trunk port
# Enable the VLAN-VPN tunnel function
# Configure GigabitEthernet 1/0/2 as a trunk port
Configure Switch D # Enable Mstp
Table of Contents
Introduction to
802.1x Configuration
Architecture of 802.1x Authentication
Valid direction of a controlled port
Port access entity
Port access control method
Controlled port and uncontrolled port
Format of an EAPoL packet
Mechanism of an 802.1x Authentication System
Encapsulation of EAPoL Messages
Format of an EAP packet
EAP relay mode
802.1x Authentication Procedure
Fields added for EAP authentication
Describes the basic EAP-MD5 authentication procedure
EAP terminating mode
9802.1x authentication procedure in EAP terminating mode
Timers Used
Checking the supplicant system
Additional 802.1x Features Implemented
Guest Vlan function
Checking the client version
Enabling 802.1x re-authentication
Introduction to 802.1x Configuration
Dot1x
Basic 802.1x Configuration
Configuring Basic 802.1x Functions
Dot1x port-control authorized-force
Dot1x authentication-method chap
Dot1x handshake enable
Dot1x interface interface-list
Dot1x retry max-retry-value
Timer and Maximum User Number Configuration
Dot1x max-user user-number
Configuring Proxy Checking
Advanced 802.1x Configuration
Configuring Client Version Checking
Dot1x port-method portbased
Enabling DHCP-triggered Authentication
Configuring Guest Vlan
Dot1x dhcp-launch
Dot1x re-authenticate
Configuring 802.1x Re-Authentication
Configuring the 802.1x Re-Authentication Timer
Displaying and Maintaining
802.1x Configuration Example
# Enable 802.1x on GigabitEthernet 1/0/1 port
# Enable 802.1x globally
# Create the domain named aabbcc.net and enter its view
# Set the default user domain to be aabbcc.net
# Create a local access user account
Quick EAD Deployment Overview
Quick EAD Deployment Configuration
Configuring Quick EAD Deployment
Introduction to Quick EAD Deployment
Dot1x free-ip ip-address
Configuring a free IP range
Setting the ACL timeout period
Dot1x url url-string
Period is 30 minutes
Quick EAD Deployment Configuration Example
Displaying and Maintaining Quick EAD Deployment
Solution
Troubleshooting
System-Guard Overview
System-Guard Configuration
Configuring the System-Guard Feature
Configuring the System-Guard Feature
Displaying and Maintaining System-Guard
Table of Contents
Page
Introduction to AAA
Authentication
Authorization
AAA Overview
Introduction to ISP Domain
Introduction to AAA Services
What is Radius
Accounting
1Databases in a Radius server
Basic message exchange procedure in Radius
Client transmits this message to the server to determine if
Radius message format
Code Message type Message description
Direction client-server
Type field value Attribute type
Introduction to Hwtacacs
What is Hwtacacs
5Network diagram for a typical Hwtacacs application
Basic message exchange procedure in Hwtacacs
6AAA implementation procedure for a telnet user
Page
Configuration Introduction
AAA Configuration
AAA Configuration Task List
Creating an ISP Domain and Configuring Its Attributes
Self-service-url disable
Configuring an AAA Scheme for an ISP Domain
Configuring a combined AAA scheme
Messenger time enable limit
Hwtacacs-scheme
Configuring separate AAA schemes
Domain isp-name
Radius-scheme-name local
Accounting none
Configuring Dynamic Vlan Assignment
Local local none Authorization none
Integer string
Configuring the Attributes of a Local User
Domain isp-name
Vlan-assignment-mode
Access-limit
Password-display-mode
Service-type ftp lan-access
Authorization vlan string
Cut down user
Radius Configuration Task List
Cutting Down User Connections Forcibly
Follow these steps to cut down user connections forcibly
Servers
Configuring
Radius scheme
Configuring Radius Authentication/Authorization Servers
Radius client enable
Creating a Radius Scheme
Ip-address port-number
Configuring Radius Accounting Servers
Primary authentication
Secondary authentication
Retry stop-accounting
Configuring Shared Keys for Radius Messages
Secondary accounting
Stop-accounting-buffer
Key accounting string
Configuring the Type of Radius Servers to be Supported
Key authentication string
Optional Servers to be supported
Configuring the Status of Radius Servers
Server-type extended
Block active
State primary authentication
Authentication block
Calling-station-id mode
Local-server nas-ip ip-address
Configuring the Local Radius Authentication Server Function
Local-server enable
Key password
Configuring Timers for Radius Servers
Enabling the User Re-Authentication at Restart Function
Times interval interval
Hwtacacs Configuration Task List
Accounting-on enable send
Hwtacacs scheme
Configuring Tacacs Authentication Servers
Creating a Hwtacacs Scheme
Ip-address port
Configuring Tacacs Authorization Servers
Primary authorization
Secondary authorization
Function is enabled Number of transmission
Configuring Tacacs Accounting Servers
Configuring Shared Keys for Hwtacacs Messages
Follow these steps to configure Tacacs accounting servers
Data-flow-format packet
Authentication string
Key accounting
Mega-byte
Optional By default, the real-time Interval
Configuring the Timers Regarding Tacacs Servers
Scheme exists Set the response timeout time
Optional By default, the response timeout Tacacs servers
Displaying and maintaining Radius protocol information
Displaying and Maintaining AAA
Displaying and maintaining AAA information
Displaying and maintaining Hwtacacs protocol information
AAA Configuration Examples
Remote Radius Authentication of Telnet/SSH Users
# Associate the ISP domain with the Radius scheme
# Adopt AAA authentication for Telnet users
# Configure an ISP domain
# Configure a Radius scheme
# Create and configure a local user named telnet
Local Authentication of FTP/Telnet Users
# Configure the domain name of the Hwtacacs scheme to hwtac
Hwtacacs Authentication and Authorization of Telnet Users
Possible reasons and solutions
Troubleshooting AAA
Troubleshooting Radius Configuration
Troubleshooting Hwtacacs Configuration
Typical Network Application of EAD
EAD Configuration
Introduction to EAD
Ip-address
EAD Configuration
EAD Configuration Example
Security-policy-server
# Associate the domain with the Radius scheme
# Configure the IP address of the security policy server
Table of Contents
Performing MAC Authentication Locally
MAC Authentication Configuration
MAC Authentication Overview
Performing MAC Authentication on a Radius Server
Related Concepts
Configuring Basic MAC Authentication Functions
MAC Authentication Timers
Mac-authentication
Uppercase fixedpassword password
Mac-authentication interface
Mac-authentication Quit
Mac-authentication authmode
Configuring a Guest Vlan
MAC Address Authentication Enhanced Function Configuration
Guest-vlan-reauth interval
Mac-authentication timer
Guest-vlan vlan-id
Max-auth-num user-number
Configure the maximum number
MAC address authentication Number of MAC address
Reset mac-authentication statistics
Displaying and Maintaining MAC Authentication
MAC Authentication Configuration Example
Display mac-authentication
# Add an ISP domain named aabbcc.net
# Add a local user Specify the username and password
Set the service type to lan-access
# Specify to perform local authentication
Table of Contents
Net-id
IP Addressing Configuration
IP Addressing Overview
IP Address Classes
Class Address range Remarks
Special Case IP Addresses
Subnetting and Masking
Mask-length sub
Configuring IP Addresses
Ip address ip-address mask
Network requirement
IP Address Configuration Examples
IP Address Configuration Example
Displaying and Maintaining IP Addressing
4Network diagram for IP address configuration
Page
IP Performance Overview
IP Performance Configuration
Configuring IP Performance
Disabling Sending of Icmp Error Packets
Displaying and Maintaining IP Performance Configuration
Table of Contents
IP Address Assignment Policy
Dhcp Overview
Introduction to Dhcp
Dhcp IP Address Assignment
Obtaining IP Addresses Dynamically
Updating IP Address Lease
Dhcp Packet Format
Protocols and Standards
Dhcp Relay Agent Fundamentals
Dhcp Relay Agent Configuration
Introduction to Dhcp Relay Agent
Usage of Dhcp Relay Agent
Introduction to Option
Padding content of Option
Dhcp Relay Agent Support for Option
Mechanism of Option 82 supported on Dhcp relay agent
2Padding contents for sub-option 1 of Option
Ip-address &1-8
Configuring the Dhcp Relay Agent
Dhcp Relay Agent Configuration Task List
Dhcp-server groupNo ip
Configuring address checking
Configuring Dhcp Relay Agent Security Functions
Mac-address
Address-check enable
Dhcp relay hand enable
Dhcp-security static ip-address
Prerequisites
Configuring the Dhcp Relay Agent to Support Option
Configuring the Dhcp relay agent to support Option
Enabling unauthorized Dhcp server detection
Dhcp Relay Agent Configuration Example
Displaying and Maintaining Dhcp Relay Agent Configuration
Analysis
Troubleshooting Dhcp Relay Agent Configuration
Symptom
Solution
Page
Function of Dhcp Snooping
Dhcp Snooping Configuration
Dhcp Snooping Overview
Overview of Dhcp Snooping Option
Padding content and frame format of Option
2Extended format of the circuit ID sub-option
Mechanism of DHCP-snooping Option
Overview of IP Filtering
Dhcp-snooping information format command or
Sub-option configuration Dhcp snooping device will…
Dhcp-snooping information format command or the default HEX
IP static binding table
Dhcp Snooping Configuration
Configuring Dhcp Snooping
DHCP-snooping table
Required Specify the current port as a
Configuring Dhcp Snooping to Support Option
DHCP-Snooping Option 82 Support Configuration Task List
Enable DHCP-snooping Option 82 support
Strategy drop keep replace
Configure a handling policy for Dhcp packets with Option
Configure the storage format of Option
Dhcp-snooping information
String
Configure the circuit ID sub-option
Configure the remote ID sub-option
Vlan vlan-id circuit-id string
Vlan vlan-id remote-id
Configuring IP Filtering
Configure the padding format for Option
Remote-id sysname string
DHCP-Snooping Option 82 Support Configuration Example
Dhcp Snooping Configuration Example
# Specify GigabitEthernet 1/0/5 as the trusted port
IP Filtering Configuration Example
# Enable Dhcp snooping on Switch
# Enable DHCP-snooping Option 82 support
# Specify GigabitEthernet 1/0/1 as the trusted port
7Network diagram for IP filtering configuration
Display ip source static
Displaying and Maintaining Dhcp Snooping Configuration
Display dhcp-snooping
Trust
Follow these steps to configure a DHCP/BOOTP client
DHCP/BOOTP Client Configuration
Introduction to Bootp Client
Configuring a DHCP/BOOTP Client
Dhcp-alloc
Dhcp Client Configuration Example
Ip address bootp-alloc
Display related information on a
Displaying and Maintaining DHCP/BOOTP Client Configuration
Display bootp client interface
Bootp client
Table of Contents
ACL Matching Order
ACL Configuration
ACL Overview
Being applied to the hardware directly
Ways to Apply an ACL on a Device
Depth-first match order for rules of a basic ACL
Depth-first match order for rules of an advanced ACL
Types of ACLs Supported by Devices
ACL Configuration
Configuring Time Range
End-time end-date to end-time end-date
Time-range time-name start-time to end-time
Days-of-the-week from start-time start-date to
End-time end-date from start-time start-date to
Rule-string Rule-string , refer to ACL Command
Configuring Basic ACL
Auto config
Rule rule-id permit deny
Configuring Advanced ACL
Match-order auto config
Rule-string , refer to ACL Command
Rule-string Refer to ACL Command
Configuring Layer 2 ACL
ACL Assignment
Packet-filter inbound acl-rule
Configure procedure
Assigning an ACL Globally
Assigning an ACL to a Vlan
Inbound acl-rule
Assigning an ACL to a Port Group
System-view Packet-filter vlan vlan-id
Assigning an ACL to a Port
Displaying and Maintaining ACL
Examples for Upper-layer Software Referencing ACLs
Example for Controlling Telnet Login Users by Source IP
Example for Controlling Web Login Users by Source IP
SwitchPC
Examples for Applying ACLs to Hardware
Basic ACL Configuration Example
Advanced ACL Configuration Example
# Apply ACL 3000 on GigabitEthernet 1/0/1
Layer 2 ACL Configuration Example
# Apply ACL 4000 on GigabitEthernet 1/0/1
Example for Applying an ACL to a Vlan
# Apply ACL 3000 to Vlan
Table of Contents
Page
New Applications and New Requirements
QoS Configuration
Traditional Packet Forwarding Service
Introduction to QoS
Traffic Classification
QoS Supported by Devices
Major Traffic Control Techniques
IP Precedence decimal IP Precedence binary Description
Precedence
IP precedence, ToS precedence, and Dscp precedence
Dscp value decimal Dscp value binary Description
802.1p priority
802.1p priority decimal 802.1p priority binary Description
Priority Trust Mode
Trusting the Dscp precedence
Trusting the 802.1p precedence
Dscp precedence Target Dscp precedence
Token bucket
Protocol Priority
Priority Marking
Traffic Policing and Traffic Shaping
Traffic shaping
Evaluating the traffic with the token bucket
Traffic policing
Queue Scheduling
Traffic Redirecting
Vlan Mapping
SP queuing
7Diagram for SP queuing
Sdwrr
Burst
QoS Configuration
QoS Configuration Task List
Flow-based Traffic Accounting
Priority-trust dscp automap
Configuring Priority Trust Mode
Priority priority-level
Priority-trust cos automap
Qos cos-drop-precedence-map
Configuring Priority Mapping
Qos cos-local-precedence-map
Qos dscp-cos-map dscp-list cos-value
Qos cos-dscp-map cos0-map-dscp
Qos dscp-local-precedence-map dscp-list
Qos dscp-drop-precedence-map dscp-list
Page
Ip-precedence
Setting the Priority of Protocol Packets
System-view Protocol-priority
Protocol-type
Traffic-priority vlan vlan-id inbound acl-rule
Marking Packet Priority
Traffic-priority inbound acl-rule dscp
Dscp-value cos cos-value
Required Matching specific ACL rules
Configuring Traffic Policing
Conform con-action exceed
Reset traffic-limit inbound acl-rule
Reset traffic-limit vlan vlan-id inbound
Traffic-limit inbound acl-rule target-rate
Disabled Clear the traffic
Configuring Traffic Shaping
View Configure traffic
By default, traffic policing is Policing
Traffic-redirect inbound acl-rule interface
Configuring Traffic Redirecting
Configuration examples
Traffic-shape queue
Traffic-redirect vlan vlan-id inbound acl-rule
Acl-rule remark-vlan vlan-id
Configuring Vlan Mapping
Configuring Queue Scheduling
Traffic-remark-vlanid inbound
Queue-scheduler wrr group1
Queue-id queue-weight &1-8
Group2 queue-id queue-weight
Undo queue-scheduler queue-id
Traffic-statistic inbound acl-rule
Reset traffic-statistic inbound
Collecting/Clearing Traffic Statistics
Collect the statistics on Packets matching specific ACL
Traffic-statistic vlan vlan-id
Reset traffic-statistic vlan vlan-id
Reset traffic-statistic inbound acl-rule
Refer to Burst for information about the burst function
Configuring Traffic Mirroring
Follow these steps to enable the burst function
Enabling the Burst Function
Mirrored-to vlan vlan-id
Monitor-port
Mirrored-to inbound acl-rule
Monitor-interface
Required Mirroring for packets that
Traffic mirroring configuration
Required Destination port Exit current view
Displaying and Maintaining QoS
Configuration Example of Traffic Policing
QoS Configuration Example
Page
Manual application mode
QoS Profile Configuration
QoS Profile Application Mode
Dynamic application mode
Applying a QoS Profile
QoS Profile Configuration
QoS Profile Configuration Task List
Configuring a QoS Profile
System-view Apply qos-profile
Displaying and Maintaining QoS Profile
Qos-profile port-based
Undo qos-profile port-based
1Network diagram for QoS profile configuration
QoS Profile Configuration Example
# Enable
Table of Contents
Mirroring Overview
Mirroring Configuration
Remote Port Mirroring
Local Port Mirroring
1Ports involved in the mirroring operation
Switch Ports involved Function
MAC-Based Mirroring
VLAN-Based Mirroring
Configuring Local Port Mirroring
Mirroring Configuration
Configuration on the device acting as a source switch
Configuring Remote Port Mirroring
Configuration on the device acting as a destination switch
Monitor-port monitor-port
Configuring MAC-Based Mirroring
Remote-probe-vlan-id
Remote-destination
Mirroring-group group-id Mirroring-mac mac vlan
Configuring VLAN-Based Mirroring
Local remote-source
Mirroring-group group-id Mirroring-vlan vlan-id
Mirroring Configuration Example
Local Port Mirroring Configuration Example
Displaying and Maintaining Port Mirroring
Configure Switch C # Create a local mirroring group
Remote Port Mirroring Configuration Example
# Configure Vlan 10 as the remote-probe Vlan
4Network diagram for remote port mirroring
# Configure Vlan 10 as the remote-probe Vlan
Page
Table of Contents
ARP Message Format
ARP Configuration
Introduction to ARP
ARP Function
Proteon ProNET Token Ring
Field Description
Value Description
Experimental Ethernet
Chaos
ARP entry Generation Method Maintenance Mode
ARP Table
ARP Process
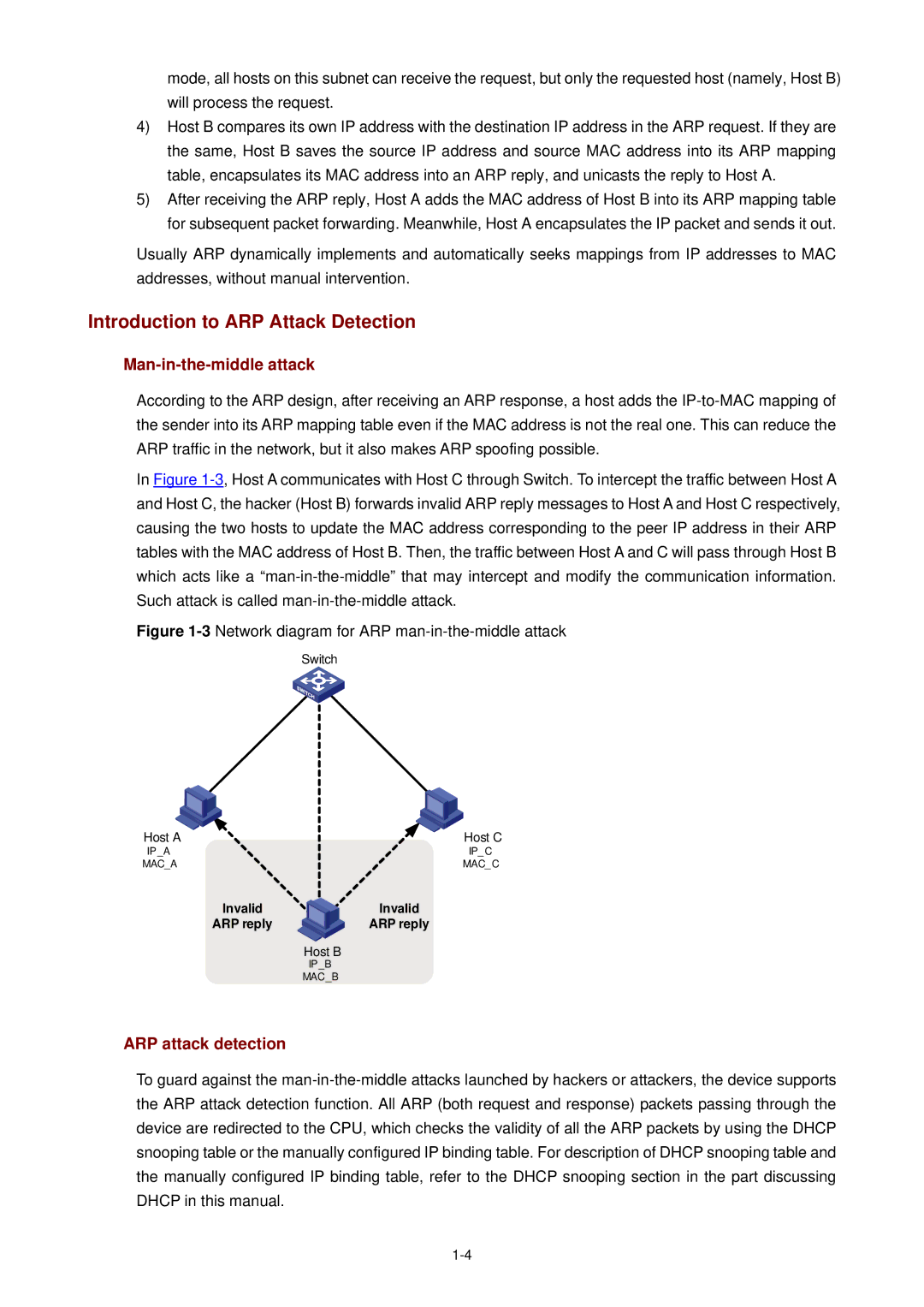
ARP attack detection
Introduction to ARP Attack Detection
Man-in-the-middle attack
Introduction to Gratuitous ARP
Configuring ARP
Configuring ARP Basic Functions
Arp timer aging aging-time
Arp detection trust
Configuring ARP Attack Detection
Arp check enable
Arp detection enable
Gratuitous-arp-learning
Configuring Gratuitous ARP
Arp restricted-forwarding
Displaying and Maintaining ARP
ARP Configuration Example
ARP Basic Configuration Example
ARP Attack Detection Configuration Example
# Enable ARP attack detection on all ports in Vlan
# Enable Dhcp snooping on Switch a
Table of Contents
Snmp Versions
Snmp Configuration
Snmp Overview
Snmp Operation Mechanism
Public MIB
MIB attribute MIB content Related RFC
Supported MIBs
MIB II based on TCP/IP network device RFC
Snmp-agent sys-info
Configuring Basic Snmp Functions
Configuring basic Snmp functions for SNMPv1 or SNMPv2c
Snmp-agent
Configuring basic Snmp functions for SNMPv3
Configuring Basic Trap
Configuring Trap Parameters
Configuring Extended Trap
Displaying and Maintaining Snmp
Snmp Configuration Examples
Snmp Configuration Examples
Enabling Logging for Network Management
2Network diagram for Snmp configuration
Network procedure
Configuring the NMS
Working Mechanism of Rmon
Rmon Configuration
Introduction to Rmon
Commonly Used Rmon Groups
Rmon Configuration
Displaying and Maintaining Rmon
Rmon Configuration Examples
Configuration procedures
# Display the Rmon extended alarm entry numbered
Table of Contents
Multicast Overview
Information Transmission in the Unicast Mode
Multicast Overview
1Information transmission in the unicast mode
Information Transmission in the Broadcast Mode
2Information transmission in the broadcast mode
Information Transmission in the Multicast Mode
Roles in Multicast
3Information transmission in the multicast mode
Application of multicast
Multicast Models
Advantages and Applications of Multicast
Advantages of multicast
SSM model
Multicast Architecture
ASM model
SFM model
Reserved multicast addresses IP addresses for permanent
IP multicast address
Class D address range Description
Ethernet multicast MAC address
Layer 3 multicast protocols
Multicast Protocols
5Positions of Layer 3 multicast protocols
Layer 2 multicast protocols
Implementation of the RPF Mechanism
Multicast Packet Forwarding Mechanism
7RPF check process
RPF Check
Page
Basic Concepts in Igmp Snooping
Igmp Snooping Configuration
Igmp Snooping Overview
Principle of Igmp Snooping
Work Mechanism of Igmp Snooping
Timer Description Message before Action after expiry Expiry
When receiving a leave message
When receiving a general query
When receiving a membership report
Complete the following tasks to configure Igmp Snooping
Igmp Snooping Configuration
Igmp Snooping Configuration Task List
Igmp-snooping version
Configuring the Version of Igmp Snooping
Igmp-snooping enable
Enabling Igmp Snooping
Enabling fast leave processing in system view
Configuring Timers
Configuring Fast Leave Processing
Enabling fast leave processing in Ethernet port view
Configuring a Multicast Group Filter
Enable fast leave processing
Required By default, the fast leave For specific VLANs
Acl-number vlan vlan-list
Configuring a multicast group filter in system view
Configuring a multicast group filter in Ethernet port view
Igmp -snooping group -policy
Vlan vlan list overflow-replace
Configuring Igmp Querier
Igmp-snooping group-limit limit
Suppressing Flooding of Unknown Multicast Traffic in a Vlan
Configuring Static Member Port for a Multicast Group
Multicast static-group
Configuring a Static Router Port
Ethernet port view
Vlan interface view
Source-ip source-address
Configuring a Port as a Simulated Group Member
Vlan view
Igmp host-join group-address
Vlan-mapping vlan
Configuring a Vlan Tag for Query Messages
Configuring Multicast Vlan
Port trunk permit vlan vlan-list
Igmp enable
Service-type multicast
Hybrid Port hybrid vlan vlan-id-list
Displaying and Maintaining Igmp Snooping
Igmp Snooping Configuration Examples
Configuring Igmp Snooping
Configure Switch a # Enable Igmp Snooping globally
3Network diagram for Igmp Snooping configuration
GigabitEthernet 1/0/1 is connected to the workstation
Device Device description Networking description
Interface IP address of Vlan 20 is
# Configure Vlan
4Network diagram for multicast Vlan configuration
Symptom Multicast function does not work on the device
Troubleshooting Igmp Snooping
Mac-address multicast
Common Multicast Configuration
Common Multicast Configuration
Configuring a Multicast MAC Address Entry
Display mac-address multicast
Displaying and Maintaining Common Multicast Configuration
Configuring Dropping Unknown Multicast Packets
Unknown-multicast drop
Table of Contents
Applications of NTP
NTP Configuration
Introduction to NTP
Implementation Principle of NTP
1Implementation principle of NTP
NTP Implementation Modes
Broadcast mode
Server/client mode
Symmetric peer mode
NTP implementation Configuration on the device Mode
Multicast mode
Complete the following tasks to configure NTP
NTP Configuration Task List
Configuring NTP Implementation Modes
Configuring NTP Server/Client Mode
Configuring the NTP Symmetric Peer Mode
NTP broadcast server
Configuring NTP Broadcast Mode
Configure the device to work
Ntp-service broadcast-server
Configuring the device to work in the multicast client mode
Configuring NTP Multicast Mode
Configuring the device to work in the multicast server mode
Server synchronization
Configuring Access Control Right
Configuring NTP Authentication
Ntp-service access peer
Role of device Working mode
Configuring NTP authentication on the client
Configuring NTP authentication on the server
While Configuring
Configuring Optional NTP Parameters
Configure on NTP Broadcast Server
Mode and NTP multicast Broadcast
Max-dynamic-sessions
Displaying and Maintaining NTP Configuration
NTP Configuration Examples
Disabling an Interface from Receiving NTP messages
# Set Device a as the NTP server of Device B
# Set Device C as the peer of Device B
Configuring NTP Symmetric Peer Mode
Configure Device C # Set Device a as the NTP server
8Network diagram for the NTP broadcast mode configuration
# Set Device a as a broadcast client
Configure Device C # Enter system view
9Network diagram for NTP multicast mode configuration
# Enable the NTP authentication function
Configuring NTP Server/Client Mode with Authentication
Configure Device B # Enter system view
# Specify the key 42 as a trusted key
Table of Contents
Algorithm and Key
SSH Configuration
SSH Overview
Introduction to SSH
Stages Description
Asymmetric Key Algorithm
SSH Operating Process
Key negotiation
Authentication negotiation
Version negotiation
Data exchange
Configuring the SSH Server
Session request
Command-authorization
SSH Server Configuration Tasks
Configuring the Protocol Support for the User Interface
Authentication-mode scheme
Generating/Destroying a RSA or DSA Key Pair
Exporting the RSA or DSA Public Key
Creating an SSH User and Specify an Authentication Type
Stelnet sftp all
Specifying a Service Type for an SSH User
Configuring SSH Management
Ssh user username service-type
Configuring the Client Public Key on the Server
Rsa peer-public-key keyname
Public-key-code end
Peer-public-key end
Publickey rsa-key keyname
Assigning a Public Key to an SSH User
Specifying a Source IP Address/Interface for the SSH Server
Ssh user username assign
Configuring the SSH Client Using an SSH Client Software
Configuring the SSH Client
SSH Client Configuration Tasks
2Generate a client key
Generate a client key
4Generate the client keys
Launch PuTTY.exe. The following window appears
Specify the IP address of the Server
As shown in -7, select SSH under Protocol
Select a protocol for remote connection
Select an SSH version
8SSH client configuration interface
Open an SSH connection with publickey authentication
10SSH client interface
Configure whether first-time authentication is supported
Configuring the SSH Client on an SSH2-Capable Device
Open an SSH connection with password authentication
Establish the connection between the SSH client and server
Ssh2 source-interface
Displaying and Maintaining SSH Configuration
Specifying a Source IP address/Interface for the SSH client
Ssh2 source-ip ip-address
# Generate RSA and DSA key pairs
SSH Configuration Examples
# Enable the user interfaces to support SSH
Page
14SSH client interface
# Assign the public key Switch001 to client client001
# Set the client’s command privilege level to
Page
18Generate a client key pair
Page
22SSH client interface
Device system-view Device interface vlan-interface
# Establish a connection to the server
# Generate a DSA key pair
# Set the user command privilege level to
# Assign the public key Switch001 to user client001
25Network diagram of SSH client configuration
# Assign public key Switch001 to user client001
# Set AAA authentication on user interfaces
# Configure the user interfaces to support SSH
# Establish the SSH connection to server
# Specify the host public key pair name of the server
Table of Contents
Introduction to File System
File System Management Configuration
File System Configuration
File System Configuration Tasks
File Operations
Format device
Prompt Mode Configuration
Flash Memory Operations
Execute filename
File prompt alert quiet
File System Configuration Example
Introduction to File Attributes
File Attribute Configuration
Attribute Description Feature Identifier
Configuring File Attributes
Table of Contents
Description Remarks
FTP and Sftp Configuration
Introduction to FTP and Sftp
Introduction to FTP
Introduction to Sftp
FTP Configuration
FTP Configuration The Device Operating as an FTP Server
Service-type ftp
Enabling an FTP server
Configuring connection idle time
Ftp timeout minutes
Ftp disconnect user-name
Disconnecting a specified user
Ftp-server source-interface
Ftp-server source-ip ip-address
Configuring the banner for an FTP server
Displaying FTP server information
FTP Configuration The Device Operating as an FTP Client
Basic configurations on an FTP client
Close
Cdup
Lcd
Disconnect
Configuration Example The Device Operating as an FTP Server
# Upload the config.cfg file. ftp put config.cfg
FTP Banner Display Configuration Example
4Network diagram for FTP banner display configuration
# Enter the authorized directory on the FTP server
Follow these steps to enable an Sftp server
Sftp Configuration
Sftp Configuration The Device Operating as an Sftp Server
Complete the following tasks to configure Sftp
Time for the Sftp server Minutes by default
Sftp Configuration The Device Operating as an Sftp Client
Basic configurations on an Sftp client
Ftp timeout time-out-value
Remove remote-file
Help all command-name
Sftp host-ip host-name
Delete remotefile
Display sftp source-ip
Sftp Configuration Example
Sftp source-interface
Sftp source-ip ip-address
# Create a local user client001
# Specify the SSH authentication mode as AAA
# Specify the service type as Sftp
# Enable the Sftp server
Sftp-client
# Exit Sftp
Introduction to Tftp
Tftp Configuration
Tftp Configuration
Complete the following tasks to configure Tftp
Tftp-server acl acl-number
Tftp Configuration The Device Operating as a Tftp Client
Basic configurations on a Tftp client
Tftp ascii binary
Display tftp source-ip
Tftp Configuration Example
Tftp source-interface
Tftp source-ip ip-address
Device tftp 1.1.1.2 get config.cfg config.cfg
Table of Contents
Classification of system information
Information Center
Information Center Overview
Introduction to Information Center
Ten channels and six output directions of system information
Module name Description
Outputting system information by source module
System Information Format
Sysname
Priority
Timestamp
Introduction to the Information Center Configuration Tasks
Information Center Configuration
Set for the system
Configuring Synchronous Information Output
Setting to output system information to the console
Setting to Output System Information to the Console
Terminal logging
Enabling system information display on the console
Terminal monitor
Terminal debugging
Info-center monitor channel
Setting to Output System Information to a Monitor Terminal
Setting to output system information to a monitor terminal
Enabling system information display on a monitor terminal
Info-center loghost source
Setting to Output System Information to a Log Host
Info-center loghost
Info-center source
Setting to Output System Information to the Trap Buffer
Setting to Output System Information to the Log Buffer
Info-center trapbuffer
Info-center snmp channel
Setting to Output System Information to the Snmp NMS
Info-center logbuffer
Log Output to a Unix Log Host
Information Center Configuration Examples
Displaying and Maintaining Information Center
# mkdir /var/log/Switch # touch /var/log/Switch/information
Log Output to a Linux Log Host
2Network diagram for log output to a Linux log host
Log Output to the Console
3Network diagram for log output to the console
4Network diagram
# Enable terminal display
Table of Contents
Introduction to Loading Approaches
Host Configuration File Loading
Remote Loading Using FTP
Loading procedure using FTP client
Restart Switch
Loading procedure using FTP server
2Remote loading using FTP server
Use the put command to upload the file config.cfg to Switch
Remote Loading Using Tftp
Basic System Configuration
Basic System Configuration and Debugging
Display clock
Displaying the System Status
Debugging the System
Enabling/Disabling System Debugging
Displaying Operating Information about Modules in System
Displaying Debugging Status
Tracert
Network Connectivity Test
Network Connectivity Test
Ping
Device Management
Device Management Configuration
Device Management Configuration Tasks
Rebooting the Device
Schedule reboot regularity
Scheduling a Reboot on the Device
Schedule reboot at hhmm
Schedule reboot delay
Identifying pluggable transceivers
Identifying and Diagnosing Pluggable Transceivers
Introduction to pluggable transceivers
Diagnosing pluggable transceivers
Table of Contents
Introduction to VLAN-VPN
VLAN-VPN Configuration
VLAN-VPN Overview
Implementation of VLAN-VPN
Adjusting the Tpid Values of VLAN-VPN Packets
Protocol type Value
VLAN-VPN Configuration
Enabling the VLAN-VPN Feature for a Port
Vlan-vpn tpid value
Tpid Adjusting Configuration
Vlan-vpn uplink enable
Displaying and Maintaining VLAN-VPN
4Network diagram for VLAN-VPN configuration
VLAN-VPN Configuration Example
Data transfer process
SwitchA vlan-vpn tpid
Page
Selective QinQ Overview
Selective QinQ Configuration
Selective QinQ Overview
Vlan-vpn vid vlan-id
Selective QinQ Configuration
Enabling the Selective QinQ Feature for a Port
Inner-to-Outer Tag Priority Mapping
Vlan-vpn priority
Selective QinQ Configuration Example
Configuring the Inner-to-Outer Tag Priority Mapping Feature
Processing Private Network Packets by Their Types
# Enable the VLAN-VPN feature on GigabitEthernet 1/0/3
2Network diagram for selective QinQ configuration
SwitchA-GigabitEthernet1/0/3 vlan-vpn enable
Page
Table of Contents
Introduction to HWPing
HWPing Configuration
HWPing Overview
Test parameter Description
Test Types Supported by HWPing
HWPing Test Parameters
Supported test types Description
Dns-server
Username and password
Dns
HWPing server configuration tasks
HWPing Configuration
Configuration on a HWPing Server
HWPing client configuration
HWPing Client Configuration
HWPing server configuration
Datasize size
Timeout time
Test-enable
Count times
Test-type ftp
Test-type dhcp
Source-port port-number
Filename file-name
Password password
Ftp-operation get put
Username name
Http-operation get post
Destination-ip command to
Dns-server ip-address
Test-type http
Test-type jitter
Destination-port
Test-type snmpquery
Jitter-packetnum number
Jitter-interval interval
This IP address and the one
Configure the destination Configured on the HWPing
Server for listening services
Operation- tag
Tcppublic
Hwping-server
Tcpconnect ip-address7
Test-type tcpprivate
Udppublic
Test-type udpprivate
Test-type dns
Time Three seconds Optional Configure the service type
Address is specified
Configuring HWPing client to send Trap messages
Icmp Test
HWPing Configuration Example
Administrator-name operation-tag
Displaying and Maintaining HWPing
# Display test results
Dhcp Test
# Configure the test type as dhcp
FTP Test
# Configure the source IP address
# Set the probe timeout time to 30 seconds
Http Test
# Configure the test type as http
# Configure the IP address of the Http server as
Jitter Test
# Configure the IP address of the HWPing server as
Network diagram
Configure HWPing Client Switch a # Enable the HWPing client
# Configure the test type as jitter
Snmp Test
# Configure the test type as snmp
7Network diagram for the Snmp test
TCP Test Tcpprivate Test on the Specified Ports
8Network diagram for the Tcpprivate test
# Configure the test type as tcpprivate
UDP Test Udpprivate Test on the Specified Ports
# Configure the test type as udpprivate
DNS Test
# Configure the IP address of the DNS server as
# Configure the test type as dns
Index
Table of Contents
Resolution procedure
DNS Configuration
Static Domain Name Resolution
Dynamic Domain Name Resolution
DNS suffixes
Configuring Domain Name Resolution
Configuring Static Domain Name Resolution
Static Domain Name Resolution Configuration Example
DNS Configuration Example
Configuring Dynamic Domain Name Resolution
2Network diagram for static DNS configuration
Dynamic Domain Name Resolution Configuration Example
# Configure com as the DNS suffix
# Configure the IP address 2.1.1.2 for the DNS server
Displaying and Maintaining DNS
Troubleshooting DNS Configuration
Table of Contents
Smart Link group
Smart Link Configuration
Smart Link Overview
Basic Concepts in Smart Link
Control Vlan for sending flush messages
Master port
Slave port
Flush message
Operating Mechanism of Smart Link
Configuring Smart Link
Complete the following tasks to configure Smart Link
Configuring a Smart Link Device
Smart-link flush enable control-vlan vlan-id port
Configuring Associated Devices
Precautions
Flush enable control-vlan
Displaying and Maintaining Smart Link
Smart Link Configuration Example
Implementing Link Redundancy Backup
# Return to system view
# Configure to send flush messages within Vlan
SwitchD system-view
Introduction to Monitor Link
Monitor Link Configuration
How Monitor Link Works
2Network diagram for a Monitor Link group implementation
Creating a Monitor Link Group
Configuring Monitor Link
Configuring the Uplink Port
Port monitor-link group
Configuring a Downlink Port
Uplink
Displaying and Maintaining Monitor Link
Monitor Link Configuration Example
# Create Smart Link group 1 and enter Smart Link group view
# Configure to send flush messages in Vlan
SwitchC monitor-link group
Table of Contents
Advantages of PoE
PoE Configuration
PoE Overview
Introduction to PoE
Maximum Power Provided by Each Electrical Port
PoE Configuration
PoE Features Supported by the Device
PoE Configuration Task List
Poe max-power max-power
Enabling the PoE Feature on a Port
Setting the Maximum Output Power on a Port
Poe enable
Poe priority critical high
Setting PoE Management Mode and PoE Priority of a Port
Setting the PoE Mode on a Port
Poe power-management
Upgrading the PSE Processing Software Online
Configuring the PD Compatibility Detection Function
Poe legacy enable
Poe update refresh
Networking requirements
PoE Configuration Example
Displaying and Maintaining PoE Configuration
PoE Configuration Example
# Upgrade the PSE processing software online
1Network diagram for PoE
Introduction to PoE Profile
PoE Profile Configuration
PoE Profile Configuration
Configuring PoE Profile
All-profile interface
Displaying and Maintaining PoE Profile Configuration
PoE Profile to Port
Display poe-profile
# Create Profile1, and enter PoE profile view
PoE Profile Configuration Example
PoE Profile Application Example
# Create Profile2, and enter PoE profile view
# Display detailed configuration information for Profile1
# Display detailed configuration information for Profile2
Table of Contents
Page
Routing Table
IP Routing Protocol Overview
Introduction to IP Route and Routing Table
IP Route
Page
Routing Protocols and Routing Priority
Routing Protocol Overview
Static Routing and Dynamic Routing
Classification of Dynamic Routing Protocols
Load sharing
Load Sharing and Route Backup
Route backup
Routing Information Sharing
Displaying and Maintaining a Routing Table
Static Route
Static Route Configuration
Introduction to Static Route
Configuring a Static Route
Static Route Configuration
Default Route
Displaying and Maintaining Static Routes
Static Route Configuration Example
# Approach 2 Configure a static route on Switch B
Troubleshooting a Static Route
# Approach 2 Configure a static route on Switch a
# Approach 1 Configure static routes on Switch B
RIP routing database
RIP Configuration
RIP Overview
Basic Concepts
Routing loops prevention
RIP timers
RIP Startup and Operation
Rip
RIP Configuration Task List
Basic RIP Configuration
Configuring Basic RIP Functions
Specifying the RIP version on an interface
Setting the RIP operating status on an interface
RIP Route Control
Rip metricin value
Configuring RIP Route Control
Setting the additional routing metrics of an interface
Configuring RIP route summarization
Disabling the router from receiving host routes
Configuring RIP to filter incoming/outgoing routes
Setting RIP preference
RIP Network Adjustment and Optimization
Configuring RIP-1 packet zero field check
Configuration Tasks
Configuring RIP timers
Configuring split horizon
Simple password md5
Setting RIP-2 packet authentication mode
Configuring RIP to unicast RIP packets
Rip authentication-mode
RIP Configuration Example
Displaying and Maintaining RIP Configuration
Configure Switch C # Configure RIP
Troubleshooting RIP Configuration
Failed to Receive RIP Updates
Configure Switch B # Configure RIP
Filters
IP Route Policy Configuration
IP Route Policy Overview
Introduction to IP Route Policy
Route policy
IP Route Policy Configuration Task List
Route Policy Configuration
For ACL configuration, refer to the part discussing ACL
Defining if-match Clauses and apply Clauses
Defining a Route Policy
Apply cost value
IP Route Policy Configuration Example
Displaying and Maintaining IP Route Policy
If-match ip next-hop acl
Configuration considerations
SwitchC-acl-basic-2000 quit SwitchC acl number
Configuration verification
Precautions
Troubleshooting IP Route Policy
Table of Contents
Protocol UDP port number
UDP Helper Configuration
Introduction to UDP Helper
Configuring UDP Helper
Cross-Network Computer Search Through UDP Helper
UDP Helper Configuration Example
# Enable UDP Helper on Switch a
Displaying and Maintaining UDP Helper
Table of Contents
Appendix a Acronyms
Protocol Independent Multicast-Sparse Mode
Medium Access Control
Non Broadcast MultiAccess
Protocol Independent Multicast-Dense Mode