Appendix B - Wireless Technology
EAP Authentication
EAP (Extensible Authentication Protocol) is an Enterprise authentication protocol that can be used in both a wired and wireless network environment. EAP requires the use of an 802.1x Authentication Server, also known as a RADIUS server. Although over 40 different EAP methods are currently defined, the current internal Modero 802.11g wireless card and accompanying firmware only support the following EAP methods (listed from simplest to most complex):
The following use certificates:
EAP requires the use of an 802.1x authentication server (also known as a RADIUS server). Sophisticated Access Points (such as Cisco) can use a
Microsoft Sever 2003
Juniper Odyssey (once called Funk Odyssey) Meetinghouse AEGIS Server DeviceScape RADIUS Server
Cisco Secure ACS
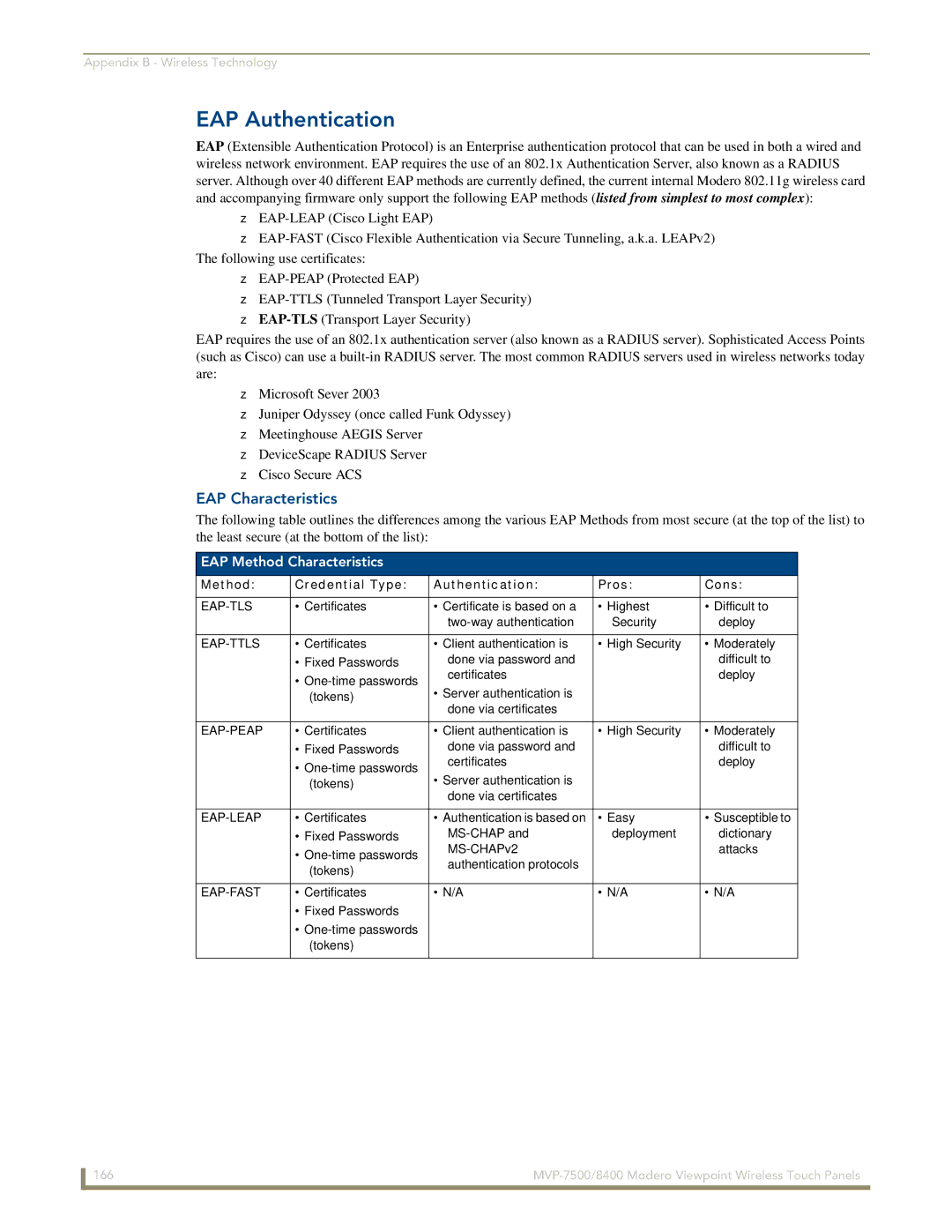
EAP Characteristics
The following table outlines the differences among the various EAP Methods from most secure (at the top of the list) to the least secure (at the bottom of the list):
EAP Method Characteristics
Method: | Credential Type: | Authentication: | Pros: | Cons: |
|
|
|
|
|
• Certificates | • Certificate is based on a | • Highest | • Difficult to | |
|
| Security | deploy | |
|
|
|
|
|
• Certificates | • Client authentication is | • High Security | • Moderately | |
| • Fixed Passwords | done via password and |
| difficult to |
| • | certificates |
| deploy |
| • Server authentication is |
|
| |
| (tokens) |
|
| |
|
| done via certificates |
|
|
|
|
|
|
|
• Certificates | • Client authentication is | • High Security | • Moderately | |
| • Fixed Passwords | done via password and |
| difficult to |
| • | certificates |
| deploy |
| • Server authentication is |
|
| |
| (tokens) |
|
| |
|
| done via certificates |
|
|
|
|
|
|
|
• Certificates | • Authentication is based on | • Easy | • Susceptible to | |
| • Fixed Passwords | deployment | dictionary | |
| • |
| attacks | |
| authentication protocols |
|
| |
| (tokens) |
|
| |
|
|
|
| |
|
|
|
|
|
• Certificates | • N/A | • N/A | • N/A | |
| • Fixed Passwords |
|
|
|
| • |
|
|
|
| (tokens) |
|
|
|
|
|
|
|
|
166 |