Security 15-31
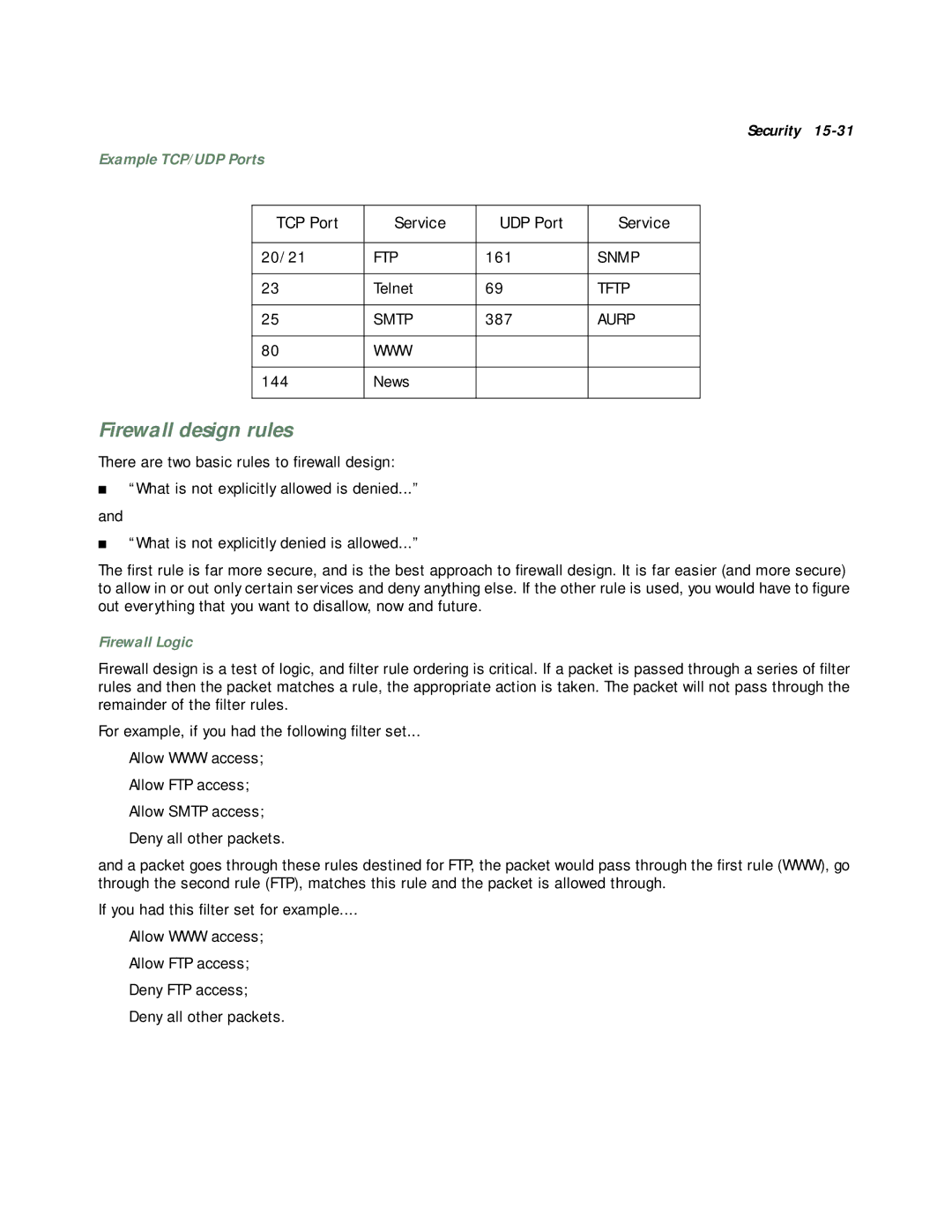
Example TCP/UDP Ports
TCP Port | Service | UDP Port | Service |
|
|
|
|
20/21 | FTP | 161 | SNMP |
|
|
|
|
23 | Telnet | 69 | TFTP |
|
|
|
|
25 | SMTP | 387 | AURP |
|
|
|
|
80 | WWW |
|
|
|
|
|
|
144 | News |
|
|
|
|
|
|
Firewall design rules
There are two basic rules to firewall design:
■“What is not explicitly allowed is denied...”
and
■“What is not explicitly denied is allowed...”
The first rule is far more secure, and is the best approach to firewall design. It is far easier (and more secure) to allow in or out only certain services and deny anything else. If the other rule is used, you would have to figure out everything that you want to disallow, now and future.
Firewall Logic
Firewall design is a test of logic, and filter rule ordering is critical. If a packet is passed through a series of filter rules and then the packet matches a rule, the appropriate action is taken. The packet will not pass through the remainder of the filter rules.
For example, if you had the following filter set...
Allow WWW access;
Allow FTP access;
Allow SMTP access;
Deny all other packets.
and a packet goes through these rules destined for FTP, the packet would pass through the first rule (WWW), go through the second rule (FTP), matches this rule and the packet is allowed through.
If you had this filter set for example....
Allow WWW access;
Allow FTP access;
Deny FTP access;
Deny all other packets.