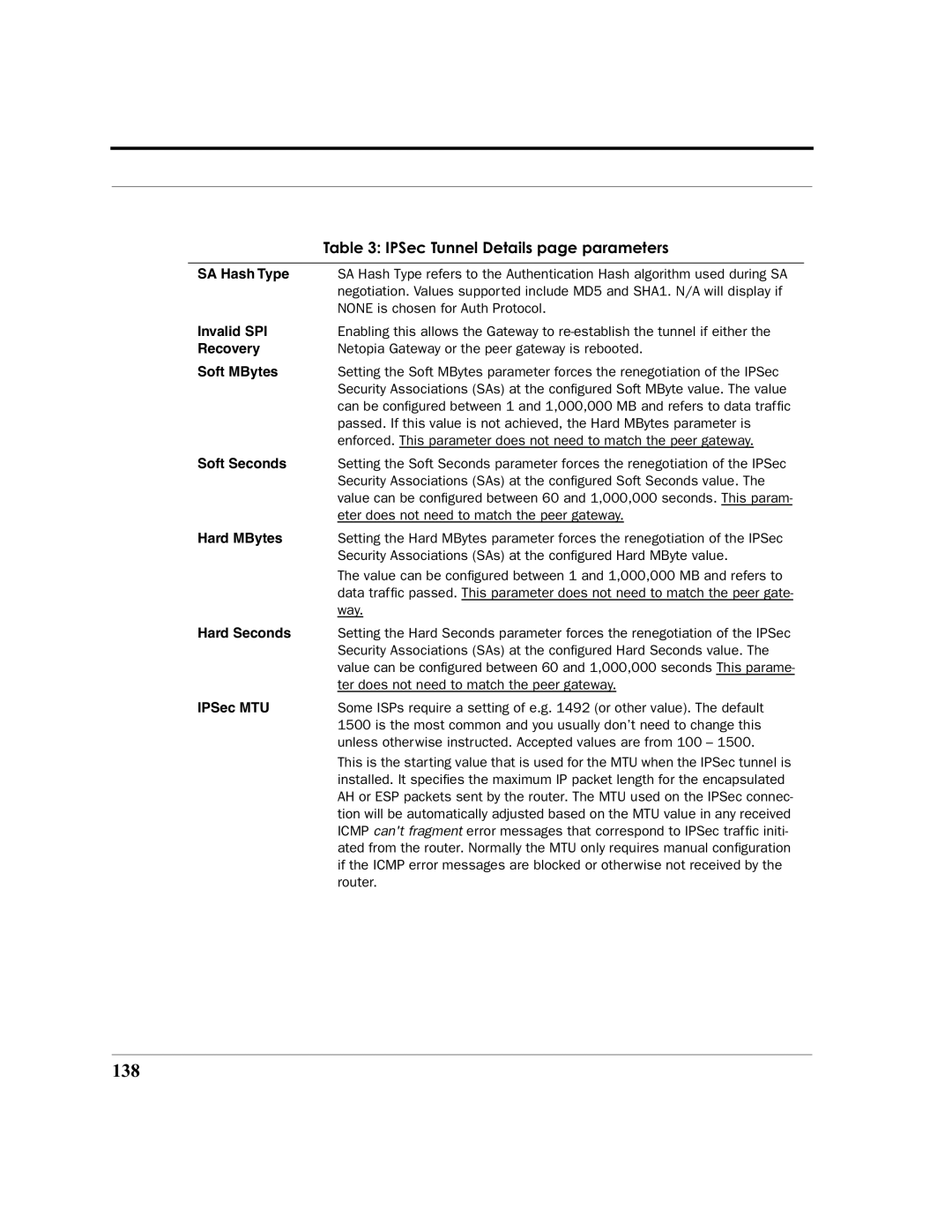
| Table 3: IPSec Tunnel Details page parameters |
|
|
SA Hash Type | SA Hash Type refers to the Authentication Hash algorithm used during SA |
| negotiation. Values supported include MD5 and SHA1. N/A will display if |
| NONE is chosen for Auth Protocol. |
Invalid SPI | Enabling this allows the Gateway to |
Recovery | Netopia Gateway or the peer gateway is rebooted. |
Soft MBytes | Setting the Soft MBytes parameter forces the renegotiation of the IPSec |
| Security Associations (SAs) at the configured Soft MByte value. The value |
| can be configured between 1 and 1,000,000 MB and refers to data traffic |
| passed. If this value is not achieved, the Hard MBytes parameter is |
| enforced. This parameter does not need to match the peer gateway. |
Soft Seconds | Setting the Soft Seconds parameter forces the renegotiation of the IPSec |
| Security Associations (SAs) at the configured Soft Seconds value. The |
| value can be configured between 60 and 1,000,000 seconds. This param- |
| eter does not need to match the peer gateway. |
Hard MBytes | Setting the Hard MBytes parameter forces the renegotiation of the IPSec |
| Security Associations (SAs) at the configured Hard MByte value. |
| The value can be configured between 1 and 1,000,000 MB and refers to |
| data traffic passed. This parameter does not need to match the peer gate- |
| way. |
Hard Seconds | Setting the Hard Seconds parameter forces the renegotiation of the IPSec |
| Security Associations (SAs) at the configured Hard Seconds value. The |
| value can be configured between 60 and 1,000,000 seconds This parame- |
| ter does not need to match the peer gateway. |
IPSec MTU | Some ISPs require a setting of e.g. 1492 (or other value). The default |
| 1500 is the most common and you usually don’t need to change this |
| unless otherwise instructed. Accepted values are from 100 – 1500. |
| This is the starting value that is used for the MTU when the IPSec tunnel is |
| installed. It specifies the maximum IP packet length for the encapsulated |
| AH or ESP packets sent by the router. The MTU used on the IPSec connec- |
| tion will be automatically adjusted based on the MTU value in any received |
| ICMP can't fragment error messages that correspond to IPSec traffic initi- |
| ated from the router. Normally the MTU only requires manual configuration |
| if the ICMP error messages are blocked or otherwise not received by the |
| router. |