Text Part Number OL-23091-01
Americas Headquarters
Page
Iii
N T E N T S
Manager
Editing Values
Telephony Features Available for the Cisco Unified IP Phone
Vii
Network Configuration
Viii
Verifying Dhcp Settings
Technical Specifications D-1
OL-23091-01
Audience
Overview
Organization
Chapter Description
Related Documentation
Cisco Unified Communications Manager Administration
Cisco Unified IP Phone 7900 Series
Cisco Unified Communications Manager Business Edition
Cisco Product Security Overview
Document Conventions
Convention Description
Boldface font
Xiv
An Overview of the Cisco Unified IP Phones
Cisco Unified IP Phone 7962G
Cisco Unified IP Phone 7942G
Cisco Unified IP Phone 7941G and 7941G-GE
Networking Protocol Purpose Usage Notes
What Networking Protocols are Used?
Cppdp
CDP
Dhcp
Cisco Tftp in the Cisco Unified Communications
See Network Configuration Menu,
Manager Features and Services Guide
IPv6 in the Cisco Unified Communications
See the LLDP-MED and Cisco Discovery Protocol
IPv6 Support on Cisco Unified IP Phones
Communications Manager Security Guide
Unified Communications Manager System Guide
Related Topics
Configuring Telephony Features
Feature Overview
Related Topic
Providing Users with Feature Information
See Troubleshooting Guide for Cisco Unified
Topic Reference
Communications Manager
Feature Description
Overview of Supported Security Features
Feature Description
More information, see Device Configuration Menu,
Understanding Security Profiles
More information
Establishing and Identifying Secure Conference Calls
Call Security Interactions and Restrictions
Establishing and Identifying Protected Calls
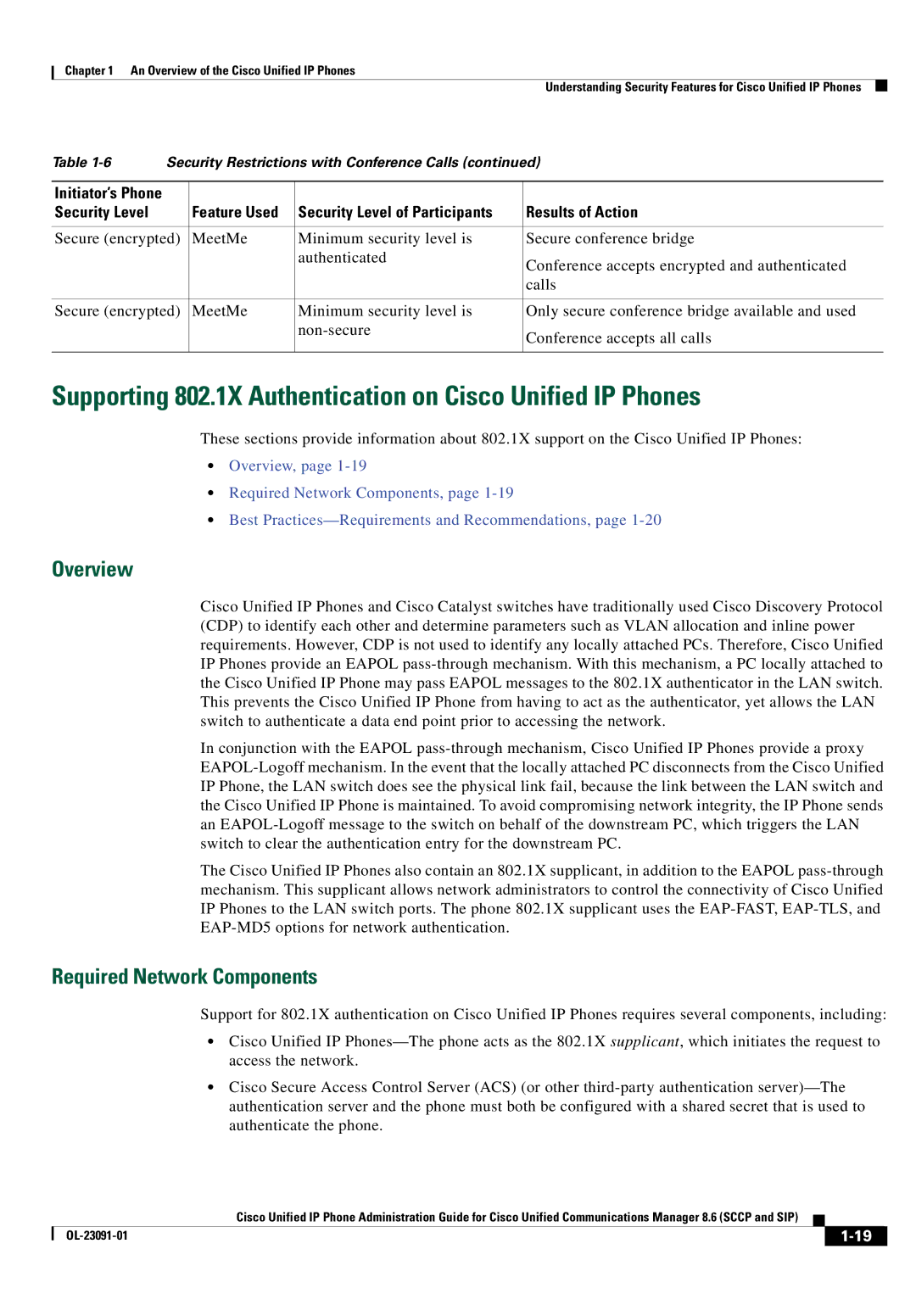
Security Restrictions with Conference Calls
Supporting 802.1X Authentication on Cisco Unified IP Phones
Overview
Required Network Components
Best Practices-Requirements and Recommendations
Security Restrictions
Reducing Power Consumption on the Phones
OL-23091-01
Purpose For More Information
Communications Manager Administration
See Cisco Communications Manager
Guide
Checklist for Installing the Cisco Unified IP Phones
Installing Cisco Unified IP Phones
Administration Guide
Task Purpose For More Information
See Installing the Cisco Unified IP Phones
See Providing Power to the Cisco Unified IP
See Feature Key Capacity Increase for Cisco
Phones,
Network Configuration IPv4 Configuration and configure
See Configuring Startup Network Settings
Choose Settings Network Configuration IPv4
Choosing Settings Network Configuration
Network Configuration IPv6 Configuration
Network Configuration IPv6 Configuration and configure
See Cisco Unified IP Phone 7962G, 7942G
7961G, 7961G-GE, 7941G, and 7941G-GE
A P T E R
Related Topic
Providing Power to the Cisco Unified IP Phones
Power Guidelines
Power Outage
Power Type Guidelines
Obtaining Additional Information about Power
Understanding Phone Configuration Files
Understanding Phone Configuration Files
Security Guide, Configuring the Cisco CTL Client
Resolving Startup Problems,
Understanding the Phone Startup Process
Purpose Related Topics
Adding Phones with Auto-Registration,
Security Guide, Security by Default
Adding Phones with Auto-Registration
Requires
Method Address?
Adding Phones with Auto-Registration and Taps
Adding Phones with BAT
Procedure
Using Cisco Unified IP Phones with Different Protocols
See Configuring Startup Network Settings,
Converting a New Phone from Sccp to SIP
Deploying a Phone in an Sccp and SIP Environment
Converting an In-Use Phone from One Protocol to the Other
OL-23091-01
Before You Begin
Setting Up the Cisco Unified IP Phones
Network and Access Ports, Handset, Speakerphone, Headset,
Cisco Unified Communications Manager Configuration
Understanding the Cisco Unified IP Phone Components
Network Requirements
Handset
Network and Access Ports
Speakerphone
Connecting a Headset
Headset
Audio Quality
Enabling a Wireless Headset on the Cisco Unified IP Phones
Using External Devices
Disabling a Headset
Before You Begin
Installing the Cisco Unified IP Phones
See Adding Phones to the Cisco Unified Communications
Adapter port
Connect a straight-through Ethernet cable from
See Network and Access Ports, page 3-3for guidelines
Cisco Unified IP Phone 7962G and 7942G Cable Connections
Attaching a Cisco Unified IP Phone Expansion Module
Feature Key Capacity Increase for Cisco Unified IP Phones
Click Apply Config
Apply Configuration Information dialog appears
Adjusting the Placement of the Cisco Unified IP Phone
Adjusting Cisco Unified IP Phone Placement on the Desktop
Configuring Softkey Templates,
Mounting the Phone to the Wall
Securing the Phone with a Cable Lock
Parts Used in Wall Mounting the Cisco Unified IP Phone
Verifying the Phone Startup Process
Configuring Startup Network Settings
Configuring Security on the Cisco Unified IP Phones
From the phone, choose Settings Security Configuration
Related Topic
Configuration Menus on the Cisco Unified IP Phones
Configuring Settings on the Cisco Unified IP Phones
Unlocking and Locking Options
Displaying a Configuration Menu
Editing Values
IPv4 Network Settings
Overview of Options Configurable from a Phone
Category Description
PC Vlan
IPv6 Network Settings
Network Configuration Menu
Option Description To Change
Option Description To Change
System Enterprise Phone
Configuration
Unified CM, the data
Cannot be changed on
VPN
OL-23091-01
Option Description To Change
Cisco Unified Communications Manager Security
Guide. For information about unlocking CTL
ITL files, see Unlocking the CTL and ITL Files
From the new Tftp Server
Configuration menu. a new
4describes the IPv6 configuration menu options
Option Description To Change
Unified Communications Manager Security Guide. For
Yes
Information about unlocking the CTL file, see Unlocking
CTL and ITL Files,
Understanding DHCPv6 and Autoconfiguration
Device Configuration Menu
Configuration in the Cisco Unified Communications Manager
Unified CM Configuration Menu
State
Designation Description
SIP General Configuration Menu
SIP Configuration Menu for SIP Phones Only
Device Settings SIP Profile
See Cisco Unified Communications Manager Security Guide
Displaying a Configuration Menu, Device Configuration Menu,
Line Settings Menu for SIP Phones
Call Preferences Menu for SIP Phones
Http Configuration Menu
Routing Directory Number
Device Phone Add a New Speed Dial
Is activated
Locale Configuration Menu
NTP Configuration Menu for SIP Phones
NTP Configuration Menu for SIP Phones
Reference
Device Phone Phone Configuration
UI Configuration Menu
Phone Configuration
Parameters
Gets used see Media Configuration Menu
User Preferences Audio Preferences Wideband Handset
User Preferences Audio Preferences Wideband Headset
Media Configuration Menu
That the remote party receives. The remote party
Is the party who is on a call with the party whose
See also Recording Tone
User
Phone Configuration to set this value
Preferences Audio Preferences
Wideband Handset
Ethernet Configuration Menu
For more information, see the Cisco Unified
Communications Manager System Guide, Cisco
Web Page Access,
Security Configuration Menu
Displaying a Configuration Menu, Network Configuration Menu,
QoS Configuration Menu
Call Statistics Screen, Streaming Statistics,
Network Configuration Menu
Option Description To Change
Protocol. Settings include Enabled-default Disabled
Settings Common Device Configuration
See Table
MIC
Security Configuration Menu
Proxy Function in Cisco Unified Communications
LSC
CTL File Submenu
System Administration Guide, Security
Cisco Unified Communications Operating
Cisco Unified Communications Manager
ITL File Submenu
ITL file, see Security by Default
Unlocking the CTL and ITL Files
Cisco Unified Communications
Security Guide
Unified Communications Manager
Cisco Unified
Communications Operating
Configuring the Cisco CTL Client in Cisco Unified
System Administrator Guide
Trust List Menu
Capf server used by the phone. Also displays
802.1X Authentication and Status
Authentication
Trusted Srst router that is available to
802.1X Authentication Device
Choose Settings Security Configuration
802.1X Authentication EAP-MD5
EAP-MD5
Connecting to VPN
VPN Configuration
25describes the 802.1X Authentication Real-Time Status
When the power is lost
VPN Configuration Settings
Choose Settings Security
Configuration VPN Configuration
Concentrator 3, as desired
Concentrator 1, Concentrator 2, or
AES128-SHA
AES256-SHA DES-CBC3-SHA
Configuring Features, Templates, Services, and Users
Administration Guide, Cisco Unified IP
Feature Description Configuration Reference
Features and Services Guide, Barge
Choose System Service Parameter and select
Communications Manager Features
Administration Guide, SIP Profile
Services Guide, Call Pickup
Amwi
Configuration System Enterprise Phone
Services Guide, External Call Transfer
Restrictions
Communications Manager Feature
Services Guide, Presence
Features and Services Guide, Call Back
Features and Services Guide, Call Display
Communications Manager System Guide
Forward Maximum Hop Count service parameter
Services Guide, Monitoring and Recording
During a call when it is being recorded
Identification enabled
Incoming call information on the phone screen
Unified Communications Manager Features
Communications Features and Services
Services Guide, Cisco IP Manager
CMC
Guide, CTI Route Point Configuration
Services Guide, Custom Phone Rings
System Guide, Conference Bridges
Phone Services Configuration
Services Guide, Do Not Disturb
Services
System Guide, Cisco Unified IP Phone
Unified Communications Manager Features
Manager Features and Services Guide, Hold
Feature, see Cisco Unified Communications
Administration Guide, Hunt List
Administration Guide, CTI Route Point
Feature and Services Guide, Intercom
See Cisco Unified Communications
Manager System Guide, Cisco Unified IP
Features and Services Guide, Malicious
Administration Guide, Message Waiting
Cisco Communications Manager System
Services Guide, Music On Hold
Mlpp
Plar
Administration Guide, Phone Button
Features and Services Guide Barge
Administration Guide, Modifying Phone
Features and Services Guide, Quality
Features and Services Guide, Custom
Phone Rings
Creating Custom Phone Rings,
Manager Administration System
Administration Device Phone
Administration Guide, Conference Bridge
Unified Communications Manager
Mobility and Cisco Unified Mobility
Features and Services Guide, Cisco Unified
Advantage and Cisco Unified Mobile
Communicator Integration
On the call. The user might hear a monitoring
Administration Guide, Device Pool
Settings Common Phone Profile,
Configuration Layout pane and select
Administration Guide, Time Period
Manager Administration Guide
Configuring Product Specific Configuration Parameters
Cisco VT Advantage Administration
Administration Guide, Cisco Voice-Mail
Device Device Settings
Configuration Window Path Parameters
Common Phone Profile
Device Phone Product
Configuring Corporate and Personal Directories
Configuring Corporate Directories
Configuring Personal Directory
Cisco Unified IP Phone 7962G
Modifying Phone Button Templates
Cisco Unified IP Phone 7942G
Cisco Unified IP Phone 7961G /7961G-GE
Find and List IP Phone Services window displays
Choose Device Device Settings Phone Services
Configuring Softkey Templates
Adding Users to Cisco Unified Communications Manager
Setting Up Services
Giving Users Access to the User Options Web Pages
Managing the User Options Web Pages
Click Add Selected
Click Device Association
Specifying Options that Appear on the User Options Web Pages
Enabling EnergyWise on the Cisco Unified IP Phone
Field Description
Field Description
Setting up UCR
Configuring UCR 2008 in Phone
Choose Device Phone
Configuring UCR 2008 in Enterprise Phone Configuration
Configuring UCR 2008 in Common Phone Profile
Set the Https Service parameter to https only
Choose Device Device Settings Common Phone Profile
OL-23091-01
Customizing the Cisco Unified IP Phones
Customizing and Modifying Configuration Files
Ringlist.xml File Format Requirements
Creating Custom Phone Rings
Configuring a Custom Phone Ring
Creating Custom Background Images
PCM File Requirements for Custom Ring Types
List.xml Example
List.xml File Format Requirements
PNG File Requirements for Custom Background Images
Configuring a Custom Background Image
Configuring Wideband Codec
Monitoring the Cisco Unified IP Phones Remotely
Accessing the Web Page for a Phone
Click Update
Disabling and Enabling Web Page Access
Device Information
Phone. -1describes these items
UDI
Templates, Services, and Users
Network Configuration
Description
Vlan
Cannot be changed on the phone
PC Vlan
Network Statistics
OL-23091-01
Streaming Statistics
Device Logs
Stream 1 and Stream
Stream 4, or the Stream 5 hyperlink
MOS LQK
Information, see Monitoring the Voice Quality of Calls,
Cisco Unified IP Phone uses
Uses
Voice Quality Metrics
Related Topics
A P T E R
See Using Cisco Unified IP Phones with Different
For your phone, see Using the Certificate Authority
Model Information Screen
Status Menu
Status Messages Screen
Select Status Messages
Message Description Possible Explanation and Action
Configuration 802.1X Authentication option on
Address. See Network Configuration Menu
Authentication and Status,
Unified Communications Manager Security Guide
If you are using DHCP, check the Dhcp server
Network Configuration Menu, page 4-5section
Menu, page 4-5for details
Configuration Menu, page 4-34for details
See Firmware Versions Screen, page 8-12to verify
Device Phone
Configuration Menu, page 4-5for details
Provided a DNS server. Check the Dhcp server
See Cisco Unified Communications Manager Security
Message Description Possible Explanation and Action
Select Status Network Statistics
Network Statistics Screen
Port
IPv4
IPv6
Firmware Versions Screen
Select Firmware Versions
To exit the Firmware Version screen, press the Exit softkey
Expansion Module Status Screen
Select Expansion Module
To exit the Expansion Module screen, press the Exit softkey
Press the Settings button Select Status
Call Statistics Screen
Select Call Statistics
That the Cisco Unified IP Phone uses
Preceding 8-second interval of the voice stream. For more
Using Test Tone
Place a call
Status Menu
Resolving Startup Problems
Troubleshooting and Maintenance
Identifying Error Messages, Checking Network Connectivity,
Verifying Tftp Server Settings
Identifying Error Messages
Checking Network Connectivity
Verifying IP Addressing and Routing
Verifying Cisco Unified Communications Manager Settings
Verifying DNS Settings
Cisco CallManager and Tftp Services Are Not Running
Choose Tools Control Center Feature Services
Be removed from the phone and deleted if necessary
Creating a New Configuration File
Cisco Unified IP Phone Resets Unexpectedly
Symptom Cisco Unified IP Phone Unable to Obtain IP Address
Verifying the Physical Connection
Checking Static IP Address Settings
Verifying Dhcp Settings
Verifying the Voice Vlan Configuration
Verifying that the Phones Have Not Been Intentionally Reset
Checking Power Connection
Eliminating DNS or Other Connectivity Errors
Problem Possible Cause
Troubleshooting Cisco Unified IP Phone Security
General Troubleshooting Tips
Explanation
Unlocking and Locking Options, page 4-2for details
To resolve this problem, re-enable the port from the switch
Summary Explanation
Halfduxcollisionexceedthreshold
OL-23091-01
Performing a Basic Reset
Resetting or Restoring the Cisco Unified IP Phones
Problem Solution
Press the Services, Settings, or Directories
Performing a Factory Reset
Options see Unlocking and Locking Options
Locking Options, page 4-2. Then press
Monitoring the Voice Quality of Calls
Using the Quality Report Tool
Using Voice Quality Metrics
Where to Go for More Troubleshooting Information
Troubleshooting Tips
Metric Change Condition
Cleaning the Cisco Unified IP Phone
Providing Information to Users Via a Website
Giving Users Access to the User Options Web Pages
How Users Get Copies of Cisco Unified IP Phone Manuals
How Users Subscribe to Services and Configure Phone Features
How Users Access a Voice Messaging System
Installing the Synchronizer
How Users Configure Personal Directory Entries
Ready to Install window displays
Configuring the Synchronizer
Programs Cisco Systems TabSync
OL-23091-01
Features
Feature Support by Protocol for Cisco Unified IP Phone
Manager
MWI
FAC
Tool
Cisco Unified IP Phone Service Application
SDK Compliance Supported
Development Notes
Services Guide
Cisco Unified Communications Manager Features
Cisco Unified Communications Manager Assistant
Cisco Unified IP Phone Expansion Module
Adding Language Overlays to Phone Buttons
Supporting International Users
Support for International Call Logging
Specification Value or Range
Physical and Operating Environment Specifications
100-240 VAC, 50-60 Hz, 0.5 A-when using the AC adapter
Cisco Unified IP Phone 7962G and 7942G
Network and Access Port Pinouts
Cable Specifications
Network Port Connector
Pin Number
Pin Number Function
Access Port Connector
OL-23091-01
Example User Information for these Procedures
Basic Phone Administration Steps
Adding a User From an External Ldap Directory
Proceed to Configuring the Phone, page E-3
Choose System Ldap Ldap Directory
Click Perform Full Sync Now
Proceed to the section Configuring the Phone, page E-3
Configuring the Phone
Example johndoe
Example doe
Procedure
OL-23091-01
Click Device Associations
Choose User Management End User
Performing Final End User Configuration Steps
IN-1
PNG file
Capf Certificate Authority Proxy Function
IN-2
Client matter codes
Conference joining Configurable call forward display
PCM file requirements
IN-3
IN-4
Fast dial B-3
Hold status Ihold Hold reversion
Hunt groups
IN-5
IN-6
Immediate Divert enhanced feature
IN-7
Host Name IPv4 Alternate Tftp Bootp Server Default Router
CDP Cppdp Dhcp Http Rtcp RTP Sccp SIP TCP Tftp TLS UDP
Lldp
IN-8
IN-9
Dscp For Configuration
IN-10
Description Establishing Identifying Restrictions
IN-11
Trivial File Transfer Protocol
Mobile connect TLS Mobile voice access Transfer
Secure and nonsecure indication tone
DNS
Accessing Debug Display
Disabling access to Ethernet Information
IN-13
IN-14
Stream
IN-15