Wireless LAN Mobility System
United States Government Legend
3Com Corporation 350 Campus Drive Marlborough, MA USA
Contents
Managing User Passwords
Configuring AAA for Administrative and Local Access
Configuring and Managing Ports and Vlans
Configuring and Managing IP Interfaces and Services
Displaying Password Information
108
Configuring and Managing Mobility Domain Roaming
Configuring Snmp
Configuring Network Domains
Configuring MAP Access Points
MAP Overview Country of Operation 179
Configuring RF Load Balancing for Maps
RF Load Balancing Overview 267
268
Configuring User Encryption
Configuring Wlan Mesh Services
Configuring RF AUTO-TUNING
Configuring Maps to be Aeroscout Listeners
Configuring Quality of Service
Configuring and Managing Spanning Tree Protocol
Configuring and Managing Igmp Snooping
Configuring and Managing Security Acls
380
416
Why Use Keys and Certificates? 413
Managing Keys and Certificates
414
479
Configuring AAA for Network Users
475 Using an ACL Other Than portalacl
460
514
494 Clearing a Security ACL from a User or Group 495
496
503
Managing 802.1X on the WX Switch
Configuring Communication with Radius
Managing Sessions
Configuring Soda Endpoint Security for a WX Switch
Rogue Detection and Countermeasures
Troubleshooting a WX Switch
631 Using the Trace Command
Managing System Files
Enabling and Logging Into WEB View
Obtaining Support for Your 3COM Products
Glossary Index Command Index
Supported Radius Attributes
Traffic Ports Used by MSS
Conventions
List conventions that are used throughout this guide
Icon Description
This manual uses the following text and syntax conventions
Including new features and bug fixes
3WXM for advanced configuration and management
Documentation
Pddtechpubscomments@3com.com
Comments
About this Guide
Network operations
To configure and manage the switch and its attached MAPs
Overwrite a parameter with another set command. Use display
Overview
Alphanumeric characters, except for tabs and spaces, and is
Text Entry
Conventions
Case-insensitive
IP Address and Mask Notation
MAC Address Notation
User Globs
User Globs
User Glob Users Designated
Vlan Globs
MAC Address Globs
WX1200# display port poe 1,2,4,6
WX1200# set port enable
WX1200# reset port
Matching Order for Globs
CLI Keyboard Shortcuts
Command-Line
Editing
Operating systems
Wildcard Characters
Using CLI Help
Commands that begin with those characters. For example
At your access level, type the following command
WX1200# display i?
WX1200# display ip ?
WX1200# display ip telnet
Set ap apnumber auto security
Understanding Command Descriptions
Set ap name command has the following complete syntax
Set ap
„ Web Quick Start WXR100, WX1200, and WX2200
Switches
„ CLI quickstart command
Methods
WX Setup Methods
Gets its Configuration
How a WX Switch
WX2200 Only
Quick Start
Accessing the Web To access the Web Quick Start
WX Setup Methods
Web Quick Start WXR100, WX1200 and WX2200 Only
CLI quickstart
Set enablepass command
WX Setup Methods
Single-Switch Deployment
Verify the configuration changes
Remote WX
„ On Linux systems, change directories to
Select File Switch Network Plan
To open the network plan
Start 3WXM by doing one of the following
3Com Mobility System Software MSS supports authentication
Here is an overview of configuration topics
Operation
Configuring AAA for Administrative and Local Access
Building
About
Administrative
Access
Before You Start
Console
Configuration via
Administrator
First-Time
WX1200# save config
Password
Setting the WX Enable Password for the First Time
WX1200# set enablepass
3WXM Enable Password
WX1200# set authentication console * local
WX1200# set authentication console * none
Configuring AAA for Administrative and Local Access
Configuring
Configuring AAA for Administrative and Local Access
Saving
Configday. To do this, type the following command
Configuration, all changes are lost
Displaying the AAA
Administrative AAA
Scenarios
Radius
Administrative AAA Configuration Scenarios
Success configuration saved
Restrictions apply to user passwords
Passwords, and how to display password information
Clear user username
Configuring Passwords
Set user username password encrypted password
WX# set user Jose password spRin9
Set authentication max-attempts number
Setting the Maximum Number of Login Attempts
Set authentication password-restrict enable disable
WX# set authentication password-restrict enable
Password Length
Configuring Password Expiration Time
Clear user username lockout
WX# clear user Nin lockout
WX# display aaa
Managing Ports
Configuring
Vlan
Port Type Parameter MAP Access Wired Authentication Network
Maximum MAPs Supported Per Switch
Setting a Port for a Directly Connected MAP
Configuring a MAP Connection
Valid dap-num Values
Setting a Port for a Wired Authentication User
Switch Model Valid Range
WX1200# set port type wired-auth 7 success change accepted
Clearing a Port
Name Setting a Port Name
Clearing a Distributed MAP
Removing a Port Name
Set port media-type port-listrj45
Clear port media-type port-list
Display port media-type port-list
Parameters
10/100 Ports-Autonegotiation and Port Speed
Set port speed port-list10 100 auto
Disabling or Reenabling Power over Ethernet
Gigabit Ports Autonegotiation and Flow Control
Disabling or Reenabling a Port
Resetting a Port
To reset a port, use the following command
Displaying Port Configuration and Status
To display port statistics, use the following command
Displaying PoE State
Displaying Port Statistics
Clear port counters
Clearing Statistics Counters
Counters begin incrementing again, starting from
Monitoring Port Statistics
WX1200# monitor port counters
Use the keys listed in to control the monitor display
Key Controls for Monitor Port Counters Display
Key Effect on monitor display
Load Sharing
Configuring a Port Group
To configure a port group, use the following command
Groups can participate in a port group
Clear port-group name name
To remove a port group, use the following command
WX1200# display vlan config
Removing a Port Group
WX1200# display port-group name server2
Displaying Port Group Information
Interoperating with Cisco Systems EtherChannel
Display port-group name group-name
Users and VLANs
VLANs, IP Subnets, and IP Addressing
Roaming and VLANs
Vlan Names
Traffic Forwarding
802.1Q Tagging
Tunnel Affinity
To create a VLAN, use the following command
Creating a Vlan
Set vlan vlan-numname name
WX1200# set vlan 2 name red
To add a port to a VLAN, use the following command
Adding Ports to a Vlan
You can specify a tag value from 1 through
Removing an Entire Vlan or a Vlan Port
To completely remove Vlan ecru, type the following command
To change the tunneling affinity, use the following command
Specify a value from 1 through 10. The default is
Display security l2-restrict vlan vlan-idall
Clear security l2-restrict counters vlan vlan-idall
Display vlan config vlan-id
WX1200# display vlan config burgundy
Security l2-restrict
Forwarding
Database
Port associated with the MAC address
Displaying
Information Displaying the Size of the Forwarding Database
Displaying Forwarding Database Entries
WX1200# clear fdb dynamic success change accepted
Adding an Entry to the Forwarding Database
Removing Entries from the Forwarding Database
WX1200# display fdb
Changing the Aging Timeout Period
Displaying the Aging Timeout Period
Configuration change. Type the following commands
Port and Vlan
Scenario
WX1200# set port type ap 2-4 model ap2750 poe enable
Port status
WX1200# display port poe
Display Port status
Save the configuration. Type the following command
Set port type wired-auth 5,6
WX1200# set vlan default port
MTU Support
Adding an IP Interface
Configuring Managing IP Interfaces
Statically Configuring an IP Interface
To add an IP interface to a VLAN, use the following command
Configuring and Managing IP Interfaces
Set interface vlan-idip dhcp-client enable disable
WX1200# set interface corpvlan ip dhcp-client enable
WX1200# display interface
To remove an IP interface, use the following command
Disabling or Reenabling an IP Interface
Displaying IP
Configuring the System IP Address
To display the system IP address, use the following command
To clear the system IP address, use the following command
Configuring and Managing IP Routes
WX1200# display ip route
Display ip route destination
WX1200# display ip route
To remove a static route, use the following command
Managing SSH
Managing Management Services
Login Timeouts
Set ip ssh server enable disable
You can verify the key using the following command
For example
Adding an SSH User
Managing SSH Server Sessions
Changing the SSH Service Port Number
Use the following commands to manage SSH server sessions
These commands display and clear SSH server sessions
Adding a Telnet User
Telnet Login Timers
Set ip telnet server enable disable
Enabling Telnet
Displaying Telnet Status
Changing the Telnet Service Port Number
Resetting the Telnet Service Port Number to Its Default
Use the following commands to manage Telnet server sessions
Displaying Https Information
Managing Https Enabling Https
Set system idle-timeout seconds
Clear system idle-timeout
Sessions
To specify a Motd banner, use the following command
Following command sets the Motd banner on the WX
Prompting the User to Acknowledge the Motd Banner
Removing a DNS Server
To add a DNS server, use the following command
To remove a DNS server, use the following command
Adding a DNS Server
Specify a domain name of up to 64 alphanumeric characters
Adding the Default Domain Name
To add the default domain name, use the following command
Removing the Default Domain Name
Display ip alias name
Here is an example
Set ip alias name ip-addr
Clear ip alias name
Managing Time
Parameters
Daylight savings time or similar summertime period
Clearing the Time Zone
To display the time zone, use the following command
To clear the time zone, use the following command
Displaying the Time Zone
Clearing the Summertime Period
To display the summertime period, use the following command
To clear the summertime period, use the following command
Displaying the Summertime Period
Display timedate
Statically Configuring System Time Date
Set timedate date mmm dd yyyy time hhmmss
WX1200# set timedate date feb 29 2004 time 235800
To remove an NTP server, use the following command
NTP client is disabled by default
Resetting the Update Interval to Default
To display NTP information, use the following command
Displaying NTP Information
Entries
Managing the ARP
IP address to the ARP table
Permanent entries to the ARP table
Set arp permanent static dynamic ip-addrmac-addr
Set arp agingtime seconds
WX1200# set arp agingtime
Remote Device
Pinging Another
Device
Logging In to a
Tracing a Route
WX1200# traceroute server1
Time and date parameters
IP Interfaces
WX1200# set ip dns enable
WX1200# Set ip Dns Server
Ip dns
Sun Feb 29 2004, 235902 PST
Configuring and Managing IP Interfaces and Services
All Snmp versions are disabled by default
„ SNMPv3-SNMPv3 adds authentication and encryption options
USM users, with individually configurable access levels
Authentication options, and encryption options
Set system location string set system contact string
To enable an Snmp protocol, use the following command
Configuring Community Strings SNMPv1 SNMPv2c Only
Set snmp protocol v1 v2c usm all enable disable
Clear snmp usm usm-username
To create a USM user for SNMPv3, use the following command
To clear a USM user, use the following command
Clear snmp community name comm-string
Configuring Snmp
Command Examples
To clear a notification profile, use the following command
WX1200# set snmp security encrypted success change accepted
Clear snmp notify profile profile-name
ClientRoamingTraps-Generated when a client roams
Configuring Snmp
Command Examples
Configuring Snmp
To clear a notification target, use the following command
Security unsecured authenticated encrypted
Clear snmp notify target target-num
Command Examples
Information
To enable the MSS Snmp service, use the following command
Following command enables the Snmp service
To display USM settings, use the following command
Display snmp counters
To display notification profiles, use the following command
Display snmp notify profile
Display snmp notify target
Mobility Domain Roaming
Mobility Domain
Configuring a
Configuring the System IP Address on
Set mobility-domain mode seed domain-name mob-domain-name
Set mobility-domain member ip-addr
Set mobility-domain mode member seed-ip ip-addr
On the other member switches in the Mobility Domain
On the primary seed
On the secondary seed
Domain Status display mobility-domain command. For example
Displaying Mobility Domain Configuration
Switch
WX-WX Security
Domain
Monitoring
VLANs and Tunnels
A Mobility
WX1200# display tunnel
WX1200# display roaming vlan
Understanding Sessions Roaming Users
Vlan
WX1200 display sessions network verbose
Mobility-domain
WX1200# set mobility-domain member seed-ip
Vlan-wep 192.168.12.7 192.168.15.5
Domains
Network Domain
How a user connects to a remote Vlan in a Network Domain
Configuring a WX Switch’s affinity for a Network Domain seed
Network Domain
Set network-domain mode seed domain-name net-domain-name
Set network-domain peer ip-addr
Set network-domain mode member seed-ip ip-addraffinity num
Set network-domain mode member seed-ip ip-addraffinity num
WX4400# display network-domain
Clear network-domain seed-ip ip-addr
WX Switch following command
Clear network-domain mode seed member
Clear network-domain
Configuring Network Domains
WX1200# display network-domain
Upseed Upmember 30.30.30.1
Combinations of multiple connections
Through radio signals
„ Two direct connections to a single WX or two WX switches
MAP Overview
Example 3Com Network
MAP Overview
Distributed MAP Network Requirements
Distributed MAPs and STP
Distributed MAPs and Dhcp Option
No configuration is required on the WX
MAP Parameters
Resiliency and Dual-Homing Options for MAPs
Dual-Homed Direct Connections to a Single WX
Dual-Homed Configuration Examples
Dual-Homed Direct and Distributed Connections to WX Switches
Network Backbone
WX switch
How a Distributed MAP Obtains an IP Address through Dhcp
Establishing Connectivity on the Network
Static IP Address Configuration for Distributed MAPs
DNS server replies with the system IP address of a WX switch
Configuring MAP Access Points
MAP Overview
Configuring MAP Access Points
MAP Boot Examples
MAP Booting over Layer 2 Network
MAP Overview
MAP sends Dhcp Discover message from the MAP’s port
MAP Booting over Layer 3 Network
MAP sends a unicast Find WX message to WX1
Dual-Homed MAP Booting
MAP sends a Dhcp Discover message from the MAP’s port
MAP Booting with a Static IP Address
Auth-dot1x Enable
Defaults for Service Profile Parameters
Cipher-tkip Enable
Auth-psk Disable
Beacon Enable
Cipher-ccmp Disable
Soda Disable
No-broadcast Disable
Proxy-arp Disable
Set radio-profile auth-psk command
12.0,24.0
User-idle-timeout 180
Web-portal-session
Timeout
Web-portal
Web-portal-form
Model Address Allocation
Public and Private SSIDs
Each radio can support the following types of SSIDs
MAC Address Allocations on MAPs
AP8250
Radios AP2750
SSIDs
AP7250
Beacon-interval 100
Defaults for Radio Profile Parameters
Not configured
Encryption
Max-rx-lifetime 2000
Parameter Default Value Frag-threshold 2346
Rfid-mode Disable
Service-profile
Radio-Specific Parameters
RF Auto-Tuning
Default Radio Profile
Lists the defaults for these parameters
ANT-5360-OUT
Parameter Default Value Description Antennatype
Max-power
Mode Disable
To specify the country, use the following command
You specify the country of operation
Set system countrycode code
Country Codes
Country Codes
Country Codes
CountryCode
How an Unconfigured MAP Finds a WX To Configure It
WX switch can have one Auto-AP profile
Configured MAPs Have Precedence Over Unconfigured MAPs
Example WX1200 MAP Capacities and Loads
WX1200 a WX1200 B
WX1200# set ap auto success change accepted
Configuring an Auto-AP Profile
Configurable Profile Parameters for Distributed MAPs
WX# set ap auto mode enable success change accepted
MAP Parameters
Radio Parameters
Set ap auto persistent apnumber all
WX# display ap status auto
Configure the MAP using the following command
Auto-AP profile is not used to configure the MAP. Instead,
MAP configuration persistent across switch restarts
Configuring a MAP
Configuring Static IP Addresses on Distributed MAPs
Success change accepted
Changing Bias
Clearing a MAP from the Configuration
To clear a MAP, use the following command
Changing MAP Names
WX# set ap 1 bias low success change accepted
Disabling or Reenabling Automatic Firmware Upgrades
Set ap apnumber upgrade-firmware enable disable
Forcing a MAP To Download its Operational Image from the WX
Set ap apnumber blink enable disable
Enabling LED Blink Mode
Encryption Options
Encryption Key Fingerprint
Verifying a MAP Fingerprint on a WX Switch
MAP Can Establish
WX# display ap status
Setting the MAP Security Requirement on a WX
Set ap security require optional none
WX# set ap security require
An Ssid can be up to 32 alphanumeric characters long
Creating a Service Profile
Set service-profile name ssid-name ssid-name
Fingerprint Log Message
Disabling or Reenabling Beaconing of an Ssid
Removing a Service Profile
Changing a Service Profile Setting
Disabling or Reenabling Encryption for an Ssid
Lists the rate settings and their defaults
SSIDs are beaconed by default
Changing the Fallthru Authentication Type
To change the fallthru method, use the following command
Beacon-rate
Transmit Rates
11b-1.0,2.0
11g-1.0,2.0,5.5,11.0
Transmit Rates
Enforcing the Data Rates
WX# set radio-profile rp1 rate-enforcement mode enable
WX# set radio-profile rp1 service-profile sp1
Disabling Idle-Client Probing
Changing the User Idle Timeout
Threshold can be a value from 1 through 15. The default is
Changing the Short Retry Threshold
Changing the Long Retry Threshold
Set service-profile name long-retry threshold
To create a radio profile, use the following command
Creating a New Profile
Changing Radio Parameters
Set radio-profile name dtim-interval interval
To change the Dtim interval, use the following command
Set radio-profile name max-rx-lifetime time
To change the RTS threshold, use the following command
Set radio-profile name rts-threshold threshold
Set radio-profile name frag-threshold threshold
Set radio-profile name max-tx-lifetime time
Resetting a Radio Profile Parameter to its Default Value
To remove a radio profile, use the following command
Removing a Radio Profile
Configuring the Channel and Transmit Power
Model Type Gain dBi Description
Configuring the External Antenna Model and Location
Beamwidth Model Type Horizontal Vertical
Specifying the External Antenna Model
MP-341, MP-352, MP-262 External Antenna Models
MP-620 External Antenna Models
Assigning a Radio Profile and Enabling Radios
Set radio-profile name service-profile name
Specifying the External Antenna Location
Profiles
Reenabling Radios
Disabling or
WX1200# clear ap 3 radio
To restart a MAP, use the following command
Reset ap apnumber
Clear ap apnumber radio 1 2 all
Configuring MAP Access Points
Configuring a Vlan Profile
Enabling Local Switching on a MAP
Set ap apnumber local-switching mode enable disable
Clearing the Vlan Profile from a MAP
Set ap apnumber local-switching vlan-profile profile-name
Clear ap ap-numberlocal-switching vlan-profile
Applying a Vlan Profile to a MAP
WX# clear vlan-profile locals vlan red
Removing a Vlan Profile from the WX Switch
To remove Vlan profile locals, type the following command
Clear vlan-profile profile-namevlan vlan-name
Displaying MAP Information
Displaying MAP Configuration Information
Display ap config apnumber radio 1
WX1200# display ap config
Displaying Connection Information for Distributed MAPs
Display ap global apnumber serial-id serial-ID
WX4400# display ap global
Displaying a List Distributed MAPs That Are Not Configured
Connection
Information for
WX# display service-profile sp1
Display service-profile name ?
Display ap status terse apnumber all radio 1
WX# display radio-profile default
Displaying MAP
Display radio-profile name ?
Displaying Static IP
Following command displays the status of a Distributed MAP
WX# display ap counters
Display ap counters apnumber radio 1
Following command displays ARP entries for AP
Displaying Vlan Profile Information
Displaying the ARP Table for a MAP
Displaying Forwarding Database For a MAP
Following command displays FDB entries for AP
Display ap acl hits ap-number
WX# display ap acl hits
Display ap acl map ap-number
WX# display ap acl map
Configuring RF Load
Configuring RF Load Balancing
Set load-balancing mode enable disable
Disabling or Re-Enabling RF Load Balancing
Set band-preference none 11bg 11a
Clear ap apnumber radio radio-numload-balancing group
Set load-balancing strictness low med high max
WX# display load-balancing group ap 2 radio
Displaying RF Load Balancing Information
Exempting an Ssid From RF Load Balancing
Radios in the same load-balancing group as ap2/radio1
Configuring RF Load Balancing for Maps
Services
Mesh Services
Configuring Wlan
Use the following command to specify the pre-shared key
Set ap num boot-configuration mesh mode enable disable
Set ap num boot-configuration mesh ssid mesh-ssid
Mesh Services following commands
Set ap num radio num link-calibration mode enable disable
Following illustration
Wireless Bridging
AP, m = mesh AP = mesh portal
Rfid Reports Inactive Antenna Link Calibration Enabled
Displaying Wlan
WX# display ap status terse Total number of entries
Bssid1 000b0efdfdcd, ssid mesh-ssid mesh
802.11i standard
Encryption settings are configured in the service profile
Then authorized to join a Vlan
„ WPA2 Robust Security Network
Wireless Encryption Defaults
Configuration Required
Encryption Type Client Support Default State MSS
Default Encryption
Configuring User Encryption
WPA Encryption with Tkip Only
WPA Encryption with Tkip and WEP
Configuring WPA
Configuring User Encryption
Configuring WPA
Encryption Support for WPA and Non-WPA Clients
Lists the encryption support for WPA and non-WPA clients
Creating a Service Profile for WPA
Enabling WPA
Specifying the WPA Cipher Suites
Set service-profile name auth-psk enable disable
Changing the Tkip Countermeasures Timer Value
Enabling PSK Authentication
Set service-profile name tkip-mc-time wait-time
Set service-profile name auth-dot1x enable disable
Set service-profile name psk-raw hex
Displaying WPA Settings
WPA settings appear at the bottom of the output
WX1200# display service-profile sp1
Set radio-profile name service-profile name
Set service-profile name rsn-ie enable disable
WX1200# set service-profile rsn success change accepted
Ccmp
RSN settings appear at the bottom of the output
Assigning the Service Profile to Radios Enabling the Radios
Configuring WEP
Encryption for Dynamic and Static WEP
To set the value of a WEP key, use the following command
Traffic, use the following commands
Set service-profile name wep key-index num key value
Tkip
Encryption Configuration Scenarios
Encryption Configuration Scenarios
WX1200# set service-profile wpa-wep success change accepted
305
Clients
WX1200# display aaa Default Values
WX1200# display service-profile sp1
Save the configuration. Type the following command
Configuring User Encryption
RF Auto-Tuning
RF Auto-Tuning can perform the following tasks
Power setting if needed
Disabled for power configuration
How Channels Are Selected
Channel Tuning
Power Tuning
Defaults for RF Auto-Tuning Parameters
Tuning the Transmit Data Rate
Defaults for RF Auto-Tuning Parameters
RF Auto-Tuning
Settings
Changing
Set radio-profile name auto-tune channel-interval seconds
Changing the Channel Tuning Interval
Enabling Power Tuning
Changing the Channel Holddown Interval
Channel or set ap dap radio tx-power command for each radio
Tuned Settings
Changing the Power Tuning Interval
Changing the Maximum Default Power Allowed On a Radio
Values of RF attributes
Displaying RF Auto-Tuning Settings
Displaying
Radios in radio profile rp2
WX# display ap config
WX# display ap config 2 radio
Commands
Display auto-tune Neighbors ap 2 radio
WX1200# display auto-tune attributes ap 2 radio
Configuring RF AUTO-TUNING
Aeroscout Listeners
Configuring MAP Radios to Listen for AeroScout Rfid Tags
Status
Using an AeroScout Engine
Select Locate AeroScout Tag
QoS Parameters
MSS and how to configure and manage them
Optimized forwarding of wireless traffic for time-sensitive
About QoS
Set service-profile cac-mode
QoS Parameters
Set service-profile idle-client-probing
QoS Feature Description Configuration Command
Set service-profile proxy-arp
Keepalives and timeouts for clients set service-profile
On page 332 shows how WX switches classify ingress traffic
QoS on WX Switches-Classification of Ingress Packets
QoS on WX Switches-Marking of Egress Packets
Configuring Quality of Service
WMM QoS Mode
IP ToS
WMM QoS on the WX Switch
Service Forwarding Type
WMM Priority Mappings
CoS MAP Forwarding Queue
Default CoS-to-MAP-Forwarding-Queue Mappings
WMM QoS in a 3Com Network
MAP B receives the packet and does the following
To configure CAC, see Configuring Call Admission Control on
SVP QoS Mode
WMM QoS Mode
Changing QoS Settings
Set radio-profile name wmm-powersave enable disable
Set radio-profile name qos-mode svp wmm
Changing the Maximum Number of Active Sessions
Set service-profile name cac-mode none session
Set service-profile name cac-session max-sessions
Enabling CAC
Changing CoS Mappings
To change CoS mappings, use the following commands
Using the Client’s Dscp Value to Classify QoS Level
Set service-profile name use-client-dscp enable disable
Profile’s QoS Settings following command
Displaying QoS Information
WX1200# display radio-profile rp1
This example, the QoS mode is WMM
Displaying a Service
QoS Mode Wmm
WX1200# display qos default
Displaying the Default CoS Mappings
Display service-profile name cac session
WX# display service-profile sp1 cac session
Display qos cos-to-dscp-map cos-value
Displaying a DSCP-to-CoS Mapping
Displaying a CoS-to-DSCP Mapping
Display qos dscp-to-cos-map dscp-value
WX# display ap qos-stats
Displaying MAP Forwarding Queue Statistics
WX1200# display qos dscp-table
Display ap qos-stats apnumber clear
Configuring Quality of Service
Separate instance of PVST+ on each tagged Vlan
Loop in the topology and blocks one or more redundant paths
Tree protocol PVST+
All network ports as untagged members of the same Vlan
Enabling
Spanning Tree
Protocol
Set spantree priority value all vlan vlan-id
Snmp Port Path Cost Defaults
Port Speed Link Type Default Port Path Cost
Port Priority
Changing the STP Port Cost
Resetting the STP Port Cost to the Default Value
WX1200# clear spantree portcost 3-4 success change accepted
Changing the STP Port Priority
Resetting the STP Port Priority to the Default Value
Changing the STP Hello Interval
To change the hello interval, use the following command
Changing the STP Forwarding Delay
To change the forwarding delay, use the following command
Changing the STP Maximum Age
Features
Managing STP Fast
Convergence
Set spantree portfast port port-listenable disable
Displaying Backbone Fast Convergence State
Configuring Backbone Fast Convergence
This example, backbone fast convergence is enabled
Displaying Port Fast Convergence Information
Displaying Spanning Tree Information
Fast Convergence
Displaying Uplink Fast Convergence Information
Display spantree portvlancost port-list
Active option
Displaying the STP Port Cost on a Vlan Basis
WX1200# display spantree vlan mauve
WX1200# display spantree statistics
WX1200# display spantree blockedports Vlan default
Display spantree blockedports vlan vlan-id
Display spantree statistics port-listvlan vlan-id
Inactive
Clear spantree statistics port-listvlan vlan-id
Enables STP on the Vlan to prevent loops
Clearing STP Statistics
Counters again
WX1200# set vlan 10 name backbone port
Set port enable
Configuring and Managing Spanning Tree Protocol
IP address, the group address
Traffic. Igmp snooping is enabled by default
Feature on an individual Vlan basis
Disabling or Reenabling Igmp Snooping
Pseudo-Querier
Changing Igmp Timers
Reenabling Proxy
Reporting
You can specify a value from 2 through 255. The default is
Changing Other-Querier Present Interval
Changing the Last Member Query Interval
Set igmp mrsol mrsi seconds vlan vlan-id
Set igmp mrsol enable disable vlan vlan-id
Displaying Multicast Information
Displaying Multicast Configuration Information Statistics
Clear igmp statistics vlan vlan-id
Displaying Multicast Statistics Only
Clearing Multicast Statistics
Display igmp statistics vlan vlan-id
WX1200# display igmp Mrouter vlan orange
Display igmp querier vlan vlan-id
Display igmp querier vlan orange
Display igmp mrouter vlan vlan-id
Igmp receiver-table group 237.255.255.0/24
Overview of Security
Access Control Lists
ACL Commands
About Security
Setting Security ACLs
Traffic Direction
„ Vlan
ACL
Creating
Committing a
Security ACL
Set security acl ip acl-namepermit cos cos deny
WX1200# set security acl ip acl-1 permit 192.168.1.4
Number Protocol
Class of Service
Wildcard Masks
Common IP Protocol Numbers
Class-of-Service CoS Packet Handling
Icmp Message Type Number Icmp Message Code Number
Common Icmp Message Types and Codes
Following command filters TCP packets
Setting a TCP ACL
Following command filters UDP packets
Setting a UDP ACL
Commit acl-99, type the following command
WX1200# commit security acl acl-99 success change accepted
WX1200# commit security acl all success change accepted
Viewing the Edit Buffer
Viewing Committed Security ACLs
Viewing Security ACL Details
WX1200# display security acl hits
Displaying Security ACL Hits
ACLs
Mapping Security
WX1200# commit security acl acl-222 success change accepted
To map a security ACL to a user session, follow these steps
WX1200# display security acl map Acl-999
Displaying ACL Maps to Ports, VLANs, and Virtual Ports
WX1200# display security acl map acljoe
Clearing a Security ACL Map
Modifying a Security ACL
Modifying a Security ACL
To view the results, type the following command
WX1200# display security acl info
Set security acl ip acl-111 hits #4
ACL edit-buffer table
WX1200# rollback security acl acl-111
Dscp Values
Using ACLs to
Change CoS
Filtering Based on
Using the precedence and tos Options
Using the dscp Option
Are forwarded to any 10.10.90.x address on Distributed MAP
Following commands perform the same CoS reassignment as
Prioritization for
Legacy Voice over
Configuring and Managing Security Acls
Service
VoIP
WX4400# set security acl ip voip permit any
Commit the ACL to the configuration
Known Limitations
WX4400# commit security acl voip
Configuring a Service Profile for WPA
Configuring a Service Profile for RSN WPA2
Configuring a Radio Profile
Configuring an ACL to Prioritize Voice Traffic
Configuring a Vlan for Voice Clients
Configuring and Managing Security Acls
IP-Only Clients
Restricting
Client-To-Client
Forwarding Among
WX1200# set security acl map c2c vlan vlan-1 Out
Address, and how to map the ACL to a port and a user
WX1200# set security acl ip c2c permit 0.0.0.0
WX1200# commit security acl c2c
To save your configuration, type the following command
Configuring and Managing Security Acls
Certificates
Managing Keys and Certificates
About Keys and Certificates
Managing Keys and Certificates
File Type Standard Purpose
Generate key command
Generate request command. Copy
Pkcs Object Files Supported by 3Com
Certificates
Automatically
Generated by MSS
Creating Keys and Certificates
Certificate
Procedures for Creating and Validating Certificates
For Your Network more complex to use
File Type Steps Required Instructions Self-signed
# crypto generate key admin 1024 admin key pair generated
Crypto generate key admin domain eap ssh web 128 512 1024
# crypto generate self-signed admin Country Name US
Crypto generate self-signed admin eap web
Crypto pkcs12 admin eap web filename
To enter the one-time password, use the following command
Filename is the location of the file on the WX switch
Crypto otp admin eap web one-time-password
Crypto generate request admin eap web
# crypto generate request admin Country Name US
Crypto certificate admin eap web PEM-formatted
END Certificate
# crypto ca-certificate admin Enter PEM-encoded certificate
Displaying Certificate and Key Information
# display crypto certificate admin Certificate
Generate self-signed certificates
For SSH configuration information, see Managing SSH on
Key and Certificate
Object files
WX1200# display crypto certificate eap
WX1200# display crypto certificate admin
Display certificate information for verification
WX1200# crypto generate self-signed web
WX1200# display crypto certificate web
WX1200# crypto otp web SeC%#6@o%e
WX1200# crypto otp admin SeC%#6@o%c
Pkcs12 admin 2048admn.p12
WX1200# crypto otp eap SeC%#6@o%d
CSR and a Pkcs #7 Object File
WX1200# crypto generate request admin
WX1200# crypto certificate admin
WX1200# crypto ca-certificate admin
WX1200# display crypto ca-certificate admin
About AAA for Network Users
Authentication
MSS provides the following types of authentication
Authentication Types
„ Web „ Last-resort „ None
Authentication Algorithm
Authentication Flowchart for Network Users
Ssid Name Any
Last-Resort Processing
User Credential Requirements
Configuring AAA for Network Users
About AAA for Network Users
Configuring AAA for Network Users
Network Users
AAA Tools for
Wildcard Any for Ssid Matching
Local Override Exception
AAA Rollover Process
Remote Authentication with Local Backup
Shows the results of this combination of methods
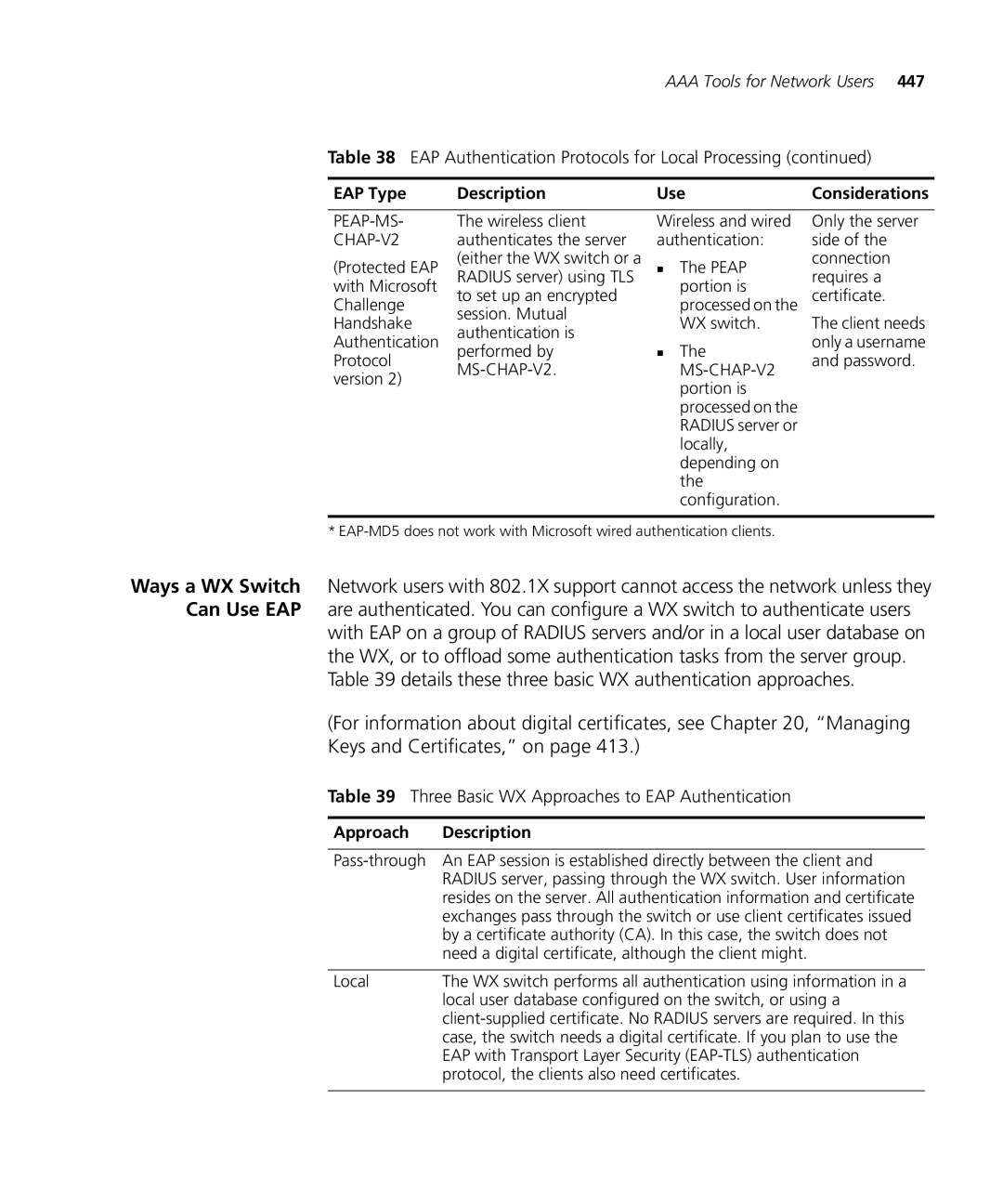
EAP Type Description Use
EAP Authentication Protocols for Local Processing
Approach Description
Three Basic WX Approaches to EAP Authentication
Eap
Effects Authentication Type On Encryption Method
Encryption Available to Various Authentication Methods
Authentication Last-Resort WebAAA
Configuring 802.1X Authentication
Success change accepted
Configuring 802.1X Authentication
Authentication Rule Requirements
Clear dot1x bonded-period
To set the Bonded Auth period, use the following command
Bonded Auth Period
Set dot1x bonded-period seconds
WX1200# set dot1x bonded-period 60 success change accepted
Bonded Auth Configuration Example
Displaying Bonded Auth Configuration Information
Display dot1x config
WX1200# display dot1x config
Authentication
Authorization by
MAC Address
WX1200# clear mac-user 010f03040506 success change accepted
Clearing MAC Users and Groups
Clear mac-user mac-addrgroup
Clear mac-user mac-address
For example, to add the MAC user 000102030405 to Vlan red
For a complete list of authorization attributes, see on
Set radius server server-nameauthor-password password
How WebAAA Portal Works
Display of the Login
WebAAA
WX Switch Requirements
Configuring Web Portal WebAAA
Configuring AAA for Network Users
Portal ACL and User ACLs
Client NIC Requirements
WX Switch Recommendations
„ Configure the NIC to use Dhcp to obtain its IP address
Network Requirements
Configuring Web To configure Web Portal WebAAA
Web Portal WebAAA Configuration Example
Portal WebAAA
Configure individual WebAAA users
Display the service profile to verify the changes
WX1200# display config
Display the configuration
Displaying Session Information for Web Portal WebAAA Users
Display sessions network user user-glob
WX4400# display sessions network ssid mycorp
Configuring Web Portal WebAAA
Copying and Modifying the Web Login
„ If the switch nonvolatile storage has a page in web named
Change the logo
Custom Login Page Scenario
Map a radio to the temporary radio profile and enable it
Save the modified
Change the warning statement if desired
Change the greeting
URLs variables you can include in a redirect URL
Variables for Redirect URLs
Values for Literal Characters
Display security acl info acl-nameall editbuffer
Add the last rule contained in portalacl
Set service-profile name web-portal-acl aclname
Period
Commit security acl
Set service-profile name web-portal-session-timeout seconds
Last-Resort Access
WX1200# display service-profile last-resort-srvcprof
481
Process for Users of a Third-Party AP
Configuring AAA for Users of Third-Party APs
Requirements Third-Party AP Requirements
Radius Server Requirements
Set authentication mac wired mac-addr-glob method1
Set authentication proxy ssid ssid-nameuser-glob
Set radius proxy port port-listtag tag-valuessid
WX4400# set authentication proxy ssid mycorp ** srvrgrp1
WX4400# set authentication mac wired aabbcc010101 srvrgrp1
Authorization
Assigning
Attributes
Authentication Attributes for Local Users
Filter-id
Idle-timeout
Attribute Description Valid Values End-date
Start-date,end-date, or both
Attribute Description Valid Values Service-type
Session-timeout
Ssid
Time-of-day
Attribute Description Valid Values Start-date
Or group in the local WX database and specify its value
Attribute Description Valid Values Url
Vlan-name
Set service-profile name attr attribute-name value
Assigning a Security ACL Locally
Commands for Assigning a Security ACL Locally
Assigning a Security ACL on a Radius Server
Encryption-Type Encryption Algorithm Value Assigned
Assigning and Clearing Encryption Types Locally
Encryption Type Values and Associated Algorithms
Assigning and Clearing Encryption Types on a Radius Server
Vlan Assigned By
After Roaming
Vlan Assignment After Roaming from One WX to Another
Location Policy
Overriding or
Configuring AAA for Network Users
Set location policy deny if
Set location policy permit
WX1200# set location policy deny if user eq *.theirfirm.com
Displaying and Positioning Location Policy Rules
Applying Security ACLs in a Location Policy Rule
Clear location policy rule-number
To delete a location policy rule, use the following command
Clearing Location Policy Rules Disabling
WX1200 display location policy
Network resource usage
Wireless Network
Accounting for
Users
WX1200-0013#display accounting statistics
User started on WX1200-0013
User roamed to WX1200-0017
WX1200# display accounting statistics
User terminated the session on WX1200-0017
WX1200# display aaa
Avoiding AAA
Problems
Configuration Order
WX switch and how to avoid them
Configuration for a Correct Processing Order
Configuration Producing an Incorrect Processing Order
All of the ports or Distributed MAPs
Name and identifying the accessible port or ports
Accessing any MAP access ports, Distributed MAPs, or wired
Mobility Profile
To remove a Mobility Profile, type the following command
WX1200# display mobility-profile Mobility Profiles
Clear mobility-profile name
Network User
NamePorts ========================= Tulip
WX1200# set server group sg1 members r1
Save the configuration
WX1200# set user Natasha password moon
WX1200# set radius server r1 address 10.1.1.1 key sunny
WX1200# set radius server r1 address 10.1.1.1 key starry
WX1200# set user Natasha attr session-timeout
WX1200 save config
WX1200# set user Natasha attr vlan-name red
Save the configuration
WX1200# display location policy
Redirect bldga-prof-VLAN users to the Vlan bldgb-eng
Configuring AAA for Network Users
With Radius
Wireless Client, MAP, WX Switch, and Radius Servers
„ Transmission attempts
„ Timeout WX wait for a server response 5 seconds
Before You Begin
Radius Servers
Clear radius deadtime key retransmit timeout
WX switch uses to authenticate itself to the Radius server
Set radius server server-nameaddress ip-address key string
Configuring Individual Radius Servers
WX1200# clear radius deadtime success change accepted
WX1200# set radius client system-ip success change accepted
Radius Server
Radius servers, type the following command
Ordering Server Groups
Set server group group-namemembers server-name1
Set server group group-nameload-balance enable
Configuring Load Balancing
To configure load balancing, use the following command
Enable load balancing by typing the following command
Clear server group group-name
To remove a server group, type the following command
Adding Members to a Server Group
Set server group group-namemembers
Configure Radius servers. Type the following commands
Radius and Server
Group
Display the configuration. Type the following command
Configuring Communication with Radius
Enabling
On Wired
Managing
Ports
WX1200# clear dot1x port-control success change accepted
Set dot1x port-control Forceauth forceunauth auto port-list
Set dot1x tx-period seconds
Authentication
Configuring Key Transmission Time Intervals
Set dot1x key-tx enable disable
WX1200# clear dot1x tx-period success change accepted
Setting EAP
Retransmission
Attempts
Set dot1x reauth-max number-of-attempts
Enabling Disabling Reauthentication
Setting the Maximum Number Reauthentication Attempts
Set dot1x reauth enable disable
WX1200# set dot1x reauth-period
Setting Reauthentication Period
WX1200# clear dot1x reauth-max success change accepted
Set dot1x reauth-period seconds
Set dot1x quiet-period seconds
Clear dot1x max-req
Set dot1x timeout supplicant seconds
Setting Timeout for an Authorization Server
Type the following command to reset the timeout period
Set dot1x timeout auth-server seconds
Configuration
Display dot1x clients stats config
WX1200# display dot1x clients
WX1200# display dot1x stats
Managing 802.1X on the WX Switch
Endpoint Security
About Soda
Soda Endpoint Security Support on WX Switches
About Soda Endpoint Security
Functionality tasks
Configuring Soda Functionality
Https//hostname/soda/ssid/xxx.html
Install soda agent agent-fileagent-directory directory
WX1200# install soda agent soda.ZIP agent-directory sp1
WX1200# copy tftp//172.21.12.247/soda.ZIP soda.ZIP
Enabling Soda Functionality for the Service Profile
Set service-profile name soda mode enable disable
Set service-profile name enforce-checks enable disable
Set service-profile name soda success-page
Clear service-profile name soda success-page
Set service-profile name soda failure-page
Clear service-profile name soda failure-page
Set service-profile name soda remediation-acl acl-name
Clear service-profile name soda remediation-acl
Set service-profile name soda logout-page
Clear service-profile name soda logout-page
Set ip https server enable
Uninstall soda agent agent-directory directory
Uninstalling the Soda Agent Files from the WX Switch
Set service-profile name soda agent-directory directory
Clear service-profile name soda agent-directory
WX1200# uninstall soda agent agent-directory sp1
Configuring Soda Endpoint Security for a WX Switch
Displaying Clearing Administrative Sessions
Display sessions admin console telnet client
Clear sessions admin console telnet client session-id
WX1200# clear sessions admin
Displaying Clearing All Administrative Sessions
Displaying Clearing an Administrative Console Session
WX1200 display sessions admin
Displaying Clearing Administrative Telnet Sessions
Displaying Clearing Client Telnet Sessions
WX1200 display sessions telnet
Displaying Clearing Network Sessions
Display sessions network
WX1200# display sessions network
Network Session to get more in-depth information
WX1200# clear sessions network user Bob
Displaying Clearing Network Sessions by Username
WX1200# display sessions network user E
Clear sessions network user user-glob
For example, to clear all sessions for MAC address
Address set of MAC addresses, type the following command
Clear sessions network vlan vlan-glob
WX1200# clear sessions network vlan red
WX1200 display session network session-id
Session Timers
Session-id command
Changing Network
To disable the user idle timeout, use the following command
Changing or Disabling the User Idle Timeout
RF Detection
About Rogues
Rogue Classification
Rogue Detection Lists
Rogue Detection Algorithm
Dynamic Frequency Selection DFS
Rogue Detection and Countermeasures
Detection Features
Summary of Rogue lists the rogue detection features in MSS
Rogue Detection Features
Countermeasures
Clear rfdetect vendor-list client ap mac-addrall
Set rfdetect vendor-list client ap mac-addr
Set rfdetect ssid-list ssid-name
WX1200# display rfdetect ssid-list Total number of entries
Clear rfdetect ssid-list ssid-name
Rfdetect Black-list
To display the client black list, use the following command
Following example shows the client black list on WX switch
Set rfdetect black-list mac-addr
Rfdetect Attack-list
To display the attack list, use the following command
Following example shows the attack list on a switch
Set rfdetect attack-list mac-addr
Clear rfdetect ignore mac-addr
To display the ignore list, use the following command
Mac-addris the Bssid of the device you want to ignore
Set rfdetect ignore mac-addr
Countermeasures
Enabling Countermeasures
Signatures
Reenabling Active
Scan
Enabling MAP
WXR100desk# set rfdetect signature ?
Creating an Encrypted RF Fingerprint Key as MAP Signature
Set rfdetect signature key encrypted keyvalue
WXR100desk# set rfdetect ?
Notifications
Reenabling Logging
Rogues
Enabling Rogue
IDS and DoS Alerts
Rogue Detection and Countermeasures
Examples
IDS and DoS Log Messages
Message Type Example Log Message
Client aabbccddeeff is sending rsvd mgmt frame D
IDS and DoS Log Messages
Detection
You can use the CLI commands listed in to display rogue
Rogue Detection Display Commands
Displaying RF
Rogue Detection Display Commands
WX# display rfdetect clients
Display rfdetect clients mac mac-addr
Detection Counters command
Display rfdetect counters
WX1200# display rfdetect counters
Displaying Ssid or Bssid Information for a Mobility Domain
Display rfdetect mobility-domain ssid ssid-namebssid
WX1200# display rfdetect mobility-domain
Displaying RF Detection Information
WX1200# display rfdetect visible ap Radio
Displaying the APs Detected by MAP Radio
Display rfdetect data
WX1200# display rfdetect data
Displaying Countermeasures Information
Display rfdetect countermeasures
WX# display rfdetect countermeasures
Rogue Detection and Countermeasures
About System Files
Displaying Software
Version Information
To also display MAP information, type the following command
WX# display version
WX# display version details
Boot
To display boot information, type the following command
Working with Files
WX1200# dir file
Following command displays the files in the old subdirectory
WX1200# dir boot0
URL can be one of the following
WX1200# dir core
WX1200# copy floor2wx tftp//10.1.1.1/floor2wx
„ boot0/filename „ boot1/filename
Md5 boot0 boot1filename
WX1200# copy tftp//10.1.1.107/wxb04102.rel boot1wxb04102.rel
To delete a file, use the following command
WX1200# md5 boot0wxb04102.rel
Delete url
To remove subdirectory corp2, type the following example
WX1200# mkdir corp2 success change accepted. WX1200# dir
WX1200# rmdir corp2 success change accepted
Running
Configuration Files
Save config filename
WX1200# display config area vlan
WX1200# load config newconfig
WX1200# save config newconfig
Set boot configuration-file filename
Load config url
Clear boot config
Set boot backup-configuration filename
WX1200# clear boot backup-config
Backup boot configuration Backup.cfg
System
Managing System Files
WX1200# backup system tftp/10.10.20.9/sysabak critical
System Image
Switch for
Upgrade
Upgrading
Reset system force
Upgrading an Individual Switch Using the CLI
WX1200# reset system
Upgrade Scenario
WX1200# backup system tftp//172.16.0.10/sysabak
WX1200# copy tftp//172.16.0.10/WX040101.20 boot1WX040100.20
Troubleshooting a
WX Setup Problems and Remedies
Type the save config
WX Setup Problems and Remedies
Is Lost
Recovering
Enable Password
System When
Levels
System Log
Log Message
Components
Event Severity Levels
System Log Destinations and Defaults
Display log buffer trace
Clear log buffer trace
Clear log server ip-addr
WX1200# display log buffer severity error
Logging to the Log Buffer
Set log buffer severity severity-level
To clear the buffer, type the following command
To disable console logging, type the following command
Logging to the Console
For information on severity levels, see on
Setting Telnet Session Defaults
Set log sessions severity severity-levelenable
Logging Messages to a Syslog Server
Logging to the Trace Buffer
To disable session logging, use the following command
Changing the Current Telnet Session Defaults
To disable trace logging, use the following command
Saving Trace Messages in a File
Displaying the Log Configuration
Tracing Session Manager Activity
Using the Trace
Command
Tracing Authentication Activity
Clear trace all trace area
Tracing Authorization Activity
Tracing 802.1X Sessions
WX1200# display trace
WX1200# display log trace severity error
WX1200# set trace ?
WX1200# display log trace facility
Interfaces
Using display
Commands
For more information about Vlan interfaces, see Configuring
Database FDB information, type the following command
Mirroring
Configuring Port
Port Mirroring
Requirements
Monitoring Traffic
Remotely
Monitoring
Remote Traffic
WX1200# set snoop snoop1 observer 10.10.30.2 snap-length
Deleting a Snoop Filter
Displaying Configured Snoop Filters
To delete a snoop filter, use the following command
Editing a Snoop Filter
Removing Snoop Filter Mappings
Following command shows the mapping for snoop filter snoop1
Displaying the Snoop Filters Mapped to a Radio
Displaying the Snoop Filter Mappings for All Radios
Preparing an Observer Capturing Traffic
Filter operates until you manually disable it
Following command enables snoop filter snoop1
Following command shows statistics for snoop filter snoop1
Set snoop filter-nameall mode enable disable
Capturing System
Sending it to
Technical Support
Corenetsys.core.217.tar
Corenetsys.core.217.tar
Support
System Requirements
WEB View
Logging Into Web View
Stated
3Com Mobility System Software MSS supports the standard
On page 652. Also supported are 3Com vendor-specific
Attributes VSAs, listed in on
Supported Standard Extended Attributes
Rcv Sent Access Acct Attribute Type Resp? Reqst? Description
Supported Standard and Extended Attributes
Filter-id outboundacl.out
Filter-id inboundacl.in
Displayed, they must
NAS
Radius
Acct-Output Yes
3Com
Vendor-Specific
Users, on
YY/MM/DD-HHMM
3Com VSAs
Protocol Port Function
Traffic Ports Used by MSS
IP/ICMP
Dhcp Server
Chapter E Dhcp Server
Set interface dhcp-server command’s primary-dns
Set ip dns server command
Dhcp Server
Displaying Dhcp
Server Information
Displayed instead
Product to Gain
Service Benefits
Solve Problems Online
Register Your
Professional
Warranty
Access Software
Purchase Extended
Country Telephone Number
US and Canada Telephone Technical Support and Repair
Latin America Telephone Technical Support and Repair
Glossary
802.11b
Radio that can receive and transmit signals at Ieee 802.11b
802.11a
GHz and data rates of up to 54 Mbps
See security ACL
See ACE
AES
BSS
Ccmp
Bssid
CBC-MAC
CCI
Chap
CPC
CRC
CSR
Dhcp
DES
Dynamic Host See Dhcp Configuration Protocol
EAP-TLS
EAP
ESS
Etsi
FCC
FDB
Fhss
Gbic
GMK
GTK
Hmac
ICV
Hpov
Https
IAS
Infrastructure
Igmp snooping
Industry Canada
Information element
Ldap
ISL
ISO
Lawn
MAC
MD5
MAP
MIC
Mpdu
MS-CHAP-V2
NAT
Msdu
MSS
MTU
Pkcs
Peap
PEM
PIM
PMK
PRF
Prng
PSK
PVST+
PTK
RC4
RSA
RSN
Rssi
Ssid
SHA
SIP
SSH
STP
SSL
TLS
TLV
Ttls
Vlan
NII
Web View
Vlan glob
VSA
Watch list
WEP
WPA IE
Wisp
Wlan
WPA
Glossary
Glossary
Numbers
Index
Sessions, clearing 557 sessions, displaying
Cipher suites, RSN enabling
ARP
Index
Index
See also MAC addresses MAC addresses
Names
Https
Radius
717
Repair support, Europe, Middle East, and Africa Configuring
Seed, Mobility Domain configuring 154 defined
STP
Index
Usernames Invalid certificate Case-sensitive
Index
Command Index
Clear summertime
Load config 61 Md5 606 mkdir Monitor port counters
Command Index
729
Set radius proxy port
Command Index