19.5 Overall View
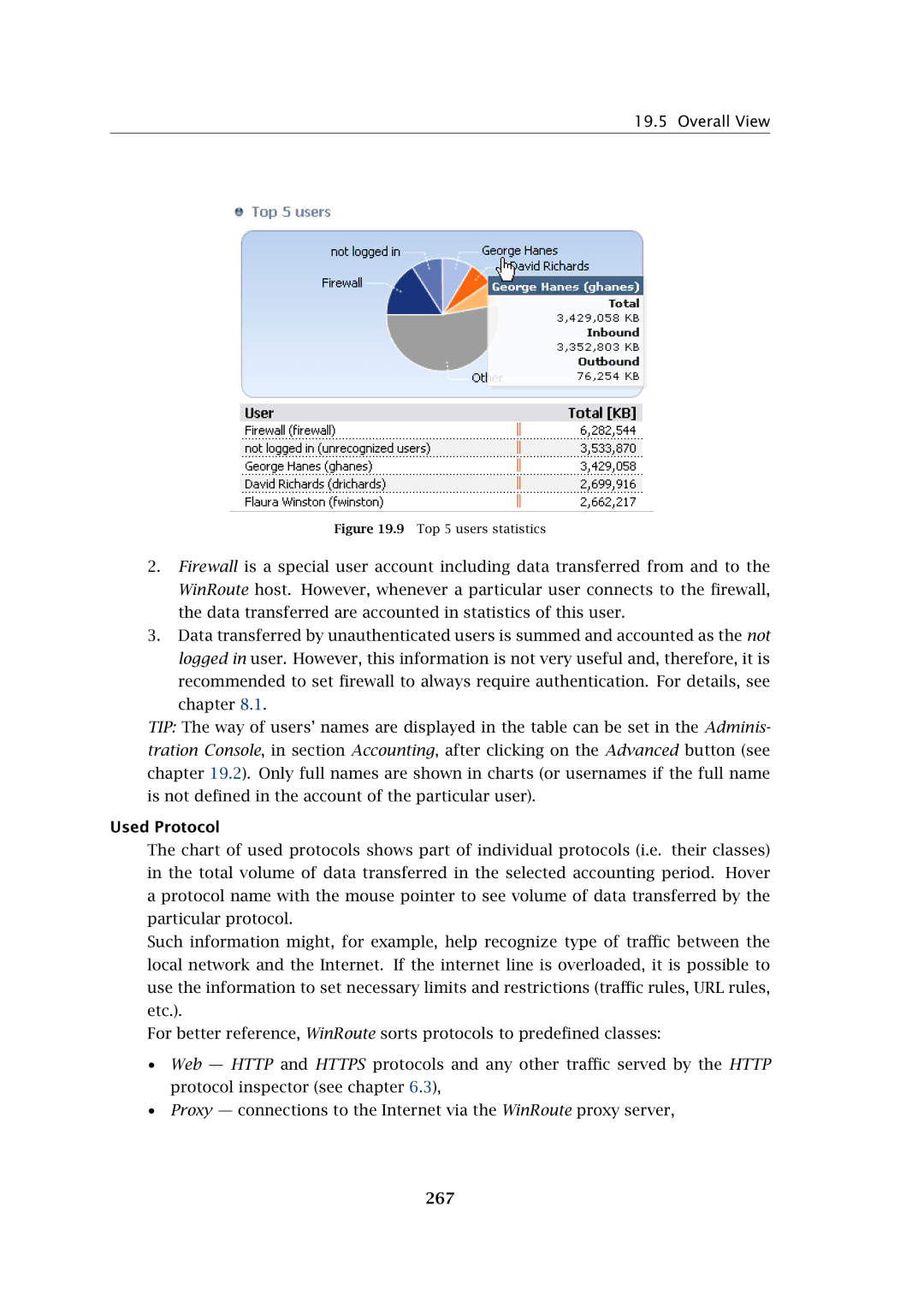
Figure 19.9 Top 5 users statistics
2.Firewall is a special user account including data transferred from and to the WinRoute host. However, whenever a particular user connects to the firewall, the data transferred are accounted in statistics of this user.
3.Data transferred by unauthenticated users is summed and accounted as the not logged in user. However, this information is not very useful and, therefore, it is recommended to set firewall to always require authentication. For details, see chapter 8.1.
TIP: The way of users’ names are displayed in the table can be set in the Adminis- tration Console, in section Accounting, after clicking on the Advanced button (see chapter 19.2). Only full names are shown in charts (or usernames if the full name is not defined in the account of the particular user).
Used Protocol
The chart of used protocols shows part of individual protocols (i.e. their classes) in the total volume of data transferred in the selected accounting period. Hover a protocol name with the mouse pointer to see volume of data transferred by the particular protocol.
Such information might, for example, help recognize type of traffic between the local network and the Internet. If the internet line is overloaded, it is possible to use the information to set necessary limits and restrictions (traffic rules, URL rules, etc.).
For better reference, WinRoute sorts protocols to predefined classes:
•Web — HTTP and HTTPS protocols and any other traffic served by the HTTP protocol inspector (see chapter 6.3),
•Proxy — connections to the Internet via the WinRoute proxy server,