Chapter 20 Logs
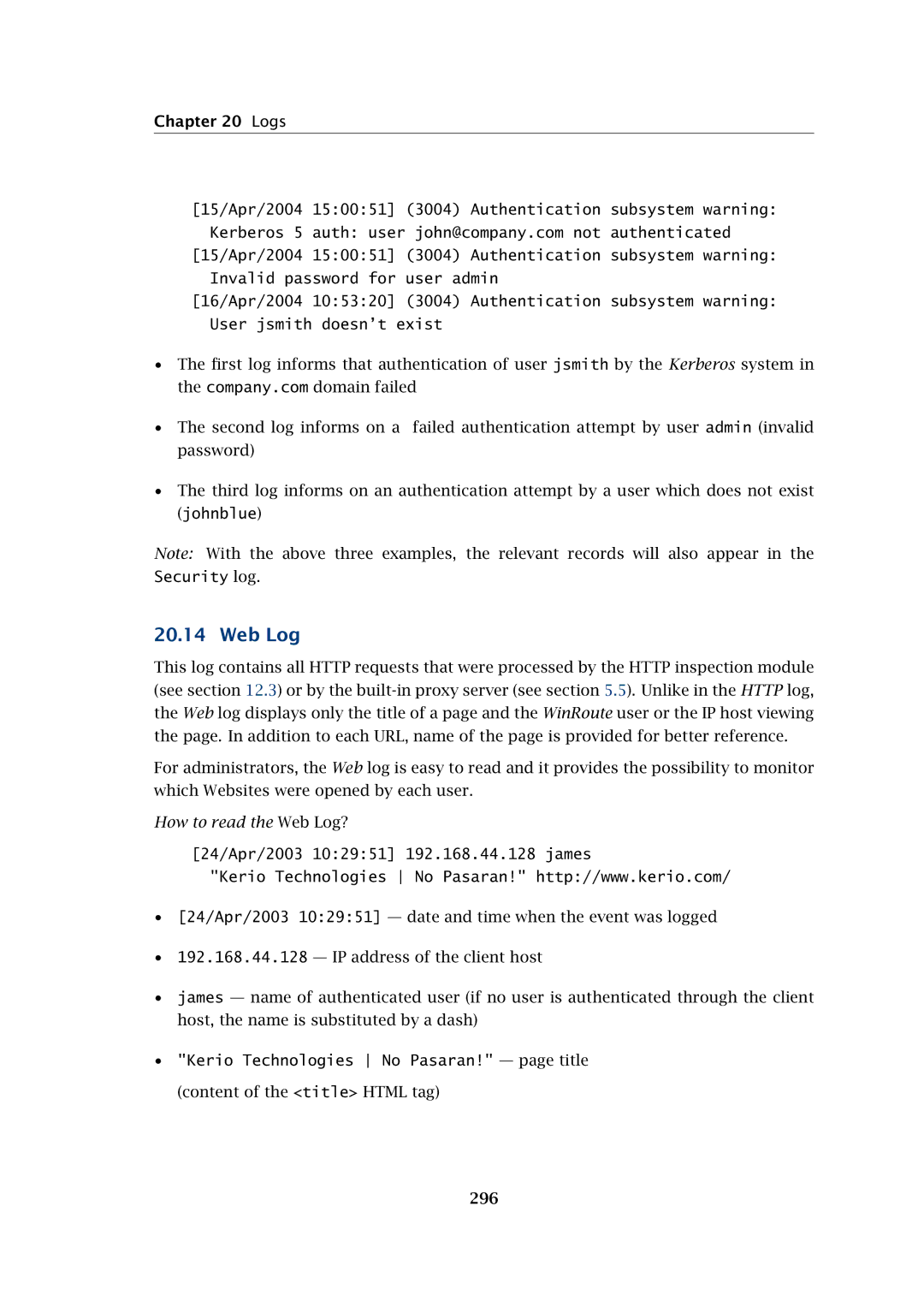
[15/Apr/2004 15:00:51] (3004) Authentication subsystem warning: Kerberos 5 auth: user john@company.com not authenticated
[15/Apr/2004 15:00:51] (3004) Authentication subsystem warning: Invalid password for user admin
[16/Apr/2004 10:53:20] (3004) Authentication subsystem warning: User jsmith doesn’t exist
•The first log informs that authentication of user jsmith by the Kerberos system in the company.com domain failed
•The second log informs on a failed authentication attempt by user admin (invalid password)
•The third log informs on an authentication attempt by a user which does not exist (johnblue)
Note: With the above three examples, the relevant records will also appear in the Security log.
20.14 Web Log
This log contains all HTTP requests that were processed by the HTTP inspection module (see section 12.3) or by the
For administrators, the Web log is easy to read and it provides the possibility to monitor which Websites were opened by each user.
How to read the Web Log?
[24/Apr/2003 10:29:51] 192.168.44.128 james
"Kerio Technologies No Pasaran!" http://www.kerio.com/
•[24/Apr/2003 10:29:51] — date and time when the event was logged
•192.168.44.128 — IP address of the client host
•james — name of authenticated user (if no user is authenticated through the client host, the name is substituted by a dash)
•"Kerio Technologies No Pasaran!" — page title (content of the <title> HTML tag)
296