Wireless LAN Mobility System
WX4400 3CRWX440095A WX1200 3CRWX120695A WXR100 3CRWXR10095A
3Com Corporation 350 Campus Drive Marlborough, MA USA
United States Government Legend
Contents
Getting Started
Enabling Keyboard Shortcut Mnemonics Windows XP Only
125 Placing Third-Party Access Points
131
175 Launching a Web Management Session with the Switch 176
186 Configuring Snmp 187
Resetting CoS Mapping to their Default Values
233
241 Configuring an 802.1X Wireless Service 242
244
247
258
299 Creating a Radius Server Group 300
316
319
320
337
Example 3 Deployment Site Has DNS But No Dhcp
WX File Management Options Devices Tab
347
356
Enabling or Disabling Management of a Switch by 3WXM
Viewing the Operation Log 358
Applying Policy Changes to Switches 375
375
394
Generating a Radio Details Report 395
Generating a Site Survey Order Generating a Work Order
410 Displaying 802.11 Coverage
412
439
465
468
496
Register Your Product 507
Page
List conventions that are used throughout this guide
Conventions
Icon Description
Documentation
Comments
Pddtechpubscomments@3com.com
Example
Requirements for 3WXM client 3WXM Client
Hardware Requirements
Hardware Requirements for Running 3WXM Client
Hardware Requirements for 3WXM Monitoring Service
Hardware Requirements for Running 3WXM Monitoring Service
Hard drive space Available Monitor resolution
Number Radios WX Switches 50+ WX Switches
Installation
Software
Preparing for
User Privileges
Installing 3WXM
Installing 3WXM
Installing 3WXM
Click Uninstall
Click Continue
Overview
Plan is displayed by the 3WXM client
Display Panels
Display Panels
Alerts
Alert Category Description
Alerts
Rogue Detection
Saving or Discarding Configuration Changes
Reviewing and Deploying Switch Configuration Changes
Configuration Wizards
Working with the 3WXM User Interface
Resize Icons
Properties Dialogs
Option Description
3WXM Menu Options
Menu Option Description
3WXM Tool Bar Options
Menu Option Description
Configuration
Verification
Copying, Pasting
Deleting
Objects
Organizer Panel
Copy and Paste Content Panel
Replace Organizer Panel
Enabling Keyboard
Shortcut
Mnemonics
Windows XP Only
Enabling Keyboard Shortcut Mnemonics Windows XP Only
Working with the 3WXM User Interface
Switch Manager 3WXM, restricting access to 3WXM, creating
Following steps describe how to start 3WXM
Starting 3WXM
Managing network plans, and defining a Mobility Domain
Next
Starting 3WXM
Getting Started
Restricting Access to 3WXM
Accounts
Working with Network Plans
Plan
Creating a Network To create a network plan
Plans
3WXM installation directory on the 3WXM Services host
Can also share a network plan with others
Saving a Network Plan with a New Name
Managing Network Plans
Plan
Managing Network Plans
To disable notification
Defining a Mobility Domain
Traffic Ports Used for AAA Servers and Management Servers
Protocol Port Function
Creating a
Creating a WX Switch
Third-Party AP
Working with Network Plans
Auto-Tuning
Settings to
Changing
Country Code
Uploading a WX Switch into Network Plan
Click Next Click Finish
Converting Auto DAPs into Statically Configured APs
Affinities for Network Domain Seeds
Affinity Value Assigned To
RF Planning
Toolbar icons available in RF Planning Tools
RF Planning Overview
Modifying a Site
Creating or
To create or modify a site
Creating or Modifying a Site
Modifying Buildings in a Site
Creating or Modifying Buildings in a Site
Planning the 3COM Mobility System
Modifying Floors
Drawing Floor
Importing or
Details
To prepare a drawing before importing it into 3WXM
Planning the 3COM Mobility System
Importing or Drawing Floor Details
Operating Tips
Useful AutoCAD Operations and Naming-Conventions
Common AutoCAD Layer Names
Importing the Drawing
To crop the paper space
Floor Plan After Importing
To adjust the scale
Floor Plan After Cropping
To adjust the origin point
Origin point
New location of origin point
Hiding Layers
Shows the same floor plan as after hiding unnecessary layers
Adding or removing a layer
Moving an object from one layer to another
To clean up a drawing
Importing or Drawing Floor Details
Planning the 3COM Mobility System
To draw an object
Object Action
Planning the 3COM Mobility System
To create RF obstacles for all objects in a layer
To create RF obstacles for an area in a drawing
To use the Create RF Obstacle Dialog box
To create RF obstacles by grouping objects
Create RF Obstacle dialog box is shown in Figure
Drawing RF Obstacles
3WXM supports concave polygons. a concave
Specifying the RF Characteristics of a Floor
Adding LOS Points
Site Survey Recommendations
To import LOS points from a file
Specifying the RF Characteristics of a Floor
Planning the 3COM Mobility System
To create LOS points in 3WXM
Click Next. The radio configuration page appears
Specifying the RF Characteristics of a Floor
To delete an LOS point
To move an LOS point
Generating a Site Survey Order
Click Generate
Importing RF Measurements
Click Next
Applying the RF Measurements to the Floor Plan
To create a wiring closet
Planning the 3COM Mobility System
Shared Coverage Areas
Shows an example of shared coverage areas
Drawing a Coverage Area
Unsupported Shared Coverage Area Example
Object Action
Specifying the Wireless Technology for a Coverage Area
Specifying Coverage Area Properties
Click Next. The Floor Properties page appears
Specifying Floor Properties for the Coverage Area
Specifying Default Device Settings for the Coverage Area
Planning the 3COM Mobility System
WX4400 switches support indirect MAP connections only
Configuring Capacity Calculation for Data
Configuring Capacity Calculation for Voice
Planning the 3COM Mobility System
Areas
Planning the 3COM Mobility System
Defining Wireless Coverage Areas
Planning the 3COM Mobility System
Defining Wireless Coverage Areas
Planning the 3COM Mobility System
Creating and Placing An Icon for a Third-Party Access Point
AP Icon to its Floor
Location
Place tab
Planning the 3COM Mobility System
Placing Third-Party Access Points
Planning the 3COM Mobility System
Placing Installed
Auto-Configured
MAPs
Plan
Planning the 3COM Mobility System
To specify design constraints
WX4400 switches support indirect MAP connections only
Computing MAP Placement
To compute and place MAPs
Go to To review coverage area computation
To review coverage area computation
Planning the 3COM Mobility System
Locking and Unlocking MAPs
To lock a MAP
To assign channels
Channel Assignment to Minimize Co-Channel Interference
Computing MAP Placement
Planning the 3COM Mobility System
To compute optimal power
Planning the 3COM Mobility System
To resolve optimal power computation problems
Verifying the Wireless Network
Resolving coverage gaps
To place an RF measurement point
„ To list disabled access points, select Show Disabled MAPs
Signal strengths for any location on the floor
To use the RF interactive measurement mode
RF Measurement Information
Shows the information available in the RF measurement table
Value
Generating RF
Network Design
Information
To generate a work order report
Click Generate Work Order
WX Switch Configuration Objects
Parameters
WX Switch Object Types
Category Object Type Description
WX Switch Object Types
AAA
Adding a WX Switch to the Network Plan
Creating a WX Switch Using the Create Wireless Switch Wizard
Configured Switch Network Plan
Click Management Interface
Configuration File
Click WX Associations
Configuring Basic
Settings
Advanced
Reviewing
Using the Create Wireless Switch Wizard
Password is encrypted when you type it Click Next
Configuring WX System Parameters
To set up a switch
„ V2c
Setting Up a Switch
„ 11b „ 11g
Modifying Basic Switch Parameters
Changing the WX To change the WX software version
Software Version
Model
Select the model from the drop-down list Click OK
Information
To convert an Auto DAP
To delete an Auto DAP
Viewing Port Settings
Viewing Changing Port Settings
Settings
Enabling Link Notifications
Click Properties Select Snmp Link Traps
Click Next
Configuring WX System Parameters
Viewing and Changing Port Settings
Configuring WX System Parameters
Viewing and Changing Port Settings
Viewing Port Groups To view port groups
Select Port Groups
Content panel, select the row for the port group
Creating a Port Group To create a port group
Group
Click Properties
3WXM, Https is always enabled and listens on port
Management Service Settings
Select Management Services
Viewing
Viewing and Changing Management Settings
Configuring an Snmp V1 or V2c Community String
Task List panel, select Community
Configuring a USM Snmp V3 User
Configuring WX System Parameters
Configuring a Notification Profile
Configuring a Notification Target
Click Properties
Community string names are transmitted in clear text
Configuring WX System Parameters
Select the object you want to modify
Configuring 3WXM Services as a Notification Target
Task List panel, select 3WXM Notification Target
Community string names are transmitted in clear text
Click Finish
Trace Settings
Setting Log
Viewing Log Settings To view log settings
Configure logging to the console
Creating an External Log Server
Creating a Trace Area
Configuring IP
Services Settings
Setting
Static routes
Select IP Services
You cannot use the word all as the name of an IP alias
Select IP Services
Select IP Services
Configuring VLANs
Users and VLANs
Roaming and VLANs
Viewing VLANs To view VLANs
Configuring WX System Parameters
Viewing and Configuring VLANs
To tag a port or port group, select the Tag checkbox
Changing STP Port Settings in a Vlan
Click OK
Enabling STP Fast Convergence Features
Configuring WX System Parameters
Configuring Static Multicast Ports
Click Properties
Viewing and Configuring VLANs
Restricting Layer
A Vlan
Select Dhcp Server to enable it on the Vlan
Server that stores confidential salary information
Configuring ACLs
Last ACE of an ACL
Viewing ACLs To view ACLs
To configure an ACL
IP Protocol Number
Configuring WX System Parameters
„ 0 normal-Packets with normal TOS defined are filtered
To enable the hit counter for an ACE
Configuring Advanced ACL Settings
To change the hit sample rate
To enable the established option for TCP ACEs
To specify the type and code for Icmp ACEs
Icmp Messages and Codes
Icmp Message Type Number Code Number
Adding a New ACE to a Configured ACL
Viewing and Configuring ACLs
Individual ACE from an ACL
Mappings
Changing CoS
Mappings
Mapping
Setting a Range Dscp Values to a
Configuring WX System Parameters
Viewing Configuring Wireless Services
Service Profiles
Service Profile Parameters
Service Profile Parameters
Access Rules
Service Profile Type Access Rule Type Default Access Glob
Viewing and Configuring Wireless Services
„ Local EAP-TLS-EAP with TLS
Services
Viewing Wireless To view wireless services
Select Wireless Services
„ WPA
Select the EAP type
Configuring Wireless Parameters
„ WPA
Configuring Wireless Parameters
Web-Portal WebAAA Service
„ Static WEP Click Next
Viewing and Configuring Wireless Services
Access Service
„ WPA
Go to step Click Finish
Service Profile Tab
WPA, RSN Tab
Broadcast Settings Tab
Authorization Attributes Tab
Static WEP Tab
Voice Configuration Tab
Radio Profile Selection Tab
Client Timeout tab lists settings for client session timers
Client Timeout Tab
Rate Configuration Tab
Viewing and Configuring Wireless Services
Soda Tab
Click Properties
Modifying Encryption Settings
Viewing and Configuring Wireless Services
Modifying Access Rules
Profiles
Configuring Radio
Select Radio Profiles
Creating a Radio To create a radio profile
Profile
Click Reset To Default
Radio Profile Tab
Attributes Tab
Auto Tune Tab
Service Profile Selection Tab
Radio Selection Tab
Profile Settings
Auto-DAP Profile
Profile Settings
Viewing and Changing the Auto-DAP Profile
Configuring MAPs
DAPs into Statically Configured DAPs Deleting Auto DAPs
Through radio signals
See Deleting Auto DAPs on
Viewing the To view the configured MAPs
Configured MAPs
Select Access Points
Maximum MAPs Supported Per Switch
„ 112233445566778899aabbccddeeff00
Transmit Power box, specify the transmit power for the radio
To configure a directly connected MAP
Channel Number list, select the channel number for the radio
Click the plus sign next to Wireless
Transmit Power box, specify the transmit power for the radio
Configuring Wireless Parameters
Configured
Viewing Radio To view radio settings
Changing Radio
Select Radios
Detection Settings
Changing RF
Select RF Detection
OUI List
List
Edit the MAC address in the MAC Address box Click OK
Countermeasures
Select RF Detection Select Enable AP Signature
Configuring Wireless Parameters
Creating
Managing Users
Local User
Database
You can create two types of users in the local database
Groups in the Local Database
User
Creating a Named To create a named user
Select Local User Database
Group and Assigning Users To It
Creating and Managing Users in the Local User Database
Task List panel, select MAC User Group
Encryption-type
Authentication Attributes for Local Users
End-date
Filter-id
Idle-timeout
Mobility-profile
Session-timeout
Service-type
Ssid
Start-date
Start-date , end-date , or both
Time-of-day
Time-of-day tu1000-1600,th1000-1
600
Time-of-day wk0900-1700,sa2200
Radius Settings
Group
A 3Com Mobility System
Url
Server
Settings, Servers, Server Groups
Select Radius
Click Next
Viewing and Configuring Radius Settings
To change default values for Radius parameters
Configuring Global
802.1X Settings
802.1X Settings
Select
Attempts
Click Save
Network Access
Network Access Rules
Select 802.1X Access Rules
Rules
Viewing and Configuring 802.1X Network Access Rules
„ Local EAP-TLS-EAP with TLS
Viewing and Configuring 802.1X Network Access Rules
Network Access Rule
Configuring MAC
Select MAC Access Rules
Viewing and Configuring MAC Network Access Rules
Page
Viewing Configuring WebAAA Network Access Rules
Viewing Web AAA To view Web AAA network access rules
Creating a Web AAA To create a Web AAA network access rule
Viewing and Configuring WebAAA Network Access Rules
Select Last Resort Access Rules
Viewing Configuring Last-Resort Network Access Rules
Task List panel, select Last Resort Network Access
Viewing and Configuring Last-Resort Network Access Rules
Configuring WX
Administrator
Administrator Access Rules
Select Admin Access Rules
Rule for Console Access
Rule for Telnet or SSH Access
Viewing and Configuring WX Administrator Access Rules
Support for
Configuring AAA
Users
Viewing and Configuring AAA Support for Third-Party AP Users
Proxy for a Client
Port Connected to Third-Party AP
Changing Location
Policy Rules
Policy Rules
Select Location Policy
Creating a Location To create a location policy rule
Policy Rule
Viewing and Changing Location Policy Rules
Profiles
Changing Mobility
Select Mobility Profiles
Viewing and Changing Mobility Profiles
Page
Remotely
How Remote WX Configuration Works
Drop Ship WXR100 Only
Shows the location of the Fn switch and the LED
Staged WX
„ The network plan containing the WX switches must be open
„ 3WXM must be installed and 3WXM Services must be running
3WXM Requirements
Configuration by
Switch for
Staging a WX
Enable the auto-config option
Save the configuration changes
Power off or restart the switch
Configure an IP interface on the Vlan
Configure DNS server information
Enable the MSS DNS client
WX4400# set ip dns domain examplecorp.com
WX4400# save config
Configuration with
Configured Switch
Completing its
Replacing a Switch
Reusing its
Replaced switch’s configuration
At the remote office
How Switch Replacement Works
Replacement
To enable replacement of remote switches
Enabling
To replace a switch
WX File
Document where the options are described
Options
Devices Tab
Switches in the network plan
WX File Management Options in 3WXM
Devices Tasks
Task Option Description Group
Task Task Option Group Description
Task Task Option Group
Configuration Changes
Synchronizing Local
Network
Changes
Undoing Local or To undo local or network changes
Network Changes
To immediately deploy local changes
Nonmatching
To schedule deployment of local changes
To synchronize the changes, do one of the following
To add a system image
Repository. Images are stored
To delete a system image
To immediately install an image on WX switches
To schedule installation of an image on WX switches
Rebooting WX Switches or MAP Access Points
You can use 3WXM to reboot WX switches and MAPs
To reboot WX switches and the MAPs they are managing
To reboot MAPs without rebooting the switch
Switch by 3WXM
Enabling or
Disabling
Management of a
Canceling a
Operation Log
Scheduled Operation
To display the operation log
Importing Exporting Switch Configuration Files
To import a configuration
To export a configuration
To modify configuration polling options
Modifying
Change Polling
Alerts panel
Managing WX System Images and Configurations
Changes
Toolbar Options on Verification Tab
To disable a specific instance of a warning or error
To resolve an error or warning
Select the warning or error message
To globally disable a warning or error
To change verification options
To disable or reenable a rule
Or for specific instances
Verifying Configuration Changes
„ 802.1X-EAP certificate for a WX switch
„ WebAAA certificate for a WX switch
When 3WXM connects to 3WXM Services or a WX switch,
Distributing PKS #12 files
Certificates
Processing
To process a certificate
Managing
Certificate that is stored in the 3WXM certificate store
To review certificate details
Select Tools Certificate Management
Switches
Or more WX switches
Distributing
Certificates to WX
Policies
Access the Create Policy wizard
Viewing Policies
Creating a Policy
To view policies
Changes to Switches
Feature Settings Policy
Applying Policy
Feature Categories
For This Feature Area See System Features
Wireless Features
AAA Features
Event Log
Displaying
Toolbar Options
Refreshing Event
Data
Reviewing Event
Filtering Event
To filter messages by content
Using the Event LOG
Severity
To export filtered data
Generating Reports
Configuration reports
Mobility Domain Configuration
WX Configuration
Client Errors
Generating an
Inventory Report
To generate an inventory report
Inventory Report Sections
Mobility Domain
Generating a
Report
Configuration Report
WX Configuration Report Sections
Summary Report
Details Report
Click Generate
Errors Report
„ Session Properties „ Location History
Generating a Network Usage Report
Network usage report lists network usage statistics
Summary Report
Scope is always MAP Radio and cannot be changed
Details Report
Generating a Rogue Summary Report
Click Generate
Select the language „ English „ German
Click View Work Order
Switches and shows information based on those traps
3WXM Services regularly checks the status of the network
Statistics and the event log
Accessing
To access monitored data
Requirements for
Monitoring
Using the Explore Window
Monitoring the Network
Toolbar Options in Link Display of Explore View
„ Green Up
IconDescription
Lists the options on the toolbar in the floor display
Toolbar Options in Floor Display of Explore View
Toolbar Options in Floor Display of Explore View
Monitoring the Network
Using the Explore Window
Monitoring the Network
Coverage Display Options in Explore Window
Display Option
3Com radio on the floor
To take an RF measurement
Rssi measurements RF measurement point
Using the Status
Immediately updated for the new measurement point
Summary View
Click on the new measurement point. The measurement data is
Using the Client
Monitor View
On the network
Toolbar Options in Client Monitor View
Data Displayed When a Mobility Domain or Site is Selected
That you can double-click on the arrow to change
Number of times authentication for a client failed
Data Displayed When a Switch, MAP, or Radio is Selected
Client Activity Columns When a Mobility Domain is Selected
Ssid
Activity Details for Authentication Failure
Activity Details for Association Failure
Activity Details for Authorization Failure
Peap
Activity Details for Authorization Successful
ColumnDescription
Have been collected and will be transmitted to the new
Activity Details for Client Cleared
Activity Details for Disassociation
Activity Details for Dot1x Failure
Data Displayed When a Mobility Domain is Selected
Activity Details for Roam
Data Displayed When a WX Switch, MAP, or Radio is Selected
Client Sessions Columns When a Mobility Domain is Selected
Displaying Session Details
SNR
Session Properties Columns
„ Updatedtoroam User is roaming. Session
Session Statistics Columns
Session Statistics Columns
Adding a Client to the Watch List
Clients on the watch list by MAC address
Location History Columns
Using the Client Monitor View
„ natasha@example.com
Click Next. The search results appear
Displaying the Client Watch List
Details are displayed on the following tabs
Geographical
Location On the floor To display a client’s session
Monitoring the Network
Session
Using the RF
Window
Displaying RF
RF Monitor RF Neighborhood Columns
Window
Bssid
RF Monitor Activity Log Columns
Statistics
RF Monitor Environment Columns
RF Monitor Environment Columns
RF Trends Columns
Can indicate interference from a non-802.11 device
To access performance statistics from the network
Statistics
Monitoring the Network
Accessing Realtime Performance Statistics
„ Octets In/Out „ Packets In/Out „ Errors In/Out
Viewing Current Data
Viewing Historical Data
Viewing Data in Percentages
Exporting Performance Data
To export data to a file
Monitoring the Network
Rogues
Converting a rogue into a third party AP
That truly are rogues
Rogue Detection Requirements
Snmp Notifications for RF Detection
Notification Type Description Rogue detection notifications
IDS/DoS notifications
Snmp Notifications for RF Detection
Detecting and Combatting Rogue Devices
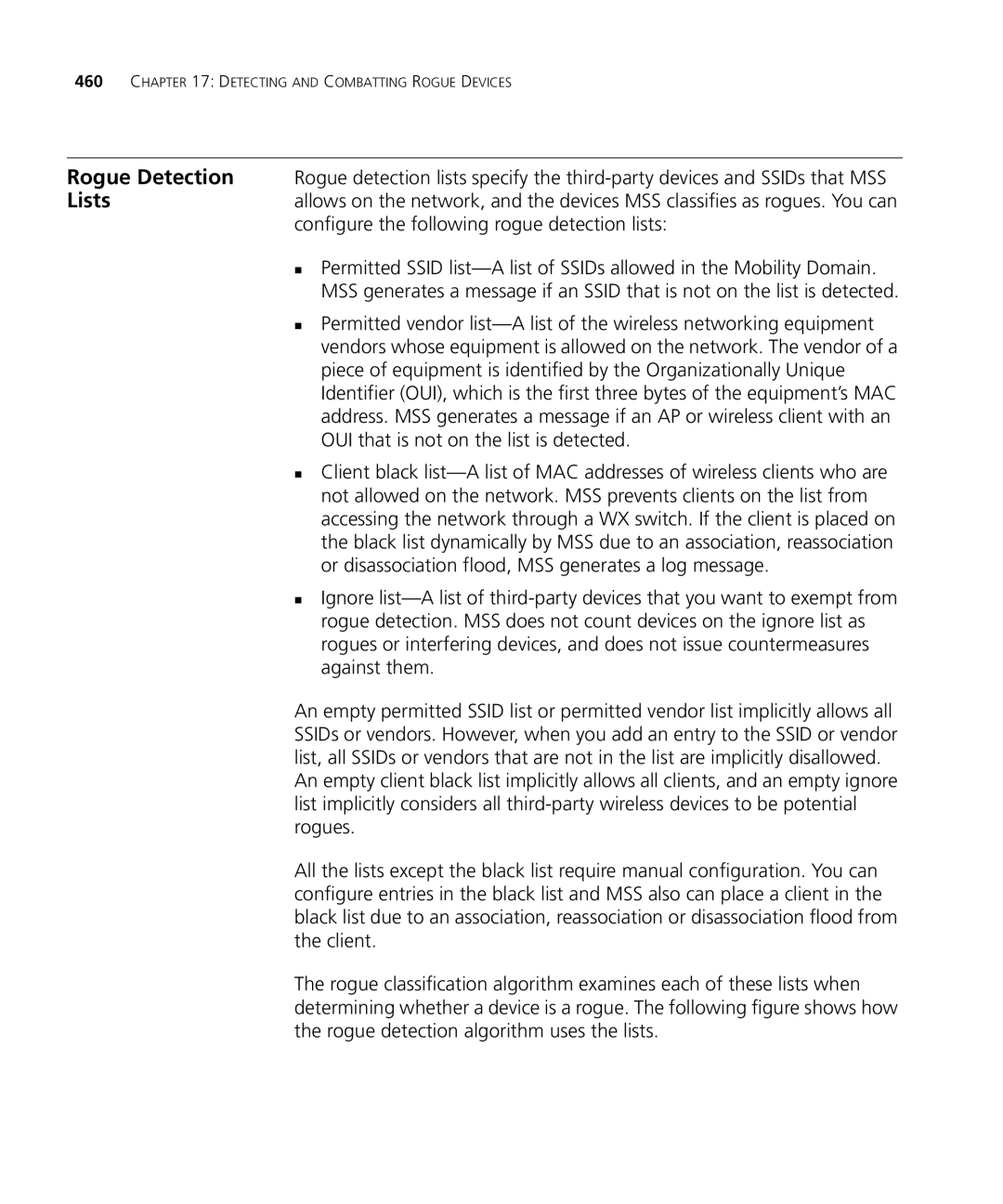
Rogue Detection Lists
Detection Screen
Using the Rogue
Main 3WXM tool bar
Toolbar Options on Rogue Detection Screen
To filter the rogue list
Current, Current Hour, Current Day, and History Tabs
Listeners Tab
Activity Log Tab
Activity Log Columns
Clients Tab
Lists the information displayed on the Clients tab
Listeners Columns
Client Columns
Displaying a
Rogue’s
Geographical
Location
Displaying a Rogue’s Geographical Location
To add a device to the ignore list
Adding a Device to
Attack List
Converting a Rogue
Into a Third Party
To display the list
To remove a third-party AP
Configuring RF
Adding a Rogue’s
Clients to the Black
List
Detecting and Combatting Rogue Devices
Importing RF
Measurements
RF obstacle data
Importing the To import the measurements
Optimizing a Network Plan
Measurements to Floor Plan
Locating and Fixing
Coverage Holes
Coverage holes by displaying coverage
Locating a Coverage To locate a coverage hole
Locating and Fixing Coverage Holes
Installed to Network Plan
Preferences Values
Resetting
Tools Preferences
Changing Network
Synchronization
Changing User Interface Options
To change network options
Within Window Style, select one of the following
Changing Tools
Certificate
Check on
Click the Certificate Handling tab
Typical Client’s Transmit Power
Changing Options
For RF Planning
You can change the following RF planning options
To Change a Color
Defining a Color from the Palette
Defining a Color by Changing HSB Properties
Defining a Color by Changing RGB Properties
Changing 3WXM Logging Options
Chapter a Changing 3WXM Preferences
Preferences
Chapter B Changing 3WXM Services Preferences
3WXM Services
Services
Starting or
Stopping
To connect to 3WXM Services
Connecting to 3WXM Services
Start 3WXM client
Verify that the service is running on the server
Data
To complete the connection
Information, and access control to 3WXM Services
Changing Service
To change service settings
WX connection settings control the timeout and retries for
Service will accept from the WX switches
Click the WXs Connection Settings tab
Changing WX
Changing WX Connection Settings
Sources of Monitor Data
Click the Monitoring Settings tab
Polling Interval is 5 minutes and cannot be changed
Https//ip-addr
Managing Network Plans
Chapter B Changing 3WXM Services Preferences
Backup
Chapter B Changing 3WXM Services Preferences
Services
Register Your
Product
Purchase
Access Software
Troubleshoot
Online
Downloads
Contact Us
Latin America Telephone Technical Support and Repair
Country Telephone Number
US and Canada Telephone Technical Support and Repair
Index
Numbers
Index
Monitors WX switch performance
Saving
SSH
Index
Index