6 | User Guide Integrated |
|
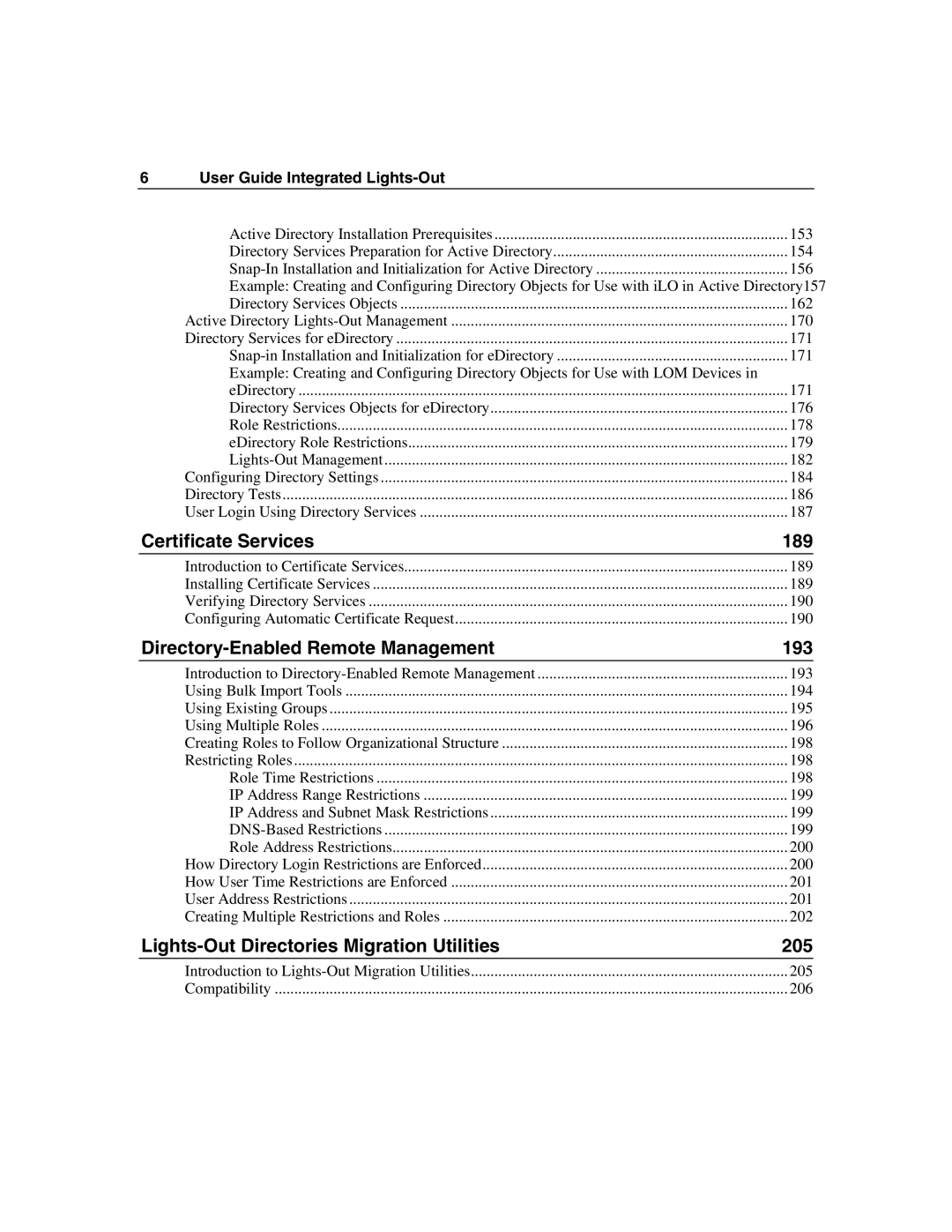
| Active Directory Installation Prerequisites | 153 |
| Directory Services Preparation for Active Directory | 154 |
| 156 | |
| Example: Creating and Configuring Directory Objects for Use with iLO in Active Directory157 | |
| Directory Services Objects | 162 |
| Active Directory | 170 |
| Directory Services for eDirectory | 171 |
| 171 | |
| Example: Creating and Configuring Directory Objects for Use with LOM Devices in |
|
| eDirectory | 171 |
| Directory Services Objects for eDirectory | 176 |
| Role Restrictions | 178 |
| eDirectory Role Restrictions | 179 |
| 182 | |
| Configuring Directory Settings | 184 |
| Directory Tests | 186 |
| User Login Using Directory Services | 187 |
Certificate Services | 189 | |
| Introduction to Certificate Services | 189 |
| Installing Certificate Services | 189 |
| Verifying Directory Services | 190 |
| Configuring Automatic Certificate Request | 190 |
| 193 | |
| Introduction to | 193 |
| Using Bulk Import Tools | 194 |
| Using Existing Groups | 195 |
| Using Multiple Roles | 196 |
| Creating Roles to Follow Organizational Structure | 198 |
| Restricting Roles | 198 |
| Role Time Restrictions | 198 |
| IP Address Range Restrictions | 199 |
| IP Address and Subnet Mask Restrictions | 199 |
| 199 | |
| Role Address Restrictions | 200 |
| How Directory Login Restrictions are Enforced | 200 |
| How User Time Restrictions are Enforced | 201 |
| User Address Restrictions | 201 |
| Creating Multiple Restrictions and Roles | 202 |
| 205 | |
| Introduction to | 205 |
| Compatibility | 206 |