Sros Command Line Interface
Publication Number
Table of Contents
CLI Introduction
Reference Guide Introduction
Command Reference GuideUnderstanding Configuration Modes
Enable
Using CLI Shortcuts
Command Reference GuidePerforming Common CLI Functions
Config-eth 0/1#ip address
Debug Undebug all
Understanding CLI Error Messages
Command Descriptions
Command Descriptions
Basic Mode Command Set
Basic Mode Command SET
Enable #configure terminal Config#enable password password
Enable
Enable
Logout
Address
Ping address
Ping
Show clock
Show snmp
Show snmp
Show version
Show version
Telnet
Telnet address
#traceroute
Traceroute address
Sros Command Line Interface Reference Guide
Enable Mode Command SET
Sros Command Line Interface Reference Guide
#clear access-list MatchAll
Clear access-list listname
Clear arp-cache
Enable #clear arp-cache
Clear arp-entry address
Enable #clear arp-entry
Clear bridge group#
Enable #clear bridge
Clear buffers max-used
Enable #clear buffers max-used
Clear counters interface
Enable #clear counters ethernet 0/1
Clear crypto ike sa policy priority
Enable #clear crypto ike sa
Clear crypto ipsec sa
Clear dump-core
Enable #clear dump-core
Clear event-history
Enable #clear event-history
Out
Clear ip bgp * as-number ip address in out soft
Soft
#clear ip bgp
#show ip igmp groups
Clear ip igmp group group-address interface
#clear ip igmp group ethernet 0/1
#clear ip igmp group #show ip igmp groups
#clear ip igmp group
Clear ip policy-sessions
Usage Examples
Enable #clear ip policy-stats MatchALL
Enable #clear ip policy-stats
Clear ip policy-stats classname entry policy class #
#clear ip prefix-list test
Clear ip prefix-list listname
#clear ip route
Clear ip route
Clear lldp counters
Enable #clear lldp counters
Clear lldp counters interface interface
Clear lldp neighbors
Enable #clear lldp neighbors
Clear pppoe interface id
Enable #clear pppoe
Clear process cpu max
Enable #clear process cpu max
Clear qos map map name
Clear qos map
#clear qos map
#clear qos map priority
Clear spanning-tree counters interface interface
Enable #clear spanning-tree counters interface eth 0/1
Interface
Enable #clear spanning-tree detected-protocols
Clock auto-correct-dst
Enable #clock auto-correct-DST
Clock no-auto-correct-dst
Enable #clock no-auto-correct-DST
Clock set time day month year
Enable #clock set 034200 22 Au
Clock timezone text
Following list shows sample cities and their timezone codes
Enable #clock timezone -4-Santiago
Configure
#copy running-config startup-config
#copy startup-config backup.bak
Copy source destination
#copy myfile.biz newfile.biz
Copy console filename
Enable #copy console config
Copy flash destination
Enable #copy flash tftp
Copy filename interface interface slot/port
Enable #copy configfile interface adsl 0/1
#copy tftp flash
Copy tftp destination
#copy xmodem flash Destination filename newfile.biz
Copy xmodem destination
#debug aaa
Debug aaa
Enable #debug access-list MatchAll
Debug access-list listname
Debug atm events
Enable #debug atm events
Debug atm oam vcd loopback end-to-end segment Llid
Enable #debug atm oam
Number
Debug atm packet interface atm vc ATM port VPI/VCI vcd vcd
#debug bridge
Debug bridge
Ike
Enable #debug crypto ipsec
Ike negotiation
Ipsec
Enable #debug backup
Debug backup
Debug dialup-interfaces
Enable #debug dialup-interfaces
Debug dynamic-dns verbose
Enable #debug dynamic-dns verbose
Verbose Turns on verbose messaging
Debug firewall
Enable #debug firewall
Events
Debug frame-relay events llc2 lmi
Llc2
Lmi
Debug frame-relay multilink interface
Enable #debug frame-relay multilnk
Enable #debug hdlc verbose
Debug hdlc errors verbose
Debug interface interface
Enable #debug interface ethernet
Debug interface adsl events
Enable #debug interface adsl events
Updates
Debug ip bgp events in out keepalives updates
In/out
Keepalives
Debug ip dhcp-client
Enable #debug ip dhcp-client
Debug ip dhcp-server
Enable #debug ip dhcp-server
Debug ip dns-client
Enable #debug ip dns-client
Debug ip dns-proxy
Enable #debug ip dns-proxy
Send
Debug ip icmp send recv
#debug ip icmp
#debug ip igmp
Debug ip igmp group-address
Debug ip ospf
#debug ip rip
Debug ip rip events
#debug ip tcp events
Debug ip tcp events
#debug ip tcp md5
Debug ip tcp md5
Debug ip udp
Enable #debug ip udp
#debug isdn events
Debug isdn events
Shows information about received packets
Debug lldp rx tx verbose
Shows information about transmitted packets
Verbose Shows detailed debugging information
Debug port-auth general packet both rx tx supp-sm
Enable #debug port-auth packet rx
General
Both
Authentication
Debug ppp authentication errors negotiation verbose
Errors
Enable #debug ppp authentication
Debug pppoe client
Enable #debug pppoe client
#debug radius
Debug radius
Debug sntp
Config
Debug spanning-tree config events general root
Root
#debug spanning-tree general
Debug spanning-tree bpdu receive transmit all
Enable #debug spanning-tree bpdu all
Receive
Transmit
Debug system
Enable #debug system
Dir
Enable #dir
#disable
Disable
#erase startup-config
Erase filename startup-config
Events
Enable #events
#logout
Cancel
Reload cancel in delay
Enable #reload
#reload cancel
#show access-lists
Show access-lists listname
Show arp
Enable #show arp
Show atm pvc traffic interface atm interface
Enable #show atm pvc interface atm
Show atm pvc Show atm pvc traffic interfaces atm interface
Pvc
Frame-relay slot/port
Enable #show bridge
#show buffers
Show buffers
Show buffers users
Enable #show buffers users
Show cflash
Enable #show cflash
Detail
Show clock detail
Show clock
#show configuration
Show configuration
Copyright 2005 Hewlett-Packard Development Company, L.P 113
#show connections
Show connections
Show crypto ca certificates crls profiles
Enable #show crypto ca certificates CA Certificate
Show crypto ike
Client configuration
Pool
Policy
Enable #show crypto ike policy Crypto IKE Policy
Transform-set
Show crypto ipsec
Port number
Show crypto map
Show debugging
Enable #show debugging
Enable #show backup interfaces Backup interfaces
Show backup interfaces
#show dialin interfaces Dialin interfaces
Show dialin interfaces
#show dynamic-dns eth 0/1
Show dynamic-dns
Show event-history
Enable #show event-history
Show flash
Enable #show flash
Show frame-relay
Enable #show frame-relay lmi
Frame-relay
#show frame-relay pvc
Active Inactive Deleted Static Local
Show frame-relay fragment frame-relay port.sublink
Enable #show frame-relay fragment
Dlci = 17 Fragment Size =
Enable #show frame-relay fragment frame-relay
Show frame-relay multilink interface detailed
Enable #show frame-relay multilink
#show hosts
Show hosts
Show interfaces interface
Enable #show interfaces t1 1/1
Total-24-hourintervals
#show interfaces dds 1/1
#show interfaces modem 1/2 modem 1/2 is UP
#show interfaces fr
Atuc
Performance statistics
Show interfaces shdsl
Performance-statistics
Total-24-hour
LOS
Enable #show interfaces shdsl 1/1
Technology Review
Enable #show ip access-lists
Show ip access-lists listname
Show ip arp
Enable #show ip arp
#show ip bgp
Show ip bgp
#show ip bgp 10.15.240.0/28
Show ip bgp network ip /length network-mask
Advertised-routes
Show ip bgp neighbors ip address
#show ip bgp neighbors 10.15.43.34 advertised-routes
#show ip bgp neighbors
Network NextHop Metric Path 0.0/8 10.15.43.17 100 0.0/9
#show dhcp-client lease
Show ip dhcp-client lease interface
#show ip dhcp-server binding
Show ip dhcp-server binding client ip address
Show ip igmp groups group-address
Enable #show ip igmp groups
Show ip igmp interface interface
Enable #show ip igmp interface eth 0/1 is UP
Show ip interfaces interface brief
Enable #show ip interfaces
Brief
#show ip mroute
Show ip mroute group-addressinterface summary
#show ip ospf
Show ip ospf
Area id
Show ip ospf database
Enable #show ip ospf database Ospf router with ID
Show ip ospf interface interface type interface number
Enable #show ip ospf interface ppp
Enable #show ip ospf neighbor
Show ip ospf summary-address
Enable #show ip ospf summary-address
Show ip policy-class policyname
Enable #show ip policy-class
Show ip policy-sessions policyname
Enable #show ip policy-sessions
Show ip policy-stats policyname
Enable #show ip policy-stats
Summary
Show ip prefix-list detail summary listname
#show ip prefix-list test ip prefix-list test 4 entries
#show ip protocols
Show ip protocols
Connected
Enable #show ip route rip
Ospf
Rip
Copyright 2005 Hewlett-Packard Development Company, L.P 165
Show ip traffic
Enable #show ip traffic IP statistics
#show lldp
Show lldp
#show lldp device Router
Show lldp device system name
#show lldp interface ethernet 0/1 eth 0/1 TX/RX
Show lldp interface interface
Show lldp neighbors interface interface detail
Copyright 2005 Hewlett-Packard Development Company, L.P 171
#show lldp neighbors statistics
Show lldp neighbors statistics
Show memory heap
Enable #show memory heap
Heap
65520 131056
#show output-startup
Show output-startup
Show port-auth supplicant interface interface id summary
Enable #show port-auth supplicant interface eth 0/2
#show pppoe ppp
Show pppoe
Show processes cpu
Enable #show processes cpu
#show qos map qos map priority map entry
Show qos map
#show qos map priority qos map priority
#show qos map interface frame-relay 1 fr
#show qos map priority 10 qos map priority
Show queue atm interface id frame-relay interface id ppp
Enable #show queue fr
Interface id
Show queuing fair
Enable #show queuing
Fair
#show radius statistics
Show radius statistics
Copyright 2005 Hewlett-Packard Development Company, L.P 185
Show sntp
Show sntp
Show spanning-tree bridgegroup#
Enable #show spanning-tree
#show startup-config
Show startup-config
Copyright 2005 Hewlett-Packard Development Company, L.P 189
#show startup-config checksum
Show startup-config checksum
#show running-config checksum
Show tcp info control block
Enable #show tcp info
Show users
Enable #show users
Enable #show version
Enable #telnet 10.200.4.15 User Access Login Password
Terminal length text
Enable #terminal length
Enable #traceroute
Undebug all
Enable #undebug all
Wall message
#wall Reboot in 5 minutes if no objections
Write erase memory network terminal
Enable #write memory
Erase
Router#configure terminal
Global Configuration Mode Command SET
Copyright 2005 Hewlett-Packard Development Company, L.P 201
Banner
Password-prompt
Fail-message
Username-prompt
None
Config#aaa authentication enable default line
Line
Groupname
None
Aaa group server radius listname
Config#aaa group server radius myServers config-sg-radius#
Aaa on
Example
Group groupname
Copyright 2005 Hewlett-Packard Development Company, L.P 208
Aaa processes threads
Config#aaa processes
Login
Banner exec login motd character message character
Exec
Motd
Bridge group# protocol ieee
Config#no bridge 17 protocol ieee
Config#boot config flash myconfig
Boot config cflash flash filename cflash flash backup file
Cflash
Flash
Config#boot system flash myimage.biz
No-backup
Config#crypto ca authenticate testCAprofile
Crypto ca authenticate name
Quit
Crypto ca certificate chain name
Crypto ca enroll name
Config#crypto ca enroll MyProfile
Crypto ca import name certificate
Config#crypto ca import MyProfile certificate
END Certificate
Crypto ca import name crl
Config#crypto ca import MyProfile crl
Crypto ca profile name
Config#crypto ca profile MyProfile
Crypto ike
Config#crypto ike policy 1 config-ike#
Local-id address
Config#crypto ike local-id address
Enable #configure terminal
Copyright 2005 Hewlett-Packard Development Company, L.P 225
Config-eth 0/1#no shutdown config-eth 0/1#exit
Asn1-dn name
Crypto ike remote-id
Domain.com
John*@domain.com
Crypto ike remote id address 10.10.10.0
Copyright 2005 Hewlett-Packard Development Company, L.P 229
Syntax Description
Crypto ipsec transform-set setname parameters
Copyright 2005 Hewlett-Packard Development Company, L.P 231
Ipsec-ike
Crypto map
Ipsec-manual
Config#crypto map testMap 10 ipsec-ike
Md5
Enable password md5 password
Event-history on
Config#event-history on
Error
Event-history priority error fatal info notice warning
Info
Fatal
Config#event-history priority info
Config#ftp authentication MyList
Ftp authentication listname
Config#ftp authentication default
Hostname name
Config#hostname Atlrtr
Interface port-type slot/port
Config#interface serial 1/1
Point-to-point
Interface frame-relay label point-to-point
Config#interface fr
Config#bind 5 t1 1/1 9 fr
Config-hdlc 7#ip address 193.44.69.1
Config#interface hdlc
Interface hdlc label
Config#bind 5 t1 1/1 9 hdlc
Interface loopback label
Config#interface loopback
Config-ppp 7#ip address 193.44.69.1
Config#interface ppp
Interface ppp label
Config#bind 5 t1 1/1 9 ppp
Interface tunnel id
Config#interface tunnel 1 config-tunnel 1#
Ip access-list extended listname
Port list
Any
Discard Port
Pim-auto-rp
Destination ip
Netbios-dgm Port 138 netbios-ns Port 137 netbios-ss Port
Range 0 to
Copyright 2005 Hewlett-Packard Development Company, L.P 254
Allow list access list names
Copyright 2005 Hewlett-Packard Development Company, L.P 256
Ip access-list standard listname
Remark
Config#ip access-list standard MatchAll
Log
Permit or deny any
Copyright 2005 Hewlett-Packard Development Company, L.P 259
Lost
Ip classless
Ip crypto
Config#no ip routing Config#ip default gateway
Ip default-gateway ip address
Ip dhcp-server excluded-address start ip end ip
Ip dhcp-server ping packets #packets
Config#ip dhcp-server ping packets
Config#ip dhcp-server ping timeout
Ip dhcp-server ping timeout milliseconds
Ip dhcp-server pool name
Config#ip dhcp-server pool Sales
Ip domain-lookup
Config#ip domain-lookup
Ip domain-name name
Config#ip domain-name procurve
Ip domain-proxy
Config#ip domain-proxy
Security data processing will be attempted
Ip firewall
Config#ip firewall
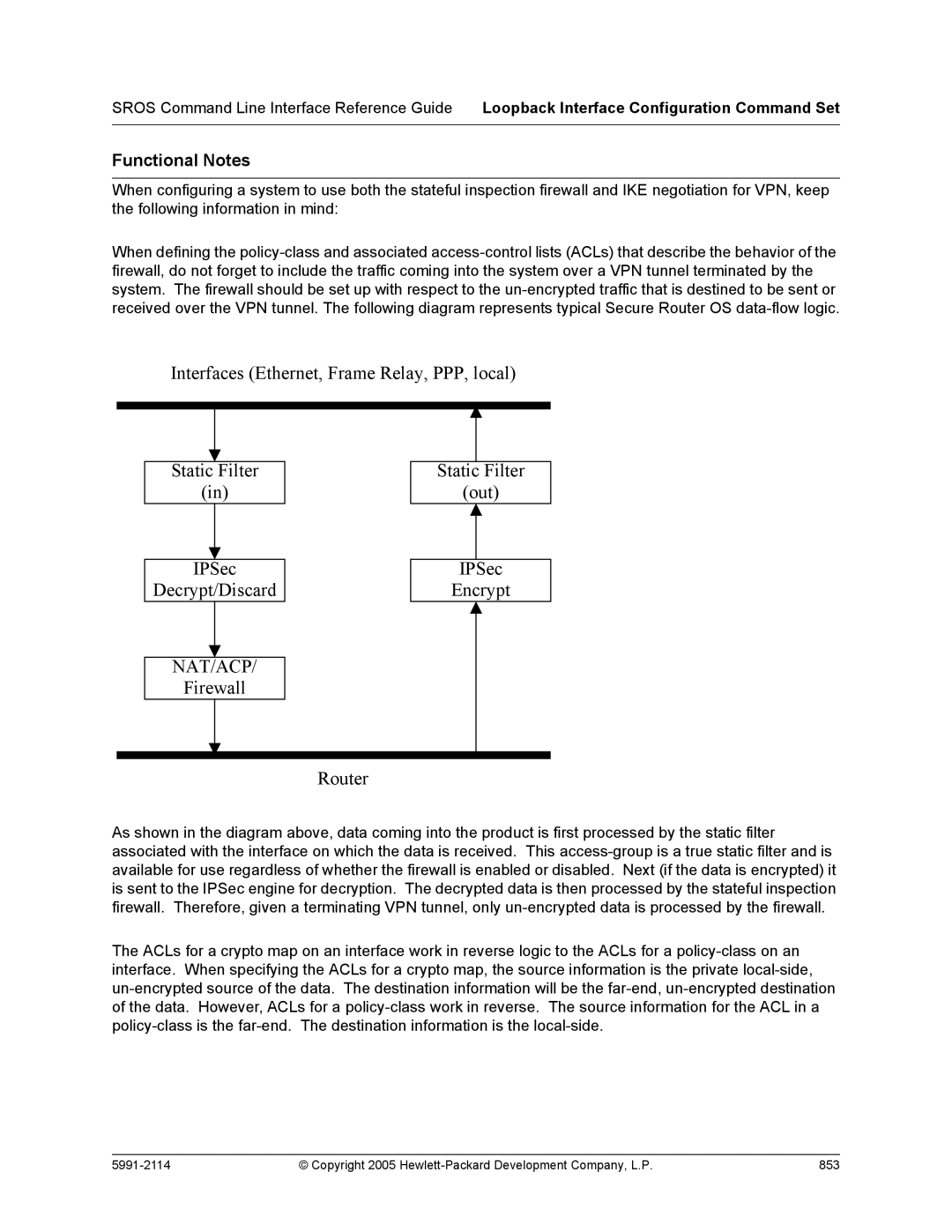
Packet Flow
Concepts
Attack Protection
Attacks that send TCP URG Yes
Application Specific Processing
Ip firewall alg ftp pptp sip
Config#no ip firewall alg ftp
Ip firewall check reflexive-traffic
Config#ip firewall check reflexive-traffic
Ip firewall attack-log threshold value
Config#ip firewall attack-log threshold
Ip firewall check syn-flood
Config#ip firewall check syn-flood
Ip firewall check winnuke
Config#ip firewall check winnuke
Ip firewall policy-log threshold value
Config#ip firewall policy-log threshold
Ip forward-protocol udp port number
Copyright 2005 Hewlett-Packard Development Company, L.P 284
Ip ftp access-class policyname
Ip ftp agent
Ip ftp source-interface interface
Config#ip ftp source-interface loopback
Ip host name address1
Config#ip host mac 10.2.0.2 config#ip host dal
Ip igmp join group-address
Config#ip igmp join
Ip mcast-stub helper-address ip address
Config#ip mcast-stub helper-address
Ip multicast-routing
Config#ip name-server 172.341.1.111
Max-sessions
Ip policy-class policyname max-sessions number
Copyright 2005 Hewlett-Packard Development Company, L.P 294
Copyright 2005 Hewlett-Packard Development Company, L.P 295
Allports
Ip policy-timeoutprotocol range port seconds
Ftp-data Port
Copyright 2005 Hewlett-Packard Development Company, L.P 298
Description
Ip prefix-list listname description text
Deny
Config#ip prefix-list test seq 10 permit 0.0.0.0/0 le
Ip radius source-interface interface
Config#ip radius source-interface ethernet 0/1
Ip route ip address subnet mask interface or ip address
Ip routing
Ip snmp agent
Config#ip snmp agent
Ip sntp source-interface interface
Config#ip sntp source-interface loopback
Ip subnet-zero
Config#ip subnet-zero
Ip tftp source-interface interface
Config#ip tftp source-interface loopback
Console
Line console telnet line-number ending number
Config#line telnet 0 4 config-telnet0-4#
Config#line console 0 config-con0#
Minimum-transmit-interval
Reinitialization-delay
Transmit-interval
Ttl-multiplier
Config#lldp reinitialization-delay
Config#lldp minimum-transmit-interval
Config#lldp transmit-interval
Config#lldp transmit-interval 15 config#lldp ttl-multiplier
Logging console
Logging email address-listemail address email address
Logging email on
Config#logging email on
Config#logging email priority-level warning
Logging email priority-level error fatal info notice warning
Logging email receiver-ip ip address
Config#logging email receiver-ip
Logging email sender
Logging email source-interface interface
Config#logging email source-interface loopback
Logging facility facility type
Logging forwarding on
Config#logging forwarding priority-level warning
Logging forwarding receiver-ip ip address
Config#logging forwarding receiver-ip
Logging forwarding source-interface
Config#logging forwarding source-interface loopback
Mac address-table aging-time aging time
Config#mac address-table aging-time
Interface
Qos map mapnamesequence number
Copyright 2005 Hewlett-Packard Development Company, L.P 327
Radius-server
Enable-username name
Challenge-noecho
Deadtime minutes
Copyright 2005 Hewlett-Packard Development Company, L.P 329
Acct-port1813 Auth-port1812
Radius-server host
Router ospf
Config#router ospf config-ospf#
Router rip
Config#router rip config-rip#
Copyright 2005 Hewlett-Packard Development Company, L.P 333
Snmp-server chassis-id id string
Listname
Snmp-server community community view viewname ro rw
Snmp-server contact string
Config#snmp-server contact Network Administrator
Config#snmp-server enable traps snmp
Snmp-server enable traps trap type
Snmp-server host address traps community trap type
Config#snmp-server host 190.3.44.69 traps My Community snmp
Copyright 2005 Hewlett-Packard Development Company, L.P 339
Snmp-server location string
Config#snmp-server location 5th Floor Network Room
Snmp-server management-url URL
Snmp-server management-url-label label
Config#snmp-server management-url-label watch
Snmp-server source-interface interface
Config#snmp-server source-interface ethernet 0/1
Snmp-server view view-name oidtree excluded included
Config#snmp-server view block 1.3.6.1.2.1.2. included
Config#sntp server time.nist.gov version
Config#sntp server time.nist.gov
Sntp server address or hostname version
Config#spanning-tree bpduguard default
Spanning-tree bpduguard default
Config#spanning-tree edgeport bpdufilter default
Spanning-tree edgeport bpdufilter default
Spanning-tree forward-time seconds
Spanning-tree hello-time seconds
Spanning-tree max-age seconds
Config#spanning-tree max-age
Config#spanning-tree mode rstp
Spanning-tree mode rstp stp
Rstp
Stp
Spanning-tree pathcost method short long
Config#spanning-tree pathcost method long
Spanning-tree priority value
Config#spanning-tree priority
Config#username procurve password procurve
Username username password password
Dhcp Pool Command Set
Dhcp Pool Command SET
Client-id
Client-identifier identifier
Fecn Becn
Client-name name
Default-routeraddress secondary
Dns-serveraddress secondary
Domain-name domain
Ieee802
Hardware-addresshardware-address type
Copyright 2005 Hewlett-Packard Development Company, L.P 363
Host address subnet mask or prefix length
Config#ip dhcp-server pool MyPool config-dhcp#lease 0
Config#ip dhcp-server pool MyPool config-dhcp#lease
Config#ip dhcp-server pool MyPool config-dhcp#lease 0 0
Lease days hours minutes
Netbios-name-serveraddress secondary
Config-dhcp#netbios-node-type
Netbios-node-type type
Network address subnet mask or prefix length
Ntp-serverip address
Config#ip dhcp-server pool MyPool config-dhcp#ntp-server
Hex
Option option value ascii hex ip value
Tftp-server server
Config#ip dhcp-server pool MyPool config-dhcp#tftp-server
Timezone-offset offset
IKE Policy Command Set
IKE Policy Command SET
Attribute policynumber
Client authentication host
Config-ike#client authentication host xauth-type radius
Client authentication host xauth-type generic otp radius
Config-ike#client authentication server list clientusers
Client authentication server list listname
Config-ike#client configuration pool ConfigPool
Client configuration pool poolname
Main
Initiate main aggressive
Aggressive
Local-id address asn1-dn fqdn user-fqdnipaddress or name
Config-ike#local-id address fqdn user-fqdn ipaddress or fqdn
Copyright 2005 Hewlett-Packard Development Company, L.P 381
Following example disables version 2 on Ike policy
Nat-traversal version allow disable force
Config-ike#respond anymode
Config#crypto ike policy
Peer ip address any
Copyright 2005 Hewlett-Packard Development Company, L.P 384
Respond main aggressive anymode
Config-ike#respond anymode config-ike#initiate main
IKE Policy Attributes Command Set
IKE Policy Attributes Command SET
Config-ike-attribute#authentication pre-share
Authentication dss-sig pre-share rsa-sig
Dss-sig
Pre-share
Aes-128-cbc aes-192-cbc aes-256-cbc des 3des
Encryption aes-xxx-cbc des 3des
Group 1
Hash md5 sha
Lifetime seconds
IKE Client Command Set
IKE Client Command SET
Dns-serveraddress1 address2
Config-ike-client-pool#dns-server 172.1.17.1
Ip-rangestart ip end ip
Config-ike-client-pool#ip-range 172.1.1.1
Config-ike-client-pool#netbios-name-server 172.1.17.1
Netbios-name-serveraddress1 address2
Crypto Map IKE Command Set
Crypto MAP IKE Command SET
Antireplay
Ike-policypolicy number
Match address listname
Config#ip access-list extended NewList
Copyright 2005 Hewlett-Packard Development Company, L.P 400
Set peer address
Config-crypto-map#set peer
Group1
Set pfs group1 group2
Group2
Set security-association lifetime kilobytes seconds value
Set transform-setsetname1 setname6
Config#crypto ipsec transform-set Set1 esp-3des esp-sha-hmac
Crypto MAP Manual Command SET
Copyright 2005 Hewlett-Packard Development Company, L.P 406
Copyright 2005 Hewlett-Packard Development Company, L.P 407
Copyright 2005 Hewlett-Packard Development Company, L.P 408
Copyright 2005 Hewlett-Packard Development Company, L.P 409
Address Enter the IP address of the peer device
Set session-key inbound outbound
Authenticator
Inbound
Outbound
Copyright 2005 Hewlett-Packard Development Company, L.P 412
74686973206973206D7920636970686572206B6579
Gateway
Set transform-set setname
Radius Group Command Set
Radius Group Command SET
Server acct-port port number auth-port port number
CA Profile Configuration Command Set
CA Profile Configuration Command SET
Crl optional
Ca-profile#email address joesmith@company.com
Email address email address
100
Enrollment retry count period
Ca-profile#enrollment terminal
Enrollment terminal
Enrollment url url
Ca-profile#fqdn company.com
Fqdn fqdn
Ca-profile#ip-address
Ip-address address
Ca-profile#password procurve
Password password
Serial-number
Ca-profile#subject-name cert
Subject-name name
Certificate Configuration Command Set
Certificate Configuration Command SET
Certificate serial-number
Certificate ca serial-number
Config-cert-chain#no certificate ca
Crl
Ethernet Interface Configuration Command Set
Ethernet Interface Configuration Command SET
Access-policy policyname on
Full-duplexon page 448 half-duplexon
Policyname
Access-policy policyname
Associate the access policy with the Ethernet 0/1 interface
Copyright 2005 Hewlett-Packard Development Company, L.P 438
Arp arpa
Config#interface eth 0/1 config-eth 0/1#arp arpa
Bandwidth value
Config#interface eth 0/1
Bridge-group group#
Config#interface eth 0/1 config-eth0/1#bridge-group
Crypto map mapname
NAT/ACP
Copyright 2005 Hewlett-Packard Development Company, L.P 444
Dynamic-dns dyndns dyndns-custom dyndns-static hostname
Username password
Config-atm1.1#dynamic-dns dyndns-custom host user pass
Encapsulation 802.1q
Full-duplex
Config#interface ethernet 0/1
Half-duplex
Ip access-group listname in out
Ip address dhcp
Dlci high order Dlci lower
Config#interface eth 0/1 config-eth 0/1#ip address dhcp
Secondary
Ip address address mask secondary
Ip dhcp release
Ip dhcp renew
Ip helper-address address
Copyright 2005 Hewlett-Packard Development Company, L.P 458
Ip igmp
Copyright 2005 Hewlett-Packard Development Company, L.P 460
Ip mcast-stub downstream
Config-eth 0/1#ip mcast-stub downstream
Ip mcast-stub upstream
Config-eth 0/1#ip mcast-stub upstream
Ip ospf
Config-eth 0/1#ip ospf authentication null
Ip ospf authentication message-digest null
Message-digest
Null
Ip ospf network broadcast point-to-point
Config-eth 0/1#ip ospf network broadcast
Broadcast
Point-to-point
Ip proxy-arp
Ip rip receive version version
Ip rip send version version
Ip route-cache
Ip unnumbered interface
Lldp receive
Config-eth 0/1#lldp send-and-receive
Mac-address address
Mtu size
Config#interface eth 0/1 config-eth 0/1#mtu
Username username
Snmp trap
Config#interface eth 0/1 config-eth 0/1#snmp trap
Snmp trap link-status
Spanning-tree bpdufilter enable disable
Spanning-tree bpduguard enable disable
Spanning-tree cost cost value
Config#interface eth 0/1 Config-eth0/1#spanning-tree cost
Spanning-tree edgeport
Auto
Spanning-tree link-type auto point-to-point shared
Shared
Spanning-tree port-priority priority level
Speed 10 100 auto
Config#interface ethernet 0/1 config-eth 0/1#speed
Mb Ethernet
Native
Vlan-id vlan id native
DDS Interface Configuration Command Set
DDS Interface Configuration Command SET
Clock rate rate
Config#interface dds 1/1
Clock source option
Config#interface dds 1/1 config-dds 1/1#clock source line
Data-coding scrambled
Loopback dte line remote
Config#interface dds 1/1 config-dds 1/1#loopback line
Dte
Remote
Remote-loopback
Config#interface dds 1/1 config-dds1/1#remote-loopback
Config#interface dds 1/1 config-dds 1/1#snmp trap
Copyright 2005 Hewlett-Packard Development Company, L.P 493
Router#configure terminal Routerconfig#interface serial 1/1
Serial Interface Configuration Command SET
Et-clock-source source
Ignore dcd
Config#interface serial 1/1 config-ser 1/1#ignore dcd
Invert etclock
Invert rxclock
Config#interface serial 1/1 config-ser 1/1#invert rxclock
Invert txclock
Serial-mode mode
Shutdown
Config#interface serial 1/1 config-ser 1/1#shutdown
Config#interface serial 1/1 config-ser 1/1#snmp trap
Config-ser 1/1#no snmp trap link-status
T1 Interface Configuration Command Set
T1 Interface Configuration Command SET
Clock source internal line through through t1 interface id
Config#interface t1 1/1 Config-t1 1/1#clock source line
Internal
Through
Coding ami b8zs
Config#interface t1 1/1 config-t1 1/1#coding ami
Fdl ansi att none
Config#interface t1 1/1
D4 superframe format SF
Framing d4 esf
Esf Extended SF
Lbo long value
Config#interface t1 1/1 config-t1 1/1#lbo long
Lbo short value
Config#interface t1 1/1 config-t1 1/1#lbo short
T1 Network Interface
Loopback network line payload
Fdl
Loopback remote line fdl inband
Inband
Loopback remote payload
Rai
Remote-alarm rai
Config#interface t1 1/1 config-t11/1#remote-loopback
Show test-pattern
Config-t1 1/1#show test-pattern Qrss Errored Seconds
Copyright 2005 Hewlett-Packard Development Company, L.P 517
Timeslots
Tdm-group group number timeslots 1-24speed 56
Test-pattern ones zeros clear insert p215 p220 p511 qrss
Router#configure terminal Routerconfig#interface t1 1/2
DSX-1 Interface Configuration Command SET
Config#interface t1 1/2 config-t1 1/2#coding ami
Esf Extended superframe format
Config#interface t1 1/2 config-t1 1/2#framing d4
Line-length value
Config#interface t1 1/2 config-t11/2#line-length
Copyright 2005 Hewlett-Packard Development Company, L.P 524
Loopback remote line inband
Config#interface t1 1/2 config-t11/2#remote-loopback
Message-oriented
Signaling-mode message-oriented none robbed-bit
Robbed-bit
Copyright 2005 Hewlett-Packard Development Company, L.P 528
Test-pattern ones zeros
Config#interface t1 1/2 config-t11/2#test-pattern ones
Ones Generate continous ones Zeros Generate continous zeros
E1 Interface Configuration Command Set
E1 Interface Configuration Command SET
Clock source internal line through
Config#interface e1 1/1 config-e1 1/1#clock source line
Coding ami hdb3
Config#interface e1 1/1 config-e1 1/1#coding ami
Ami
Hdb3
Framing crc4
Config#interface e1 1/1
Crc4
Loop-alarm-detect
Loopback network line
Config#interface e1 1/1 Config-e1 1/1#loopback network line
Loopback remote
Ais
Remote-alarm rai ais
Config-interface# Interface configuration mode
Sa4tx-bit 0
Config#interface e1 1/1 config-e11/1#sa4tx-bit
Config-e1 1/1#show test-pattern Qrss Errored Seconds
Copyright 2005 Hewlett-Packard Development Company, L.P 541
Tdm-group group number timeslots 1-31speed 56
Test-pattern ones zeros clear insert p215 p220 p511
Config#interface e1 1/1 config-e11/1#test-pattern ones
Ts16
Config#interface e1 1/1 config-e1 1/1#ts16
Interface Configuration Command set
Interface Configuration Command SET
Config#interface e1 1/2 config-e1 1/2#coding ami
Config#interface e1 1/2
Config#interface e1 1/2 Config-e1 1/2#loopback network line
Copyright 2005 Hewlett-Packard Development Company, L.P 549
511
Config#interface e1 1/2 config-e11/2#test-pattern ones
Show
Show qrss
Config#interface e1 1/2 config-e1 1/2#ts16
Router#configure terminal Routerconfig#interface modem 1/2
Modem Interface Configuration Command SET
Caller-id override always number if-no-cid number
Dialin
Config#interface modem 1/2 config-modem 1/2#dialin
Modem countrycode countryname
BRI Interface Configuration Command set
BRI Interface Configuration Command SET
Config#interface bri 1/2 Config-bri 1/2#bonding txadd-timer
Bonding txadd-timer seconds
Bonding txcid-timer seconds
Config#interface bri 1/2 Config-bri 1/2#bonding txdeq-timer
Bonding txdeq-timer seconds
Bonding txfa-timer seconds
Config#interface bri 1/2 Config-bri 1/2#bonding txinit-timer
Bonding txinit-timer seconds
Bonding txnull-timer seconds
Copyright 2005 Hewlett-Packard Development Company, L.P 563
Isdn spid1 spid ldn
Isdn spid2 spid ldn
Typebasic-ni
Isdn switch-type type
Frame Relay Interface Config Command SET
Config#interface frame-relay 1 config-fr 1#bandwidth
Encapsulation frame-relay ietf
Fair-queue threshold
Config#interface frame-relay
Dce
Frame-relay intf-type type
Frame-relay lmi-n391dce polls
Frame-relay lmi-n391dte polls
Frame-relay lmi-n392dce threshold
Frame-relay lmi-n392dte threshold
Frame-relay lmi-n393dce counter
Frame-relay lmi-n393dte counter
Frame-relay lmi-t391dte seconds
Frame-relay lmi-t392dce seconds
Ansi
Frame-relay lmi-type type
Cisco
Q933a
Functional Note
Following example specifies Class B operation
Hold-queue queue size out
Config#interface frame-relay 1 config-fr1#hold-queue
Qos-policy out mapname
Config-fr 1#snmp trap
Copyright 2005 Hewlett-Packard Development Company, L.P 586
Spanning-tree commands begin on
Frame Relay SUB-INTERFACE Config Command SET
Copyright 2005 Hewlett-Packard Development Company, L.P 588
Create the access list this is the packet selector
Copyright 2005 Hewlett-Packard Development Company, L.P 590
Backup auto-backup
Backup auto-restore
Config#interface atm Config-atm 1.1#backup backup-delay
Backup backup-delay seconds
Backup call-mode role
Sample config for central router dialing
Ip address 10.1.1.1 255.255.255.252 backup call-mode answer
Config#interface atm Config-atm 1.1#backup connect-timeout
Backup connect-timeout seconds
Backup force state
Config#interface frame-relay 1.7 config-fr 1.7#bandwidth
Config-fr 1.16#bridge-group
Copyright 2005 Hewlett-Packard Development Company, L.P 601
Copyright 2005 Hewlett-Packard Development Company, L.P 602
Following enables automatic backup on the endpoint
Copyright 2005 Hewlett-Packard Development Company, L.P 604
Copyright 2005 Hewlett-Packard Development Company, L.P 605
Roleoriginate-answer
Copyright 2005 Hewlett-Packard Development Company, L.P 607
Copyright 2005 Hewlett-Packard Development Company, L.P 608
Config#interface fr Config-fr 1.16#backup connect-timeout
Config#interface fr Config-fr 1.16#backup force backup
Copyright 2005 Hewlett-Packard Development Company, L.P 611
Usage Examples
Frame-relay bc committed burst value
Config#interface fr Config-fr1.1#frame-relay bc
Frame-relay be excessive burst value
Config#interface fr Config-fr1.1#frame-relay be
Frame-relay fragment threshold
Frame-relay interface-dlci dlci
Config#interface fr Config-fr1.16#frame-relay interface-dlci
Out
Identifier
Address assigned to ethernet 0/1 is used in this field
Hostname
Hostname command
Copyright 2005 Hewlett-Packard Development Company, L.P 621
Ip dhcp release renew
Copyright 2005 Hewlett-Packard Development Company, L.P 623
Copyright 2005 Hewlett-Packard Development Company, L.P 624
2x the query-interval value
Copyright 2005 Hewlett-Packard Development Company, L.P 626
Config-fr 1.16#ip mcast-stub downstream
Page
Copyright 2005 Hewlett-Packard Development Company, L.P 629
Config-fr 1.16#ip ospf authentication null
Config-fr 1.16#ip ospf network broadcast
Following enables proxy-arp on the Frame Relay sub-interface
Copyright 2005 Hewlett-Packard Development Company, L.P 633
Copyright 2005 Hewlett-Packard Development Company, L.P 634
Ip route-cache address
Copyright 2005 Hewlett-Packard Development Company, L.P 636
Size
By default, this command is set to disable
Enable Enable the Bpdu block Disable Disable the Bpdu block
Spanning-tree edgeport disable
By default, a port is set to auto
Spanning-tree path-cost value
Value 128
ATM Interface Config Command Set
ATM Interface Config Command SET
Config#interface atm
Config#interface atm Config-atm 1#no snmp trap link-status
Router#configure terminal Routerconfig#interface atm
ATM SUB-INTERFACE Config Command SET
Copyright 2005 Hewlett-Packard Development Company, L.P 648
Use ip protocol to be route bridged
Atm routed-bridged ip
Config#interface atm Config-atm1.1#access-policy UnTrusted
Copyright 2005 Hewlett-Packard Development Company, L.P 651
Copyright 2005 Hewlett-Packard Development Company, L.P 652
Copyright 2005 Hewlett-Packard Development Company, L.P 653
Copyright 2005 Hewlett-Packard Development Company, L.P 654
Copyright 2005 Hewlett-Packard Development Company, L.P 655
Copyright 2005 Hewlett-Packard Development Company, L.P 656
Copyright 2005 Hewlett-Packard Development Company, L.P 657
Copyright 2005 Hewlett-Packard Development Company, L.P 658
Copyright 2005 Hewlett-Packard Development Company, L.P 659
Config#interface atm 1.1 config-atm 1.1#bandwidth
Config#interface atm 1.1 config-atm1.1#bridge-group
Copyright 2005 Hewlett-Packard Development Company, L.P 662
Copyright 2005 Hewlett-Packard Development Company, L.P 663
See Functional Notes, below, for argument descriptions
Copyright 2005 Hewlett-Packard Development Company, L.P 665
Encapsulation aal5mux aal5snap
Config-atm 1.1#encapsulation aal5snap
Encapsulation aal5mux ip ppp encapsulation aal5snap
Copyright 2005 Hewlett-Packard Development Company, L.P 667
Copyright 2005 Hewlett-Packard Development Company, L.P 668
Copyright 2005 Hewlett-Packard Development Company, L.P 669
Host name
MAC Address assigned to ethernet 0/1 is used in this field
Config#interface atm 1.1 config-atm 1.1#ip address dhcp
Copyright 2005 Hewlett-Packard Development Company, L.P 673
Config#interface atm 1.1 config-atm 1.1#ip dhcp release
Copyright 2005 Hewlett-Packard Development Company, L.P 675
Copyright 2005 Hewlett-Packard Development Company, L.P 676
Copyright 2005 Hewlett-Packard Development Company, L.P 677
Copyright 2005 Hewlett-Packard Development Company, L.P 678
Config-atm 1.1#ip mcast-stub downstream
Ip mcast-stub helper-enable
Page
Copyright 2005 Hewlett-Packard Development Company, L.P 682
Config-atm 1.1#ip ospf authentication null
Config-atm 1.1#ip ospf network broadcast
Config#interface atm 1.1 config-atm 1.1#ip proxy-arp
Copyright 2005 Hewlett-Packard Development Company, L.P 686
Copyright 2005 Hewlett-Packard Development Company, L.P 687
Config#interface atm 1.1 config-atm 1.1#ip route-cache
Copyright 2005 Hewlett-Packard Development Company, L.P 689
Config-atm 1.1#mtu
Oam-pvc managed frequency
Config#interface atm 1.1 config-atm1.1#oam-pvc manage
Oam retry up-count down-count retry-frequency
Config#interface atm 1.1 config-atm 1.1#oam retry 2 2
Pvc VPI/VCI
Config#interface atm 1.1 config-atm 1.1#pvc 8/35
Mapnamesequence number on page 326 for more information
Copyright 2005 Hewlett-Packard Development Company, L.P 695
Copyright 2005 Hewlett-Packard Development Company, L.P 696
Copyright 2005 Hewlett-Packard Development Company, L.P 697
Copyright 2005 Hewlett-Packard Development Company, L.P 698
Config#interface atm Config-atm1.1#spanning-tree path-cost
Spanning-tree port-priority value
Adsl Interface Config Command Set
Adsl Interface Config Command SET
Retrain
Snr-margin showtime monitor training monitor margin
Config-adsl0/1#snr-margin showtime monitor
Showtime monitor
Training monitor
Specifies Ansi splitterless mode
Specifies Ansi full rate mode
Config-adsl0/1#training-mode T1.413
Training-mode G.DMT G.LITE Multi-Mode T1.413
BGP Configuration Command Set
BGP Configuration Command SET
Bgp fast-external-fallover
Config-bgp#bgp fast-external-fallover
Bgp log-neighbor-changes
Config-bgp#bgp log-neighbor-changes
Bgp router-id ip address
Config-bgp#bgp router-id
Distance bgp external internal local
Config-bgp#distance bgp 30 200
Config-bgp#hold-timer
Hold-timer hold time
BGP Neighbor Configuration Command Set
BGP Neighbor Configuration Command SET
Advertisement-interval seconds
Config-bgp-neighbor#advertisement-interval
Ebgp-multihop hop count
By default, the hold time is 90 seconds
PPP Interface Configuration Command SET
Mtu size on Peer default ip address address on
Config#interface ppp Config-ppp1#access-policy UnTrusted
Copyright 2005 Hewlett-Packard Development Company, L.P 718
Copyright 2005 Hewlett-Packard Development Company, L.P 719
Alias linktext
Config#interface ppp 1 config-ppp 1#bandwidth
Multiple binds
This Step is only Valid for T1 Interfaces
Copyright 2005 Hewlett-Packard Development Company, L.P 724
Config#interface ppp 1 config-ppp1#bridge-group
Bridge-group group# bpdufilter enable disable
Bridge-group group# bpduguard enable disable
Config#interface ppp Config-ppp1#bridge-group 1 edgeport
Bridge-group group# edgeport disable
Bridge-group group# link-type auto point-to-point shared
Bridge-group group# spanning-disabled
Copyright 2005 Hewlett-Packard Development Company, L.P 731
Config-ppp 1#crypto map MyMap
Copyright 2005 Hewlett-Packard Development Company, L.P 733
Copyright 2005 Hewlett-Packard Development Company, L.P 734
Config#interface ppp Config-ppp 1#backup backup-delay
Sample config for remote router dialing out
Copyright 2005 Hewlett-Packard Development Company, L.P 737
Copyright 2005 Hewlett-Packard Development Company, L.P 738
Dialing
Dialing Out
Config#interface ppp Config-ppp 1#backup connect-timeout
State Selects the forced backup state of the link
Copyright 2005 Hewlett-Packard Development Company, L.P 742
Copyright 2005 Hewlett-Packard Development Company, L.P 743
Config-ppp 1#fair-queue
Config#interface ppp 1 config-ppp1#hold-queue
Copyright 2005 Hewlett-Packard Development Company, L.P 746
Ip address negotiated
Copyright 2005 Hewlett-Packard Development Company, L.P 748
Copyright 2005 Hewlett-Packard Development Company, L.P 749
Copyright 2005 Hewlett-Packard Development Company, L.P 750
Copyright 2005 Hewlett-Packard Development Company, L.P 751
Copyright 2005 Hewlett-Packard Development Company, L.P 752
Config-ppp 1#ip mcast-stub downstream
Config-ppp 1#ip mcast-stub upstream
Copyright 2005 Hewlett-Packard Development Company, L.P 755
Config-ppp 1#ip ospf authentication null
Config-ppp 1#ip ospf network broadcast
By default, proxy-arp is enabled
Copyright 2005 Hewlett-Packard Development Company, L.P 759
Version Specifies the RIP version
Config-ppp 1#ip route-cache
Copyright 2005 Hewlett-Packard Development Company, L.P 762
Keepalive seconds
Config#interface ppp 1 config-ppp 1#mtu
Config#interface ppp Config-ppp 1#peer default ip address
Peer default ip address address
Defining PAP
Ppp authentication protocol
Defining Chap
Peerconfig-ppp 1#ppp pap sent-username farend password same
Peerconfig-ppp 1#username Local password same
Both ends must have identical passwords
Peerconfig-ppp 1#ppp chap password different
Ppp chap hostname hostname
Config#interface ppp Config-ppp 1#ppp chap hostname myhost
Ppp chap password password
Ppp multilink
Ppp pap sent-username username password password
Pppoe ac-name name
Pppoe service-name name
Config#interface ppp Config-ppp1#qos-policy out Voicemap
Config#interface ppp Config-ppp 1#no snmp trap link-status
Tunnel Configuration Command Set
Tunnel Configuration Command SET
Router#configure terminal Routerconfig#interface tunnel
Copyright 2005 Hewlett-Packard Development Company, L.P 779
Config#ip policy-class UnTrusted
Copyright 2005 Hewlett-Packard Development Company, L.P 781
Bandwidth
Config#interface tunnel 1 config-tunnel 1#bandwidth
Refer to Functional Notes below for argument descriptions
Copyright 2005 Hewlett-Packard Development Company, L.P 784
Copyright 2005 Hewlett-Packard Development Company, L.P 785
Copyright 2005 Hewlett-Packard Development Company, L.P 786
Copyright 2005 Hewlett-Packard Development Company, L.P 787
Copyright 2005 Hewlett-Packard Development Company, L.P 788
Leave-group message Igmp Version 2, the router sends a
Copyright 2005 Hewlett-Packard Development Company, L.P 790
Copyright 2005 Hewlett-Packard Development Company, L.P 791
Copyright 2005 Hewlett-Packard Development Company, L.P 792
Following example sets the helper address as the Igmp proxy
Copyright 2005 Hewlett-Packard Development Company, L.P 794
Cost value
Command Reference GuideTunnel Configuration Command Set
Copyright 2005 Hewlett-Packard Development Company, L.P 796
Optional. Selects message-digest authentication type
Sets the network type for broadcast
Ip proxy-arpip address subnet mask
Config#interface tunnel 1 config-tunnel 1#ip proxy-arp
Ip rip receive version 1
Only transmits RIP version 1 packets on the interface
Ip rip send version 1
Only transmits RIP version 2 packets on the interface
Config#interface tunnel 1 config-tunnel 1#ip route-cache
Keepalive period retries
Config#interface tunnel
Tunnel checksum
Config#interface tunnel 1 config-tunnel 1#tunnel checksum
Tunnel destination ip address
Config#interface tunnel Config-tunnel 1#tunnel destination
Tunnel key value
Config#interface tunnel 1 config-tunnel 1#tunnel key
Config#interface tunnel 1 config-tunnel 1#tunnel mode gre
Tunnel mode gre
Tunnel sequence-datagrams
Tunnel source ip address interface
Config#interface tunnel Config-tunnel 1#tunnel source
Hdlc Command Set
Hdlc Command SET
Copyright 2005 Hewlett-Packard Development Company, L.P 812
Copyright 2005 Hewlett-Packard Development Company, L.P 813
Config#interface hdlc Config-hdlc1#access-policy UnTrusted
Copyright 2005 Hewlett-Packard Development Company, L.P 815
Config#interface hdlc 1 config-hdlc 1#bandwidth
Config#interface hdlc 1 config-hdlc1#bridge-group
Copyright 2005 Hewlett-Packard Development Company, L.P 818
Config#interface hdlc 1 config-hdlc 1#crypto map MyMap
See Functional Notes below for syntax descriptions
Copyright 2005 Hewlett-Packard Development Company, L.P 821
Config-hdlc 1#fair-queue
Config-hdlc 1#hold-queue
Copyright 2005 Hewlett-Packard Development Company, L.P 824
Copyright 2005 Hewlett-Packard Development Company, L.P 825
Copyright 2005 Hewlett-Packard Development Company, L.P 826
Copyright 2005 Hewlett-Packard Development Company, L.P 827
Sros Command Line Interface Reference GuideHDLC Command Set
Copyright 2005 Hewlett-Packard Development Company, L.P 829
Config#interface hdlc Config-hdlc 1#ip mcast-stub downstream
Copyright 2005 Hewlett-Packard Development Company, L.P 831
Copyright 2005 Hewlett-Packard Development Company, L.P 832
Config#interface hdlc Config-hdlc 1#ip ospf dead-interval
Copyright 2005 Hewlett-Packard Development Company, L.P 834
Copyright 2005 Hewlett-Packard Development Company, L.P 835
Following enables proxy ARP on the Hdlc interface
Copyright 2005 Hewlett-Packard Development Company, L.P 837
Copyright 2005 Hewlett-Packard Development Company, L.P 838
Config-hdlc 1#ip route-cache
Copyright 2005 Hewlett-Packard Development Company, L.P 840
Config#interface hdlc 1 config-hdlc 1#keepalive
Config#interface hdlc 1 config-hdlc 1#lldp receive
Config#interface hdlc 1 config-hdlc 1#lldp send
Config#interface hdlc 1 config-hdlc 1#mtu
Config-interface# Interface Configuration Mode
Config#interface hdlc Config-hdlc1#qos-policy out Voicemap
Config#interface hdlc Config-hdlc 1#no snmp trap link-status
Router#configure terminal Routerconfig#interface loopback
Loopback Interface Configuration Command SET
Copyright 2005 Hewlett-Packard Development Company, L.P 848
Copyright 2005 Hewlett-Packard Development Company, L.P 849
Copyright 2005 Hewlett-Packard Development Company, L.P 850
Config#interface loopback 1 config-loop 1#bandwidth
Copyright 2005 Hewlett-Packard Development Company, L.P 852
Copyright 2005 Hewlett-Packard Development Company, L.P 853
Copyright 2005 Hewlett-Packard Development Company, L.P 854
Copyright 2005 Hewlett-Packard Development Company, L.P 855
Copyright 2005 Hewlett-Packard Development Company, L.P 856
Copyright 2005 Hewlett-Packard Development Company, L.P 857
Copyright 2005 Hewlett-Packard Development Company, L.P 858
Copyright 2005 Hewlett-Packard Development Company, L.P 859
Copyright 2005 Hewlett-Packard Development Company, L.P 860
Copyright 2005 Hewlett-Packard Development Company, L.P 861
Copyright 2005 Hewlett-Packard Development Company, L.P 862
Config-loop 1#ip mcast-stub downstream
Page
Assign a simple-text authentication password to be used by
Config-loop 1#ip ospf authentication null
Config-loop 1#ip ospf network broadcast
Following enables proxy-arp on the loopback interface
Copyright 2005 Hewlett-Packard Development Company, L.P 869
Copyright 2005 Hewlett-Packard Development Company, L.P 870
Config#interface loopback 1 config-loop 1#ip route-cache
Config#interface loopback 1 config-loop 1#ip unnumbered ppp
Config#interface loopback 1 config-loop 1#mtu
Config-eth 0/1#snmp trap
Copyright 2005 Hewlett-Packard Development Company, L.P 875
Line Console Interface Config Command Set
Line Console Interface Config Command SET
Databits option
Config#line console 0 config-con 0#databits
Flowcontrol none software
Config#line console 0 config-con 0#flowcontrol none
Config#line console
Line-timeout minutes
Login
Config#line console Config-con 0#login authentication myList
Login authentication aaa login list
Login local-userlist
Parity option
Config#line console 0 config-con 0#parity mark
Config-con 0#password mypassword
Password md5 password
Speed rate
Stopbits option
Config#line console 0 config-con 0#stopbits
Line Telnet Interface Config Command Set
Line Telnet Interface Config Command SET
Config#line telnet 0
Access-class listname
Config-telnet0-4#access-class Trusted
Config#line telnet 0 config-telnet0#line-timeout
Copyright 2005 Hewlett-Packard Development Company, L.P 890
Copyright 2005 Hewlett-Packard Development Company, L.P 891
Copyright 2005 Hewlett-Packard Development Company, L.P 892
Config#line telnet
Router RIP Configuration Command Set
Router RIP Configuration Command SET
Auto-summary
Config#router rip config-rip#no auto-summary
Default-metric value
Network address subnet mask
Passive-interface interface
Redistribute connected metric value
Config#router rip Config-rip#redistribute connected
Metric value
Redistribute ospf metric value
Config#router rip config-rip#redistribute ospf
Redistribute static metric value
Version version
Config#router rip config-rip#version
Router Ospf Configuration Command Set
Router Ospf Configuration Command SET
Config#router ospf Config-ospf#area 192.22.72.0 default-cost
Area area id default-cost value
Not-advertise
Area area id range ip address network mask advertise
Area area id stub no-summary
Config#router ospf
Auto-cost reference-bandwidth rate
Config#router ospf Config-ospf#auto-cost reference-bandwidth
Metric type type Configure metric type 1 or
Always Always advertise default route Metric value
Metric value Metric type type
Value Set the default metric value range
Network ip address wildcard area area id
Redistribute connected
Config#router ospf config-ospf#redistribute connected
Redistribute rip
Config#router ospf config-ospf#redistribute rip
Redistribute static
Config#router ospf config-ospf#redistribute static
Summary-addressaddress mask prefix mask not-advertise
Timers lsa-group-pacing seconds
Config#router ospf config-ospf#timers spf 10
Timers spf delay hold
Quality of Service QoS Map Commands
Quality of Service QOS MAP Commands
Match dscp 0-63match ip rtp port #
Match
Priority unlimited
Priority
Set dscp
Config#qos map Voicemap 10 config-qos-map#set dscp
Set precedence
Config#qos map Voicemap 10 config-qos-map#set precedence
Common Commands
Common Commands
Alias text
Copyright 2005 Hewlett-Packard Development Company, L.P 924
Copyright 2005 Hewlett-Packard Development Company, L.P 925
Copyright 2005 Hewlett-Packard Development Company, L.P 926
Description
Config#do clear arp-cache
End
Exit
Copyright 2005 Hewlett-Packard Development Company, L.P 931
#ping
Policy-class
Show running-config
Qos-map
Checksum
Enable #show running-config Building configuration
Config#interface modem 1/2
CLI
Index
Command security levels
Fair-queue570, 667, 744, 822 fdl
Nat-traversal 382 netbios-name-server 366
Copyright 2005 Hewlett-Packard Development Company, L.P 940
VT100 configuration Warranty 2 write