Dell Command Line Reference Guide for the S6000 System 70.0
Page
Contents
Control and Monitoring
Access Control Lists ACL 182
802.1X 160
184
239
Boot Command Line Interface 323
Bidirectional Forwarding Detection BFD 317
Border Gateway Protocol 336
375
Content Addressable Memory CAM 459
Control Plane Policing CoPP 471
Data Center Bridging DCB 478
Debugging and Diagnostics 522
Dynamic Host Configuration Protocol Dhcp 546
Flex Hash and Optimized Boot-Up 591
Equal Cost Multi-Path Ecmp 583
FCoE Transit 596
Force10 Resilient Ring Protocol Frrp 612
Garp Vlan Registration Gvrp 623
Interfaces 664
23 IPv4 Routing 742
743
25 IPv6 Access Control Lists IPv6 ACLs 830
24 IPv6 Basics 818
Intermediate System to Intermediate System IS-IS 840
849
Link Aggregation Control Protocol Lacp 910
Layer 918
Link Layer Discovery Protocol Lldp 953
Multiple Spanning Tree Protocol Mstp 995
Microsoft Network Load Balancing 976
Multicast Source Discovery Protocol Msdp 979
Multicast 1012
Neighbor Discovery Protocol NDP 1021
Object Tracking 1039
Open Shortest Path First OSPFv2 and OSPFv3 1059
1090
PIM-Sparse Mode PIM-SM
Policy-based Routing PBR
Port Monitoring 1214
Private Vlan Pvlan 1222
Per-VLAN Spanning Tree Plus PVST+ 1228
Quality of Service QoS 1245
Routing Information Protocol RIP 1301
Remote Monitoring Rmon 1329
Rapid Spanning Tree Protocol Rstp 1346
Security 1360
1365
1406
Service Provider Bridging 1456
SFlow 1463
Simple Network Management Protocol Snmp and Syslog 1475
Snmp Traps 1524 Stacking 1530
Storm Control 1541
Spanning Tree Protocol STP 1551
System Time and Date 1566
Tunneling 1585
Vlan Stacking 1595
Virtual Routing and Forwarding VRF 1607
VLT Proxy Gateway 1620
Virtual Link Trunking VLT 1626
Virtual Extensible LAN Vxlan 1648
Virtual Router Redundancy Protocol Vrrp 1660
1681
Objectives
About this Guide
References
Audience
Information Icons
Accessing the Command Line
Multiple Configuration Users
CLI Basics
Obtaining Help
Keywords at Any command Mode To obtain a list
Partial Keywords using Example
To obtain a list
Esc F
Key Combination Action
Esc B
Esc D
Using the Keyword no Command
Filtering show Commands
Navigating the CLI
Ethernet Show run
Filtering the Command Output Multiple Times
Displaying All Output
Grep Ethernet Ignore-case No-more
Show feature
Feature vrf
Show feature
Command
CLASS-MAP Mode
Command Modes
BGP ADDRESS-FAMILY Mode
Configuration Mode
Dhcp Pool Mode
CONTROL-PLANE Mode
Dhcp Mode
Ecmp Group Mode
Extended Community List Mode
Exec Mode
Exec Privilege Mode
Frrp Mode
Dellconf-if# Interface mode
IP Access List Mode
Isis ADDRESS-FAMILY Mode
Prompt
Line Mode
Lldp Mode
Lldp Management Interface Mode
MAC Access List Mode
Per-VLAN Spanning Tree PVST+ Plus Mode
Multiple Spanning Tree Mstp Mode
Openflow Instance Mode
PORT-CHANNEL FAILOVER-GROUP Mode
Rapid Spanning Tree Rstp Mode
PREFIX-LIST Mode
Protocol Gvrp Mode
ROUTE-MAP Mode
Router OSPFV3 Mode
Router Isis Mode
Router Ospf Mode
Router RIP Mode
VLT Domain Mode
Spanning Tree Mode
TRACE-LIST Mode
Vrrp Mode
Boot system
File Management
Parameters
Command Modes Command History Usage Information
Version Description 70.0
Directory
Copy http
Series Original command
Http Copy via CLI
Flash
Copy
Enter http http//hostip
Filepath
Flash
40.0
Usage Information Example VersionDescription
FTOS#
Commands
Delete
Related
Filename
Command Modes Command History No-confirm
Dir
Name
Series
Format flash S-Series
Modes Command
Usage Information Related Commands VersionDescription 70.0
Fsck flash
Mkdir
VersionDescription 70.0
Introduced on S4810 and Z9000
Rmdir
Password Optional Enter the password
Mount nfs
Dell#mkdir nfsmount/nfs-mountpoint/guest
Upgrade system
00.0 Version
19.0 Version
Url
Rename
Rename url url
Version Description
Flash Boot
Show boot system
Syntax Parameters Defaults Command Modes Command History
All
Show file-systems
Show bootvar
Syntax Command Modes Command History Example
Version Description 70.0 Introduced on the S6000-ON
Field Description Sizeb
Command Modes Command History Example Command Fields
Feature
Freeb
Show os-version
File-url
Release Image Information
Show running-config
Cam-profile
Boot
Bgp
Class-map
Mac-address
Logging
Mac
Management
Spanning
Sflow
Snmp
Tree
File Management
Show startup-config
Show startup-config
Example Related Commands VersionDescription 70.0
Show version
Show version
SRC
Srcc
S6000
Bootselector
Upgrade boot
Bootflash
Booted
00.0 Version
Img-file
Verify
Verify md5 sha256 flash// img-filehash-value
Hash-value
Banner exec c line c
Control and Monitoring
Banner exec
Line
Banner login
Line c
Interactive
Defaults Command Modes Command History
Banner motd
Banner motd c line c
Usage Information Related Commands VersionDescription
Cam-acl
Command History Usage Information
20.2 0.0
Aux
Clear line
Line-number
Console
Command Modes Command History Example
Configure
Configure terminal
Dell#configure Dellconf#
Command
Disable
Disable level
Level
Enable level
Enable
Command History Usage Information Example
Optional Enter a number for a privilege level of Dell
Enable optic-info-update interval
Enable optical-info-update interval seconds
Info-update interval command
End
Seconds
End
Exec-timeout minutes seconds
Exec-timeout
Command History Related Commands
Minutes
Command Modes Command History Usage Information Example
Exit
Dell con0 is now available Press Return to get started
Ftp-server enable
Ftp-server vrf vrf-name enable
Vrf vrf-name
Ftp-server topdir directory
Command History Example
Ftp-server topdir
Enter the directory path
Syntaxftp-server username username password encryption-type
Ftp-server username
Encryption
Password
Hostname
Type
Ip ftp password
Password password command
Ip ftp source-interface interface
Command History Usage Information Related Commands
Ip ftp source-interface
Interface
Ip tftp vrf
Ip tftp vrf vrf-name
Specify the VRF that is used by the Tftp client
Parameters Defaults Command Modes Command History
Ip ftp username
Ip ftp username username
Ip ftp vrf
Ip telnet server enable
Ip telnet server enable
Vrf
Ip telnet server vrf
Ip telnet source-interface
Management
For Loopback interfaces, enter the keyword loopback
Related Telnet telnet to another device Commands
Line aux 0 console 0 vty number end-number
Commands IP access control list ACL
Line
End-number
Motd-banner
Ping
Motd-banner
Ipv6-address
Timeout
Host
Count
Sweep-min
Validate-reply
Outgoing
Size
Usage Information Example IPv4 Version
Reload
Nvram-cfg
Change
Send
Send * line console vty
Vty
Service timestamps
Show alarms threshold
Show alarms
Show running-config command
Parameters Threshold
Show command-tree
Show command-tree count no
Count
Show cpu-traffic-stats
Show cpu-traffic-stats port number all cp
Port number
All
Show debugging
No CPU traffic statistics Dell#
Show debugging
Stack-unit unit
Show environment
Fan
Pem
Unknown
Show inventory
Show inventory media slot
Media slot
0MGDH8
08YWFG
0T9FNW
Lldp
Show memory
Show memory stack-unit id
Parameters Stack-unit id
Details
Show processes cpu
Unit
Summary
Core
UNIT0
Cpuid
PID
TID
TTY
Dhclient
Show processes ipc flow-control cp rp1 rp2 stack-unit
Show processes ipc flow-control
Show processes ipc flow-control cp
Rp1
Defaults Command Modes Command History Usage Information Rp2
Show processes memory
Show processes
Memory output
Process ID
Example Example management- unit
Clients
Defaults Command Modes Command History Trace-flags
Show software ifm
Ifagt number
Stack-unit unit- id disabled- ports
Show system
Brief
Status
Type command. Modified the show system stack-unit
Stack-ports Optional Enter the keywords stack-ports for
Information about the status or topology of the stack ports
145
146 Control and Monitoring
Example S6000-ON
Show tech-support
Show tech-support stack-unit unit-id
Save
Usage Information Example S- Series
150 Control and Monitoring
Hardware watchdog stack-unit
Ssh-peer-stack-unit
Telnet
Ssh-peer-stack-unit -l username
Vrf instance
Host
Prefix-length
Source
Dell#telnet vrf vrf1
Defaults Not configured Command
Telnet-peer-stack-unit
Telnet-peer-stack-unit
Terminal length
Terminal length screen-length
Traceroute
156 Control and Monitoring
Undebug all
Undebug all
Virtual-ip
Write memory compressed terminal
Startup-config command
Write
Memory
802.1X
Important Points to Remember
Dot1x auth-fail-vlan
Disabled Exec Privilege
Debug dot1x
Syntaxdot1x auth-fail-vlan vlan-idmax-attempts number
Configuration conf-if-interface-slot/port
Vlan-id Enter the Vlan Identifier. The range is from 1 to
Dot1x auth-server radius
Dot1x auth-server
Dot1x auth-type mab-only
Dot1x auth-type mab-only
Dot1x authentication Configuration
Dot1x authentication
Dot1x authentication Interface
Vlan-id Enter the Vlan Identifier. The range is from 1 to
Dot1x guest-vlan
Dot1x guest-vlan vlan-id
Usage Information VersionDescription 70.0
Single-host
Dot1x host-mode
Dot1x host-mode single-host multi-host multi-auth
Multi-host
Defaults Command Modes Command History Usage Information
Dot1x mac-auth-bypass
Dot1x mac-auth-bypass
Dot1x max-eap-req number
Dot1x max-eap-req
Dot1x max-supplicants
Number
Dot1x port-control
Dot1x quiet-period
Auto
Dot1x quiet-period seconds
Dot1x reauthentication
Dot1x reauthentication interval seconds
Dot1x reauth-max
Dot1x server-timeout
Dot1x server-timeout seconds
Dot1x reauth-max number
Dot1x supplicant-timeout
Dot1x supplicant-timeout seconds
Parameters Defaults Command Modes Command History Seconds
Dot1x tx-period
Dot1x tx-period seconds
Show dot1x cos-mapping interface
Show dot1x cos-mapping interface interface mac-address mac
Mac-address
177
Show dot1x interface interface mac-address mac-address
Dot1x Status Enable
Show dot1x interface
Dell#show dot1x interface tengigabitethernet 1/32
Example mac- address
Dot1x Status Enable Port Control
AUTHORIZEDGUEST-VLAN
181
Remark
Access Control Lists ACL
Commands Common to all ACL Types
Remark
Description Enter a description of up to 80 characters
Show config
Show config
Common IP ACL Commands
Access-class
Access-list
Characters
Clear counters ip access-group
Ip access-group
Enter the keyword in to apply the ACL to incoming traffic
Implicit-permit
Vlan vlan-id
Show ip accounting access-list
Ip control-plane egress-filter
Name Camcount
Field Extended IP
Accounting Access-lists
Show ip
Seq
Standard IP ACL Commands
Deny
Any
Configuration Guide
Ip access-list standard
Ip access-list standard access-list-name
Permit
Mask
Host ip-address
Resequence access-list
Name StartingSeqNu
Seq
Mac
Step-to
Sequence
Extended IP ACL Commands
Ip-protocol
Destination
Byte
Monitor
Deny icmp
Optional Enter the keyword byte to count bytes
Deny tcp
Bit
Operator
Defaults Command Modes Command History Count
Port port Destination Mask
204
Deny udp
Total Ports
Port port
207
Ip access-list extended
Ip access-list extended access-list-name
Dellconf#ip access-list extended TESTListEXTEND
Dellconfig-ext-nacl#
Any host ip-address count bytes dscp value order fragments
210
Permit tcp
Operator
Numbers if you are using the range logical operand.
213
Permit udp
Range is 0 to
216
Ipv4 mac
Icmp
Tcp
Udp
Optional Enter the application layer port number. Enter
Access Control Lists ACL
Common MAC Access List Commands
Clear counters mac access-group
Clear counters mac access-group mac-list-name
Mac access-group
Vlan vlan-range
Show mac access-lists
Show mac access-lists access-list-name interface interface
Out
Show mac accounting access-list
Show mac accounting access-list access-list-nameinterface
Standard MAC ACL Commands
Count byte log monitor
Mac-source
Address Mac-source
Address-mask
Mac access-list standard
Mac access-list standard mac-list-name
Syntaxpermit any mac-source-address mac-source-address-mask
229
To remove this filter, use the no seq sequence-numbercommand
Extended MAC ACL Commands
Usage Information Related Commands
Mac-source- address
Byte log monitor
Parameters Any Host mac- address
Mac- destination- address
Mac access-list extended
Syntaxmac access-list extended access-list-namecpu-qos
Cpu-qos
Mac
Address
Destination Address-mask
Clear ip prefix-list prefix-name
IP Prefix List Commands
Clear ip prefix-list
Prefix-name
Ge min-prefix
Related Ip prefix-list configures a prefix list Commands
Ip-prefix
Length
Ip prefix-list
Ip prefix-list prefix-name
Version Description 1.0
Ip-prefix /nn
Show config
Ip prefix-list snickers
Dellconf-nprefixl#show config
Show ip prefix-list detail
Dellconf-nprefixl#
Show ip prefix-list summary
Route Map Commands
Continue
Description
Description description
Description
Match as-path
Match as-path as-path-name
Community
Match community
Pre-6.1.1.0
List-name
Match interface
Match interface interface
Match ip address prefix-list-name
Related Commands VersionDescription
Match ip address
Prefix-list
Match ip next-hop
Match ip route-source
Match metric
Match metric metric-value
Metric-value
Parameters Egp
Related Commands VersionDescription 70.0
Match origin
Igp
Match route-type
Match tag
Match tag tag-value
Tag-value
Map-name
Route-map
Syntaxroute-map map-namepermit deny sequence-number
Is permit
Dellconf#route-map dempsey Dellconfig-route-map#
Set as-path
Set as-path prepend as-number
To return to the default, enter no set automatic-tag
Set automatic-tag
Set automatic-tag
Set comm-list delete
Set comm-list community-list-name delete
Set community
Local-AS
None
No-advertise
No-export
Additive
Level-1-2
Set level
Backbone
Stub-area
Set local-preference
Set local-preference value
Value
Set metric
Set metric + metric-value
7.0
Type-1
Set metric-type
Set metric-type internal external type-1 type-2
Type-2
Set next-hop
Set next-hop ip-address
Ip-address Specify an IP address in dotted decimal format
Set origin
Set tag
Set origin igp egp incomplete
Set weight
Set weight weight
Weight
Router-originated = 32768 all other routes = Not configured
Ip prefix-list PLOSPFtoRIP
Show route-map
Version Description 7.0 Introduced on the S4810 1.0
Show route-map map-name
Deny for Standard IP ACLs
Example Related Commands VersionDescription Pre-6.1.1.0
Parameters Defaults Log
Threshold-in
Deny for Extended IP ACLs
30.0
273
Seq for Standard IPv4 ACLs
Parameters Log
275
Deny tcp for Extended IP ACLs
Deny ether-type for Extended MAC ACLs
278
Deny for Standard MAC ACLs
Deny for Extended MAC ACLs
281
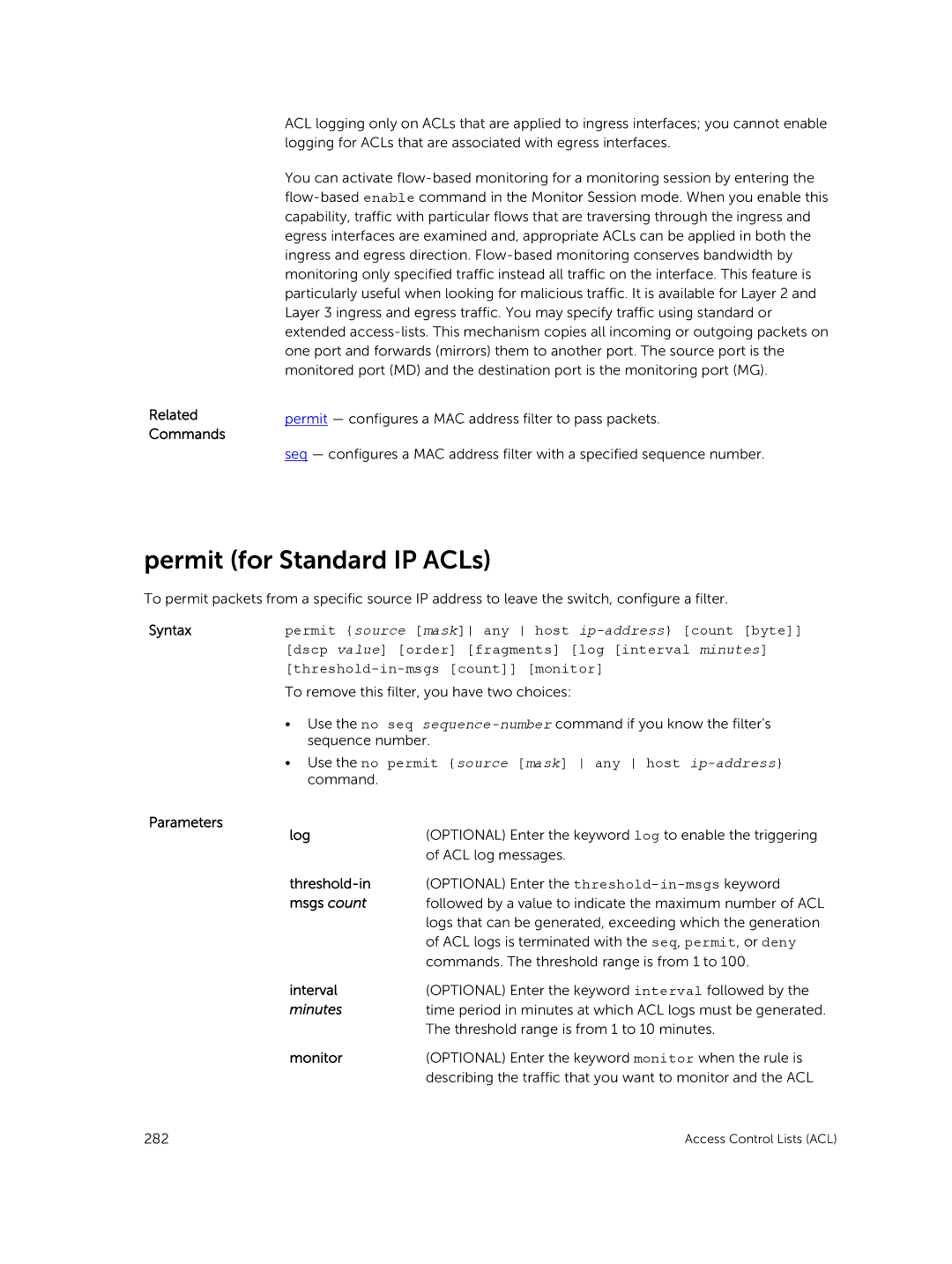
Use the no permit source mask any host ip-address command
Permit for Standard IP ACLs
283
Permit arp for Extended MAC ACLs
Permit ether-type for Extended MAC ACLs
Use the no permit ether-type protocol-type-number
Defaults Command Modes Command History Usage Information
CONFIGURATION-STANDARD-ACCESS-LIST
Permit icmp for Extended IP ACLs
Permit udp for Extended IP ACLs
Usage Information Version Description 40.0
289
Permit for Extended IP ACLs
291
Command History Usage Information Version Description 70.0
Permit for Standard MAC ACLs
Seq for Standard MAC ACLs
Version Description 70.0
CONFIGURATION-EXTENDED-ACCESS-LIST
Permit tcp for Extended IP ACLs
Usage Information Related Commands Version Description 40.0
Seq arp for Extended MAC ACLs
Commands. You can enter a threshold in the range
Byte order log interval minutes threshold-in-msgs
Seq ether-type for Extended MAC ACLs
Seq sequence-number deny permit ether-type protocol-type
Count monitor
299
Seq for IP ACLs
Operator port port count byte log interval minutes
Seq for IPv6 ACLs
Icmp ip tcp udp source address mask any host ipv6
Threshold-in-msgs count monitor
ACCESS-LIST
Permit udp for IPv6 ACLs
Permit tcp for IPv6 ACLs
305
Permit icmp for IPv6 ACLs
ACCESS-LIST
Permit for IPv6 ACLs
Version Description 70.0
Deny udp for IPv6 ACLs
Deny arp for Extended MAC ACLs
Vlan-idip-address any opcode code-number count byte
Order log interval minutes threshold-in-msgs count monitor
Deny tcp for IPv6 ACLs
Deny icmp for Extended IPv6 ACLs
Deny icmp source address mask any host ipv6-address
Deny for IPv6 ACLs
316
Bidirectional Forwarding Detection BFD
Bfd all-neighbors
Router BGP Router Isis
Ip route bfd
Milliseconds
Neighbor bfd
Peer-group
Neighbor bfd disable
322 Bidirectional Forwarding Detection BFD
Default
Boot Command Line Interface
Boot change
Primary
Boot device ftp
Boot message
Bootuser # boot change primary
Bootuser #
Defaults Command Modes Command History Example
Boot show net config retries
Boot write net config retries
Syntax Boot write net config retries int Command
Boot zero
Defaults Command Modes
Default-gateway
Syntax Command Modes Command History Usage Information
Ignore enable-password
Bootadmin # etheraddr aaaaaaaaaaaa
Etheraddr macaddr
Ignore startup-config
Related Reload Exit from this mode and reload Ftos Commands
Interface management ethernet ip address
Modes Command Version Introduced on the S6000 History
Modes Command History Usage Information Example
Syntax Reload Command
Nvram erase
Bootuser # show bootvar
Command Modes History Example Serial
Syntax Show bootvar Command
Serial console
Show default-gateway
Syntax Show default-gateway Command
Bootuser # show default-gateway
Show serial console baud rate
Bootadmin #
Show interface management ethernet
Syntax Show serial console baudrate
Settimeout
Parameters Enable
Disable
Watchdog string
Watchdog Timeout
BGP IPv4 Commands
Border Gateway Protocol
Address-family
Ipv4 vrf vrf
Ipv6 unicast
Aggregate-address
Format A.B.C.D and mask in /prefix format /x
Bgp add-path send receive both path-count
Bgp add-path
Usage Information VersionDescription
Parameters Send
Path-count
Bgp always-compare-med
Both
Bgp always-compare-med
Asnotation command
Bgp asnotation
Bgp asnotation asplain asdot+ asdot
Dellconf-routerbgp#bgp asnotation asdot+
Bgp bestpath as-path ignore
Dellconf-routerbgp#bgp asnotation asdot
Dellconf-routerbgp#bgp asnotation asplain
Bgp bestpath as-path multipath-relax
Bgp bestpath as-path multipath-relax
Bgp bestpath Med confed
Bgp bestpath med confed
Bgp bestpath med missing-as-best
Bestpath med
Bgp bestpath router-id ignore
Bgp bestpath router-id ignore
Reflection command
Bgp client-to-client reflection
Bgp client-to-client reflection
Bgp cluster-id
Bgp cluster-id ip-address number
Bgp confederation identifier
Bgp confederation identifier as-number
As-number
Bgp confederation peers
Bgp confederation peers as-number...as-number
Half-life
Bgp dampening
Route-map map-name
Reuse
Suppress Max-suppress- time
Route-map map-name
Bgp default local-preference
Bgp default local-preference value
Bgp dmzlink-bw
Bgp dmzlink-bw
Bgp enforce-first-as
Dmzlink-bw
Bgp fast-external-fallover
Bgp fast-external-fallover
Bgp four-octet-as-support
Bgp graceful-restart
Restart-time
Stale-path-time
Only
Defaults Command Modes Command History Role receiver
Bgp non-deterministic-med
Bgp non-deterministic-med
Bgp recursive-bgp-next-hop
Bgp recursive-bgp-next-hop
Bgp regex-eval-optz-disable
Bgp regex-eval-optz-disable
Border Gateway Protocol
Bgp router-id
Bgp router-id ip-address
65535.65
Clear ip bgp
429496729
535
Clear ip bgp dampening
Ipv4 unicast
Ipv4-address
Path-name
Clear ip bgp flap-statistics
Filter-list as
Regexp regular
Clear ip bgp peer-group
Parameters Command Modes Command History
Debug ip bgp
Xxxxx
Debug ip bgp dampening
0.0 Added support for VRF
Ipv4 multicast
Xxxxx peer-group peer-group-name events in out command
Debug ip bgp events
Ipv6 unicast
Parameters Command Modes Command History Usage Information
Debug ip bgp keepalives
VRF to display BGP keepalive information corresponding
Debug ip bgp notifications
VersionDescription 70.0 Added ipv6 support
Debug ip bgp soft-reconfiguration
VersionDescription 70.0 Added support for VRF
Debug ip bgp updates
Default-metric
Default-metric number
Parameters Bandwidth
Defaults Command
Deny bandwidth
Parameters Enter a description to identify the BGP protocol
Maximum-paths ebgp ibgp number
Maximum-paths
Pre-7.7.1.0 Introduced
Ebgp
Neighbor activate
Activate
Neighbor add-path
Group-name advertisement-interval command
Neighbor advertisement-interval
Neighbor advertisement-start
Syntaxneighbor ip-address advertisement-start seconds
Neighbor allowas-in
Neighbor default-originate
Route-map
Neighbor description
Name Text
Neighbor distribute-list
Peer-group- name Prefix-list- name
Neighbor ebgp-multihop
Syntaxneighbor ip-address peer-group-name ebgp-multihop ttl
Ttl
Neighbor fall-over
Neighbor local-as
Prepend
No prepend
Name Maximum
Neighbor maximum-prefix
Threshold warning-only
Threshold
Neighbor password
Type password
Parameters Defaults Command Modes
Ip-address Peer-group- name Encryption- type Password
Neighbor peer-group assigning peers
Neighbor ip-address peer-group peer-group-name dmzlink-bw
Added the dmzlink-bw parameter
Neighbor peer-group creating group
Neighbor peer-group-name peer-group
Neighbor peer-group passive
Syntaxneighbor peer-group-namepeer-group passive sessions
Neighbor remote-as
Neighbor remove-private-as
Syntaxneighbor ip-address peer-group-name remove-private-as
Neighbor route-map
Neighbor ip-address peer-group-nameroute-mapmap-name
Neighbor route-reflector-client
Ip-address Peer-group- name
Neighbor shutdown
Neighbor ip-address peer-group-name shutdown
Neighbor soft-reconfiguration inbound
Format
Neighbor timers
Keepalive
Holdtime
Neighbor update-source
Neighbor weight
Network
Ip-address Mask
Enter the mask of the IP address in the slash prefix length
Network backdoor
Network ip-address mask backdoor
Format for example, /24
Permit bandwidth
Permit bandwidth
Redistribute
Parameters Connected Static Route-map map-name
Redistribute ospf
Process-id
Match external
Match internal
Router bgp as-number
Error No router id configured
Router bgp
Dellconf#router bgp Dellconf-routerbgp#
Set extcommunity bandwidth
Set extcommunity bandwidth
Show capture bgp-pdu neighbor
Show capture bgp-pdu neighbor ipv4-address
View the current Router BGP configuration
Network
Show ip bgp
Ipv4 unicast
Network-mask
Next Hop
Weight
Field Description Network
Metric
Show ip bgp cluster-list
Show ip bgp vrf vrf-name ipv4 multicast unicast ipv6
Command Modes Command History Usage Information Ipv4 unicast
Cluster-id
Show ip bgp community
Ipv4 multicast Ipv6 unicast Community- number
Local-AS No-advertise No-export
Dell#show ip bgp community ?
Show ip bgp community-list
Exact-match
424
Show ip bgp dampened-paths
Reuse
Syntax Defaults Command Modes Command History Example
Show ip bgp detail
Show ip bgp ipv4 unicast detail
428
Show ip bgp extcommunity-list
List name
Show ip bgp filter-list
Syntaxshow ip bgp vrf vrf-name ipv4 multicast unicast ipv6
As-path-name
Show ip bgp flap-statistics
Field Description
Ip-address
Is available
Destination network
Show ip bgp inconsistent-as
000023 000000 200 32768 Dell#*n 66.66.77.77/32 0.0
Show ip bgp vrf vrf-name ipv4 unicast inconsistent-as
Field Description Next Hop
Dampened
Show ip bgp neighbors
Advertised
Detail
Command Modes Flap-statistics Routes
BGP version
Received updates
Lines Description Beginning with BGP neighbor
BGP state
List of inbound
Last reset
Lines Description Beginning with Minimum time
Outbound
MULTIPROTOEXT1 ROUTEREFRESH2 ADDPATH69 CISCOROUTEREFRESH128
Show ip bgp next-hop
Capabilities advertised to neighbor for IPv4 Unicast
Show ip bgp vrf vrf-name next-hop
Show ip bgp paths
Total Displays the total number of BGP path attributes
Hash
Show ip bgp paths community
Address
Dell#show ip bgp paths ?
Show ip bgp peer-group
NO-ADVERTISE
2001 10001
Optional Enter the name of a peer group to view
Show ip bgp regexp
Show ip bgp vrf vrf-name regexp regular-expression
Regular
Character
Show ip bgp summary
Ipv6 unicast
Identifier BGP table version
Enabled
Field Description BGP router
Network entries
Field Description Time Established Display Example Day
Show running-config bgp
Defaultsnone
Week
Timers bgp
Mbgp Commands
OS Version 1.0, Mbgp for Series IPv4 Multicast Only
Distance bgp
Internal
External
Distance
Local-distance
457
458
Content Addressable Memory CAM
CAM Profile Commands
Important Points to Remember
Cam-acl Configuration
L2pt number
Command Modes
Cam-acl-egress
VersionDescription Usage Information
Cam-optimization
Cam-optimization qos
Qos Optimize CAM usage for QoS
Usage Information Example VersionDescription 70.0
Show cam-acl
Show cam-acl
L2PT
L2Acl Block = 128 entries Ipv4Acl Ipv6Acl Ipv4Qos L2Qos
Test cam-usage service-policy input input policy name stack
Test cam-usage
Policy-map
CAM Partition
Term Explanation Stack-Unit
Portpipe
Available CAM
Example S- Series Usage Information
Scaled-l3
Hardware forwarding-table mode
Unified Forwarding Table Modes
Hosts
Show hardware forwarding-table mode
Syntax Defaults Command Modes History
Show hardware forwarding-table mode
Control Plane Policing CoPP
Service-policy rate-limit-cpu-queues
Syntaxservice-policy rate-limit-cpu-queues policy-name
Control-plane-cpuqos
Service-policy rate-limit-protocols
Service-policy rate-limit-protocols policy-name
Policy-name
Defaults Not configured Command Exec Privilege Modes
Show cpu-queue rate cp
Show cpu-queue rate cp
Show ip protocol-queue-mapping
Show ip protocol-queue-mapping
UDP DHCP-R TCP FTP
TCP BGP
UDP Dhcp
Icmp
Show ipv6 protocol-queue-mapping
Show mac protocol-queue-mapping
Data Center Bridging DCB
DCB Command
Dcb-enable
Pfc-queues
Port-type
PFC Commands
Clear pfc counters
All stack-ports
Pfc no-drop queues
Pfc no-drop queues queue-range
Unit-number
Show dcb
Dot1p Value in the Description heading Incoming Frame
Port-set
Show interface pfc
Field Description Willing Status is
For an Ieee version
Input TLV pkts
Error pkts
Example Summary FieldDescription
Output TLV pkts
Show interface pfc statistics
Show interface port-type slot/port pfc statistics
Dell#show int te 1/1 pfc statistics
ETS Commands
Clear ets counters
Clear ets counters port-type slot/port
Show interface port-type slot/port ets summary detail
Parameters Defaults Command Modes Command History Port-type
Show interface ets
Port-type slot
Example Summary VersionDescription
ETS
TSA
12%
Example Detail
Priority# Bandwidth TSA 13%
2,3,4,5,6,7 100%
TLV
Dcbx Commands
Advertise dcbx-tlv
Pkts
Dcbx port-role
Reco pfc
Dcbx version
Dcbx detail command
Ieee-v2.5 command
Dcbx version auto cee cin ieee-v2.5
Defaults Ieee-v2.5
Debug dcbx
Fcoe priority-bits
Fcoe priority-bits priority-bitmap
Priority-bitmap
Iscsi priority-bits
Iscsi priority-bits priority-bitmap
Show interface port-type slot/port dcbx detail
Configuration
Show interface dcbx detail
Port-Role
Sync
ETS Recommendation TLV enabled
ETS Configuration TLV enabled
ETS Configuration TLV disabled
ETS Recommendation TLV disabled
Dcb-map
Dcb-map map-name
Alphanumeric characters is
Priority-pgid
DCB MAP
Priority-group bandwidth pfc
Group-num
Percentage
Dcb-map stack-unit all stack-ports all
Syntaxdcb-map stack-unit all stack-ports all dcb-map-name
Dcb-map Enter the name of the DCB map Name None
Syntax Parameters Default Command Modes Command History
Dcb pfc-shared-buffer-size
Dcb pfc-shared-buffer-size KB
Dcb-buffer-threshold
Dcb buffer-threshold profile-name
S4810-YU-MR-Dellconf#dcb buffer-threshold test
Priority
Queue 0 to
Qos-policy-buffer
Policy-name
Queue
Size
Buffer
Dcb-policy buffer-threshold Interface Configuration
Dcb-policy buffer-threshold profile-name
Profile-name
Show qos dcb-buffer-threshold
Show qos dcb buffer-threshold name
Dell#show qos dcb buffer-threshold
Snapshot unit
Stack-unit
Buffer-stats
Resource
# Type Total Buffered Cells
Ucast
PG#
Ucast Mcast
Instance 1 Instance 10S 20S
Instance Shared Hdrm Shared Hdrm in Cells
Resource all Unit 0 port 1 interface Fo 0/0 Stack-unit
Stack-unit Unit 0 port 5 interface Fo 0/4
… snip … Unit 0 port 104 interface Te 0/124 Stack-unit
# Type Total Buffered Cells Ucast
# Type Total Buffered Cells Mcast
Dcb pfc-total-buffer-size
PG# Shared Cells Headroom Cells
Dcb pfc-total-buffer-size KB
Show running-config dcb-buffer-threshold
Syntax Command Modes Command History
Show running-config buffer-threshold
519
Default Command Modes Command History
Dcb pfc-queues
Dcb pfc-queues value
Dcb ets pfc enable
Dcb ets pfc enable
ExampleDellconf#dcb pfc-queues
Logging coredump stack-unit
Debugging and Diagnostics
Diagnostics and Monitoring Commands
Syntaxlogging coredump stack-unit stack-unit-number all
Alllevels
Offline Diagnostic Commands
Diag stack-unit
Level0
Verbose
Offline stack-unit
Level2
Testname
Proceed with Offline-Diags confirm yes/noy
Defaults None
Online stack-unit
Online stack-unit number
Hardware Commands
Clear hardware stack-unit
Clear hardware system-flow
Unit number
Clear hardware vlan-couters vlan-id
Clear hardware vlan-counters
Port-set
Vlan-id
Parameters Eg-acl in-acl
Hardware watchdog
Show hardware layer2
Stack-unit id
Show hardware layer3
Show hardware layer3 acl qos stack-unit number port-set
Acl qos
Cpu
Show hardware stack-unit
Option
Statistics Cpu party-bus
Number no
Port-number
533
Example Port- Stats Example Register
HOL Drops
Invalid Vlan
535
Example Details
LinkStatus of Hg Port 27 is False
Show hardware stack-unit buffer
Example Total-Buffer
Example Buffer-Info Example Queue2/ Buffer-Info
Command Modes Command History Usage Information Example Port
Buffer-info
Show hardware system-flow
Parameters Acl qos Stack-unit id Port-set number counters
OSPF2 Stub
Grat ARP
OSPF1 Stub
Vrrp Stub
Show hardware vlan-counters
Show hardware vlan-counters vlan-id
Dell#show hardware vlan-counters
Show hardware stack-unit buffer-stats-snapshot
Dell#show hardware stack-unit 1 buffer-stats-snapshot unit
# Type Q# Total Buffered Cells Ucast Mcast
1000
Feature is disabled
Dynamic Host Configuration Protocol Dhcp
Commands to Configure the System to be a Dhcp Server
Clear ip dhcp
Debug ip dhcp server
Debug ip dhcp server events packets
Packet
Default-router
Debug ipv6 dhcp
Debug ipv6 dhcp
Disable
Syntaxdisable
Dns-server address address2...address8
Dns-server
Domain-name
Domain-name name
Excluded-address
Low-address
High-address
Hardware-address address
Hardware-address
Host
Address Enter the hardware address of the client
Days
Lease
Lease days hours minutes infinite
Hours
Netbios-node-type type
Netbios-name-server
Netbios-node-type
Enter the Netbios node type
Network network /prefix-length
Pool name
Pool
Show ip dhcp binding
Show ip dhcp binding
Pool name
Show ip dhcp configuration
Show ip dhcp configuration global pool name
Global
Show ip dhcp conflict address
Show ip dhcp conflict
Show ip dhcp server
Address Display a particular conflict log entry
Commands to Configure Secure Dhcp
Arp inspection
Arp inspection
Arp inspection-trust
Clear ip dhcp snooping
Arp inspection-trust
Defaults Command Modes Command History Example Interface
Remote-id
Clear ipv6 dhcp snooping binding
Ip dhcp relay
Trust
Ip dhcp snooping
No ip dhcp snooping
0.0 Introduced on the S4810 and S4820T
No ipv6 dhcp snooping
Ipv6 dhcp snooping
Ipv6 dhcp snooping vlan
No ip dhcp snooping vlan vlan-id
Ip dhcp snooping binding
Mac address
Ip ip-address
Ipv6 ipv6
IPv6 Dhcp Snooping Binding
Vlan-id
Lease value
Syntaxno ipv6 dhcp snooping database write-delay value
Ipv6 dhcp snooping database write-delay
Ip dhcp snooping database write-delay minutes
Ip dhcp snooping database
Ip dhcp snooping database renew
Ip dhcp snooping database renew
Ipv6 dhcp snooping database renew
Ipv6 dhcp snooping database renew
Ip dhcp snooping trust
No ip dhcp snooping trust
Ipv6 dhcp snooping trust
Ip dhcp source-address-validation
Ipmac
Ip dhcp relay information-option
Syntaxip dhcp relay information-option trust-downstream vpn
Vpn
Dellconf#ip dhcp relay information-option vpn
Ip dhcp snooping verify mac-address
VersionDescription 0.0 Added support for VRF
No ip dhcp snooping verify mac-address
Ip helper-address
Parameters Default Command Modes Command History
Ipv6 dhcp snooping verify mac-address
No ipv6 dhcp snooping verify mac-address
Ipv6 helper-address
Show ip dhcp snooping
VRF
Added the discard-counters , interface keywords,
576 Dynamic Host Configuration Protocol Dhcp
Show ipv6 dhcp snooping
Show ipv6 dhcp snooping
Commands to Configure DNS
Ip name-server
Ip domain-name
Information Example
Ip domain-list vrf vrf-name name
Ip domain-list
Ip host
Ip host vrf vrf-name name ip-address
Clear host vrf vrf-name * host-name
Clear host
Dellconf#ip host vrf jay dell
Host-name
Dell#clear host vrf jay dell
Equal Cost Multi-Path Ecmp
Ecmp-group
Ecmp-group ID
Hash-algorithm
Algorithm
585
Hg-seed seed- value stack- unit
Lag hash algorithm
Version Description 1.1
Nh-ecmp checksum
Dellconf#hash-algorithm linecard 5 ip-sa-mask ff ip-da
Ip ecmp weighted
Ip ecmp-group
Link-bundle-distribution trigger-threshold
Syntaxlink-bundle-distribution trigger-threshold percent
Percent
Link-bundle-monitor enable
Link-bundle-monitor enable
Load-balance ingress-port enable
Flex Hash and Optimized Boot-Up
Load-balance ingress-port enable
ExampleDell#load-balance ingress-port enable
Offset1 value
Protocol
String
Offset2 value
Reload-type fastboot
Reload-type fastboot
C9000 Series
Lacp fast-switchover
Lacp fast-switchover
Encapsulation dot1q
Encapsulation dot1q vlan-id
VersionDescription X.x Introduced on the C9000
Clear fip-snooping database interface vlan vlan-id enode
FCoE Transit
Clear fip-snooping database interface vlan
Enode-mac
Slot
Clear fip-snooping statistics
Port-type port
Port
Debug fip snooping
Debug fip snooping rx
Feature fip-snooping
Feature fip-snooping
Fip-snooping enable
Fip-snooping enable
Fip-snooping fc-map
Fip-snooping max-sessions-per-enodemac
Fip-snooping fc-map fc-map-value
Fip-snooping port-mode fcf
Max-sessions
Fip-snooping port-mode fcf
Fip-snooping port-mode fcoe-trusted
Show fip-snooping config
Show fip-snooping config
Fip-snooping port-mode fcoe-trusted
Dell# show fip-snooping config
Show fip-snooping enode
Show fip-snooping enode enode-mac-address
ENode Interface
Show fip-snooping fcf
Field Description ENode MAC
Vlan FC-ID
No of ENodes
Show fip-snooping statistics
FCF Interface
FCF MAC
Multicast
Field Description Number of Vlan
Requests
Discovery Solicits Number
Dell# show fip-snooping statistics interface vlan
Show fip-snooping system
Show fip-snooping system
Show fip-snooping vlan
Vlan FC-MAP
Show fips status
Show fips status
Force10 Resilient Ring Protocol Frrp
Clear frrp
Clear frrp ring-id
Command History Usage Information Example Related Commands
Debug frrp
Description
Count number
Description Word
Disable the resilient ring protocol
Interface
Control-vlan
Member-vlan
Member-vlan vlan-range
Vlan-range
Master
Mode master transit
Mode
Transit
Protocol frrp
Protocol frrp ring-id
Ring-id
Show frrp
Show frrp ring-idsummary summary
Timer
Syntaxtimer hello-interval milliseconds dead-interval
Milliseconds dead-intervalmilliseconds command
Garp Vlan Registration Gvrp
Clear gvrp statistics
Clear gvrp statistics interface interface
Debug gvrp
Debug gvrp config events pdu
Parameters Config
Pdu
Commands Protocol gvrp access Gvrp protocol
Leave
Garp timers
Parameters Defaults Command Modes Command History Join
Leave-all
Gvrp enable
Gvrp enable
Fixed
Gvrp registration
Gvrp registration fixed normal forbidden
Normal
Protocol gvrp
Protocol gvrp
Syntax Command Modes Command History Related Commands
Show config
Show garp timers
Show garp timers
Show gvrp brief interface
Dell#show garp timers
Show gvrp
Parameters Brief
Show gvrp statistics
Syntaxshow gvrp statistics interface interface summary
Enter the keyword summary to display just a summary
Leave In Transmitted
Join In Transmitted
Empty Transmitted
Leave Empty Transmitted
Icmp Message Types
637
Igmp Commands
Internet Group Management Protocol Igmp
Clear ip igmp groups
Group-address
Series legacy command
Debug ip igmp
Syntaxdebug ip igmp vrf vrf-name group address interface
VRF to enable debugging of Igmp packets corresponding
Ip igmp immediate-leave
Ip igmp access-group
Ip igmp access-group access-list
Syntaxip igmp immediate-leave group-list prefix-list-name
Ip igmp last-member-query-interval
Group-list
Syntaxip igmp last-member-query-interval milliseconds
Ip igmp query-interval
20.0
Ip igmp query-interval seconds
Ip igmp query-max-resp-time
Ip igmp query-max-resp-time seconds
Ip igmp vrf vrf-name ssm-map std-access-list source-address
Ip igmp ssm-map
Ip igmp version
Ip igmp version 2
Show ip igmp groups
Syntaxshow ip igmp vrf vrf-name groups group-address detail
Optional Enter the keyword detail to display
Igmp group
Include
Show ip igmp interface
Syntaxshow ip igmp vrf vrf-name interface interface
Usage Information Example Example VRF
Group
Show ip igmp ssm-map
Show ip igmp vrf vrf-name ssm-map group
Dell#show ip igmp ssm-map
Igmp Snooping Commands
Important Points to Remember for Igmp Snooping
Important Points to Remember for Igmp Querier
Clear ip igmp snooping groups group-address interface
Clear ip igmp snooping groups
Debug ip igmp snooping
Debug ip igmp snooping group address interface
Ip igmp snooping enable
Ip igmp snooping enable
Ip igmp snooping fast-leave
Ip igmp snooping fast-leave
Ip igmp snooping flood
Ip igmp snooping flood
Usage Information VersionDescription Series legacy command
Ip igmp snooping last-member-query-interval
Ip igmp snooping mrouter
Ip igmp snooping mrouter interface interface
Snooping querier command
Ip igmp snooping querier
Ip igmp snooping querier
Show ip igmp snooping groups
Show ip igmp snooping groups group-address detail detail
Member Ports
Show ip igmp snooping mrouter
Field Description Group Address
Show ip igmp snooping mrouter vlan number
Show ip igmp groups view groups
Clear counters
Basic Interface Commands
Interfaces
Clear counters interface vrrp ipv6 vrid learning-limit
Vrrp ipv6 vrid
Learning-limit
Example Related Commands VersionDescription
Clear dampening
Clear dampening interface
Max-suppress
Dampening
Suppress
Time
Description desctext
Duplex 10/100 Interfaces
Desctext Enter a text string up to 240 characters long
Duplex half full
Flowcontrol
Half
Full
Tx on
Rx on
Rx off
Tx off
672
Example Example Values
Interface
Enter one of the following keywords and slot/port or number
Range
675
Interface group
Tengigabitethernet 1/1 5 interface group
Tengigabitethernet 1/1-5
Usage Information Example Related Commands
Interface loopback
Interface loopback number
Dellconf#interface loopback 1655 Dellconf-if-lo-1655#
Example Related Commands Version
Interface ManagementEthernet
Interface ManagementEthernet slot/port
Interface null
Interface null number
Number Enter zero 0 as the Null interface number
Interface slot
Interface range
Dellconf#interface null Dellconf-if-nu-0#
Port, interface
Pre-Version Introduced on the E-Series 1.0
Overlapping
Example Bulk
Multiple Ports
Ports
Interface range macro define
Define interface range macro name interface , interface
Interface range macro name
Interface range macro name
Enter the name of an existing macro
Interface vlan vlan-id of-instance of-id
Command Modes History Example Single Range Related Commands
Interface vlan
Interface vlan vlan-id
Introduced on the S4810 added support for OpenFlow
Dellconf#int vlan Dellconf-if-vl-3#
Intf-type cr4 autoneg
Intf-type cr4 autoneg
Keepalive
Monitor interface
KeyDescription Systest-3
Key Description Monitor time
Time
Mtu
Example All Interfaces
692
Negotiation auto
Negotiation auto
Pre-6.2.1.0
Example Configured User Information
No portmode hybrid command
Portmode hybrid
Portmode hybrid
696
Rate-interval
Example Vlan
Rate-interval seconds
No ip address
Dellconf-if-fo-1/4#show config
Interface fortyGigE 1/4
Mtu
Show config for speed
Show config from Interface Range mode
No shutdown Dellconf-if-fo-1/4#
Show interfaces
Show interfaces interface
Added support for the tunnel interface type
Hardware is
Line Description TenGigabitEthern
Et 1/1
Pluggable media
Line Description Queuing
Strategy
Input Statistics
Example Usage Information Example 1G SFP LineDescription
Example Management Ethernet
Instance
Show interfaces configured
Show interfaces configured
Show interfaces dampening
Show interfaces dampening interface summary detail
Show interfaces stack-unit
Show interfaces stack-unit unit-number
710
Show interfaces status
Stack-unit slot
Show interfaces vlan
Syntaxshow interfaces vlan vlan-id Line description
Optional Enter the name of the Vlan
Syntax Parameters Command Modes Command History Example
Show system stack-unit quad-port-profile
Show system stack-unit-numberquad-port-profile
Parameters Enter the port number. The range is from 0 to
Stack-unit quad-port-profile
100 108 116 124 Dell#
Number 124
Show interfaces switchport
Show interfaces switchport interface stack-unit unit-id
Items Description Name
802.1QTagged
Vlan membership
Net
Show interfaces transceiver
Tengigabitether
FortyGigE
Alarm threshold
Line Description Rx Power
Type Temp High Alarm
Bias High Alarm
Temperature
Line Description RX Power High
Power Low
Tx Power
Alarm Flag
Tx Disable state
Temperature High
Temperature Low
Line Description Tx Bias Low
Dell#show interfaces TengigabitEthernet 1/1 transceiver
Show range
Show range
Dellconf-if-range-te-2/2,fo-2/56#
Shutdown
Dellconf-if-range-te-2/2,fo-2/56#show range
Shutdown
Speed Management interface
Speed 10 100 1000 auto
100
Stack-unit portmode
Stack-unit stack-unitport number portmode quad
Tengigabit
Switchport
Backup
Port-channel
Port Channel Commands
Channel-member interface
Interface command
Channel-member
Port or number information
Introduced on the S-Series Introduced on the C-Series
Group
Interface port-channel
Interface port-channel channel-number
Channel
Minimum-links
Status. The range is from 1 to 16. The default is
Status. The range is from 1 to 8. The default is
Minimum-links number
Port-channel failover-group
Port-channel failover-group
Show interfaces port-channel channel-number brief
Usage Information Related Command VersionDescription 70.0
Show interfaces port-channel
Channel
Port-channel is
Series legacy command Usage
Field Description Port-Channel
Part
Example User Information FieldDescription
Untitled
Example Related Commands Field Description
Show port-channel-flow
LAG
Destination-ip
Command Modes Command History Usage Information Incoming
Source-ip
Source-port
Enhanced Validation of Interface Ranges
Ip http source-interface
Ip ftp source interface
IPv4 Routing
Arp
Arp backoff-time seconds
Range is from 1 to 3600. The default is
Arp backoff-time
Enter the number of seconds an ARP entry is black-holed
Arp learn-enable
Arp learn-enable
Arp max-entries
Arp max-entries vrf vrf-name max-number
Max-number
Arp retries
Arp retries number
Enter the number of retries. The range is from 1 to 20.
Clear arp-cache
Arp timeout
Arp timeout minutes
Enter the number of minutes. The range is from 0 to
No-refresh
Enter the name of the host to delete. Enter * to delete all
Clear host
Clear host name
Host table entries
Clear ip fib stack-unit unit-numbervrf vrf-name
Clear ip fib stack-unit
Clear ip route
Syntaxclear ip route vrf vrf-name * ip-address mask
Format to clear that IP address from the routing table
Clear tcp statistics
Clear tcp statistics all cp rp1 rp2
Debug arp
Debug arp interface count value
Count value
Debug ip dhcp
Debug ip dhcp
Introduced on the C-Series Introduced on the E-Series
Debug ip icmp
Debug ip icmp interface count value
Access-group
Debug ip packet
Example Usage Information VersionDescription
Interface in parentheses through which the packet is
Being sent out on the network
Icmp type=
Example Usage Information Field Description TCP src=
UDP src=
IP Fragment
Ip address
Ip address ip-address mask secondary
Directed-broadcast command
Ip directed-broadcast
Ip directed-broadcast
Ip domain-list
Ip domain-list name
Ip domain-lookup
Ip domain-lookup
Ip domain-name
Ip domain-name name
Ip helper-address
Ip helper-address ip-address
Ip helper-address hop-count disable
Ip helper-address hop-count disable
Count disable command
Ip host
Ip host name ip-address
Ip address
Ip icmp source-interface
Ip icmp source-interface interface
Ipv6 icmp source-interface
Ipv6 icmp source-interface interface
Managementethernet
Ip max-frag-count
Dellconf#ipv6 icmp source-interface tengigabitethernet 1/1
Ip max-frag-count count
Ip name-server
Ipv4-address2
Ipv4-address6
Ip proxy-arp
Ip proxy-arp
Destination mask command
Ip route
Address Distance
Weight weight
Interface ip
Permanent
776 IPv4 Routing
1.0/24 6.6.6.2 weight
Dellconf#do show running-config grep route ip route vrf
Test 1.1.1.0/24 4.4.4.2 weight 100 ip route vrf test
Ip source-route
Ip tcp initial-time
Ip tcp initial-time
Ip unknown-unicast
Ip unknown-unicast vrf vrf-name
Ipv4 unicast-host-route
Show ip tcp initial-time
Show ip tcp initial-time
Ip unreachables
Ip unreachables
Load-balance
Tcp-udp enable
Enable
Ingress-port
Load-balance hg
Management route
Tunnel ipv4- over-ipv4 ipv4-over-gre- ipv4 mac-in- mac
FortyGigE vlan tengigabitethernet
Managementet
Forwarding
Router-address
Hernet
Show arp
Macaddress
Clear arp-cache command
Inspection
Retries
Clear arp in-progress. Please try after sometime
Lists which CPU the entries are stored on
CPU
Usage Information Example Summary Related Commands
Show arp retries
Show arp retries
Show hosts
Show hosts
Lookup
Field Description Default domain
Name/address
Name servers
Show ip cam stack-unit
Parameters Port-set pipe- number
Field Description Destination
Mac Addr
EC C
Show ip fib stack-unit
Example ECMP-Group Example Member-Info
VId Mac-Addr
Mac-Addr
Longer-prefixes
First-Hop
VId
Related Commands FieldDescription
Show ip flow
Number tcp
Src-port
Syntaxshow ip interface interface brief configured
Show ip interface
InterfaceOPTIONAL
Optional Enter the keyword brief to view a brief
States if Icmp unreachable messages are sent
Unreachables
Example Brief
Show ip management-route
Fields Description Method
Show ip management-route all connected summary static
Show ipv6 management-route
Show ip protocols
Show ip protocols
Show ip route
Command Modes Command History Longer-prefixes
List prefix-list
Routing-tag
Dist/Metric
Version Description 7.0
Field Description Undefined
Last Change
Example Example Summary Example vrf
Example With Weighted Ecmp Enabled
Ecmp
Show ip route list
Show ip route vrf vrf-namelist prefix-list
N2- Ospf
E2- Ospf
Column Heading Description Route Source
Show ip route summary
Show ip route vrf vrf-name summary
Active Routes
Active
Example Related Commands Column Heading Description Ospf
Show ip traffic
Show ip traffic all cp rp1 rp2
Security failures
Keyword Definition Unknown
Not a gateway
Bad options
Dell#show ip traffic
Dell Networking OS repeats the request three times. These
Packets are counted in encapsulation failed
Control Processor IP Traffic
Show tcp statistics
Show tcp statistics all cp rp1 rp2
17 dup
Field Description Rcvd
Checksum
Partially
Number of packet delayed
Initiated
Closed Total rxmt
Cam-ipv6 extended-prefix Max-IPv6-prefixes
IPv6 Basics
Cam-ipv6 extended-prefix
Max-IPv6
Clear ipv6 route
Clear ipv6 route vrf vrf-name * ipv6-address prefix- length
Maximum dynamic-routes-ipv6
Limit
Show cam-ipv6 extended-prefix
Ipv6 unicast-host-route
Version Description 70.0 Introduced on the S6000-ON 30.1
Ipv6 nd dns-server
Ipv6-RDNSS
Lifetime
Ipv6 route
Dellconf-if-te-1/1#ipv6 nd dns-server 10001
To support weighted Ecmp feature. Introduced on
Tag value
Show ipv6 route views the IPv6 configured routes
Show ipv6 route
Added support for VRF. Introduced on S6000-ON
RIP
BGP,LO
Nssa
829
IPv6 Access Control Lists IPv6 ACLs
Show cam-acl-egress
Show cam-acl-egress
Show cam-acl
+F394
Example Manual Profiles Related Commands
Parameters Defaults
Permit icmp
Permit
Syntaxpermit ipv6-protocol-number icmp ipv6 tcp udp
Ipv6 access-list
Ipv6 control-plane egress-filter
Ipv6 control-plane egress-filter
Ospfv3
L2acl
Cam-acl-egress default l2acl 1-4ipv4acl 1-4ipv6acl
Cam-acl-egress
Ipv4acl 1
Cam-acl default l2acl 1-10ipv4acl 1-10ipv6acl 0-10ipv4qos
Ipv4acl
L2qos
839
Intermediate System to Intermediate System IS-IS
Adjacency-check
Adjacency-check
Advertise
Parameters Level1-into
Level2-into
Type Password
Area-password
Area-password hmac-md5 encryption-type password
Parameters Hmac-md5
Clear config
Clear config
Tag
Clear isis
Clear isis vrf vrf-name tag * database traffic
Database
Clns host
Clns host name nsap
Nsap
Debug isis
Debug isis adj-packets
Debug isis
Debug isis local-updates
Syntaxdebug isis vrf vrf-name local-updates interface
Syntaxdebug isis vrf vrf-name snp-packets interface
Packets tied to that VRF. The command displays the SNP
Debug isis snp-packets
CSNP/PSNP related debugging information
Triggers command
Debug isis spf-triggers
Debug isis vrf vrf-name spf-triggers
Debug isis update-packets
Debug isis vrf vrf-name update-packets interface
Default-information originate
Always
Metric metric
Enter a description of the IS-IS routing protocol
Distance
Enter a description to identify the IS-IS protocol
Distribute-list
Name Interface
Ospf process-id
Command Modes Command History Related Commands
Distribute-list out
Bgp as number
Distribute-list redistributed-override
Distribute-list redistributed-override
Domain-password
Domain-password hmac-md5 encryption-type password
Do not specify an encryption type or hmac-md5
Graceful-restart ietf
Graceful-restart ietf
Ietf
Graceful-restart interval
Graceful-restart interval minutes
Graceful-restart restart-wait
Graceful-restart t1
Graceful-restart restart-wait seconds
Graceful-restart t2 level-1 level-2 seconds
Graceful-restart t2
Retry-times
Parameters Level-1, level-2
Adjacency
Graceful-restart t3
Graceful-restart t3 adjacency manual seconds
Manual
Hello padding multi-point point-to-point
To-point command
Hello padding
Point-to-point
Hostname dynamic
Hostname dynamic
Ip router isis
Ignore-lsp-errors
Ignore-lsp-errors
Ip router isis tag
Ipv6 router isis
Ipv6 router isis tag
Isis circuit-type
Syntaxisis circuit-type level-1 level-1-2 level-2-only
Level-1 level-2 command
Isis csnp-interval
Isis csnp-interval seconds level-1 level-2
Isis hello-interval
Isis hello-interval seconds level-1 level-2
Isis hello-multiplier
Syntaxisis hello-multiplier multiplier level-1 level-2
Multiplier
Isis hello padding
Isis hello padding
Syntaxisis ipv6 metric default-metriclevel-1 level-2
Default-metric
Isis ipv6 metric
Isis metric
Isis metric default-metric level-1 level-2
Configured on level-1-2, or it will be capped
Greater than 63, metric-style wide should be
Isis network point-to-point
Isis network point-to-point
Isis password
Syntaxisis password hmac-md5 password level-1 level-2
Isis priority
Isis priority value level-1 level-2
Is-type
Is-type level-1 level-1-2 level-2-only
Log-adjacency-changes
Log-adjacency-changes
Lsp-gen-interval
Level-l
Rval seconds
Interval
Initialwaitinte
Secondwaiti
Lsp-mtu
Lsp-mtu size
Lsp-refresh-interval
Lsp-refresh-interval seconds
Max-area-addresses number
Max-area-addresses
Max-lsp-lifetime
Max-lsp-lifetime seconds
Maximum-paths
Maximum-paths number
Transition
Metric-style
Parameters Narrow
Wide
Multi-topology
Transition command
Parameters Transition Defaults
Multi-topology transition
Net
Entity-title
Passive-interface
Passive-interface interface
Metric-type
Parameters Defaults Command Modes Connected
Redistribute
Internal
889
Redistribute bgp
AS number
Range is from 0 to 16777215. The default is
Redistribute ospf
Be redistributed. The range is from 1 to
Defaults Command Modes Command History Metric-type
Router isis
Version Description 1.0 Introduced Usage
Router isis vrf vrf-name tag
Set-overload-bit
Set-overload-bit
Example Router-Isis VersionDescription 70.0
Spf-interval level-2 120 20 25 exit-address-family
Show isis database
Example Address- FamilyIPv6
Lspid
LSP Seq Num
Field Description IS-IS Level-1
Level-2 Link State Database
LSP Checksum
Is OSPF.00
Lspid LSP
Seq Num LSP Checksum
Metric Is MT-IPv6 OSPF.00
Lspid
Syntax Command Modes Parameters Command History
Show isis graceful-restart detail
ATT/P/OL
Show isis hostname
Show isis vrf vrf-name hostname
Enter the keyword vrf followed by the name of the VRF to
Show isis interface
Show isis vrf vrf-name interface interface
Show isis neighbors
Command Modes Command History Usage Information Level-2
Circuit Id
Show isis protocol
Field Description Type
Show isis vrf vrf-name protocol
Multi Topology Routing is enabled in transition mode
Show isis traffic
Show isis vrf vrf-name traffic interface
LSPs flooded sent/rcvd
ItemDescription
Hellos sent/rcvd
LSPs CSNPs sent/ rcvd
Spf-interval
Displays the number of LSP authentication failures
Authentication Failures Example
Level-1/Level-2
Enter the maximum number of seconds between SPF
909
Link Aggregation Control Protocol Lacp
Clear lacp counters
Syntaxdebug lacp config events pdu interface-typein out
Debug lacp
Interface-type
Lacp long-timeout
Lacp long-timeout
Timeout command
Lacp port-priority
Lacp port-priority priority-value
Lacp system-priority
Lacp system-priority priority-value
Port-channel-protocol lacp
Port-channel-protocol lacp
Show lacp
Syntaxshow lacp port-channel-numbersys-id counters
Outofsync
Lacp PDU
Example Counter Related Commands
Dell# Dell#show lacp 1 counters Port
Marker PDU Unknown Illegal Xmit Recv Pkts Rx 200 Dell#
Mac-address-table aging-time
MAC Addressing Commands
Layer
Mac-address-table aging-time seconds
Mac-address-table static
Multicast
Output-range
No mac-address-table station-move refresh-arp
Mac-address-table station-move refresh-arp
Mac learning-limit
Addresslimit
Violation
Mac learning-limit learn-limit-violation
Syntaxmac learning-limit learn-limit-violation log shutdown
Shutdown
Mac learning-limit mac-address-sticky
Mac learning-limit mac-address-sticky
Shutdown-both
Parameters Defaults Command Modes Command History Log
Mac learning-limit station-move-violation
Offending
Show mac-address-table
Mac learning-limit reset
Mac learning-limit reset
Version Description 1.0 Introduced on the E-Series Usage
Parameters Command Modes Command History Address mac
Address/ mac-address , interface/ interface , or vlan
Aging-time
Column Heading Description VlanId
Mac Address
Address Static Address
Usage Information Example Count Related Commands
Line Beginning Description With MAC Entries
Total MAC
Show mac-address-table aging-time
Show mac learning-limit
Show mac-address-table aging-time vlan vlan-id
Optional Enter the keywords violate-action to
Default vlan-id vlan-id
Virtual LAN Vlan Commands
Default vlan-id
Slot/port Limit MAC count Drops Te 1/1
Description description
Interface Vlan
Default-vlan disable
Name
Vlan-name Enter up to 32 characters as the name of the Vlan
Display the current configuration of the selected Vlan
Show vlan
Dellconf-if-vl-100#show config
Updated to support OpenFlow
Id vlan-id
Column Heading Description Column 1 no
Heading
Example Example Vlan ID Column Heading Description
NUM
Status Description Q Ports Active Te 13/47
Tagged
Status Description Ports Inactive Te 1/10
All interfaces in Layer 2 mode are untagged
Track ip
Track ip interface
Untagged
Untagged interface
Far-End Failure Detection Fefd
Debug fefd
Debug fefd events packets interface
Legacy E-Series command
Syntaxfefd disableintervalmode aggressivenormal
Fefd
Fefd disable
Fefd disable
Fefd interval
Fefd interval seconds
Fefd mode
Fefd mode normal aggressive
Aggressive
Fefd reset interface
Fefd reset
Legacy E-Series command Related
Optional Enter the following keywords and slot/port or
Fefd-global interval seconds
Fefd-global interval
Fefd-global
Syntaxfefd-global interval secondsmode normal aggressive
Enter the keyword interval followed by the number
Show fefd
Show fefd interface
Example Related Commands FieldDescription
Interface Mode Interval State
Llpd Commands
Link Layer Discovery Protocol Lldp
Advertise dot1-tlv
Advertise dot3-tlv
Vlan-name
Advertise dot3-tlv max-frame-size
Clear lldp counters
Clear lldp counters interface
Clear lldp neighbors
Clear lldp neighbors interface
Allevents packet brief detail tx rx both command
Debug lldp interface
Enable or disable Lldp
Hello
Multiplier
Mode tx rx
Mode
Multiplier integer
Protocol lldp Configuration
Integer
Protocol lldp
Protocol lldp Interface
No protocol lldp
Show lldp neighbors
Show lldp neighbors interface detail
Show lldp statistics
R1conf-if-te-1/31#do show lldp neighbors
Show lldp statistics
Layer2priority
LLDP-MED Commands
Advertise med guest-voice
DSCPvalue
Advertise med guest-voice-signaling
Advertise med guest-voice-signaling vlan-id layer2priority
DSCPvalue priority-tagged number
Based value
Advertise med location-identification
Coordinate
Civic-based
Advertise med power-via-mdi
Advertise med power-via-mdi
Advertise med softphone-voice
Advertise med streaming-video
Advertise med video-conferencing
Advertise med video-signaling
Advertise med voice
Advertise med voice-signaling
975
Arp for Multicast MAC Address
Table static command
Microsoft Network Load Balancing
Multicast-mac
Mac-address-table static for Multicast MAC Address
Defaults Command Modes Command History Example Multicast
Ip vlan-flooding
Ip vlan-flooding
Clear ip msdp peer peer address
Multicast Source Discovery Protocol Msdp
Clear ip msdp peer
Peer address
Clear ip msdp sa-cache
Rejected-sa
Clear ip msdp statistic peer peer-address
Clear ip msdp statistic
Ip msdp cache-rejected-sa
Peer-address
Peer address
Ip msdp default-peer
Ip msdp default-peer peer address list name
List name
Ip msdp log-adjacency-changes
Ip msdp log-adjacency-changes
Ip msdp mesh-group
Ip msdp mesh-group name peer address
Ip msdp originator-id
Ip msdp originator-id interface
Ip msdp peer
Connect
Sa-limit
Defaults Not configured
Ip msdp redistribute
Ip msdp redistribute list acl-name
Syntaxip msdp sa-filter in out peer-addresslist access-list
Ip msdp sa-filter in out name command
Ip msdp sa-filter
Ip msdp sa-limit
Ip msdp sa-limit number
Ip msdp shutdown
Ip msdp shutdown peer address
Ip multicast-msdp
Ip multicast-msdp
Show ip msdp
Peer peer
Sa-cache
Show ip msdp sa-cache rejected-sa
Example Sa
Cache
994
Multiple Spanning Tree Protocol Mstp
Debug spanning-tree mstp
Parameters All Bpdu Interface in out Events
Multiple Spanning Tree
Forward-delay
Forward-delay seconds
Hello-time
Hello-time seconds
Max-age
Max-age seconds
Max-age
Vlan range
Msti
Msti instance
Bridge-priority
Name
Name region-name
Tree mstp command
Protocol spanning-tree mstp
Protocol spanning-tree mstp
Enter the revision number for the MST configuration.
Revision
Revision range
Dellconf-mstp#show config
No disable Name CustomerSvc revision Msti 10 Vlan
MST region name CustomerSvc
Show spanning-tree mst configuration
Dell#show spanning-tree mst configuration
Msti VID
Instance
Show spanning-tree msti
Show spanning-tree msti instance-numberbrief guard
Guard
Example EDS and LBK
P2P
Field Description Interface Name
Spanning-tree
Usage Information Example Guard
Sts
Spanning-tree msti
Cost cost
DefaultsDisabled
Tc-flush-standard
Syntaxtc-flush-standard
1011
IPv4 Multicast Commands
Multicast
Clear ip mroute
Isis rip static ip-address tag null 0 distance command
Ip mroute
Null
Ip-address Distance
Ip multicast-limit
Static ip- address
Ip multicast-limit vrf vrf-name limit
Ip multicast-limit command is reached
Ip multicast-routing
Ip multicast-routing vrf vrf-name
Show ip mroute
Group-address source- address
Summary Vlt
1018 Multicast
Interface list
Show ip rpf
Outgoing
Show ip rpf
1020 Multicast
Neighbor Discovery Protocol NDP
IPv6 Router Advertisement RA Guard
Clear ipv6 neighbors
Clear ipv6 neighbors vrf vrf-name ipv6-address interface
Device-role
Defaults Command Modes History
Debug ipv6 nd ra-guard
Interfacetype
Router
Parameters Defaults Command Modes History
Hop-limit
Hop-limit maximum minimum limit
Parameters Policy policy
Ipv6 nd ra-guard enable
Ipv6 nd ra-guard attach-policy
Vlan vlan
Ipv6 neighbor
Defaults Command Modes History Related Commands
Ipv6 nd ra-guard policy
Ipv6 nd ra-guard policy policy-name
Neighbor vrf vrf-name ipv6-address interface interface
Hardwareaddr
Ess
Match ra
Managed-config-flag
Managed-config-flag on off
Off
Access-list
Ipv6-prefix-list
Ipv6-mac
Defaults Command Modes History Related Commands Ipv6-mac
Parameters Defaults Command Modes History Related Commands
Other-config-flag
Other-config-flag on off
Reachable-time
Retrans-timer value
Retrans-time
Router-lifetime value
Router-lifetime
Router-preference maximum
High
Defaults Command Modes History Medium
Show ipv6 nd ra-guard policy
Trusted-port Dellconf-raguardpolicylist#
Show ipv6 nd ra-guard policy policy-name
Show ipv6 neighbors
Trusted-port Interfaces Te 1/1 Dell#
Stale
Delay
Vlan CPU
Reach
Trusted-port
Syntaxtrusted-port
Debug track
IPv4 Object Tracking Commands
Object Tracking
Object-id
Delay
Delay up seconds down seconds
Description text
Show running-config track
Show running-config track object-id
Ip route
Resolution
Show track
OutputDescription
Address Object is Up
Up/Down state of tracked object for example, IPv4
Hoursminutesseconds
Threshold metric up number down number
Threshold metric
VLAN100
Up number
Track interface ip routing
Track object-idinterface interface ip routing
Track interface line-protocol
Syntaxtrack object-idinterface interface line-protocol
Track ip route metric threshold
Prefix-len
Track ip route reachability
Enter an IPv4 address in dotted decimal format. The valid
Track resolution ip route
Isis resolution
Resolution
IPv6 Object Tracking Commands
Show track ipv6 route
Show track ipv6 route brief
Dell#show track ipv6 route brief
Track object-id
Ip-address , IPv6
ResId Resource Parameter State LastChange
Track interface ipv6 routing
Syntaxtrack object-idinterface interface ipv6 routing
Track ipv6 route metric threshold
Threshold
Track ipv6 route reachability
Enter the ID number of the tracked object. Use the range to
Track resolution ipv6 route
Track resolution ipv6 route isis resolution-value ospf
Table for Isis routes to a scaled metric
1058 Object Tracking
Open Shortest Path First OSPFv2 and OSPFv3
OSPFv2 Commands
Area default-cost
Area-id
Redistribution
Area nssa
Pre
Originate
Area range
Area area-id range ip-address mask not-advertise
Not-advertise
Area stub
Area area-id stub no-summary
No-summary
Auto-cost
Auto-cost reference-bandwidth ref-bw
Ref-bw
Clear ip ospf
Clear ip ospf process-idvrf vrf-name process
Clear ip ospf statistics
Clear ip ospf process-id vrf vrf-name statistics interface
Router-id
Debug ip ospf
Bfd
Spf
Added the database-timer rate-limit option for the S4810
Field Description 814
Chk
Field Description Rid
Aid
Aut
Default-information originate
Parameters Defaults Command Modes Command History Always
Type-value
Version Description 19.0
Add a description about the selected Ospf configuration
Syntaxdistance weight ip-address mask access-list-name
Distance
Distance ospf
Distance ospf external dist3 inter-area dist2 intra-area
Distribute-list
Redistribute command
Parameters Enter the name of a configured prefix list
Optional Enter one of the following keywords and slot
Distribute-list out
Fast-convergence
Fast-convergence number
Flood-2328
Flood-2328
Graceful-restart grace-period
Graceful-restart grace-period seconds
Graceful-restart helper-reject
Graceful-restart helper-reject ip-address
Planned-only
Graceful-restart mode
Graceful-restart mode planned-only unplanned-only
Unplanned
Parameters Role helper
Graceful-restart role
Graceful-restart role helper-only restart-only
Role restart
Ip ospf auth-change-wait-time
Ip ospf authentication-key
Syntaxip ospf authentication-key encryption-type key
Ip ospf auth-change-wait-time seconds
Type Key
To return to default value, use the no ip ospf cost command
Ip ospf cost
Ip ospf cost cost
Ip ospf dead-interval
Ip ospf dead-interval seconds
Ip ospf hello-interval
Ip ospf hello-interval seconds
Ip ospf message-digest-key
Ip ospf message-digest-key keyid md5 key
Keyid
Ip ospf mtu-ignore
Ip ospf mtu-ignore
Ip ospf network
Ip ospf network broadcast point-to-point
Broadcast
Ip ospf priority
Ip ospf priority number
Ip ospf retransmit-interval
Ip ospf retransmit-interval seconds
Log-adjacency-changes
Ip ospf transmit-delay
Ip ospf transmit-delay seconds
Syntaxlog-adjacency-changes
Enable the software to forward packets over multiple paths
Mib-binding
Mib-binding
Introduced support for OSPFv3 on the S4810 and Z9000
Information MIB manager, the first Ospf process is used
Network area
Passive-interface default interface
Passive-interface
Passive-interface default
No passive-interface interface
Enter the keyword connected to specify that information
Redistribute bgp
Enter the autonomous system number. The range is from
Redistribute isis
Tag tag-value
Router-id
Router-id ip-address
Ip-address Enter the router ID in the IP address format
Vrf name
Router ospf
Router ospf process-idvrf vrf name
Added support for OSPFv3 on the S4810 and Z9000
Dellconf#router ospf Dellconf-routerospf#
Show ip ospf
Dellconf-routerospf#show config
Process ID is entered, command applies only to the first
Version Description Pre Introduced on the E-Series Example
Line Beginning Description With Routing
Show ip ospf asbr
Show ip ospf process-id vrf vrf-name asbr
Show ip ospf database
Age
Field Description Link ID
ADV Router
Seq#
Show ip ospf process-id vrf vrf-name database asbr-summary
Show ip ospf database asbr-summary
172.16.1.0 13.1.1.1 148 0x8000006d 0x533b Dell
Link-state-id
Link State ID
Field Description LS Age
LS Type
Advertising Router
Show ip ospf database external
Show ip ospf process-id vrf vrf-name database external
Pre-6.1.1.1
LS Seq Number
Forward Address
Example Related Commands Field Description Network Mask
Metrics Type
External Route
Show ip ospf database network
Show ip ospf process-id vrf vrf-name database network
Attached Router
Show ip ospf database nssa-external
Options TOS-capability, No DC, E
Show ip ospf process-id vrf vrf-name database nssa-external
Show ip ospf database opaque-area
1118
Opaque Type
Example Related Commands Description Advertising Router
Show ip ospf database opaque-as
Opaque ID
Show ip ospf database opaque-link
Parameters Command Modes Command History Related Commands
Show ip ospf database router
Show ip ospf process-id vrf vrf-name database router link
Link Data
Number of Links
Link connected
Number of TOS
Show ip ospf database summary
View LSA routing information corresponding to the Ospf
LS type Summary Network
Dell#show ip ospf 100 database summary
Summary Network Area
Checksum 0xb5a2
Show ip ospf interface
TOS
GigabitEthernet
Transmit Delay
Timer intervals
Designated
Show ip ospf neighbor
000032 Te 1/1 0.2 192.10.10.2
Dead
FULL/DR
000037 Te 1/2 0.1
Show ip ospf routes
20.20.20.1 1 FULL/DROTHER000036 192.10.10.4 Te 1/3 Dell#
Show ip ospf process-id vrf vrf-name routes
Show ip ospf statistics
1133
MD5-Error
Error Type Description IntfDown
Auth-Error
Conf-Issue
Socket
Error Type Description Seq-no
Example Usage Information
Overflow
Show ip ospf timers rate-limit
Show ip ospf process-id vrf vrf-name timers rate-limit
Show ip ospf topology
Version Description 8.0 Introduced on the S4810 Example
Show ip ospf process-id vrf vrf-name topology
Summary-address
Timers spf
Delay
Hold-interval
Timers throttle lsa all
Start-interval
Max-interval
Timers throttle lsa arrival
Timers throttle lsa arrival arrival-time
Arrival-time
Area area-id
OSPFv3 Commands
Area authentication
Ipsec spi number
Introduced on the S4810 and Z9000
Area encryption
Defaults Command Modes Key Null
Clear ipv6 Ospf vrf vrf-name process
Clear ipv6 ospf process
Debug ipv6 ospf bfd
No debug ipv6 ospf bfd interface
Multiplier 0, role 0, Disable
OSPFv3INFO Received Interface mode bfd config
Command on interface Te 1/2 Enable 1, interval 0, minrx
Dellconf-if-te-1/2#do debug ipv6 ospf bfd te 1/2
Debug ipv6 ospf packet
Debug ipv6 ospf packet events interface
Area ID
Lines Beginning Description With or Including OSPFv3
Router ID
Chksum
Period
Parameters Planned-only
Ipv6 ospf area
Ipv6 ospf process id areaarea id
Parameters Null
Ipv6 ospf authentication
Ipv6 ospf authentication null ipsec spi number MD5 SHA1
Ipsec spi number
Ipv6 ospf cost
Interface-cost
Ipv6 ospf dead-interval
Ipv6 ospf dead-interval seconds
Key- encryption- type Authentication- algorithm
Ipv6 ospf encryption
1157
Ipv6 ospf graceful-restart helper-reject
Ipv6 ospf graceful-restart helper-reject
Ipv6 ospf hello-interval
Helper-reject
Ipv6 ospf priority
Ipv6 ospf priority number
Ipv6 router ospf
Ipv6 router ospf process-idvrf vrf-name
Process-id Vrf vrf-name
Max-metric router-lsa
Series, E-Series, Z-Series, S4810
Wait-time
Interface interface command
Defaults Command Modes History Usage Information
1165
Ip-address Enter the router ID in the dotted decimal format
Show crypto ipsec policy
Name name
Policy
Show crypto ipsec policy Command Fields
Show crypto ipsec sa ipv6
Show crypto ipsec sa ipv6 interface interface
Interface TenGigabitEthernet 1/1
Dell#show crypto ipsec policy
Dell#show crypto ipsec sa ipv6
Status Active
Number Vrf vrf-name
Show ipv6 ospf database
Process
Database- summary Grace-lsa
1172
Show ipv6 ospf interface
000037 Te 1/4 63.114.8.36
Number Vrf vrf-name Interface
Show ipv6 ospf neighbor
Syntaxshow ipv6 ospf process-number vrf vrf-name neighbor
Process- number Vrf vrf-name Interface
000038 63.114.8.36 Dell#
Policy-based Routing PBR
Ip redirect-group
Ip redirect-group redirect-list-name
Ip redirect-list
Redirect-list
Protocol-type
Tunnel-id
Redirect
Tunnel
Track
Optional For TCP and UDP parameters only. Enter one
Command Version Description History 70.0
Seq
Source port
Source-port
Show cam pbr
Port-range
Show ip redirect-list redirect-list-name
Enter the name of a configured Redirect list
Show ip redirect-list
Modes Exec Privilege
1186 Policy-based Routing PBR
Clear ip pim rp-mapping
PIM-Sparse Mode PIM-SM
IPv4 PIM-Sparse Mode Commands
Clear ip pim vrf vrf-name rp-mapping rp-address
Clear ip pim tib
Clear ip pim vrf vrf-name tib group
Group
Packet in out
Debug ip pim
Bsr
Register
Ip pim bsr-border
Ip pim bsr-border
Clear ip pim rp-mapping command
Ip pim bsr-candidate
Hash-mask
Ip pim dr-priority
Ip pim dr-priority priority-value
Syntaxip pim vrf vrf-name join-filter ext-access-list
Ext-access-list
Ip pim join-filter
Ip pim neighbor-filter
Version Description 50.0
Ip pim query-interval
Ip pim query-interval seconds
Syntaxip pim vrf vrf-name register-filter access-list
Ip pim register-filter
Ip pim vrf vrf-name rp-address address group-address group
Command before creating the access-list
Ip pim rp-address
Group-address
Ip pim rp-candidate
Syntaxip pim vrf vrf-name rp-candidate interface priority
Ip pim sparse-mode
Ip pim sparse-mode
Ip pim sparse-mode sg-expiry-timer
Ip pim vrf vrf-name sparse-mode sg-expiry-timer seconds
Ip pim vrf vrf-name ssm-range accesslistname
Accesslistna
Ip pim ssm-range
Introduced on the S6000-ON. Added support for VRF on
Ip pim spt-threshold
Show ip pim bsr-router
Infinity
Parameters Command Modes Command History Example
Show ip pim interface
Show ip pim vrf vrf-name interface
Nbr Count
Field Description Address
Ver/Mode
Query Intvl
Show ip pim neighbor
Show ip pim vrf vrf-name neighbor
Uptime/expires
Show ip pim rp
Field Description Neighbor address
Ver
Command Modes Command History Example Example Mapping
Exmaple
Show ip pim ssm-range
Show ip pim summary
Group Address / MaskLen
PIM-SNOOPING
Show ip pim tib
Source-address
RPF neighbor
1213
Command Parameters Description
Port Monitoring
Rpm
Monitor session
Session-ID
Erpm
Set ip ttl
Ttlvalue
Dscp TTL
Dellconf-mon-sess-1#show config
Session
Monitor
Parameters Defaults Command Modes Command History Example
Show monitor session
Show monitor session session-ID
Show running-config monitor session
Syntaxshow running-config monitor session session-ID
Interface direction rx tx both command
Source port monitoring
Parameters Source
Enter the keyword direction then one of the packet
Private Vlan Pvlan
Private Vlan Concepts
Ip local-proxy-arp
No ip local-proxy-arp
Private-vlan mode
Syntaxno private-vlan mode community isolated primary
Isolated
Private-vlan mapping secondary-vlan
Syntaxno private-vlan mapping secondary-vlan vlan-list
Vlan-list
Switchport mode private-vlan
Parameters Host
Promiscuous
Enter the keyword trunk to configure the selected port or
Per-VLAN Spanning Tree Plus PVST+
Protocol spanning-tree pvst enter PVST+ mode
Dellconf-pvst#do show spanning-tree pvst vlan 5 brief
Extend system-id
Extend system-id
Vlan
Protocol spanning-tree pvst
Protocol spanning-tree pvst
Show spanning-tree pvst
Show spanning-tree pvst vlan vlan-id brief guard
Usage Information Example Brief VersionDescription
Example Example EDS/ LBK
TenGigabitEthernet 1/1 of Vlan 2 is Lbkinc discarding
TenGigabitEthernet 1/1 of Vlan 2 is Pvidinc discarding
Example EDS/ Pvid Example Guard Related Commands
Spanning-tree pvst
Loopguard Te 1/3/1 EDSShut Bpduguard
Cost number
1237
Dellconf-if-te-1/1#spanning-tree pvst vlan 3 cost
Spanning-tree pvst err-disable
Spanning-tree pvst err-disable cause invalid-pvst-bpdu
Dellconf-if-te-1/1#end
Tc-flush-standard
Vlan bridge-priority
Vlan vlan-rangebridge-priority value
Vlan forward-delay
Vlan vlan-rangeforward-delay seconds
Vlan hello-time
Hello-time
Vlan max-age
Max-age
1244
Qos-rate-adjust
Quality of Service QoS
Global Configuration Commands
Qos-rate-adjustment overhead-bytes
Service-class bandwidth-percentage
Service-class dot1p-mapping
Show qos dot1p-queue-mapping
Parameters Queue
Strict-priority queue
Strict-priority queue unicast number
Dot1p-priority priority-value
Per-Port QoS Commands
Dot1p-priority
Dot1p Queue Number
Committed
Rate police
Parameters Kbps
Rate Burst-KB
Rate shape
Rate shape kbps rate burst-KB
Rate
Service-class dynamic dot1p
Service-class dynamic dot1p
Policy-Based QoS Commands
Bandwidth-percentage
Buffer-stats-snapshot
Bandwidth-percentage percentage
Class-map
No buffer-stats-snapshot
Match-all
Class-map
Layer2
Clear qos statistics
Clear qos statistics interface-name
Pre- 7.7.1.0 Introduced Related Commands
Set-ip-dscp
Match ip access-group
Access-group
Set-color value
Ip-any
Match ip dscp
Syntaxmatch ip ipv6 ip-any dscp dscp-listset-ip-dscp value
Dscp-list
Match ip precedence
Match ip dscp and match ip precedence commands are mutually
2,3,4,5,6,7 or match ip dscp 0-7 command
Precedence-list
Match mac access-group
Usage Information Related Commands Version Description 70.0
Match mac access-group mac-acl-name
Match mac dot1p
Match mac dot1p dot1p-list
Dot1p-list Enter a dot1p value. The range is from 0 to
Number Enter the Vlan ID. The range is from 1 to
Match mac vlan
Policy-aggregate
Qos-policy
Policy-map-input policy-map-name cpu-qos layer2
Name cpu-qos layer2 command
Policy-map-input
Cpu-qos
Policy-map-output
Policy-map-output policy-map-name
Qos-policy-input
Qos-policy-input qos-policy-namecpu-qos layer2
Qos-policy-output
Qos-policy-output qos-policy-name
Rate-police
Rate-police kbps committed-rate burst-KB peak kbps peak
Rate-shape
Rate-shape kbps rate burst-KB
Service-policy input
Service-policy input policy-map-name layer2
Service-policy output
Service-policy input policy-map-name command
Service-policy output policy-map-name
Class-map
Service-queue
Queue-id
Input only
Parameters Ip-dscp value
Set
Show qos class-map
Mac-dot1p
Show qos policy-map
Syntaxshow qos policy-map summary interface detail
Defaults Command Modes History Example IPv4 Example IPv6
CM1 CM2 CM3 CM4 CM5 CM6 CM7
PM1
Show qos policy-map-input
Summary IPv4
PM2
Show qos policy-map-output
Show qos policy-map-output policy-map-name qos-policy-output
Show qos qos-policy-input qos-policy-name
Show qos qos-policy-input
Show qos qos-policy-output
Qos-policy Enter the QoS policy name Name None
Syntaxshow qos statistics wred-profile interface interface
Show qos statistics
Dell#show qos qos-policy-output
Wred-profile
Show qos wred-profile
Show qos wred-profile wred-profile-name
Service-class buffer shared-threshold-weight
Enter a weight for the queue on the shared buffer as a
Number in the range of 1 to
Unitnumber
Parameters Enter the policy map name
Stack Optional Enter the keyword stack-unit then the stack
Unit slot number
Following describes the test cam-usage service-policy input
Portpipe
Field Description Stack-unit
Status Allowed
Threshold
Field Description Estimated CAM
L2ACL
Min number
Diffserv
Related Wred-profile creates a Wred profile Commands
Trust
Dot1p
Wred
Wred yellow green profile-name
Parameters Yellow green
Wred ecn
Wred ecn
Wred weight
No wred weight number
Parameters Weight
Ftos conf-qos-policy-out # wred weight
Wred-profile
Wred-profile
Pps
Packets
Peak-rate
Service-pool wred
Dscp Color Map Commands
String
Dscp
Dscp yellow red list-dscp-values
Red
Qos dscp-color-map map-name
Qos dscp-color-map
Dellconf-dscp-color-map# dscp yellow 9,10,11,13,15,16
Dellconf#qos dscp-color-map mymap
Qos dscp-color-policy
Dscp-color-policycolor-map-profile-name
Show qos dscp-color-policy
Show qos dscp-color-policy summary interface detail
Show qos dscp-color-map
Map-name Enter the name of the color map
Routing Information Protocol RIP
Auto-summary
Auto-summary
Clear ip rip
Debug ip rip
Clear ip rip
Trigger
Default-metric
Enter a description of the RIP routing protocol
Syntaxdistance weight ip-address mask prefix-name
Prefix-name Optional Enter a configured prefix list name
Configure a filter for outgoing routing updates
Optional Enter the keyword connected to filter only
Ip poison-reverse
Ip poison-reverse
Ip rip receive version
Ip rip receive version 1
Ip rip send version
Ip rip send version 1
Ip split-horizon
Ip split-horizon
Ip poison-reverse sets the prefix for RIP routing updates
Neighbor
Network
Offset-list
Offset
Output-delay
Output-delay delay
This command is intended for low-speed interfaces
Redistribute connected static
Redistribute isis
Internal metric metric-value route-map map-name
Route-map map-name command
Redistribute ospf process-id match external 1 2 match
External 1 2 match internal metric metric-value
Router rip
Router rip
Dellconf#router rip Dellconf-routerrip#
Dellconf-routerrip#show config
Show ip rip database
Show ip rip database ip-address mask
Show running-config rip
Show running-config rip
Timers basic
Update
Invalid
Holddown
Flush
Version
Version 1
Rmon alarm
Remote Monitoring Rmon
Defaults Command Modes Command History Owner string
Number Variable Interval
Delta Absolute
Owner name
Rmon collection history
ControlEntry
Buckets
Rmon collection statistics
Rmon event
Rmon event number log trap community description string
Trap
Rising-threshold value event-number falling-threshold value
Rmon hc-alarm
Rmon hc-alarm number variable interval delta absolute
Delta
Event-number
Defaults Command Modes Command History Rising
Threshold value
Falling
Show rmon
Show rmon alarms
Show rmon alarms index brief
Show rmon
Index
Show rmon events
Show rmon events index brief
Example Index Example Brief Version Description 1.0
Show rmon hc-alarm
Show rmon hc-alarm index brief
Example Index VersionDescription 70.0
Snmp OID
Dell#show rmon hc-alarm brief
Show rmon history
6.1.2.1.1.3
Show rmon log
Example Index Example Brief VersionDescription
Show rmon log index brief
Show rmon statistics
Usage Information Example Index Example Brief
Show rmon statistics index brief
Command Modes Command History Example Index
Bytes packets overflow
Dell#show rmon statistics br
Bridge-priority priority-value
Rapid Spanning Tree Protocol Rstp
Bridge-priority
Priority-value
Parameters Command Modes All
Debug spanning-tree rstp
Bpdu interface in out
Enter a description of the rapid spanning tree
Disable Rstp globally on the system
Hello-time milli-second seconds
Milli-second
Protocol spanning-tree rstp
Protocol spanning-tree rstp
Disable disables Rstp globally on the system
Show spanning-tree rstp
Dellconf-rstp#show config
No disable
Bridge-priority
Te 4/8 Root 128.426 128 20000 FWD
Down EDS Shut
Te 4/1 Desg 128.419 128 20000 FWD
Te 4/9 Altr 128.427 128 20000 BLK
Spanning-tree rstp
BLK
Defaults Command Modes Command History Loopguard
Edge-port Bpduguard Shutdown-on- violation Priority priority
Introduced the hardware shutdown-on-violation options
Configuration conf-rstp
AAA Accounting Commands
Security
Aaa accounting
Role-name
Aaa accounting Suppress Null-username command
Aaa accounting suppress
Aaa accounting Suppress Null-username
Accounting
Accounting exec commands level role role-name method
Accounting exec or aaa accounting commands
Exec
Aaa radius group
Aaa radius group group-name
Show accounting
Show accounting
Authorization and Privilege Commands
Authorization
Authorization exec commands level role role-name
Aaa authorization commands
Parameters Defaults Command Modes Command History Commands
Role role-name
Aaa authorization config-commands
Aaa authorization config-commands
Aaa authorization config-commands command
Aaa authorization exec
Reset
Privilege level Configuration mode
Syntaxprivilege mode level level command reset command
Mode
Privilege level Line mode
Privilege level level
Service obscure-passwords
Obscure Password Commands
Service obscure-passwords
Passwords command
Parameters Default
Authentication and Password Commands
Aaa authentication enable
Method
Aaa authentication login
Method4
Access-class access-list-name
Syntaxenable password level level encryption-type password
Enable password
Name Not configured
Parameters Level level
Level and use the privilege level Configuration mode command
Enable restricted
Enable restricted encryption-type password
Encryption- type Password
Enable secret
Syntaxenable secret level level encryption-typepassword
Login authentication
Syntaxlogin authentication method-list-name default
Login authentication command
Password
Password-attributes
Character
Max-retry
Lockout-period
Restriction
Service password-encryption
Service password-encryption
Dell#show privilege
Commands Command modes
Show privilege
Current privilege level is
Show users all
Using
Show users
Field Description Untitled
Timeout login response
Timeout login response seconds
Username
Access-class
Nopassword
Secret
Privilege level
Ip radius source-interface
Radius Commands
Debug radius
Debug radius
Deadtime command
Radius-server deadtime
Radius-server deadtime seconds
Radius-server group
Radius-server host
Hostname Ipv4-address ipv6-address
Encryption- type key
Radius Server Group Configuration
Radius-server vrf
Dellconf-radius-group#no radius-server host
Syntaxradius-server vrf vrf-name source-interface interface
Radius-server key
Radius-server key encryption-type key
For the key entered. The options are
Radius-server retransmit
Radius-server timeout
Radius-server timeout seconds
Radius-server retransmit retries
TACACS+ Commands
Tacacs-server group
Aaa tacacsgroup group-name
Debug tacacs+
Debug tacacs+
Ip tacacs source-interface
Ip tacacs source-interface interface
Tacacs-server group group-name
Defaults Command Modes Key key
Port number timeout seconds key key
Timeout
Tacacs-server host
Tacacs-server key
Tacacs-server key encryption-type key
Tacacs-server vrf
Syntaxtacacs-server vrf vrf-namesource-interface interface
Port Authentication 802.1X Commands
Tacacs Server Group
Dot1x authentication Configuration
Dot1x authentication Interface
Dot1x auth-fail-vlan
Dot1x auth-server
Dot1x guest-vlan
Reauthentication
Dot1x mac-auth-bypass
No dot1x mac-auth-bypass
Dot1x max-eap-req
Dot1x port-control
Dot1x quiet-period
Dot1x reauthentication
Dot1x server-timeout
Dot1x reauth-max
Dot1x supplicant-timeout
Dot1x tx-period
Show dot1x interface interface
Auth-Fail Vlan Disable Auth-Fail Vlan id
Show dot1x interface
Unauthorized
SSH Server and SCP Commands
Forceauthorized
Auth PAE State Initialize Backend State Dell#
Rsa
Crypto key generate
Crypto key generate rsa rsa1
Rsa1
Crypto key zeroize rsa
Crypto key zeroize rsa
Debug ip ssh client server
Debug ip ssh
Ip scp topdir
Ip scp topdir directory
Ip ssh authentication-retries
Ip ssh authentication-retries
Ip ssh connection-rate-limit
Ip ssh connection-rate-limit
Ip ssh hostbased-authentication
Ip ssh hostbased-authentication enable
Ip ssh key-size
Ip ssh password-authentication
Parameters Enable
512-869
Ip ssh rekey time rekey-interval volume rekey-limit
Ip ssh rekey
Time minutes
Ip ssh pub-key-file
Ip ssh pub-key-file Word
Ip ssh rhostsfile
Ip ssh rsa-authentication Config
Ip ssh rsa-authentication enable
Ip ssh server
Ciphers cipher
List
Hmac-sha1 Hmac-sha1-96 Hmac-sha2-256 Hmac-sha2-256-96
Introduced the cipher, kex and mac options on the Z9000
Dell# conf
Dellconf# ip ssh server enable
Ip ssh server vrf
Dellconf# ip ssh server port
Dellconf#no ip ssh server vrf
Ip ssh source-interface
Dellconf#ip ssh server vrf vrf1
Dellconf#ip ssh server vrf management
Dellconf#ip ssh source-interface tengigabitethernet 1/42
Dellconf#do ssh 10.10.10.2 -l admin
Ip ssh vrf
Dellconf#no ip ssh source-interface
Show crypto
Show crypto key mypubkey rsa rsa1
Mypubkey
Show ip ssh
Show ip ssh client-pub-keys
RSA
Hmac
Nux-1.force10networks.com
Show ip ssh rsa-authentication
Show ip ssh rsa-authentication my-authorized-keys
EFPaHiygd8U/FXict61jWs84Co1UTsAgRzDJ9aUSS75TVac=
Ssh
Ipv4 address
Cipher
MHMAC
Pport
Secure Dhcp Commands
Clear ip dhcp snooping binding
Ip dhcp relay information-option trust-downstream vrf
1446
Defaults Command Modes Interface type
Slot/port lease time
1448
Ip dhcp snooping vlan
No ip dhcp source-address-validation
No ip dhcp snooping vlan name
Show ip dhcp snooping binding
Inherit existing
Role-Based Access Control Commands
Aaa authorization role-only
Version Description 70.0
Addrole
Role mode addrole deleterole role-name reset command
Role
Deleterole
Show role mode mode command
Mode mode
Show role
Show userroles
Dell#show role mode configure management crypto-policy
Role access secadmin, sysadmin
Userrole
1455
Service Provider Bridging
Debug protocol-tunnel
Protocol-tunnel
Out both
Protocol-tunnel rate-limit rate stp
Stp
Protocol-tunnel destination-mac
Rate-limit rate
Protocol-tunnel destination-mac xstp address
Protocol-tunnel enable
Protocol-tunnel enable
Protocol-tunnel rate-limit
Protocol-tunnel rate-limit rate
Protocols Interface 1000
Show protocol-tunnel
Show protocol-tunnel vlan vlan-id
STP,PVST
LACP,DOT1X
LLDP,GVRP
MMRP,MVRP
OAM,PAUSE
SFlow
Format for IPv4 or xxxxx format for IPv6
Defaults Command Modes Agent-addr ip- address ipv6- address
Sflow collector
Fields of zeros
1465
Sflow enable
Sflow enable Global
Sflow ingress-enable
Sflow ingress-enable
Sflow extended-switch enable
Sflow extended-switch enable
Sflow max-header-size extended
Sflow max-header-size extended
Extended
Sflow polling-interval Global
Dellconf#sflow max-header-size extended
Sflow polling-interval interval value
Sflow polling-interval Interface
Sflow sample-rate Global
Sflow sample-rate value
Sflow sample-rate Interface
Display the current sFlow configuration Syntax
Show sflow
Show sflow interface
1474
Snmp Commands
Simple Network Management Protocol Snmp and Syslog
Show snmp
Show snmp
Show snmp engineID
Show snmp engineID
Show snmp group
Show snmp group
Show snmp user
Show snmp user
Series legacy command Example
Snmp ifmib ifalias long
Snmp ifmib ifalias long
Ipv6 access
Snmp-server community
Security-name
1481
Snmp-server contact
Notification
Snmp-server enable traps
VersionDescription Series legacy command
Option
Snmp-server engineID
Linkdown Linkup
Local engineID
Remote ip- address
Udp-port port- number engineID
Snmp-server group
Groupname
Name ipv6 Access-list
Snmp-server host
Version 1 2c
Traps
Informs
Udp-port port
Added support for config and ecmp traps
Snmp-server location
Snmp-server location text
Snmp-server packetsize
Snmp-server packetsize byte-count
Byte-count
Snmp-server trap-source
Snmp-server trap-source interface
Snmp-server user
Remote ip
Encrypted
Auth-password
Priv password
Md5 sha
Up to 16 characters long
Optional Enter the keyword ipv6 then the IPv6 access list
Optional Enter both an IPv4 and IPv6 access list name
Name a string up to 16 characters long
Snmp-server user for AES128-CFB Encryption
Aes128
View-name
Snmp-server view
Syntaxsnmp-server view view-nameoid-treeincluded excluded
Oid-tree
Snmp-server vrf vrf-name
Snmp-server vrf
Excluded
Associate an Snmp agent with that VRF
Snmp trap link-status
Snmp trap link-status
Syslog Commands
Clear logging
Clear logging
Default logging buffered
Commands Buffer
Clear logging auditlog
Default logging console
Default logging console
Default logging monitor
Series legacy command Related
Default logging trap
Default logging trap
Logging
Critical , errors , warnings , notifications
Logging buffered
Logging buffered level size
Logging console
Logging console level
Errors , warnings , notifications , informational , or
Logging extended
Logging facility
Facility-type
1510 Simple Network Management Protocol Snmp and Syslog
Logging history level
Commands Logging on enables logging
Logging history
Indicate a value from 0 to 7 or enter one of the following
Logging history size
Logging history size size
Indicate a value as the number of messages to be stored
Parameters emergencies, alerts, critical, errors
Logging monitor
Logging monitor level
Logging on
Logging on
Source-interface command
Logging source-interface
Logging source-interface interface
Limit number
Logging synchronous
Syntaxlogging synchronous level level all limit number-of
Of-buffers
Parameters emergencies , alerts , critical , errors
Logging trap
Logging trap level
Logging version
Logging version
Show logging auditlog
Show logging
Dellconf#logging version
Command Modes Command History Example Partial Reverse
Show logging driverlog stack-unit unit#
Show logging driverlog stack-unit
Example History
Unit#
Terminal monitor
Terminal monitor
1523
Snmp Traps
RPM0-PCP %SNMP-4-RMONRISINGTHRESHOLD Rmon
RPM0-PCP %SNMP-4-RMONFALLINGTHRESHOLD Rmon
RPM0-PCP %SNMP-4-RMONHCRISINGTHRESHOLD Rmon
RPM0-PCP %SNMP-4-RMONHCFALLINGTHRESHOLD Rmon
SFM
CHMGR-1-MINORPS Minor alarm power supply non Redundant
CHMGR-2-MINORTEMP Minor alarm chassis Temperature
TME-2-TASK Suspended Suspended svce%d inst Task%s
TME-2-ABNORMALTASKTERMINATION Crash task%s
TRAP-5-PEERESTABLISHED Neighbor %a, state %s
Vrrpprotoerr Vrrp protocol error on %S
VRRP-6-VRRPMASTER vrid-%d on %s entering Master
TRAP-5-BACKWARDSTATETRANS Neighbor %a, state %s
Redundancy disable-auto-reboot
Syntaxredundancy disable-auto-reboot stack-unit members
Stacking
Redundancy force-failover stack-unit
VersionDescription 70.0 Introduced on the S6000
Redundancy force-failover stack-unit
Reset stack-unit
Redundancy protocol
Hard
Show redundancy
Show redundancy
Span
No block sync done Dell#
Show system stack-ports
Example Status Example Topology Related Commands
Stack-unit priority
Stack-number
Stack-unit provision
S4810S4820T
S6000Z9000
Stack-unit stack-group
Syntaxstack-unit unit-idstack-group stack-group-id
Unit-id Enter the stack unit ID
Upgrade system stack-unit
Upgrade boot system stack-unit all stack-unit-number a B
Boot
1540 Stacking
Storm Control
Show storm-control broadcast interface
Show storm-control broadcast
Show storm-control multicast
Show storm-control multicast interface
Show storm-control unknown-unicast
Show storm-control unknown-unicast interface
Storm-control broadcast Configuration
Syntaxstorm-control broadcast packetspersecond
Packetsperse
Percentagedeci
Malvalue
Cond
Storm-control broadcast Interface
Storm-control multicast Configuration
Control multicast packetspersecond in command
Storm-control multicast packetspersecond
Storm-control multicast Interface
Storm-control unknown-unicast Configuration
Syntaxstorm-control unknown-unicast packetspersecond
Storm-control unknown-unicast Interface
Wred-profile name
1550 Storm Control
Spanning Tree Protocol STP
Syntaxbridge-priority priority-value primary secondary
Address as the destination MAC address in its BPDUs
Bpdu-destination-mac-address
Debug spanning-tree
Gvrp
General
Stp-id
Pvst, or rstp
Root
Disable
Spanning Tree
Enter the number of seconds the Dell Networking OS waits
To return to the default value, use the no hello-timecommand
1557
Protocol spanning-tree
Protocol spanning-tree stp-id
Show spanning-tree
Enter 0 zero to display information about that specific
Identifier
Timers
Field Description Bridge
We are
32768 0001.e800.0a56 Te 1/3
Example Brief Usage Information
32768 0001.e800.0a56 Te 1/2
32768 0001.e800.0a56 Dell#
Example Guard Field Description Instance
LIS
EDS
Portfast bpduguard shutdown-on- viol ation Priority priority
1565
System Time and Date
Clock summer-time date
End-time
Clock summer-time recurring
End-month
End-year
Start-week
End-week
Clock timezone
Timezone
Name Offset
Adjust
Authentication
Debug ntp
Ntp authenticate
Ntp authenticate
Ntp broadcast client
Ntp broadcast client
Ntp multicast client
Ntp disable
Ntp disable
Ntp multicast client multicast-address
Parameters Ntp
Ntp master stratum
Ntp master stratum
Masterstratum
Key keyid
Ntp server
Address key keyid prefer version number
Prefer
Ntp source
Ntp source interface
Ntp trusted-key
Ntp trusted-key number
Ntp authentication-key
Ntp authentication-key number md5 0 7 key
Md5
Show clock
Show clock detail
Parameters Detail
Show ntp associations
Show ntp associations
Remote
Delay
Field Description None
Ref clock
Master synced, # master unsynced, + selected, candidate
Show ntp vrf associations
Show ntp status
Show ntp status
1583
Commands Configurations
Tunneling
Tunnel-mode
Tunnel source
Number anylocal
Ip-address Ipv6-address Interface-type- number Anylocal
Tunnel keepalive
Ip-address ipv6
Unlimited
Tunnel allow-remote
Tunnel dscp
Tunnel dscp mapped value
Mapped
Tunnel flow-label value
Tunnel flow-label
Tunnel hop-limit
Tunnel hop-limit value
Tunnel destination
Tunnel destination ip-address ipv6-address
Ip unnumbered
Interface-type interface- number
Version 70.0 30.1 40.1
Ipv6 unnumbered
Version 70.0 30.1 40.0
1594 Tunneling
Vlan Stacking
Dei honor
Dei enable
Dei enable
Dei honor 0 1 green red yellow
Dei mark
Dei mark green yellow 0
Member
Stack-group-id
No stack-unit unit-idstack-group stack-group-id
Unit-id
Use no stack-unit unit-id stack-group stack-id
Vlan-stack access
Vlan-stack access
Vlan-stack compatible
Compatible command
Dell#show vlan Codes * Default VLAN, G Gvrp VLANs
Vlan-stack compatible
Tag-dot1p
Vlan-stack dot1p-mapping
Vlan-stack protocol-type
Sp-tag-dot1p
Enter the hexadecimal number as the stackable Vlan tag
Stack trunk command
Vlan-stack trunk
Vlan-stack trunk
1605
1606
Virtual Routing and Forwarding VRF
Ipv6 unknown-unicast
No ipv6 unknown-unicast
Description string
Ip vrf forwarding
Ip vrf forwarding vrf-name management
Vrf-name
Example
Syntax Parameters Defaults Command Modes
Ip route-export
Route-export
Ip route-import
Ip route-import tag route-map-name
Parameters Route-import
Ipv6 route-export
Ipv6 route-export tag route-map-name
Parameters Route-export
Ipv6 route-import
Ipv6 route-import tag route-map-name
Match source-protocol
Syntaxmatch source-protocol bgp isis ospf connected static
Imported-ospf
Redistribute imported-bgp import-ospf import-isis
Imported-bgp
Imported-isis
Maximum dynamic-routes
Command History Related Commands Version Description 70.0
Interface management
Interface management
Show ip vrf
Show ip vrf vrf-name
Show run vrf
Show run vrf vrf-name
1619
No proxy-gateway lldp
VLT Proxy Gateway
Proxy-gateway lldp
Dellconf#vlt-domain Dellconf-vlt-domain#proxy-gateway lldp
Proxy-gateway static
Remote-mac-address exclude-vlan
Remote-mac
Peer-domain-link port-channel exclude-vlan
Parameters Port-channel
Proxy-gateway peer-timeout
No peer-timeout value
Dellconf-vlt-domain-proxy-gw-lldp# peer-timeout
Vlt-peer-mac transmit
Show vlt-proxy-gateway
Lldp
Dell#show vlt proxy-gateway VLT Proxy Gateway Brief
Back-up destination ipv4-address ipv6 ipv6-address
Virtual Link Trunking VLT
Back-up destination
Interval seconds
Clear vlt statistics
Delay-restore
Delay-restore
Command History Example Related Commands
Parameters Delay-restore
Lacp ungroup member-independent
Lacp ungroup member-independent vlt port-channel
Multicast peer-routing timeout
Multicast peer-routing timeout value
Usage Information Example Version Description 70.0
Peer-link port-channel
Peer-down
Vlan vlan id
Peer-routing
Peer-routing
Primary-priority
Peer-routing-timeout
Peer-routing-timeout value
No primary-priority
Show vlt brief
Show vlt brief
Show vlt backup-link
Show vlt backup-link
DellVLTpeer1# show vlt backup-link
Show vlt counters
Show vlt counters arp igmp-snoop interface mac ndp
ARP
Show vlt detail
Show vlt detail
Show vlt inconsistency
Show vlt inconsistency ip mroute
225.1.1.2
Command Exec Modes Command History
Show vlt mismatch
Show vlt mismatch
Example for Q- in-Q implementatio n over VLT
128 4094 100 Dell#
Show vlt private-vlan
Show vlt private-vlan
Show vlt role
Show vlt role
Show vlt statistics
Show vlt statistics arp domain igmp-snoop mac
Command Modes Command History Related Commands Example
Show vlt statistics igmp-snoop
Show vlt statistics igmp-snoop
Unit-id
DellVLTpeer1#show vlt statistics igmp-snoop
Unit-id 0
Vlt domain
Vlt domain domain-id
Domain-id
Vlt-peer-lag port-channel
Vlt-peer-lag port-channel id-number
Id-number
Debug vxlan
Feature vxlan
Virtual Extensible LAN Vxlan
Version Description 70.0 Introduced on the S6000-ON Usage
Parameters Secure
Fail-mode
Vxlan-instance
Version Description 70.0 Introduced on the S6000-ON Related
Vxlan-instance VAP
Instance ID
Version Description 70.0 Introduced on the S6000-ON 40.0
Maxbackoff
Gateway-ip
Gateway-ip IP address
Ptcp
Controller
Controller ID
Pssl
Show vxlan vxlan-instance
Show vxlan vxlan-instance instance ID
Show running-config vxlan
Show vxlan vxlan-instance unicast-mac-remote
Vnid Vnid
VNI MAC
Show vxlan vxlan-instance unicast-mac-local
Tunnel
4656 000001000001 36.1.1.1
Example Related Commands Version Description 0.0
Show vxlan vxlan-instance statistics interface
Port Vlan VNI MAC
Dell#show vxlan vxlan-instance 1 physical-locator
Show vxlan vxlan-instance physical-locator
Version Description 70.0 Introduced on the S6000-ON Example
Tunnel count
Show vxlan vxlan-instance logical network
Show vxlan vxlan-instance instance ID logical-network name
Clear vxlan vxlan-instance instance ID statistics
Clear vxlan vxlan-instance statistics
Clear mac-address-table dynamic all
Clear mac-address-table dynamic all
Advertise-interval
IPv4 Vrrp Commands
Virtual Router Redundancy Protocol Vrrp
Centisecs
Authentication-type
Syntaxauthentication-type simple encryption-type password
Parameters Defaults Command Modes Command History Simple
Clear counters vrrp
Clear counters vrrp vrrp-id ipv6 vrf vrf-name
Vrrp-id
Bfd database interface ipv6 packets state timer
Debug vrrp
Command Modes Command History Usage Information Packets
Timer
Virtual-address command and enter no disable
Hold-time
Hold-time seconds centisecs centisecs
Preempt
Preempt
Priority
Priority priority
Show config verbose
Vrrp-group
Dellconf-if-vrid-4#show config
Show vrrp
Virtual-address
Grp
Master addr
Adv rcvd
Example Brief Usage Information Description Virtual addrs
Hold Down
Virtual MAC
Example Example Vrrp VRF Description Virtual IP address
Tracking states
Track
Track interface priority-cost cost
Priority-cost
Virtual-address
Ip-address1
Vrrp delay minimum
Vrrp delay minimum seconds
Enter the number of seconds for the delay for Vrrp
Vrrp-group
Vrrp delay reload
Vrrp delay reload seconds
Vrrp-group vrrp-id
Version
Version 2 3 both
IPv6 Vrrp Commands
Clear counters vrrp ipv6
Debug vrrp ipv6
Vrid
Enter the keyword bfd to enable debugging of all Vffp BFD
Show vrrp ipv6
Show vrrp ipv6 vrid interface brief vrf vrf-name
Line Beginning Description With GigabitEthernet
State master
Address Virtual IP address
Vrrp-ipv6-group
Vrrp group and is also used for VRF routing